A new variant of the Virlock family of wormed ransomware has been detected actively propagating in the wild. Virlock not only encrypts every file in a file system, but infects them simultaneously. This converts each file into a potential infection root for branching out once it is shared over the network or through physical media. Netskope Threat Research Labs published a detailed blog on how the Virlock infection works in two harmful ways: by encapsulating the capabilities of both ransomware and a worm.
Such infection vectors possess a bigger threat to an enterprise environment where cloud storage services are used for collaboration. Any infected user within the collaboration group can transfer the infection to other machines once the service syncs the file across all of the users in the group. This gives rise to the classic malware fan-out effect wherein cloud services inadvertently amplify the threat landscape.
Netskope Threat Protection blocks all known variants of Virlock with the detection name of PE.Gn.5 and PE.Gn.8. The Virlock file infectors can be blocked from syncing to the cloud, both from the original infected user and also from the cases where Virlock might be syncing from the cloud to a new user in the same collaboration group, as shown in Figure 1.
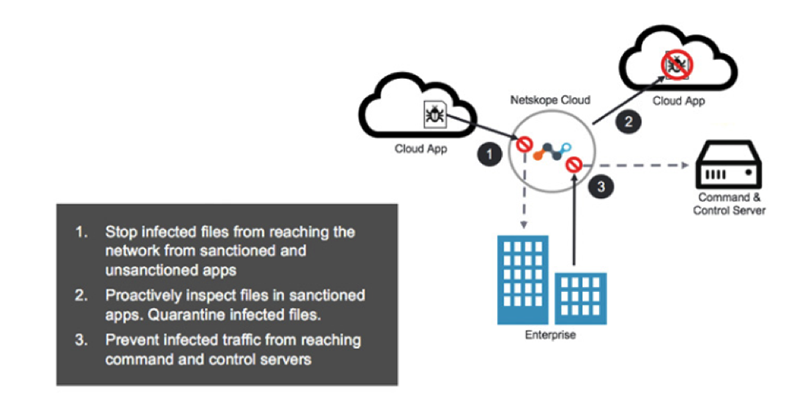
Figure 1: Netskope Threat Protection preventing Virlock infection fan-out.
Netskope recommends the following best practices to enterprises in order to protect from ransomware threats:
- Detect and remediate all threats at rest in sanctioned cloud services using a threat-aware cloud access security broker (CASB) like Netskope.
- Detect and remediate all threats being downloaded from unsanctioned cloud services using a threat-aware cloud access security broker (CASB) like Netskope.
- Regularly back up and turn on versioning for critical content in cloud services.
- On managed devices, administrators should enable the option to view known file extensions.
- Administrators should advise their users to avoid executing any files with dual extensions unless they are very sure that the files are benign.
- Administrators should warn users to avoid opening untrusted attachments, regardless of those attachments’ extensions or file names
- Enterprise users should always keep their systems and antivirus updated with the latest releases and patches.
The post Virlock’s resurgence poses bigger threat to file syncing over the cloud appeared first on Netskope.




 Back
Back 






















 Read the blog
Read the blog