Summary
Netskope has recently released two exciting enhancements to our Advanced UEBA product. The enhancements are:
- Key Detection Scenarios, which provide a reason for the impact on a user’s confidence index (UCI) score
- User Confidence Alerts, which generate alerts for UCI scores that cross below a threshold
Together, these two new features streamline operationalization of Advanced UEBA by providing operators alerts when it identifies users exhibiting risky behavior and an at-a-glance summary of the risky activity observed for each user.
In this blog post, we’ll discuss both of these features and provide some insight into how they can be used to discover and address real threats to your organization.
Key Detection Scenarios for Actionable Alerts
Advanced UEBA contains a feature called the User Confidence Index (UCI), analyzing and correlating user activity to present a holistic view of which users present the most risk through a scoring system that goes from 0-1000.
While the users with the lowest UCI scores represent the highest risk to the organization, operators need to understand at-a-glance why a user is risky so that they can trigger appropriate investigation and remediation workflows. For that reason, we recently introduced the “Key Detection Scenario” label for each risky user.
The Key Detection Scenario provides the predominant reason for each user’s moderate or poor UCI. In order to determine the Key Detection Scenario, we look at the labels on the alerts and display the scenario that accounts for the biggest impact on the user’s UCI.
The example below shows a user has a UCI score of 399 out of 1000 (in the moderate risk range), and the Key Detection Scenario is “Insider threat – Data movement.” This means that the user is moving data from a corporate managed cloud app to an unmanaged cloud app or instance. The user may be exfiltrating sensitive data to a personal cloud storage app, and this is an incident that should be investigated further.
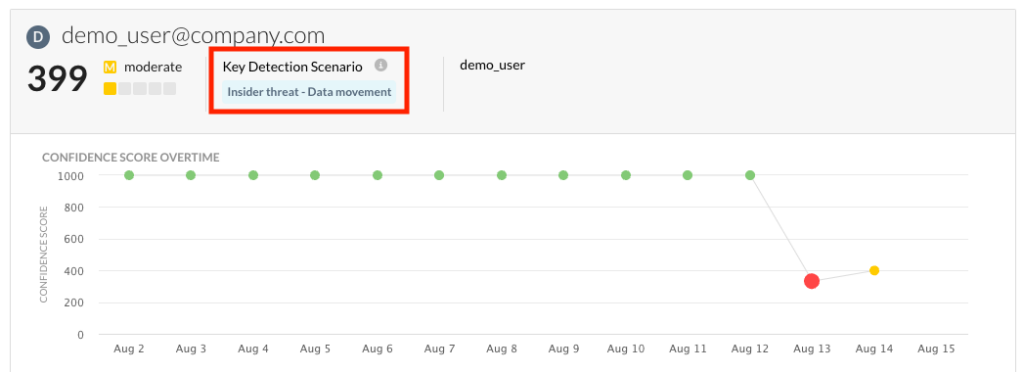
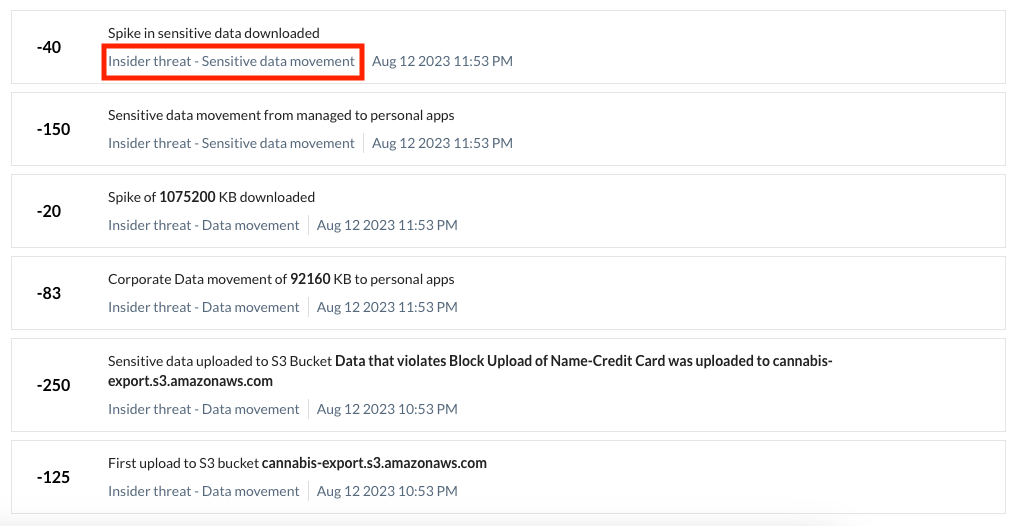
On the incidents page, you can also see the alerts that contributed to the user’s UCI score, and the detection scenario associated with each alert:
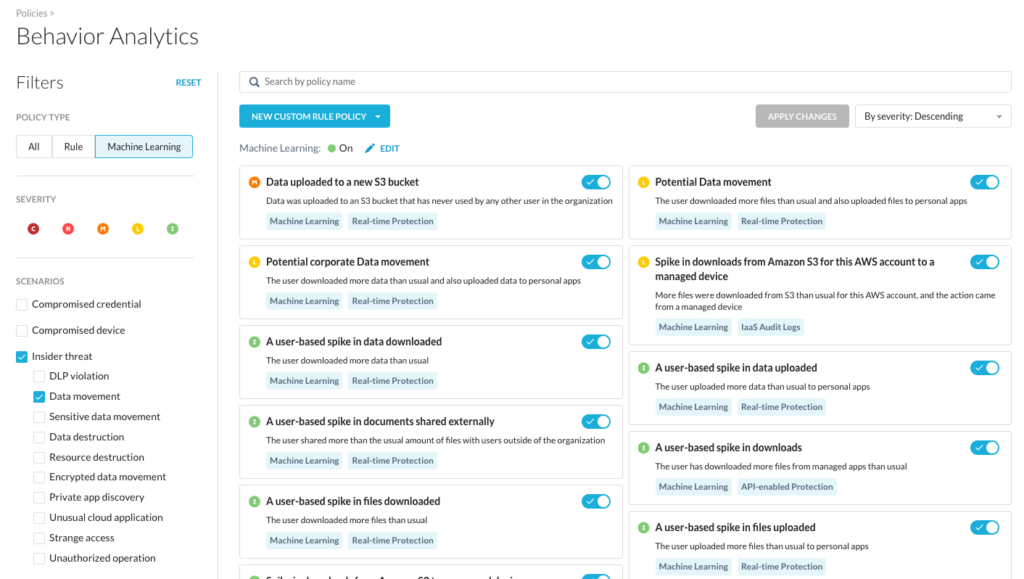
In addition to having a narrative around the current user’s score, we can click on the Key Detection Scenario value to pivot to the Policy page, which shows us which policies fall under this particular scenario, as shown below. Here we could take further action on any of the policies being used for this scenario that we deem appropriate, such as adjusting the severity or disabling them:
Key Detection Scenario Values
Key Detection Scenarios are meant to give actionable insights to operators. Since there are more than 100 different UEBA policies, we have a wide variety of possible scenarios that would require a very different response. For example, if the Key Detection Scenario associated with a user’s UCI score is “Compromised device – Ransomware,” then the team can examine the user’s devices for ransomware and address it. However, if the Key Detection Scenario was “Insider threat – Data movement,” then the response may entail looking at what applications the user was moving data to, and if they violated DLP policies.
Below are the different scenarios currently available when this article was written. You will notice that all of the scenarios fall into three main categories that UEBA uses, which are compromised credential, compromised device, and insider threat. The policies all fit into these categories, so every alert will have only one of these values assigned when it is triggered.
- Compromised credential – Application discovery
- Compromised credential – Data destruction
- Compromised credential – Data movement
- Compromised credential – Private app data movement
- Compromised credential – Resource destruction
- Compromised credential – Strange access
- Compromised credential – Unauthorized operation
- Compromised device – Application discovery
- Compromised device – Command and control
- Compromised device – Encrypted data movement
- Compromised device – Malicious site
- Compromised device – Malware
- Compromised device – Ransomware
- Compromised device – Third party
- Compromised device – Unusual application
- Insider threat – Data destruction
- Insider threat – Data movement
- Insider threat – DLP violation
- Insider threat – Encrypted data movement
- Insider threat – Private app discovery
- Insider threat – Resource destruction
- Insider threat – Sensitive data movement
- Insider threat – Strange access
- Insider threat – Unauthorized operation
- Insider threat – Unusual cloud application
User Confidence Alerts
Netskope Advanced UEBA automatically computes the User Confidence Index (UCI) score for every user on the platform. However, manually monitoring thousands of users is not scalable. This is why, to enable our customers to scale and to streamline operations, we have also implemented User Confidence Alerts. User Confidence Alerts generate an alert any time a UCI score goes below a threshold.
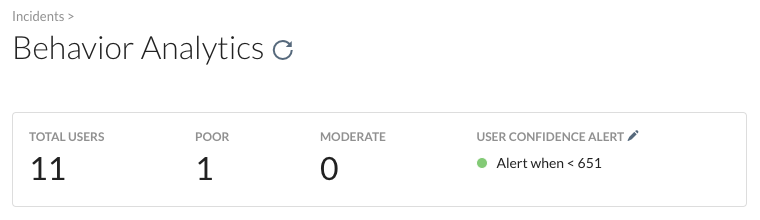
The threshold is set in the Incident view, as shown below. If you click on the pencil icon, you are able to set the threshold to any integer between 1 and 999. By default, scores between 351 and 650 are considered moderate, and 350 or below are considered poor. We believe alerting below 651 is a good start for most organizations.
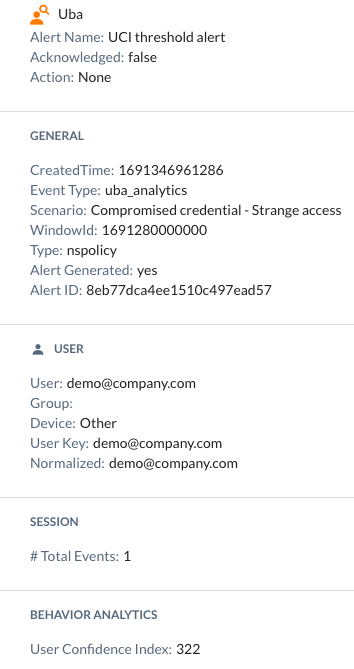
The alerts generated will also include pertinent information, such as the user involved and why their UCI dropped, so that security operations teams can respond. The alerts will appear in SkopeIT, and can be forwarded to other systems like a SIEM or a SOAR.
An example of what this type of alert looks like is shown below. It shows that our demo user reached a UCI of 322 (which is poor), and the Key Detection Scenario around the drop is, “Compromised credential – Strange access.”
The key difference here is that now your security operations teams will receive an alert to surface this situation to you, so you don’t have to go looking for the riskiest users. In addition to being able to see the alerts within the Netskope platform, you can also export these alerts to external systems using the Netskope Cloud Exchange. The cloud exchange module, “CTO”, can automatically open tickets in your ITMS system and integrate it with your processes, or send alerts to incident responders via Slack or MS Teams to expedite the response.
Conclusion
In this blog post, we discussed two great new features for our Advanced UEBA customers:
- Key Detection Scenarios, which provide a reason for the impact on a user’s confidence index (UCI) score
- User Confidence Alerts, which generate alerts for UCI scores that cross below a threshold
There will be a follow-up to this blog coming soon, covering more information about how to conduct investigations using Advanced UEBA that go beyond the features mentioned here. Enabling the SOC to quickly find and investigate issues, create watchlists, and seamlessly exchange data between systems is something that we are constantly improving.
We are excited because Advanced UEBA has been battle tested, and uncovered many true positives for our customers already. We know that these features will make it easier than ever to find, assess, and address real threats in your organization. For more information on the UCI and these features, please visit this article. If you would like to see real case studies of incidents found with Advanced UEBA, you can see those here.




 Retour
Retour
















 Lire le blog
Lire le blog