Have you ever wondered what vulnerabilities are exploited the most by threat actors? The answers you have been eagerly waiting for could be found inside a joint Cybersecurity Advisory (CSA) coauthored by the cybersecurity authorities of the United States (CISA), Australia (ACSC), Canada (CCCS), New Zealand (NZ NCSC), and the United Kingdom (NCSC-UK), plus the U.S. National Security Agency (NSA) and Federal Bureau of Investigation (FBI). In fact, the alert AA22-117A provides details on the Top 15 Common Vulnerabilities and Exposures (CVEs) routinely exploited by malicious cyber actors in 2021, as well as other frequently exploited CVEs.
Unsurprisingly, the usual suspects such as Log4Shell, and the different flavors of ProxyShell (CVE-2021-34523, CVE-2021-34473, and CVE-2021-31207) and ProxyLogon (CVE-2021-27065, CVE-2021-26858, CVE-2021-26857, CVE-2021-26855) are very well positioned in this unwelcome chart, but in general, the opportunistic and state-sponsored threat actors were still very busy over the course of 2021 exploiting virtually any possible vulnerability targeting internet-facing services.
Top 15 Routinely Exploited Vulnerabilities in 2021 (from AA22-117A)
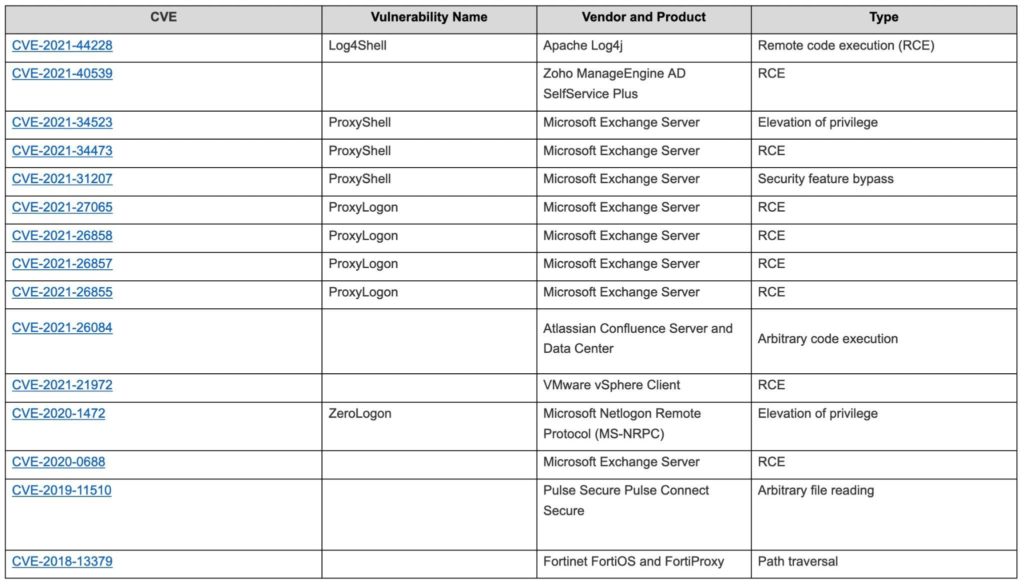
Similarly, the data shows that too many organizations have poor patching procedures in place. In fact, what is also (un)surprising is the fact that among the top 15 exploited vulnerabilities there were also two old exploits (CVE-2018-13379 and CVE-2019-11510) targeting legacy remote access technologies that were supposed to have been patched a long time ago (given that the two vulnerabilities date back to 2018 and 2019).
Remote working has become the new normal, and organizations need to make their systems accessible from a distributed workforce without significant impacts on the user experience (which sometimes collides with the legacy concept of security), and this is creating an incredible opportunity for the attackers.
How Netskope mitigates the risk of internet-facing systems being exploited by threat actors
Netskope Private Access provides an alternative to legacy remote access technologies, embracing the Zero Trust paradigm and allowing organizations to publish virtually any resource without making it explicitly visible and capable of accepting explicit inbound connections (and hence mitigating the risk of exploitation of zero-day or unpatched vulnerabilities). It is possible to publish resources located in a local data center, but also in a private or public cloud, segmenting the access at the application level (in contrast to a traditional layer 3 VPN) and performing a security posture check before the access to the requested resource is granted.
At every moment the organization can monitor access to the published assets thanks to a specific dashboard available with Netskope Advanced Analytics, with rich details and insights, supporting the security and operation teams.
Stay safe!

















