This is a series of articles focused on Next Gen SWG use cases. This is the fourth in a series of six use cases.
In my recent blog, I continued my blog series covering the most common use cases our customers are addressing with our Next Gen Secure Web Gateway (SWG). Next up is advanced threat protection.
Whether it is blocking access to malicious websites or scanning for malware being downloaded from the web, SWGs have played a critical role for more than a decade in protecting the enterprise against threats. The challenge is that the threat landscape has evolved and legacy SWGs were not built to provide the capabilities needed to protect against today’s modern cloud-enabled threats. Let’s take a look at how threats have evolved and how defenses also need to evolve to be more effective.
Before we get into examples of how specific threats have evolved, let’s start by looking at how the world around us has changed. This is important because modern threats not only adapt well to the changing environment, but these threats also take advantage of the gaps that exist in legacy security tools and their ability to provide adequate protection.
Rise of the remote worker
Prior to COVID-19, I would have shared stats that a large majority of the enterprise workforce is no longer solely located at a corporate office. We live in a globally, location-independent workplace with employees accessing applications and data from coffee shops, train stations, and of course, from home. The current global pandemic has obviously increased the number of remote workers. In fact, our research team recently reported that out of the millions of users going through the Netskope Security Cloud, about two-thirds of those users were remote. The fact is that while COVID-19 is obviously contributing to work from home numbers, when things get back to normal, we will continue to work from everywhere.
One of the challenges with legacy, appliance-based SWGs is they were built to be deployed on-premises, protecting users located behind the appliance. For remote workers not situated behind the appliance, a common way to cover them is by using a VPN configuration to backhaul the user’s traffic through the corporate data center where the SWG appliance is located and then back out to the intended destination. Also known as “hairpinning,” this has many challenges from poor user experience to increased load on the enterprise data center.
A Next Gen SWG was architected to be location-independent, covering users whether they access the web from an office, train station, coffee shop, or their home office. Core to this architecture is the ability to deploy a lightweight steering client on the employee’s managed device and steer their web and cloud traffic to a single inspection and control point in the cloud. This provides direct-to-net coverage irrespective of where the user is located.
The world is cloudy
Covering employees wherever they are is only the first step. Arguably, the bigger challenge is legacy SWG appliances and cloud-delivered SWGs introduced in the last seven to eight years are ineffective in covering today’s modern, cloud-enabled threats.
When the legacy SWG market first emerged more than a decade ago, cloud adoption was a relatively small percentage of overall web traffic. Salesforce was the dominant app and Office 365 was just entering the market. Today, more than 85% of web traffic consists of cloud apps. According to a recent Netskope Cloud Threat report, an enterprise uses more than 2,400 cloud apps. While a relatively small percentage is managed by IT, lines of business and users continue to freely adopt cloud apps at a staggering pace. This is good for the business, but also introduces risk tied to cloud-enabled threats and losing sensitive data.
Appliance-based legacy SWGs in addition to cloud-delivered SWG products introduced in the last seven to eight years, were not built to understand cloud traffic. They were architected to look at URLs, which makes sense since web traffic was king when they were built. Inspecting URLs to make sense of cloud traffic is like trying to find a needle in a haystack in a dark room with a broken light.
A Next Gen SWG understands the language of the cloud and can decode rich contextual details about cloud usage and identify risky activities. Details about the user, device, location, app, app instance, activity, and content are all decoded, parsed, and analyzed to detect risky activities and threats. Granular policies can then be applied to individual apps, app instances (e,g, corporate, partner, personal), or at the category level. Granular policies enable you to stop the bad and safely enable the good.
The new enemy: cloud-enabled threats
With cloud usage dominating enterprise web traffic, cloud-enabled threats are also on the rise. Netskope’s Tom Clare recently blogged about the cloud-enabled threat landscape and shared the following stats:
- 44% of threats were cloud-enabled in 2019 with a span over 1600+ cloud services and apps
- For the first time, 51% of threats are now file-less while 49% are malware-based
- The #1 attack method is phishing, and the #1 target is SaaS/webmail
- The apps with the most threats are: Office 365 OneDrive, Box, G Drive
- SaaS enables threats with trusted domains and valid certificates to evade legacy defenses
- Allow listing cloud apps provides a red carpet entry for threats and data exfiltration
- Published attacks are heavily using cloud services within the delivery and exploit kill chain stages
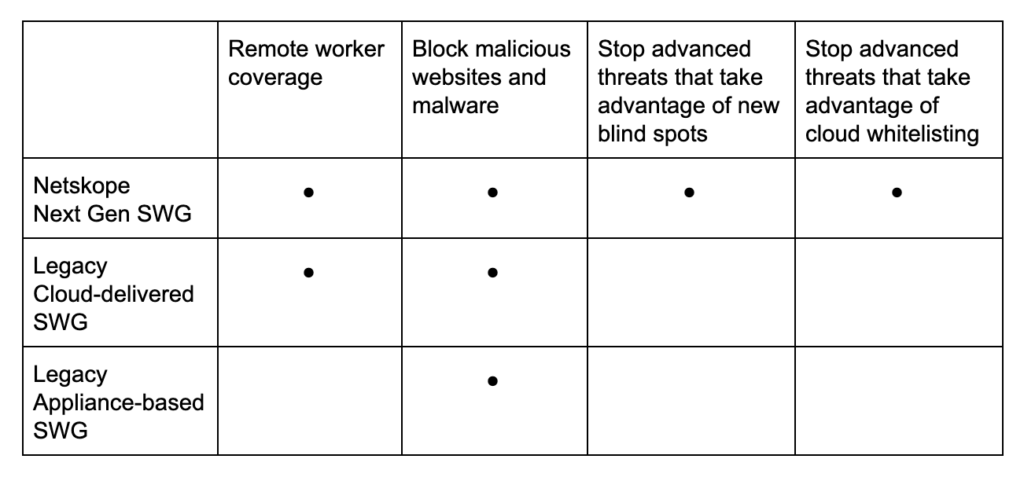
A Next Gen SWG covers remote users, is able to see beyond the URL, and decode the language of the cloud, enabling protection against today’s advanced, cloud-enabled threats. Legacy, appliance-based SWGs as well as legacy, cloud-delivered SWGs are ineffective in protecting you in today’s cloud-first world.
Threat protection requirements have evolved far beyond what legacy SWG and legacy cloud-delivered SWG products can provide. You can learn more about this Next Gen SWG use case and watch a demo here. Don’t forget to also consider the other use cases and associated requirements covered in this blog series and stay tuned for my next blog post covering use case #5, advanced data protection.




 Voltar
Voltar
















 Leia o Blog
Leia o Blog