Harvey Ewing: When you say security is a team sport, you hit the nail on the head. This is something that we have to be spot on with our operators, our clinicians, the people that are supporting the process, front, middle and back, in addition to our technologists. We focus across that spectrum. I don't think that there's a better way to put it today in that it has to be a team sport because as you well know, the perimeter is essentially gone in today's day and age. We have to focus from a human aspect all the way down to the lowest level of the technology stack that we have.
Announcer 1: Hello and welcome to Security Visionaries. Working in the healthcare industry has many challenges, but patient data is a top priority. From doctors to operators and technicians, that data has to remain secure and private. Harvey Ewing, Chief Information Officer at R1 RCM is ensuring that everyone in his organization acts as a human firewall. Harvey has over 25 years of experience in cybersecurity and governance risk and compliance. At R1 RCM, he is responsible for security, delivery and improvement of enterprise technology.
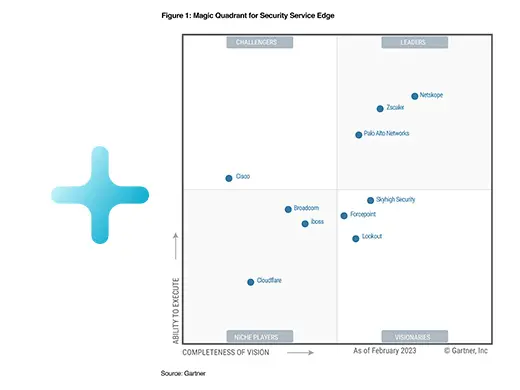
The Security Visionaries podcast is powered by the team at Netskope. At Netskope, we are redefining cloud, data, and network security with a platform that provides optimized access and zero trust security for people, devices, and data anywhere they go. To learn more about how Netskope helps customers be ready for anything on their sassy journey, visit N-E-T-S-K-O-P-E.com. Please enjoy this interview between Harvey Ewing and your host Mike Anderson.
Mike Anderson: Welcome to today's episode of Security Visionaries. I'm your host Mike Anderson. I'm our Chief Digital and Information Officer at Netskope. Today we are joined by Harvey Ewing and Harvey has got an amazing story because he started his career out as a security leader, all the way through and then became a CIO. So as we talk about our theme, security as a team sport, I feel like Harvey would be the best guest to come talk to us about that journey. So Harvey, how are you? Tell us a little bit about your background and that journey from, and that pivot from, CISO to CIO.
Harvey Ewing: Absolutely. Doing well, Mike. Great to be here. Thanks for having me. Very interesting story. I actually started out many years ago on the business side of things, so I actually have a business degree. That turned very quickly in the mid nineties into information security, which has been something I've had a passion for to this day. My last role at MoneyGram International, I was actually hired in as a Chief Information Security Officer there. About eight months into my tenure, my boss at the time, Camilla Chittle, came to me and said, "Hey, we'd like to move you into the CIO role, which I think is an excellent opportunity to bring the teams together."
I was a bit reticent at first and I thought this is a significant change. However, one thing that did stick in my mind was I can bring a couple of groups of technologists together that traditionally don't play well together. That was really the drive behind why I took the role as CIO for MoneyGram. I also kept the CISO role at the same time, which was a very unique experience. Obviously doing two jobs for the price of one was great for MoneyGram, but beneficial to me as well.
Mike Anderson: That's great. Now you've pivoted over to R1, so you left kind of the financial services space. I know you spent time in energy and in various industries. A lot of our people listening, maybe you aren't familiar with R1, so maybe give us a background on R1, the business you're in today. We'll kind of dive into more of the team sport.
Harvey Ewing: Yeah, absolutely. So you're right, big transition from financial services into healthcare. R1 is a revenue cycle management company and what that means is R1 will assist healthcare organizations with optimizing how they take care of the revenue stream for their patients. So we essentially will allow healthcare providers to focus on what matters to them most, their patients and the care that they're delivering. R1 will assist with intake of patients, the management of the patients throughout the payment and claims process, all the way to post care in some cases as well. So we also have recently acquired a company that will focus on revenue intelligence as well. So R1, the combined entities, really focus on providing the ability for healthcare providers to receive pay for the services that have been rendered, in turn allowing them to focus on what matters most and that's healthcare in their patients.
Mike Anderson: So if I hear you right, so when I go in and I pay my medical bill, I put my credit card in, it's actually you that's processing my credit card and taking the collections for them.
Harvey Ewing: That's exactly right. So R1 does assist in that manner. That's correct.
Mike Anderson: That's great. So, I imagine security is going to be of utmost importance when you talk about healthcare and then taking payment from patients that are going in. I know your CISO Cecil and we have a lot of good conversations. Talk about security and kind of the focus you've got on that as you look at R1's business and how do you prioritize that related to other areas of investment you're making as an organization?
Harvey Ewing: Yeah, that's a great question and something that R1 is incredibly focused on. Considering the amount of information that R1 has access to based on the services that we provide our clients, it's every piece of private information that you can think about, all the way from PII to private health information to payment information when services are rendered. So security is something that is at the forefront, which is a great thing. There's a tremendous amount of support at R01 for Cecil and the cyber security aspect. Obviously HIPAA is a very important part of everything that we do. Both the security and privacy role drive a lot of our response. But I will say that it's something that we can't do alone.
So when you say security is a team sport, you hit the nail on the head. This is something that we have to be spot on with our operators, our clinicians, the people that are supporting the process, front, middle and back, in addition to our technologists. We focus across that spectrum and I don't think that there's a better way to put it today in that it has to be a team sport because as you well know, the perimeter is essentially gone in today's day and age and we have to focus from a human aspect all the way down to the lowest level of the technology stack that we have.
Mike Anderson: No, absolutely. You brought up earlier that the security teams and perhaps the other teams they have to work with, there can be a little bit of friction between those two. You've got Cecil owning security, you've got the infrastructure team that owns a lot of that network side and then you also your application teams obviously that have to be part and parcel to that. How are you helping bridge those teams to make sure that they're collaborating well together so you can accomplish some of the secure outcomes you're trying to drive?
Harvey Ewing: Absolutely, and that's another good question, Mike. The first step, much like MoneyGram, was putting the appropriate infrastructure, security, network people in the same room to make sure that we're collaborating and we're sharing information and to take the emotion out of a lot of things that occur obviously in traditional infrastructure and really making sure that those teams are acting as a team. So one of the things that I talk about within IT is really something I call healthy conflict. What that means is driving to be the best that we can be in a positive manner. I want to make sure that everyone across the team, no matter what level in the organization they're in, that they know that they're to challenge the status quo, to make sure that they understand that their voice matters and to do it in a positive way, which can sometimes be difficult.
All technologists seem to want to think that they're the best and smartest in the room, which is not always a bad thing. But sometimes we have to make sure that we're doing this non emotionally and people aren't concerned around someone challenging what they've done or how we've always done it. I think that's a good thing and I hate the phrase, "Well, this is how we've always done it" and challenging that phrase is something that is at the base of what we do. The other aspect that you mentioned as well is really bringing together application developers. A lot of people talk about shifting left, but it's not really talking about shifting left, it's actually shifting left. That can be difficult because as we move through the CICD process, as people are moving into the cloud, as infrastructure becomes less of a challenge across the organization and is no longer a critical path, we get to focus on how do we really create code that is secure? Bringing the application developers and application security engineers into the same team is something that I've focused on as well.
Even those two groups will report to different people. Getting them to collaborate, making sure that they're working together, and instead of application security engineers simply being people that are going to find vulnerabilities or find issues with code and handing that back to the developer to say, "Hey, you need to go fix this," which can be difficult. It's really making sure that the application security engineers are seen as a partner. So hiring coders and putting them in the team from a security aspect and then providing the solution to the developers. So you truly do move that iteration to the left side of the equation. Now once the developers know that the application security engineers are there to partner on making the code and producing and deploying good code together, you iterate a little bit more on the left hand side, but you really hit the gas on the right hand side.
Once the team is solidified and understand that we're not there to point fingers, we're not there to call out that they've done a bad job. We're there just to fix the issue so the company can be ensured that we're deploying the best code that we can, things seem to work very, very well. So it truly is a collaborative combined approach and both teams are striving to deliver the best code that we can. So if you put all of those aspects together, Mike, and I know that's a really long winded answer to your question, but it's really breaking down the emotional aspect of it. It's also formulating that team that knows that we're truly going to work together to be successful internally so the company can be successful externally.
Mike Anderson: I have a friend named Matt LeMay who wrote a book called Agile for Everybody and it talked about breaking down silos, and people get comfortable working in the silo they're in and a lot of times they get focused there. Unless someone says "you have to bring your head up and work with other people," you don't get the agility you're really looking for. So it's great that you're driving that and it sounds like you really got, what I picked up from when you said it's really accelerating velocity of how quickly you can get releases out. Because I would have to imagine that you've seen a reduction in security stopping things from going into production because it's being built-in by design versus being a gate at the very end that often sends things back, sometimes to the starting point to get rearchitected or re-engineered.
Harvey Ewing: That's exactly it, Mike. You nailed it in about five paragraphs less than I did. But that's the intent and exactly what we want to do, and you're right. Instead of iterating and going all the way back to the beginning and trying to get a dedicated velocity to handle vulnerabilities, when you're doing it as part of the development process, it's really going to speed you up as you move through test and into upper environments and then into production.
Mike Anderson: I have to imagine, it's interesting, cause you got both perspectives. When I talk to CISOs they always talk about, well security, it's like this, you continually are putting more money into it and you're trying to figure, "Okay, when does this get leveled out to some percent that I can predict the CFO view," right? But at the same time you've got the, I think it was the CISO from McKesson said, I'm revenue generation because if we don't have a good security program, we can't win new business because people won't trust us with their data. I have to imagine that has a big play for you. How have you seen that play out? Because I think of team sport, it's not just within IT and security, it's the entire organization has that security mindset because someone else is going to trust you with their data. They got to feel like you've got at least as good a security controls as they do or even better.
Harvey Ewing: Yeah, absolutely. Again, another good point Mike, and it's important and we do get brought into the commercial and sales side from those teams in order to address those exact questions. Obviously the information that we're dealing with is the most sensitive types of information that we're going to handle for you and they're wanting to make sure that we're going to handle it appropriately and I can certainly understand why. So the important thing is sitting down and ensuring clients that we are doing the right thing, we're having the tough conversations about how we're addressing risks today. We're looking out to the strategic horizon. We're making sure that we're evolving with the threats and risks that are out there. I think that once we overcome that hurdle from a technology perspective, it's also to make sure in incumbent for us to make sure that the business leaders that we're working with are comfortable with how we address their data, how we control their data, how we monitor access to the data, who has access, when do they have access, where does it flow to.
These are all very important aspects and when we're able to do that, we become a competitive advantage for the sales team. The security team is able to go in and make sure that we address the questions that the client may have and then we let the business know that we're an enabler for the overall process and that we're combining our efforts with the other teams within the company and especially the sales teams to deliver what they're promising and that we can do that effectively and make sure that we protect the data that they have to keep protected to serve their clients. We can access that data appropriately. We can do our job so they can do their job better and that's take care of their patients.
Mike Anderson: That's great. I have to imagine when you look at your board, how are you managing that back to the board? Cause they're kind of part of that team sport as well. You got to get the board on board with what level of risk are they willing to accept. If you're talking to your peers, given your experiences a security and IT leader, what kind of advice would you give? A, how do you manage that board conversation? Then two, what advice would you give to a peer when they're thinking about how they approach security and also the questions the board's going to ask. That's two questions. Maybe take both of them in part.
Harvey Ewing: Yeah, absolutely. I think it's very, very important. Any technologist that's going to present to the board has to do one thing that's imperative in my opinion. That's not speak technical jargon but to speak business language. When you're talking about risk, risk is the key factor. Every company on the planet assumes some level of risk. R1 is no different. So going in and talking to the board is more about what is the level of risk that the company is willing to accept. What may be important from my perspective on the cyber side may not be as important to the board in terms of where we're going, how much risk they're willing to accept. So it's really creating a simple equation that indicates the level of risk that we have and may in one particular area, understanding how much it's going to cost to mitigate a specific level of risk in driving to the amount of risk that the board wants to take.
They're not going to want to spend a million dollars to reduce a hundred thousand dollars of risk. I think once you've had a chance to put that algorithm together and really take the business factors into account and you present an equation that's going to matter to the board to let them make a decision on, "Okay, here's our quantifiable level of risk, here's how much we believe we need to spend to mitigate that level of risk to get to an X level of residual risk," that they're either happy with or they're not. If they're not happy with it and they want to mitigate more risk, they may give you more money. They may say "No, we want to drive that risk down." Awesome. They also may say "No, we're willing to accept risk in these particular areas so we want you to spend less for now and maybe we'll come back and address additional levels of risk with more money later."
But it's really getting in developing that rapport with the board members. R1 board is very intent on understanding what the various levels of cyber risk are, how we're addressing them, how we're evolving with them, what they truly mean to the business. Brand and reputation in this industry is very, very important. We've all had challenges, R1 included. We've addressed those challenges, we've made pivots, we're having to go back and reevaluate some of the risks that we have based on changes in the threat landscape and having those conversations and being transparent, you don't have to know every answer to every question.
It's okay to say, "No, I don't know, let me bring that information back to you." But it's imperative that you don't go in and overwhelm people with the old fear, uncertainty and doubt. It's going in with quantifiable information based on risk that the business is concerned about or enumerating risk that they need to be aware of in the appropriate manner and then putting together a pragmatic approach to here's what we believe the risk is, here's what we believe the cost will be to mitigate that risk. Is this acceptable? Are you willing to accept more risk or less risk? Whatever that answer may be, we can tailor our solution based on the amount of risk the company is willing to accept and that drives where we are going to go from an investment perspective.
Mike Anderson: No, that makes a lot of sense. Given that unique perspective, again in your background, you're obviously very involved in the security topic within R1. Do you feel like other CIOs and other industries should have that same level of involvement? What advice would you give to your peers around the level of involvement they should have and what they should do to help their teams to become more secure in their organizations and be part of that team sport.
Harvey Ewing: Yeah, it's a really interesting question that you ask Mike because I think that especially more CIOs are getting a seat at the table, more CSOs are getting a seat at the table and that's really important because security success from a technology perspective is always top down. It's not bottom up. So it needs to start at the board level to make sure that you have the support that you need. The fatal mistake that I made early in my career is just going in guns blazing with so much technical speak that the board says, "I really don't understand what we're trying to solve here." So I think that one of the greatest things that has helped me is really looking at technology and security through the lens of a board member. What is their focus? Knowing your audience, really digesting technology related issues into a business presentation, something that is digestible, it's easy to understand and most importantly it's directly impactful to the business.
That's something that it took me a while to learn, quite honestly in my early career. When you do it from a technologist perspective, you get less return from the board. They'll thank you for your presentation, they may not be able to really assimilate the data that you're presenting. It's important to really go in and look at these particular challenges through the view of the business, introduce yourself to the board members if you're not on the board. Ask for time with those board members if you can. When you do have a seat at the table, develop that relationship with those board members. Don't wait till the board meeting occurs to really try to define your relationship within that short presentation. Reach out, set up a recurring cadence of short meetings with the board members that are responsible for evaluating your requests and the technology and security investments that the company is making.
Once you develop that relationship, once you are transparent and you present information that's relevant to the decisions that they're trying to make, they will then seek you out. In my experience in the past when I've done that, if I didn't have a seat directly at the table, board members would reach out to me directly outside of those meetings to ask for information and to talk about specific challenges. Once given a seat at the table and you develop that rapport and you develop that trust and you have that transparency, they're going to value that tremendously.
There's all sorts of changes that are going on at the executive level. The SCC is pushing the fact that boards need to be more cognizant of cyber-related issues and that board members need to have specific experience and expertise in cyber. So the opportunities are going to grow. I think that it now is the time to take advantage of those and to do it in a pragmatic way that assists the business and allows board members to make the decisions that they need to make that they're comfortable with, knowing that they're directing the company in the right way that reduces their risk is imperative for you and incredibly beneficial for them.
Mike Anderson: So I'm going to pivot for a second. There's always the insights on the board and saying, I mean that's super valuable. So as a CIO, you always know there's like those pet areas that you love to go that's like I'm an application guy by background. So it's like always get drawn to the application side. You're a security person from background, so imagine that has a lot of calling to you. So obviously security's there. When you think about your tech stack or the places you're focusing, what's your area you love to go spend time with?
Harvey Ewing: Oh gosh, another great question and you're right. I do love to dive back in when I get the chance to. It's not often these days and the team is pretty scary when I do it and it's really having tools that provide good visibility. Prevention isn't always, will be the goal. We know we're going to fail so we have to have tools that can not only secure the human, obviously that's a big area that's growing with the perimeter that's just breaking down due to so many factors in the organization. But you have to have tools that provide you with a visibility to understand and react to what's going on. If you don't have that visibility, you really can't address what you can't see. So it's really the tools that have evolved over the years that I really go back to and it's giving me that in depth ability to even trace packets.
As things evolve, Mike, it's really taking advantage of tools that are going to help me assimilate data as well. There's just so much data out there, tools that allow me to understand what are anomalies that are occurring. So, if we take a look at some of the breaches that are going on and if we take a look at the way some of the threats that are evolving, we have to know when users are doing things that are outside of their normal behavior. I think it's quite interesting, as a matter of fact, when you read some of the articles and you hear about some of the consternation that's going on with Chinese related companies that are purchasing farmland. I read an article recently where one of these particular companies actually placed 5G antennas in that farmland because it was next to or in range of some other large provider.
If someone is able to take that information and really gain inroads to corporations for authorized users, how do we know that they're doing that? It's really having the visibility and the ability to dissect what's going on in your environment and knowing what's out of the normal. Those tools that give me that ability are really what I like to take a look at. How do I piece all the puzzle together? What do I look for? How do I determine when someone is impersonating a power user in the environment? I mean, it's just fascinating. There's so many different areas to go. There's always something that you can find and looking for that is something that I'm passionate about and been doing with various tools throughout my entire career.
Mike Anderson: That visibility, where's the data flowing? We've had that question a lot internally because of what's going on in Russia and Ukraine and just the whole geopolitical environment today. It's like, "Where's my data going? Who has it? I don't want to go in the wrong places." So, that's spot on. If we look at the tech stack, obviously part of the, when you think about business process, a lot of times it's also how do you reduce friction in the process? Because it's, the more friction you put in for security, if the security's not instrumented correctly, it keeps people from getting their job done and that can create friction in the process. What are some examples where you're using technology to reduce friction in your business, whether it's in security or in a business process or application you're building? What's an example of that from a reduction of friction in your business?
Harvey Ewing: Yeah, it's a really good question as well, Mike. I think that this has really been accelerated due to COVID and remote work and work from home. I think that COVID really has changed the world. So I think reduction in friction is twofold in this case. That's really allowing users to work securely from anywhere. That's a very big benefit to companies. Obviously retaining talent is really being molded by the way in which, or we provide the ability for users to work. Conversely, it's making sure that companies can trust the work that's being done irrespective of device in irrespective of location. That's a challenge. Obviously this is something that you and your company focus on each and every day and it's important. So providing connectivity from anywhere securely to the systems that you need access to 24/7 is really one of the ways that we're reducing that friction.
It, again, works on both sides of the equation for our employees and for the company. I'm a firm believer that we're going to continue to need to be able to do this as the perimeter continues to erode. We find talent across the globe in many cases. When we can provide users with that flexibility, they're going to be happier, they're going to be more productive, they're going to want to work for the company, they're going to be less likely to move companies if they're happy and they find that level of balance, being able to work from anywhere that's approved, obviously from an R1 perspective in my case. But also making sure that they're doing what they should be doing. They have only access to the systems that they should have access to and they can't go outside of those bounds.
That has to be transparent. We can't have users that are jumping through a whole lot of hoops. Security should be as transparent as possible, ever present, but it shouldn't be something that the user is aware of in a perfect world. So the more we make security and access transparent, but secure, the better that we're doing as a team.
Mike Anderson: That's great. It's interesting, it takes me back to a comment you made earlier about people and one of the things we ran internally that was exciting is we made these t-shirts and we said, "You're the human firewall" for our people. I think we, it's so if you look at your organization, you talked about enabling people through security as well earlier, right? IT as an enabler, security as an enabler, not a roadblock. What are some things you're doing to activate your people inside R1 to be human firewalls for your business to be enablers? What are some examples of how you're doing that?
Harvey Ewing: We are really focusing on that human firewall and I think that's a great way to put it. Users have to be trained just like anyone else, to look for potential threats, to understand a significant portion of footholds in organizations come through email attacks. Why shouldn't I click on that link? What do I need to look for? Why is this important to the company? It's really engaging users in a positive manner to understand that they're on the front lines of the security of the company and that they truly are a valuable target for anyone that may want to attack R1 or any company that they may be working for. I like to engage users as much as possible and really to ensure that they understand why we're doing this. Why does all this security stuff matter? What does it really have to do with me?
I just want to get my job done. So it's not pushing a ton of training on users at the same time. It's more of a light method in my opinion that works best. When we deliver it to users, doing it in an engaging fashion, I like to deliver security awareness training through comedy. There are a lot of tools out there in which you can do that and I think that it really hits home. If we can poke a little fun at ourselves while we're doing and people understand that they typically enjoy it, they get involved. There was one particular tool that I used at a previous company that was two characters. One was named Human Error, the other one was named Sound Judgment. The training was very, very effective to the point to where I used to have Sound Judgment and Human Error shirts printed and people love the Human Error shirt. They loved to wear the human error shirt around the company and that's when you can tell that things are hitting home and they're enjoying it.
When you can laugh about it, but the training makes sense. Why do I not want to use the same password across every site that I have? Why do I not want to leave my system unlocked and walk away from it for an extended period of time? Again, poking fun at some of these situations and making it less dramatic I think has been a big hit. It's the same thing that we're doing at R1 and it's really engaging people to understand that it does matter. We don't want to scare you to death, we just want you to gauge and understand how important this is and we're going to poke a little bit of fun at ourselves. I think that the normal users like that a lot.
Mike Anderson: Yeah, I just had this vision in my head of that time before you had a passcode on your phone, you'd leave your phone on the table and you come back and they sent text messages to your friends that you really didn't want them to send that. I just had that vision in my head.
Harvey Ewing: Absolutely.
Mike Anderson: That always makes it fun.
Harvey Ewing: Absolutely.
Mike Anderson: One of the things I've been trying to champion is this whole concept of better digital citizenship. It's like at the end of the day, people would not click on the things we don't want them to click on. They wouldn't buy the things we don't want them to buy. Then when they have ideas around IT and technology and security, they bring them to us. We collaborate together. That would be the perfect digital citizen. Obviously we're a little bit away from that. What are some of things security, maybe even non-security you're doing to promote better digital citizenship within R1?
Harvey Ewing: You bring up another really good point in digital citizenship, and I think that's a really good way to put it. Because data is ubiquitous and making sure that people that do have authorized access to data do the right thing with the data. Ensuring that they use it for what they need to use it for and only what they need to use it for. Don't try to store it outside of approved areas, understanding how we're handling that patient data. R1 is a company that moves very, very quickly. We evolve very quickly, we have thousands of internal users and so it's imperative for our users to understand that we have access to some of the most sensitive data that we can have access to and to really treat it appropriately. We are working very diligently to do that. Data governance is a universe in and of itself.
It's something that R1 takes seriously. The way that we're building really the business culture around being a good steward of data is to actually do what I just said. We're creating data stewards across the entire organization. We're training those data stewards. Those data stewards are responsible for curating data in their area of control and responsibility. When you empower people to do that and you educate people on why that's important, employees get it. They understand. They want to do the right thing and we encourage it, we celebrate it. When we do the right thing, we acknowledge the people that are taking good care of the data that clients and patients have entrusted with us. When we celebrate it, people get on board. So we don't get mad at people when they make mistakes. I would say the vast amount of issues that we address from a data perspective are not people that are trying to do malicious things or trying to be expedient and get their work done.
We really work with people to educate and help correct some of the behaviors that they may be exhibiting that may not be aligned with how we should ultimately protect that data. But when they do, we celeNous récompensons les personnes qui le font. Cela permet d'instaurer une véritable confiance dans l'environnement et un engagement envers nous, car nous n'allons pas venir et nous n'allons pas vous dire que vous avez des problèmes ou faire quelque chose qui rendra votre travail plus difficile. Nous nous réjouirons de ces victoires et les gens en seront encouragés et continueront à traiter les données comme il se doit. Il s'agit donc encore une fois de s'engager, de faire comprendre aux gens pourquoi nous faisons ce que nous faisons, en quoi c'est important, puis de récompenser ce succès et de créer un élan à partir de là.
Mike Anderson : Oui, la carotte fonctionne toujours mieux que le bâton. Lorsque vous pouvez reconnaître les comportements que vous souhaitez voir chez les gens et les mettre en évidence, cela incite les autres à faire de même. C'est donc une excellente chose que vous fassiez cela. C'est une excellente façon de procéder. Cela fonctionne dans tous les domaines de la vie. J'essaie de faire en sorte que mes enfants fassent de même. "C'est un très bon travail. Je vais vous récompenser pour ce bon comportement," contre "Vous n'auriez pas dû faire ça" et cela ne fonctionne jamais de la même manière. Cette même psychologie fonctionne avec notre personnel. Je vais passer à un autre sujet dans un instant. C'est intéressant. J'en avais entendu parler, mais au début de la pandémie, lorsque j'étais chez Schneider Electric, notre président a déclaré : "Ma boule de cristal est cassée et je n'arrive pas à savoir ce que l'avenir me réserve." Donc, si nous devions avancer dans le temps comme nous le faisons actuellement, si nous nous tournons vers l'avenir, dans quels domaines pensez-vous que les DSI et les responsables technologiques devraient investir aujourd'hui pour être prêts pour l'avenir ?
Harvey Ewing : Wow. C'est une question difficile, Mike. Je suis sûr que lorsque je reviendrai sur ce spectacle dans quelques années, je me moquerai de moi-même et dirai : "Wow, j'avais tellement tort." Mais je vais lui donner ma meilleure chance. Je pense qu'il s'agit d'une question de normalisation des comportements. Harvey fait-il ce qu'il doit faire normalement ? Va-t-il au-delà des limites de ce qu'il fait habituellement, de la manière dont il le fait lorsqu'il travaille ? Je pense que cela sera très important. Je pense également que l'IA et la ML vont constituer un défi très intéressant et que la pile technologique traditionnelle que nous avons aujourd'hui va vraiment être bousculée non seulement par des technologies émergentes comme Quantum, mais aussi par les progrès de l'IA et de la ML. Lorsque vous êtes un humain et que vous vous battez contre un algorithme très complexe qui va penser un peu plus vite que vous, comment pouvez-vous suivre ? Nous aurons donc besoin d'outils, d'un cryptage capable de résister à l'énergie quantique. Nous allons avoir besoin d'outils capables d'évoluer avec les stratégies d'IA et de ML. Comment rester à la hauteur de l'IA et de la ML qui sont destinées à des fins malveillantes ? Je pense que cela va être fascinant. Si je pouvais me projeter dans l'avenir, ce serait pour comprendre, "Comment suivre les progrès de la technologie malveillante ? Comment protéger des systèmes qui seront facilement cassés à l'avenir ?" Je pense donc que c'est dans ces domaines que je voudrais vraiment disposer d'outils et me concentrer.
Mike Anderson : Je pense que vous avez raison, et c'est juste que cela devient une partie évolutive de notre paysage de menaces. Un sujet qui revient souvent. La presse en parle partout. Je sais que vous et moi en avons déjà parlé, mais la question de la confiance zéro revient souvent. La confiance zéro sera-t-elle un sujet dont nous continuerons à parler dans trois ou cinq ans ? Comment cela s'articule-t-il avec la manière dont les entreprises élaborent des stratégies de protection des données ? Que pensez-vous de la question de la confiance zéro dans son ensemble et comment pensez-vous qu'elle va évoluer dans notre réflexion sur la protection des données ?
Harvey Ewing : Oui, je pense que c'est impératif, Mike. La confiance zéro est une chose qu'il faut absolument faire à l'avenir pour un grand nombre de raisons que nous avons évoquées ces dernières minutes. Les gens auront toujours besoin d'accéder à des informations sensibles pour faire leur travail, mais comment savoir si nous avons autorisé la bonne personne, si nous avons une main-d'œuvre à distance ou une partie hybride de celle-ci, comment puis-je vraiment savoir si je donne l'autorité aux bonnes personnes ? La confiance zéro, c'est bien, c'est facile à dire, mais c'est très difficile à faire. Je pense qu'il faudra un écosystème d'outils pour nous aider à y parvenir. Je pense qu'un grand nombre des protections sur lesquelles travaille Netskope seront vraiment impératives. Je pense qu'il faudra vraiment une stratégie pour permettre une confiance zéro à long terme. Nous allons devoir continuer à pivoter pour comprendre comment nous autorisons de manière appropriée. Je pense que c'est la seule façon de donner accès aux données sensibles, à la propriété intellectuelle ou à d'autres types de systèmes nécessitant une autorisation. Il n'y a pas vraiment d'autre solution puisque le périmètre disparaît à terme.
Mike Anderson : Je vous remercie de m'avoir accordé votre temps. J'ai donc quelques brèves informations à vous communiquer en guise de conclusion. Cela va donc être amusant. Je me suis inspirée de Brene Brown, car je suis une grande fan de son podcast. Nous allons donc essayer de faire le tour de la question. J'ai donc quelques questions à vous poser. Quel est le meilleur conseil que vous ayez reçu en matière de leadership ?
Harvey Ewing : Oh, mon Dieu. C'est quelque chose que j'essaie d'ajouter chaque jour. J'échoue presque tous les jours, mais je n'ai plus d'émotion. Essayez de relever les défis difficiles avec le moins d'émotion et le plus de pragmatisme possible.
Mike Anderson : C'est un excellent conseil. Quel serait votre dernier repas ?
Harvey Ewing : Oh, mon Dieu. Je pense que je vais devoir dire le plus gros steak que j'ai pu trouver.
Mike Anderson : Vous savez quoi ? Il faudra bien qu'on aille manger un steak un jour. Merci d'avoir rejoint notre podcast aujourd'hui. Ce sera un amour.
Harvey Ewing : C'est une bonne idée.
Mike Anderson : Nous aurons des sueurs froides pendant des jours. Ce sera formidable.
Harvey Ewing : C'est très bien.
Mike Anderson : Celui-ci va vous surprendre. Quelle est votre chanson préférée et qu'est-ce qu'elle nous apprend sur vous ?
Harvey Ewing : Je crois que j'en ai deux. L'un d'eux est tiré de The Youth, Hank Williams Jr, Cowboy Can Survive. L'autre est Tears for Fears, Everyone Wants to Rule the World. So Country Boy Can Survive est révélateur de ma jeunesse. Je peux tout surmonter parce que je suis à l'épreuve des balles. Puis, lorsque j'ai commencé à m'intéresser à la cybernétique, aux infrastructures et à la distribution, j'ai publié Everyone Wants to Rule the World (Tout le monde veut dominer le monde).
Mike Anderson : C'est très bien. D'accord. Quel est le dernier livre que vous avez lu ?
Harvey Ewing : Le Servant Leadership est vraiment le dernier livre que j'ai lu. La plupart des autres activités consistent à suivre l'évolution beaucoup plus rapide de la cybernétique. Je ne suis donc pas un grand lecteur, mais plutôt un consommateur d'informations qui évoluent rapidement. Il m'est donc difficile de répondre à cette question en ce qui concerne les entreprises. Le leadership au service des autres est un élément important pour moi.
Mike Anderson : C'est très bien. Très bien, dernière question. Qui admirez-vous le plus et pourquoi ?
Harvey Ewing : Il y a beaucoup de réponses à cette question. Cette fois-ci, je vais devoir donner raison à ma femme. Sans elle, je ne serais pas là où je suis aujourd'hui. Elle est mon plus grand soutien, celle qui me maintient dans le droit chemin et me permet vraiment de faire tout ce que je fais chaque jour. Nous n'aurions pas pu le faire sans elle.
Mike Anderson : Oh, c'est très bien. Harvey, j'apprécie vraiment que vous preniez le temps de parler à nos auditeurs aujourd'hui. Avant de partir, y a-t-il quelque chose, une dernière réflexion ou une chose que vous aimeriez partager avec nos auditeurs avant de conclure ?
Harvey Ewing : J'apprécie tout le monde, j'apprécie le temps que vous m'avez accordé, Mike. Je pense que du point de vue de la sécurité, il faut simplement garder la foi et continuer à avancer parce que sans tous les professionnels de la technologie et de la sécurité, il n'y aurait pas d'affaires aujourd'hui. Tout ce qu'ils font est donc important et j'apprécie leurs efforts.
Mike Anderson : Merci beaucoup. C'est un excellent conseil et nous apprécions que vous soyez notre invité.
Harvey Ewing : Merci, Mike. Je vous en remercie.
Mike Anderson : Merci d'avoir écouté le podcast Security Visionaries d'aujourd'hui avec mon invité spécial Harvey Ewing. J'aime toujours vous laisser sur quelques points clés de notre conversation. Les trois choses que j'ai retenues de la conversation d'aujourd'hui avec Harvey, c'est d'abord et avant tout de passer à gauche et nous passons à gauche, c'est-à-dire d'intégrer la sécurité dans le processus de conception, dans le processus de développement autour de la façon dont nous créons des applications. Car nous ne voulons pas que la sécurité soit un obstacle qui freine l'innovation et le rythme auquel nous pouvons déployer de nouvelles capacités pour nos utilisateurs et nos clients. Deuxièmement, nous devons mettre le conseil en ligne en toute sécurité. Nous devons nous assurer qu'ils comprennent pourquoi la sécurité est importante et nous devons le faire d'une manière qu'ils puissent comprendre. Nous devons parler en termes simples. Dans le meilleur des cas, il est toujours bon d'utiliser des analogies. Comment présenter la sécurité en termes compréhensibles par le conseil d'administration, c'est-à-dire en fonction de mon appétit pour le risque ? Le dernier point à retenir est la transparence, honnêtement tout est essentiel. Nous devons être transparents avec nos employés sur la manière dont nous attendons d'eux qu'ils travaillent. S'agit-il d'un hybride ? Comment peut-on s'attendre à ce qu'ils fonctionnent du point de vue de la sécurité ? Nous devons définir des attentes et faire preuve de transparence à l'égard de nos employés. J'espère donc que notre entretien d'aujourd'hui avec Harvey Ewing vous a apporté quelque chose. Je sais que je l'ai fait, et j'ai hâte que vous nous rejoigniez pour écouter notre prochain épisode du podcast Security Visionaries.
Annonceur 2 : Le podcast Security Visionaries est alimenté par l'équipe de Netskope, rapide et facile à utiliser. La plateforme Netskope offre un accès optimisé et une sécurité "Zero Trust" pour les personnes, les appareils et les données, où qu'ils se trouvent. Aider les clients à réduire les risques, à accélérer les performances et à obtenir une visibilité inégalée sur l'activité de n'importe quelle application cloud, web ou privée. Pour en savoir plus sur la façon dont Netskope aide ses clients à être prêts à tout au cours de leur voyage insolent, visitez N-E-T-S-K-O-P-E.com.
Annonceur 3 : Merci d'avoir écouté les visionnaires de la sécurité. Veuillez prendre un moment pour évaluer et commenter l'émission et la partager avec quelqu'un que vous connaissez et qui pourrait l'apprécier. Restez à l'écoute des épisodes qui paraîtront toutes les deux semaines, et nous vous donnons rendez-vous pour le prochain.
Pourquoi Netskope
Pourquoi Netskope
Nos clients
Nos partenaires
Plateforme
Plate-forme Netskope One
Caractéristiques de la plate-forme Netskope One
NewEdge
Partenaires technologiques et intégrations
Produits
Produits de périphérie du service de sécurité
Borderless SD-WAN
Secure Access Service Edge
Solutions
Transformation du réseau
Modernisation de la sécurité
Cadres
Gouvernements et industries
Ressources
Ressources
Blog
Événements et ateliers
Définition de la sécurité
Entreprise
Entreprise
Équipe de direction
Solutions pour les clients
Formation et certification




























)

