I had the pleasure of spending some time with our Australian and New Zealand teams this month, and throughout my trip I heard over and over again that one of the most beloved and differentiating things within the Netskope platform is the facility for user coaching. It’s actually something I hear from teams around the world, but sometimes it is a feature that can get lost when we talk about the vast capabilities packed within a SASE platform. So, I picked up my roving reporter notebook and cornered Dane Blackmore, head of our NZ team, to find out more…
Emily: OK, let’s start at the beginning for anyone not sure what this is all about. What exactly do we mean by ‘“real-time user coaching”?
Dane: An effective user coaching system is something that is embedded into an organisation’s cybersecurity platform. The idea is to give clear “just-in-time” feedback to users on how to avoid risky behaviour, while simultaneously showing them safer alternatives to achieve their objectives.
Emily: This sounds like a nice and simple use case, and not hugely technical. Forgive the silly question, but is it hard to do?
Dane: It’s not hard to use, for a security administrator, but its simplicity belies some pretty clever stuff going on under the bonnet. Our user coaching is built upon App Scores (we have the security and operating credentials of nearly 60,000 different cloud applications detailed out-of-the-box) as well as an organisation’s own tailored policies. And it gets particularly powerful when the platform that it is built into has granular awareness of changing context including user location, device, identity, user behaviour, threat, application risk… At that point, user coaching can become an intertwined part of a zero trust approach, making users a critical part of defence.
Emily: Oh I like that. So often we hear about users being the weakest link, but this kind of flips that doesn’t it?
Dane: Absolutely. I heard one member of the team internally explaining the other day that regardless of the clever technology in place, no organisation ever completely avoids every phishing email or dodgy cloud link arriving in front of the user. But all it takes is for one user to not click it and we win. That’s what user coaching does. Humans are not the weakest link in our security posture, they are our last line of defence, so it’s important that we recognise that and train them.
Emily: Ah but every organisation trains users in cybersecurity. I have sat through plenty of annual training courses.
Dane: And there is value to be found there. But how much of what you were told have you retained? It’s the fact that the helpful information is presented in the moment when it is needed—the real-time bit—that is what’s really powerful.
Emily: OK, talk me through that. What does that look like? Are we talking about a security version of Mr Clippy?
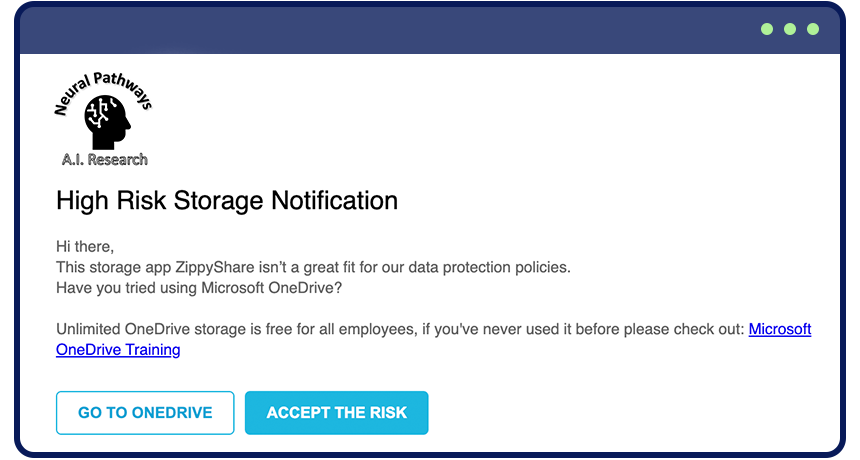
Dane: Ha! Nowhere near as annoying (a key point actually, because this is designed to help the user as much as the security team). Let’s look at an unintentional risky behaviour, when users access unsanctioned tools for data storage (for example Zippyshare), data sharing (for example WeChat or WeTransfer), or data conversion (for example online PDF converters). As the IT department has no control over data once it lands in these applications, they have no way to ensure that data doesn’t fall into the wrong hands and become a future risk to the organisation. In most cases employees accessing these services are simply unaware of the risk, and are trying to be productive with tools they are familiar with. Rather than just blocking this activity outright (potentially leading to a disgruntled employee who tries harder to work around the system), user coaching can be deployed to explain the risk, and recommend other, safer tools for achieving the same outcomes.
These training messages are often in the form of a pop-up box, and the wording can be crafted to say anything you like (though many can be easily lifted out of the box, when you are looking to quickly implement basic standards based on our App Scores).
Emily: What do they say?
Dane: It could be something as simple as “This app isn’t a great fit for our data protection policies. Have you tried using X” (a fully managed and secure alternative… probably being paid for already by the organisation!). A favourite example of mine actually came from an Australian customer who didn’t want to block access to an app, but wanted to dissuade employees from using it unless absolutely necessary. They switched a box so it no longer said “proceed” and instead said “accept the risk”. As you can imagine, that made users stop and think. They read the alert info when before they had unthinkingly proceeded. And that one switch caused a huge change in the percentage that went on to use the riskier app.
Another interesting application of user coaching that I have seen customers using lately turns it into a two-way feedback loop between IT and the organisation’s employees.Rather than just treating IT as an omniscient force that dictates a list of approved (or sanctioned) applications, this approach assumes an ongoing growth of sanctioned applications over time, and seeks feedback from the business around which applications should be supported. Real-time user coaching can be deployed here to request “Business Justification” from users trying to access unmanaged apps, for example it might say:
“Hi there user, we can see you are trying to access the tool Microsoft Dynamics which fits into the category of CRM Tools. Our company’s managed CRM tool is Salesforce, can you please explain what functionality you need from this tool that you can’t do today with Salesforce?”.
The user feedback provided can then be collated, and used to determine whether there is a suitable overall business justification for investing in licences for the requested new applications.
Emily: Yeah, this is all pretty cool.
Dane: Feedback from our NZ Netskope customers is that real-time user coaching has helped to reduce some of the friction between the IT department and the rest of the business, while also reducing the number of problem tickets from users who in the past haven’t understood why they were being blocked from tools they saw as productive.
Emily: OK, one last question… Can you give me some top tips for how to make real-time user coaching as effective as possible?
Dane: Top tips… ok… Firstly it should be highly customisable. While out of the box stuff gives a huge helping hand at the start, you want it to fit the specific needs of each organisation, and administrators should have the flexibility to perform different levels of enforcement depending on the context of the situation. Some examples might be:
- Application is known to be very high risk—block it outright, explain why, and redirect users to safer alternatives.
- Application is medium risk—inform users of the risk but allow them to continue, so long as they provide a written justification.
- Application is low risk but not IT-managed, user attempts data upload (no sensitive information)—allow upload to happen without restriction.
- Application is low risk but not IT-managed, user attempts data transfer (includes PII, PCI, or other sensitive information)—block transfer, inform and redirect user to managed storage.
There’s no limit to the granularity you could go into. And I think I would also reiterate that user coaching is good, but real-time feedback is key. You want to give lessons and recommendations within the flow of an activity for immediate action and better stickiness in terms of people remembering things for next time too.
Emily: Dane, this has been so interesting. I can see why customers like this feature so much. Thank you for taking the time to talk about it with me.
I love hearing about the ways customers are using our technology. For more about user coaching, take a look at this blog from Mike Anderson that gets into how real-time coaching can help with Shadow IT. Your roving reporter will be back with more tales from the frontline soon!

















