
Any organization that’s undergone a security transformation knows the promise of zero trust network access (ZTNA): secure, least-privilege access to private applications, anywhere, on any device. But turning that promise into operational reality is often far from simple. Between fragmented tools, complex configurations, and sprawling environments, implementing ZTNA can quickly become a manual, time-consuming, and error-prone process.
What if you had an intelligent assistant to guide you every step of the way?
Netskope is excited to introduce a game-changing capability within Netskope One Private Access: the Private Access AIOps Agent. This isn’t just another feature; it’s an AI-powered partner designed to help implement precise application segments and context-aware policies with ease. It continuously reviews configurations, refines access controls, and handles routine housekeeping tasks to keep your ZTNA posture optimized, secure, and efficient.
The challenge: ZTNA complexity vs. zero trust promise
Implementing ZTNA right means shifting from broad network access to fine-grained, context-aware and adaptive zero trust controls. That includes:
- Discovering all private applications, often starting with broad IP subnets and wild-card domains
- Refining those into precise application segments
- Defining access policies based on user roles, device posture, location, data, and threat protection controls
- Auditing continuously for gaps, unused rules, and stale configurations
This process, while crucial for security, can be manual, time-consuming, and prone to human error, especially for organizations where the volume of both users and applications have increased over the course of several years via mergers and acquisitions. Operationalizing ZTNA can seem overwhelming, and in some cases may lead to questioning the security benefits that ZTNA is meant to deliver.
Your AI-powered assistant for ZTNA administration
The Private Access AIOps Agent provides “Admin supervised” capabilities designed to actively strengthen and continuously optimize your ZTNA posture in the enterprise.
Here’s how it implements and improves the ZTNA posture:
1. From broad access to precision-built application segments and policies
ZTNA often begins with broad definitions, IP subnets, wildcard domains, and wide network destinations, simply to get visibility and ensure coverage. But zero trust maturity demands more than that.
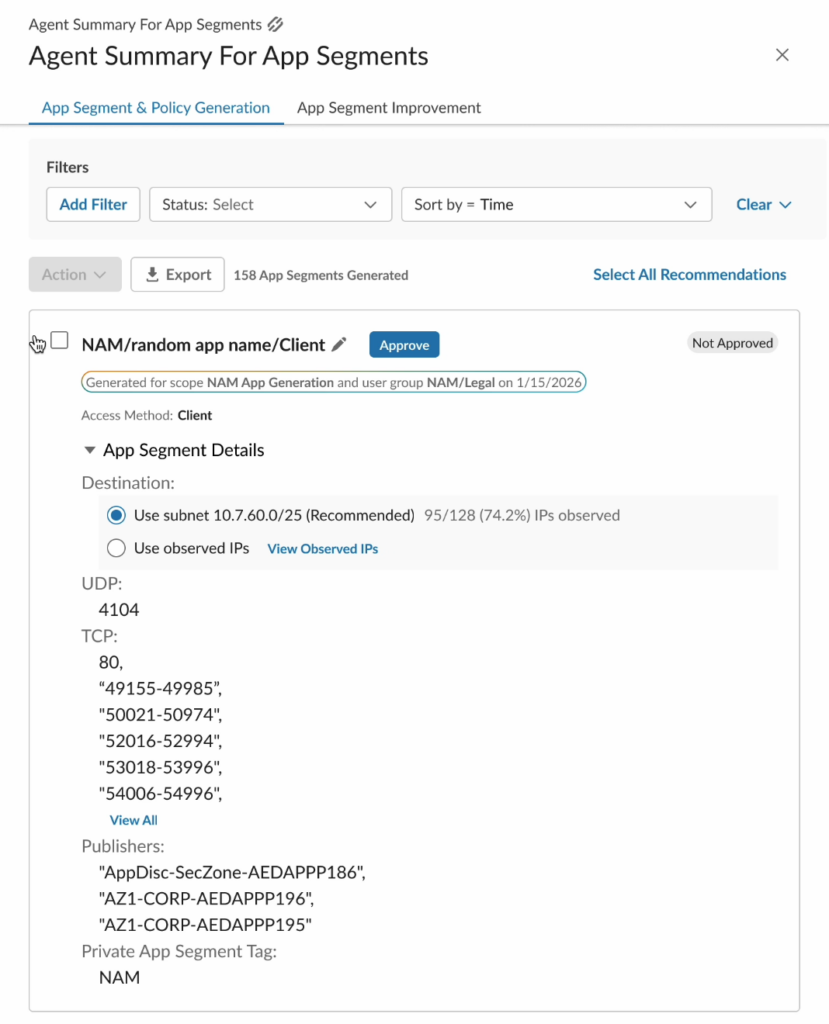
The Private Access AIOps Agent analyzes your existing policies and network destinations, and automatically generates granular application segments that reflect actual access patterns. Instead of “any user to any destination in this range,” you get precise, least-privilege definitions aligned to how applications are actually used.
Administrators remain in control. They can direct the Private Access AIOps Agent to generate granular segments based on specific application types, access methods, active directory attributes, or even individual users. The result? Precise entitlement, tighter policies, and a faster path to true least-privilege access, without investing significant manual effort.
2. Continuous auditing and intelligent clean-up
Zero trust isn’t a one-time project. Scope evolves. Entitlement changes. Applications are introduced. And over time, configuration sprawl creeps in.
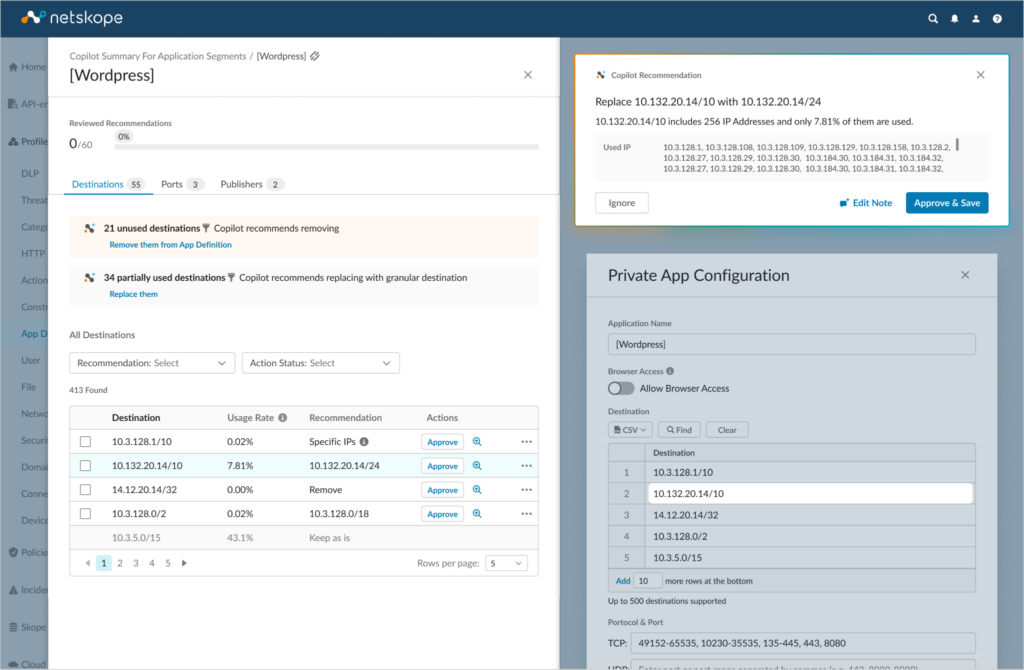
The Private Access AIOps Agent continuously evaluates your existing application segments and policies within your tenant and surfaces actionable recommendations to strengthen your posture. That includes:
- Replacing broad network destinations and wildcard domains with precise IP destinations and FQDNs in existing application definitions
- Identifying and removing dormant configurations—unused destinations and ports, as well as offline publishers.
This optimization reduces attack surface, simplifies operations, and ensures your ZTNA environment stays aligned with zero trust principles as your organization grows and changes.
The future of ZTNA is intelligent, adaptive, and continuous
With the Private Access AIOps Agent, Netskope isn’t just offering a tool, it’s providing a strategic advantage. This capability reflects our commitment to providing a compelling VPN alternative, while meeting the evolving demands of implementing ZTNA across the enterprise. With AI-driven accuracy, you can move faster, reduce risk, and secure access at scale across any device, including unmanaged, IoT, and OT endpoints.
ZTNA shouldn’t stall under operational complexity. With Private Access AIOps Agent, it becomes intelligent, continuous, and built to scale.
Ready to modernize your private access strategy? Netskope’s Private Access AIOps Agent is here to be your trusted guide.
See how Netskope One Private Access delivers secure, intelligent connectivity, anywhere, for any user or device.




 Indietro
Indietro

















 Leggi il blog
Leggi il blog