Overview of the Netlify Scam
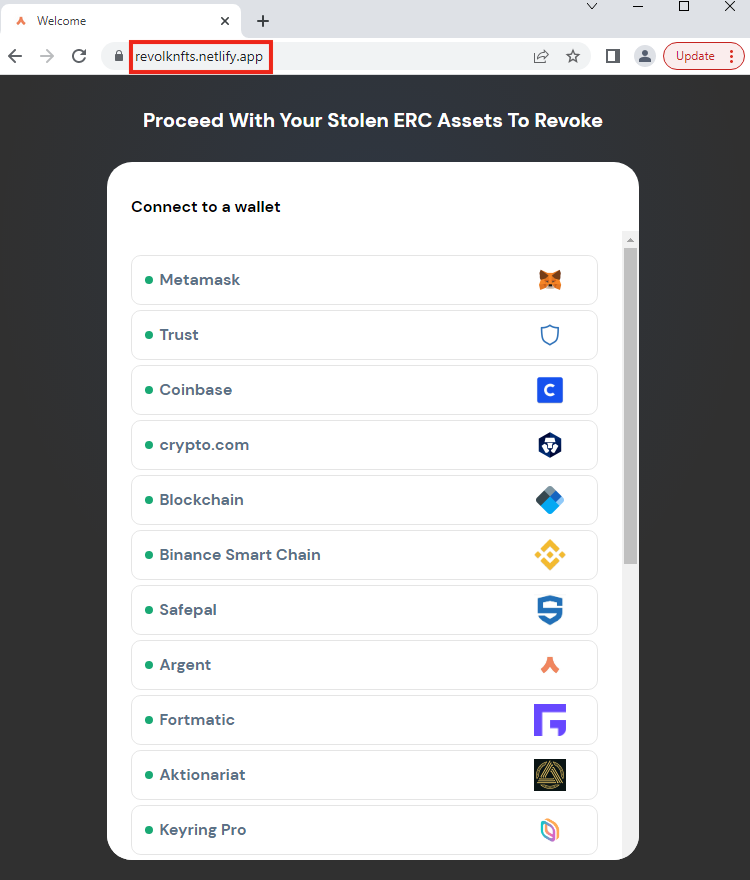
Netskope Threat Labs spotted a new crypto-phishing attack that aims to steal sensitive data from crypto wallets, including private keys and security recovery phrases, disguising itself as a service to revoke stolen ERC (Ethereum Request for Comments) assets. The page was created and hosted with Netlify, which is a free cloud service to create websites and apps.
What makes this Netlify scamming technique novel is that the attacker is targeting 21 cryptocurrency wallets in the same page, eliminating the need to maintain individual websites for each type of crypto wallet, like we saw in the crypto-phishing campaigns we spotted in August and September. Those attacks were targeting multiple crypto wallets through a chained phishing attack abusing Google Sites and Microsoft Azure.
In this blog post, we will analyze this phishing page to demonstrate how this new technique works.
How the Netlify Crypto Phishing Attack Works
The phishing page is hosted with Netlify and the main page tries to lure the victim by mimicking a service to revoke stolen ERC assets. To lure the user to use the fake service the page offers a fake connection with 21 different cryptocurrency wallets, which include:
- MetaMask
- Trust
- Coinbase
- crypto.com
- Blockchain
- Binance Smart Chain
- Safepal
- Argent
- Fortmatic
- Aktionariat
- Keyring Pro
- BitKeep
- SparkPoint
- OwnBit
- Infinity Wallet
- Wallet.io
- Infinito
- Torus
- Nash
- BitPay
- imToken
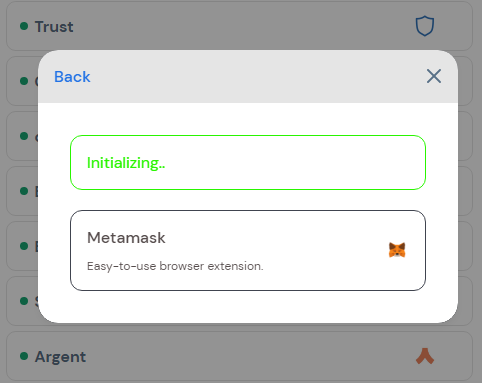
Once the victim selects a cryptocurrency wallet to connect, the phishing page displays a fake modal that simulates a connection with the wallet’s service.
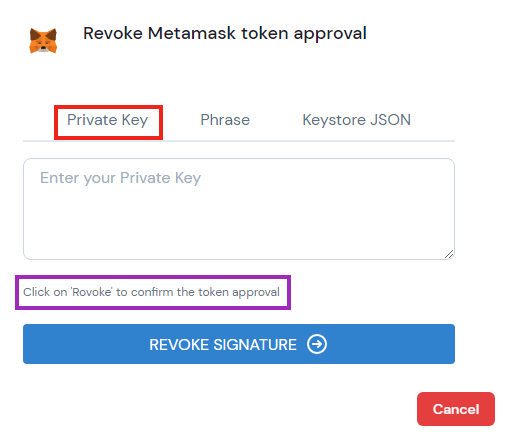
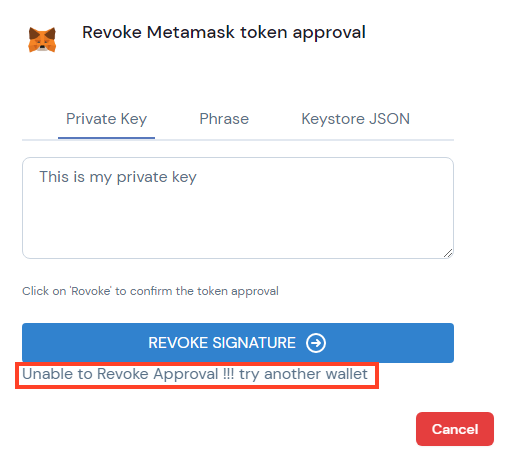
Then, a new modal is displayed, asking the victim for sensitive data in order to proceed with the fake revoking service. It tries to steal three different types of data. The first one is the cryptocurrency private key.
In this specific modal, there’s even a typo in the word “Revoke”.
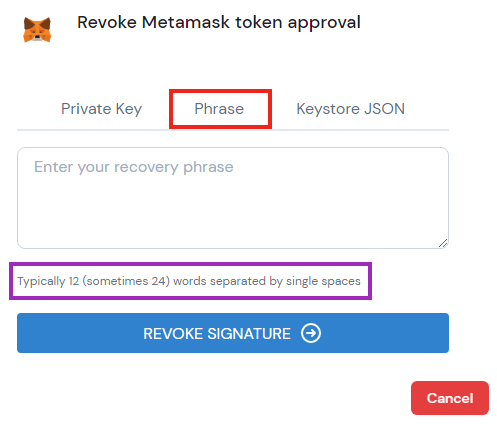
The second piece of data it tries to steal is the security recovery phrase, which can be used to import the wallet, as we explained in a previous blog post.
And lastly, it tries to steal a keystore file in JSON format.
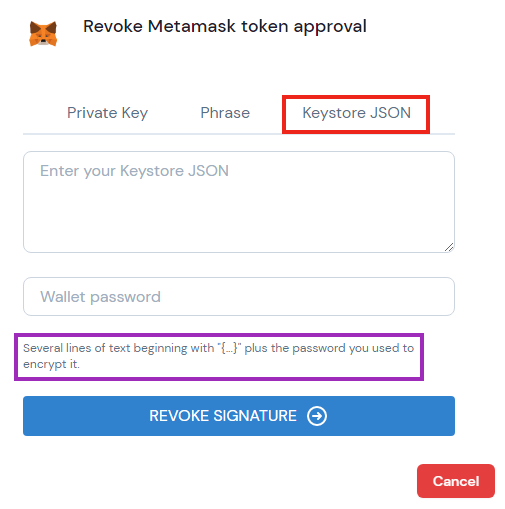
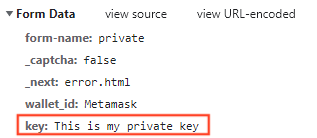
Once the “Revoke Signature” button is clicked, the webpage sends the sensitive data to the attacker through a POST request to the same page.
Finally, after stealing the data, the page shows a message that says it was not possible to revoke and asks to try for another digital wallet. It also automatically closes the modal and opens a new one for a different wallet.
These three pieces of sensitive data (privacy key, recovery phrase, and keystore JSON) that the attacker tries to steal can be all used to provide access to someone’s crypto wallet, allowing the attacker to exfiltrate currency.
Aside from these 21 targets, the webpage also contains an option to connect to “Other Wallets”, increasing the attack surface even more, covering possible crypto wallets that are not listed by the attacker.
Conclusions
This cryptocurrency wallet phishing technique shows how an attacker can increase the chances of success and also reduce their costs by targeting multiple crypto wallets at the same time with a single page hosted with a cloud application. We strongly recommend individuals to not enter sensitive details, such as private keys and secret recovery phrases, on unknown websites. If you’ve lost access to your account, please contact the official support for your wallet to verify the correct steps to follow.
Protection
Netskope Threat Labs is actively monitoring this campaign and has ensured coverage for all known threat indicators.
IOCs
Phishing URL
hxxps://revolknfts.netlify[.]app/index

















