
En el mundo interconectado de hoy, los datos se han convertido en el motor del éxito empresarial, impulsando la innovación, la participación de los clientes y la eficiencia operativa. A medida que las organizaciones se embarcan en una rápida transformación digital, la proliferación de la computación en la nube y los dispositivos móviles, las estrictas normativas de privacidad, como la LOPD y la CCPA, y el auge de tecnologías disruptivas como la IA, desempeñan un papel clave a la hora de marcar el rumbo. Estos factores han creado una necesidad apremiante de una solución de seguridad de datos dinámica y resistente que pueda adaptarse al panorama de amenazas en constante cambio y proteger los datos confidenciales en todas las etapas de su ciclo de vida.
Para afrontar este reto de forma eficaz, es esencial adoptar un enfoque unificado de la seguridad de los datos. Las organizaciones deben tener una comprensión clara y completa de su panorama de datos: dónde residen sus datos, su naturaleza y clasificación, quién puede acceder a ellos y los riesgos potenciales asociados a las interacciones con los datos. La prevención temprana de la pérdida de datos (DLP) se centraba en los puntos finales mediante la implementación de agentes en los dispositivos de los usuarios. Estos agentes supervisaban las actividades de los archivos y las transferencias de datos para evitar la divulgación no autorizada de información confidencial, principalmente mediante la detección basada en firmas y reglas predefinidas. El objetivo era detener las fugas de datos internos provocadas por las acciones de los usuarios. Aunque sigue siendo relevante, nuestro enfoque de seguridad debe ampliarse para abarcar los vectores emergentes. Entre ellos se incluyen las interacciones con los datos en la nube y la creciente prevalencia de nuevas aplicaciones distribuidas y soluciones de almacenamiento de datos. Para obtener este nivel de información, es necesario un enfoque evolucionado de la DLP. Ir más allá de la seguridad perimetral tradicional es fundamental para lograr una visibilidad y un control unificados de los vectores de datos establecidos y emergentes, eliminando así las medidas de seguridad fragmentadas.
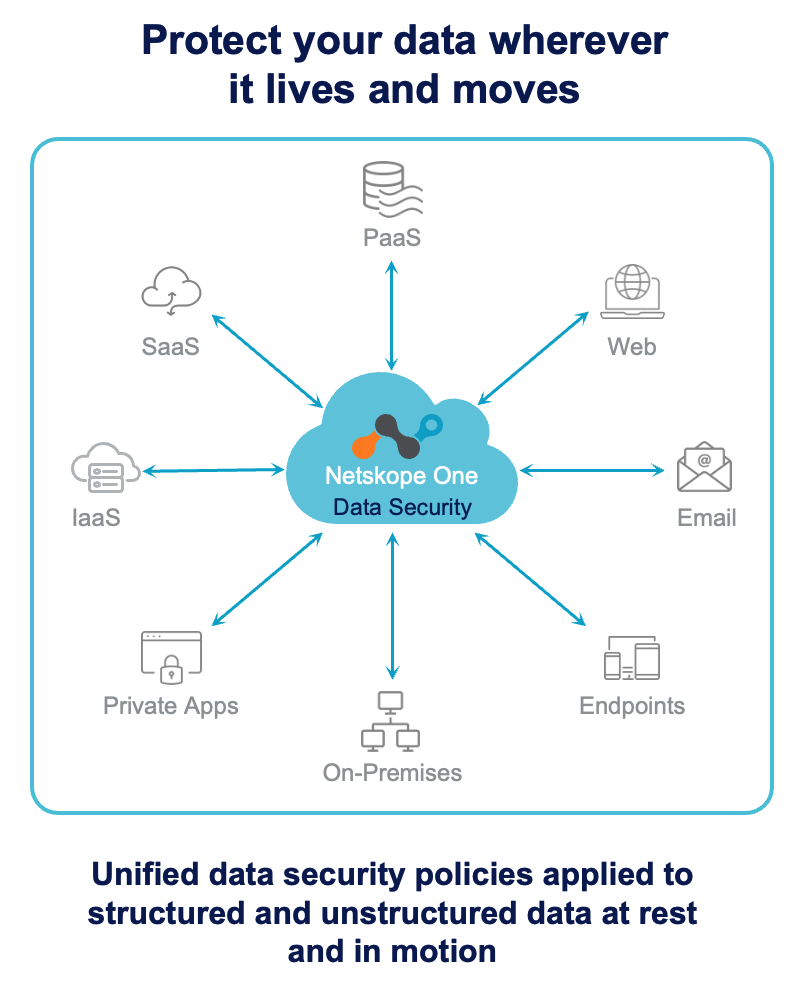
Una solución DLP completa no solo debe descubrir, clasificar y proteger los datos confidenciales, sino que también debe incluir la supervisión continua de los patrones de acceso y uso de los datos, así como la capacidad de identificar y mitigar los riesgos internos, como las fugas accidentales de datos o la exfiltración maliciosa de datos. Las funciones de aplicación, como el bloqueo de transferencias de datos no autorizadas, la puesta en cuarentena de archivos sospechosos e incluso la eliminación de datos confidenciales en tiempo real, son fundamentales para prevenir las violaciones de datos y garantizar el cumplimiento de los requisitos normativos. Estas capacidades están cubiertas por la gestión de la postura de seguridad de los datos (DSPM), que se ha convertido en una parte fundamental de cualquier estrategia integral de seguridad de datos.
Además de estas características básicas, las organizaciones deben considerar capacidades avanzadas como la gestión de derechos digitales (DRM), que permite un control granular del acceso y el uso de los datos, incluso después de que estos hayan salido de la red de la organización, y controles basados en API para aplicaciones de IA, que pueden ayudar a evitar que los datos confidenciales se utilicen inadvertidamente para entrenar modelos de IA o generar contenido potencialmente dañino. Estas herramientas pueden proporcionar una capa adicional de protección para los datos confidenciales y ayudar a las organizaciones a navegar por las complejidades de la privacidad de los datos y el cumplimiento normativo en la era de la IA.
A la hora de evaluar las soluciones DLP en un momento en el que la nube y la IA están revolucionando los enfoques de seguridad tradicionales, las organizaciones se beneficiarán de asociarse con proveedores que demuestren un profundo conocimiento del panorama de amenazas en constante evolución, un compromiso con la innovación, la capacidad de adelantarse a las amenazas emergentes y una trayectoria probada de éxito en la protección de datos confidenciales. También es esencial la capacidad de integrarse perfectamente con la infraestructura de seguridad existente, proporcionar información útil a través de informes y análisis sólidos, y ofrecer soluciones escalables que puedan crecer con las necesidades de la organización.
En resumen, un DLP sólido no es solo una buena práctica, sino una necesidad empresarial. Las organizaciones que dan prioridad a la seguridad de los datos y adoptan un enfoque proactivo del DLP, aprovechando las tecnologías avanzadas y las mejores prácticas, estarán mejor posicionadas para proteger su información confidencial, mantener la confianza de los clientes y prosperar en el competitivo panorama digital. Al proteger sus datos, las organizaciones pueden aprovechar todo su potencial y minimizar los riesgos asociados a las violaciones de datos, el incumplimiento normativo y el daño a la reputación.
Si desea obtener más información sobre cómo Netskope One DLP aborda estos retos, solicite una copia gratuita del informe IDC MarketScape: Worldwide DLP 2025 Vendor Assessment.

















