Netskope Threat Research Labs has observed an email-server message block (SMB) blended threat which uses the compromised machine as a stepping stone to propagate laterally via the EternalBlue exploit. The attack is a refinement of the attack highlighted in our earlier ongoing data theft attacks blog. This inclusion of the EternalBlue exploit is insidious because it will be launched internally from the newly infected machine, likely permitting direct access to shared SMB machines such as file shares and backup systems. This puts core data stores at risk in a fashion that may be impossible to anticipate.
Earlier this year, “The Shadow Brokers” group disclosed a series of exploits, backdoors, and several attack tools affiliated with an Advanced Persistent Threat (APT) actor dubbed “The Equation Group.” In the archive dump, one of the exploits, EternalBlue, targeted open SMB ports to leverage remote code execution by specifying malformed values during the Microsoft SMB NT Trans2 Request.
Exploits from the Shadow Brokers archive have been widely used in attacks such as WannaCry, NotPetya, and more recently BadRabbit.
Perimeter breach and internal wormed propagation
The initial attack begins with a Swiss regional email which contains a Word Document with an embedded .lnk object, detected as Backdoor.Agent.CNKZ. In the case below, the attachment looks like a preview image which would entice the user to click on it executing the payload.
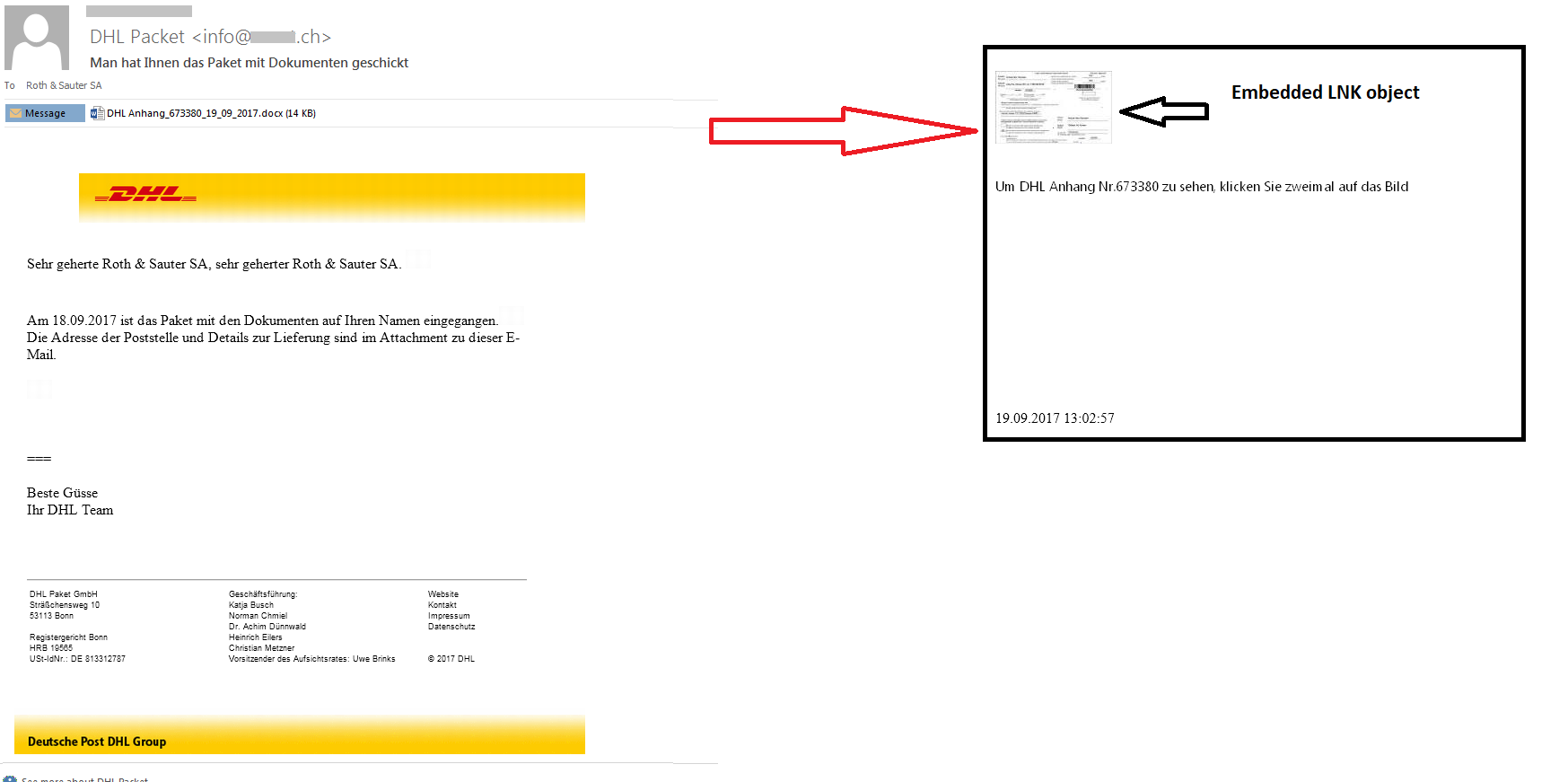
Figure 1: Embedded .lnk file in a Swiss regional attack email
On execution, the .lnk file downloads the EternalBlue payload as well as Retefe using PowerShell as shown in Figure 2. At the time of this writing, the payload at this URL has been taken down.
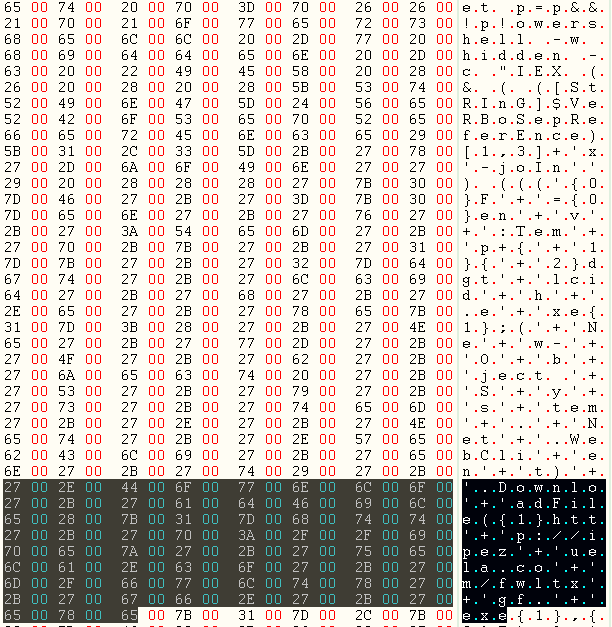
Figure 2: The .lnk file containing the EternalBlue payload URL
At this point, the threat moves from a cross-perimeter attack to an internal attack. The EternalBlue SMB exploit will be launched from the newly compromised stepping stone spreading itself across an organization’s network. The visual depiction of the SMB wormed attack against neighboring internal computers is shown in Figure 3.
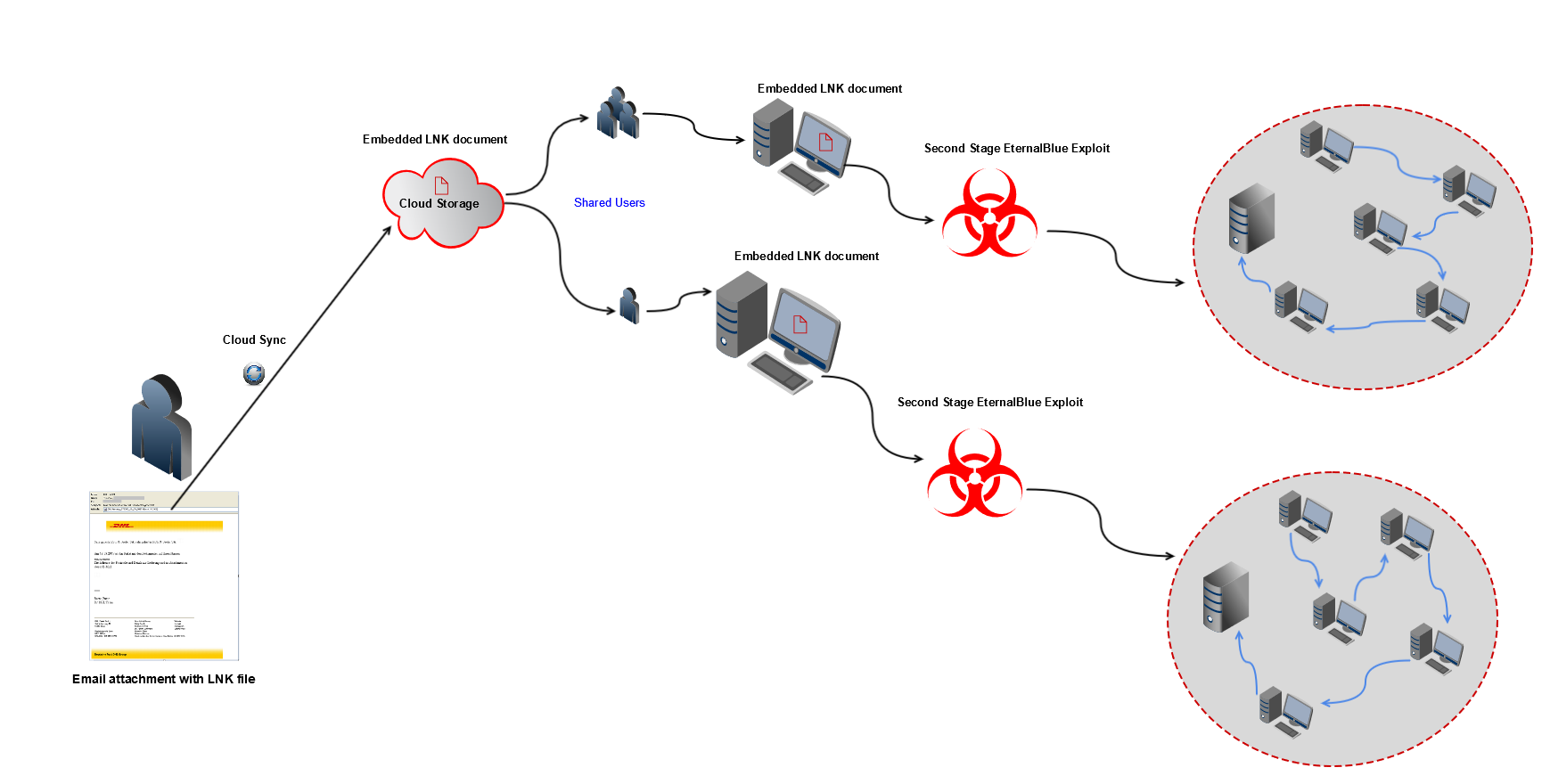
Figure 3: Depiction of the EternalBlue attack spreading internally
An additional aspect of the attack in collaborative environments is that the attachment itself can become the start of a CloudPhishing fanout whereby the initial recipient shares the attack attachment. Their peers then see the attachment and open it, assuming the initial recipient has created it.
See Figure 4 for the visual depiction of the protection using Netskope threat protection from the EternalBlue wormed infection.
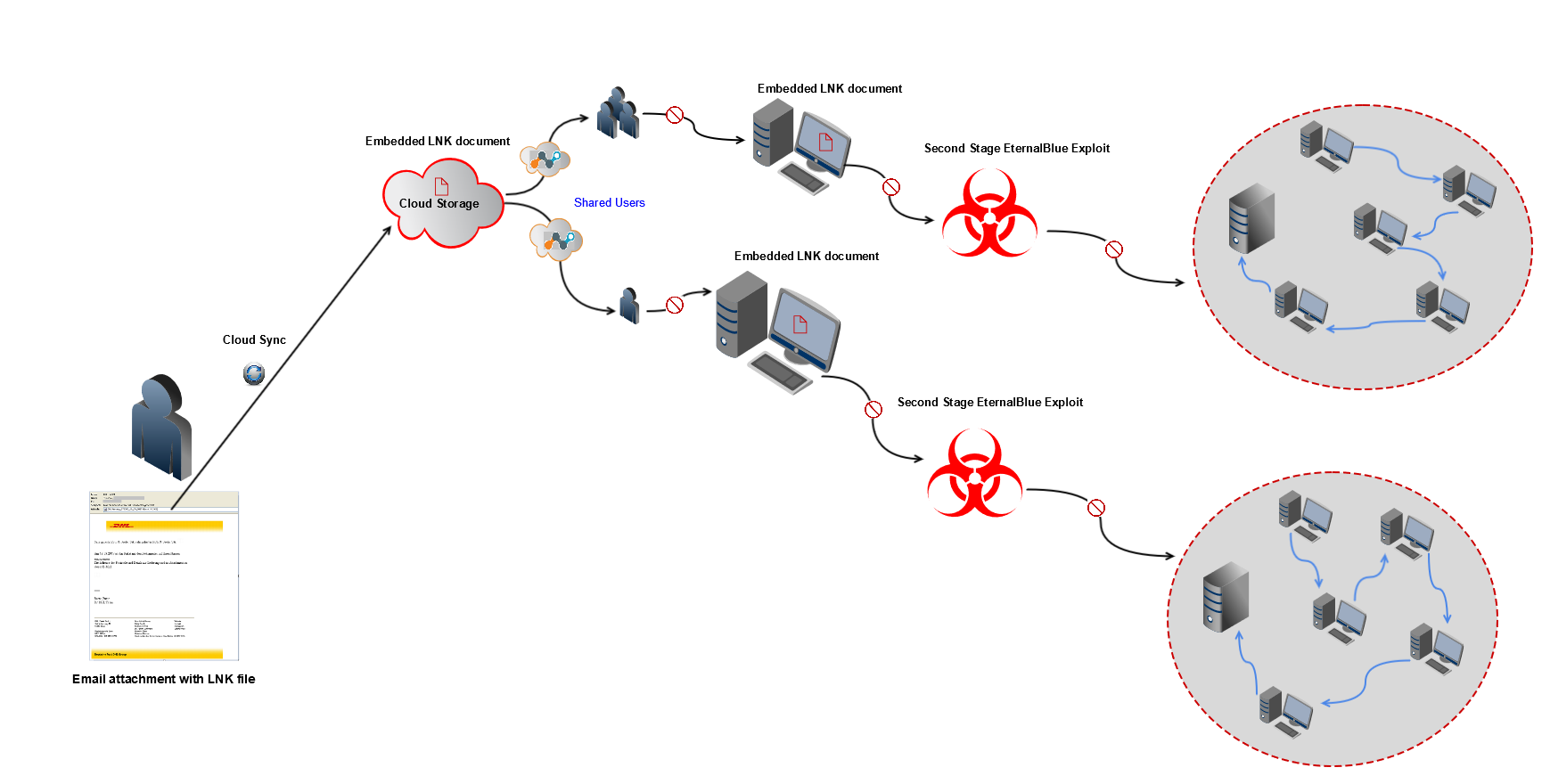
Figure 4: Early Killchain Protection using Netskope Threat Protection
Overview of the EternalBlue SMB Exploit
The EternalBlue SMB exploit was used by Wannacry, and is part of a toolkit dump release said to originate from “The Equation Group”. The exploit released by “The Shadow Brokers” earlier this year targets open SMB ports to leverage remote code execution by specifying malformed values during the Microsoft SMB NT Trans2 Request.
SMB is a file sharing protocol that provides shared access to files in a network. Since this is a widely adapted program, the vulnerability has a considerable impact. The vulnerability uses port 445 for exploit connection.
An excerpt of the configuration file of the EternalBlue SMB exploit from the dump is shown in Figure 5
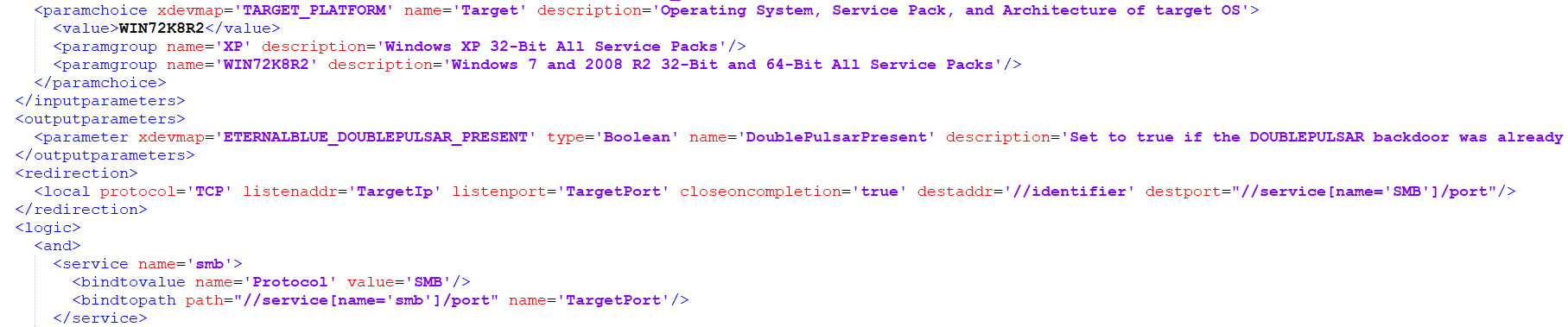
Figure 5: Configuration file of the EternalBlue SMB exploit
DoublePulsar is a Backdoor payload used by the EternalBlue exploit to download and install malware on the infected hosts.
The configuration file of the DoublePulsar payload is shown in Figure 6.
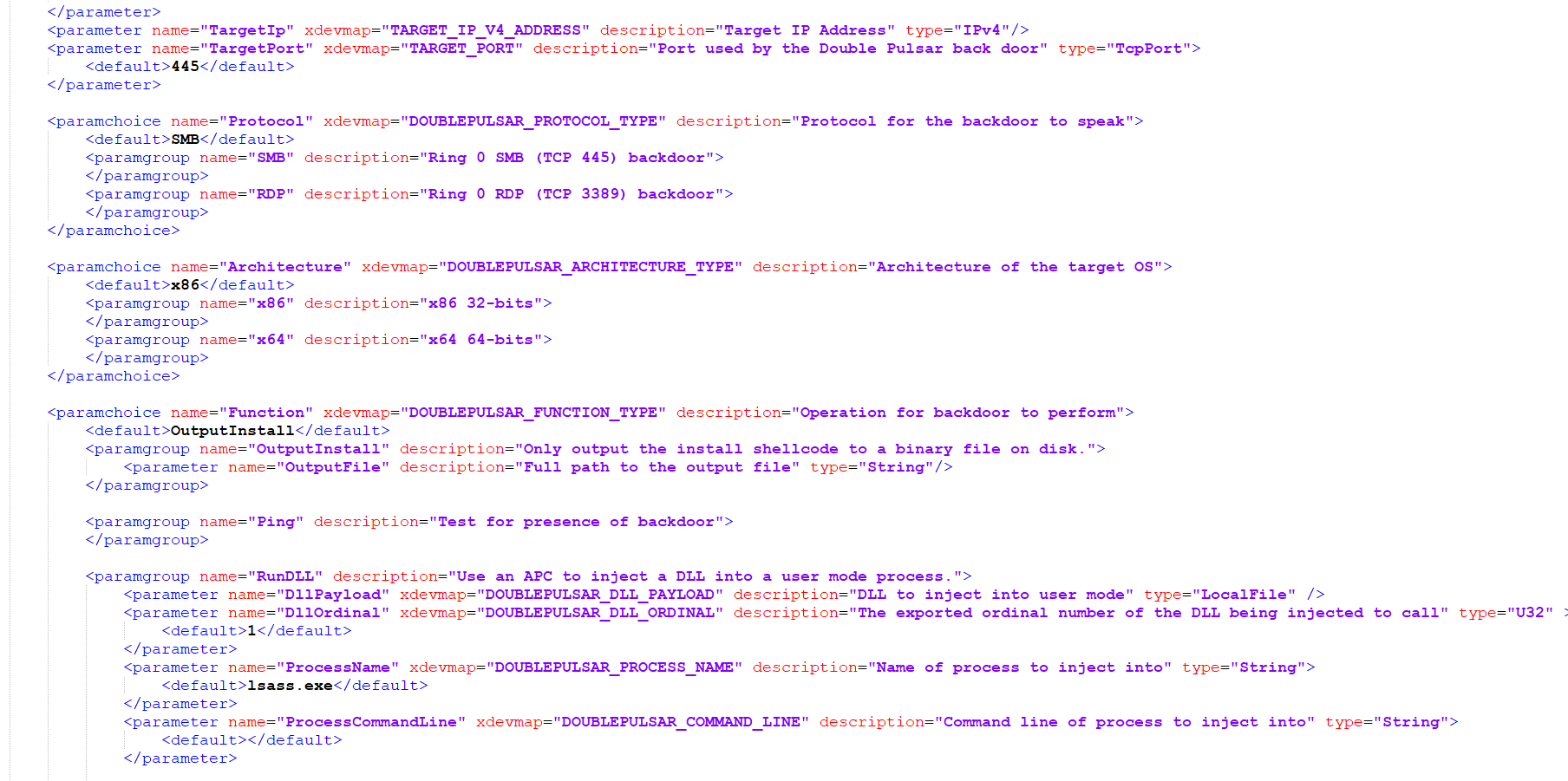
Figure 6: Configuration file of the DoublePulsar Payload
The installation of the malware using the SMB exploit is shown in Figure 7.
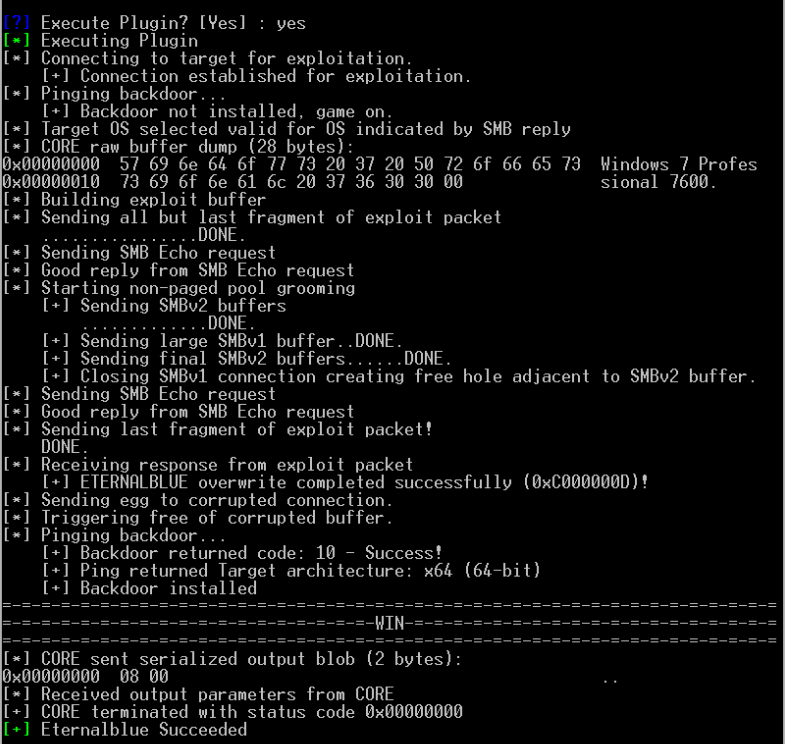
Figure 7: Installation of the payload using EternalBlue SMB exploit
A massive campaign blended with the EternalBlue exploit spread WannaCryptor ransomware across the world, infecting several systems and causing severe damage. Due to the widespread extent of such attacks, threat actors started to mix the exploit with existing malware. An estimated more than half a million devices with an SMB port open to the internet are potentially vulnerable if they have not yet patched for MS17-010. Microsoft published a patch for a number of exploits contained in the Shadow Broker’s dump as part of the March 2017 monthly security update MS17-010.
Conclusion
We have observed that the presence of embedded document files in a cloud storage and collaboration services possess a more significant threat to an enterprise environment since it arrives from a trusted source. Once an endpoint is compromised with the second stage payload like EternalBlue, it creates a wormed infection, leading all neighboring internal computers to be attacked via SMB from the newly compromised internal stepping stone system.
Such infections can potentially spread without any user intervention, leading to internal attacks that organizations may not be prepared for. The use of cloud services by enterprises, along with the implicit trust has lead to an increase in malware attacks and thus posing a new challenge for organizations. Netskope Threat Research Labs recommends security administrators to utilize a threat aware CASB that scans email traffic inline.
General Recommendations
Netskope recommends the following to combat cloud malware and threats:
- Detect and remediate cloud threats using a threat-aware CASB solution like Netskope and enforce policy on usage of unsanctioned services as well as unsanctioned instances of sanctioned cloud services
- Sample policies to enforce:
- Scan all uploads from unmanaged devices to sanctioned cloud applications for malware
- Scan all uploads from remote devices to sanctioned cloud applications for malware
- Scan all downloads from unsanctioned cloud applications for malware
- Scan all downloads from unsanctioned instances of sanctioned cloud applications for malware
- Enforce quarantine/block actions on malware detection to reduce user impact
- Block unsanctioned instances of sanctioned or well known cloud apps, to prevent attackers from exploiting user trust in cloud. While this seems a little restrictive, it significantly reduces the risk of malware infiltration attempts via cloud.
- Enforce DLP policies to control files and data en route to or from your corporate environment
- Regularly back up and turn on versioning for critical content in cloud services.
- Enable the “View known file extensions” option on Windows machines.
- Warn users to avoid executing unsigned macros and macros from untrusted sources, unless they are very sure that the macros are benign.
- Whenever you receive a hyperlink, hover the mouse over it to ensure it’s legitimate destination link.
- Enterprise users should always keep their systems and antivirus updated with the latest releases and patches. Microsoft has released the following Security Update for MS17-010, Security Update for Microsoft Windows SMB Server (4013389)
- Disable SMB for the functions or departments not using it within an enterprise. Additional details can be found in the following Microsoft support article
- Administrators can also consider adding rules to specific firewall ports to prevent SMB traffic from leaving the corporate environment as mentioned in the following Microsoft article.
- Administrators can also consider to improve credential protection for Microsoft Windows.
- Instruct users to avoid executing any file unless they are very sure that they are benign.
- Instruct users against opening untrusted attachments, regardless of their extensions or filenames.

















