Researchers discovered a vulnerability (CVE-2014-0160) in OpenSSL, an open source library for secure data transport used by most websites, including the enterprise cloud apps that we use for work. This vulnerability, which enables TLS “heartbeat” data packets to be passed without authentication with the server, allows hackers to steal information located in the memory of each server, which can include passwords and private encryption keys.
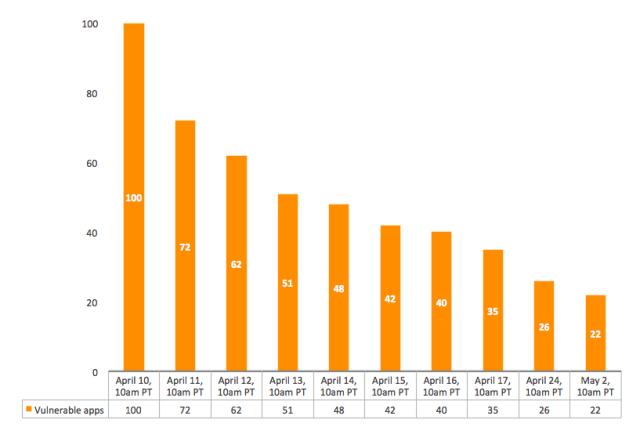
We at Netskope maintain a database of enterprise cloud apps, including ones that use SSL in order to help organizations manage their cloud app security risk. We have begun a countdown process of apps that are susceptible to this vulnerability and have not yet patched their servers. We started with the more than 4,500 enterprise cloud apps in our database, identified which ones are vulnerable, looked at the IP addresses of their SSL servers, and scanned those servers to determine whether they have been patched. We looked across the publicly-facing domains of each of the enterprise cloud apps and arrived at our count.
In an effort to release this information as quickly as possible, we have assumed that patches applied to publicly facing domains for an app have also been applied to non-publicly facing domains or subdomains. This is a good faith assumption we have made and we will update the community via this blog should we find information to the contrary. Note that this process did not result in Netskope collecting any of the data exposed by this vulnerability.
Here’s what app vendors can do to remediate their systems, if they haven’t already:
- Upgrade to OpenSSL version 1.0.1g or patch their system using a version of OpenSSL configured with -DOPENSSL_NO_HEARTBEATS.
- Revoke and reissue all certificates. Ensure new certificates use new keys.
- Alert users of the vulnerability and remediation steps.
- Have users change their passwords after the above steps have been completed.
At Netskope we also underwent the above process and have notified and published a KB article to our customers.
Learn more. Netskope Researcher, Ravi Balupari, has recorded a Netskope Movie Line Monday (we made an exception and published it on a Thursday!) about the Heartbleed bug and what it means to you. Watch it here.
Enterprise Cloud Apps That Remain Vulnerable to Heartbleed
We will periodically review the list of remaining vulnerable apps, but since we’re doing so less frequently, we will no longer publish the list to this blog. If you’d like a copy of the updated list, please reach out to us at [email protected].
We’ll be updating this status as major developments occur. Please check back with us or reach out to us at [email protected] if you have a specific question about Heartbleed or any cloud security topic.
** April 11 update **
The list has dropped from 100 to 72. The list has been updated to reflect this new total.
** April 12 update **
The list has dropped from 72 to 62. The list has been updated to reflect this new total.
** April 13 update **
The list has dropped from 62 to 51. The list has been updated to reflect this new total.
** April 14 update **
The list has dropped from 51 to 48. The list has been updated to reflect this new total.
** April 15 update **
The list has dropped from 48 to 42. The list has been updated to reflect this new total.
** April 16 update **
The list has dropped from 42 to 40. The list has been updated to reflect this new total.
** April 17 update **
The list has dropped from 40 to 35. The list has been updated to reflect this new total. Read additional analysis about The Tie Between Cloud App Enterprise-Readiness and Remediation here.
Due to slowing of remediation efforts we have changed to a weekly update frequency for this blog. Our next update will come on April 24.
** April 24 update **
The list has dropped from 35 to 26 over the course of 1 week. The list has been updated to reflect this new total.
**May 2 update**
This is our last blog update on the Heartbleed bug. The list of remaining vulnerable apps has dropped from 26 last week to 22.
If you have remaining questions, please reach out to us at [email protected].




 Back
Back 























 Read the blog
Read the blog