With an average of more than 1,000 cloud services in use by enterprises, how do you triage your cloud security and streamline the process of applying compensating controls across so many cloud services? Netskope is built to give you the flexibility of safely enabling the cloud services you wish without forcing you into a coarse-grained allow or block decision for all unsanctioned cloud services, so-called “shadow IT.” Let’s walk through a four-step triage process that you can follow to get on the path towards safe cloud enablement.
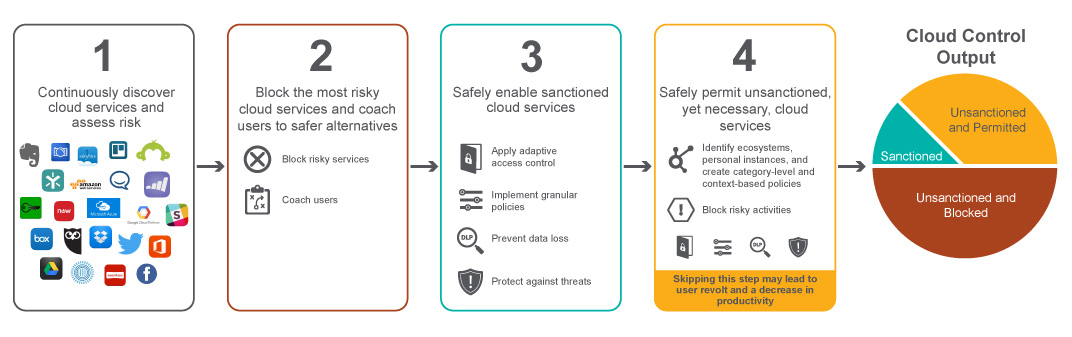
Step 1 – Continuous discovery of cloud services in use and assessing risk
Advanced discovery is often the starting point for any cloud security strategy. Understanding what cloud services are in use and assessing risk is an important first step. According to a recent Netskope Cloud Report, an average of more than 1,000 cloud services are in use by enterprises. Within that count, there are typically 40 to 50 cloud services that are sanctioned by IT. That means that 950 (95%) of them are unsanctioned and carry the Shadow IT moniker. A cloud access security broker (CASB) like Netskope can help you discover all these cloud services and assess risk by rating each of the cloud services using more than 50 different criteria, much of which is modeled after the Cloud Security Alliance’s Cloud Controls Matrix.
Step 2 – Block the riskiest cloud services and coach users to safer alternatives
Once you assess the risk of cloud services, there may be some that you simply want to block outright. We recommend that you start with either the riskiest cloud services or the cloud services that score the lowest based on the measured criteria. You may decide to deploy a CASB or your existing firewall to block the riskiest cloud services. You should also include a workflow that coaches users to use a safer alternative cloud service instead of the risky one they are attempting to use. Some enterprises may opt to skip this step and go to step four in an attempt to safely enable all cloud services and not block anything outright.
Step 3 – Safely enable sanctioned cloud services
The next step after understanding your cloud usage and assessing your risk is to start the process of mitigating risk by implementing compensating controls. This step focuses on securing cloud services such as Office 365, Salesforce, and ServiceNow that you have sanctioned or at least have administrative access and control over. A CASB like Netskope can help by providing a number of cloud security services such as access control, granular policies, cloud DLP, and threat protection, which will help by adding an extra layer of security to services that you have sanctioned.
Step 4 – Safely permit unsanctioned, yet necessary cloud services
Now that you have discovered the cloud services in use and assessed their risk, safely enabled the sanctioned, and blocked the riskiest, the final step is to safely enable the remaining unsanctioned cloud services. This is the most difficult step for a number of reasons. First, in order to safely enable unsanctioned cloud services with adaptive access control, granular policies, cloud DLP, and cloud threat protection, you need to understand what risky activities are taking place. If you don’t have administrative access to a cloud service’s published APIs then you will be blind to activity- and data-level cloud usage details. First-generation CASBs can only see coarse-grained bytes up and bytes down details for unsanctioned cloud services and can’t identify activities such as login, share, post, etc. — nor can they identify whether the data being transferred is sensitive or not. The result is that first-generation CASBs force users into a coarse-grained allow vs. block decision for unsanctioned cloud services. On the other hand, Netskope uniquely decodes granular activity- and data-level cloud usage details for unsanctioned cloud services even if they don’t have published APIs. This results in safe enablement of the cloud service with granular policy control (for example, “allow sharing between the same business unit” or “block downloads to personal mobile devices”) instead of being forced into a difficult allow or block decision.
The other challenge is that unsanctioned services often represent more than 95% of the cloud services in use. How do you put in compensating controls for hundreds or potentially thousands of cloud services? Netskope guidance is to start by identifying the discovered cloud services that are at risk for sensitive data loss and employ category-level DLP policies. Categories such as cloud storage, social media, collaboration, HR, and Finance/Accounting can represent hundreds of cloud services running in your environment that are at risk for sensitive data loss. Netskope is the only CASB that supports cloud DLP for the hundreds of unsanctioned cloud services that are at risk for sensitive data loss. Netskope also supports granular policies for thousands of unsanctioned cloud services. Netskope also uniquely supports category-level policies enabling you to cover a large number of cloud services with minimal policy administration overhead.
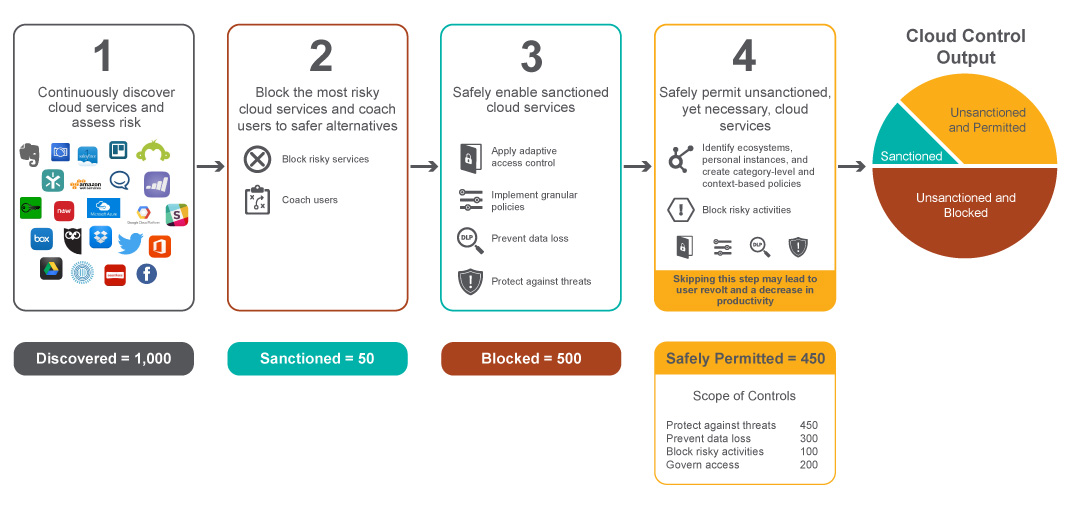
Real-world example
Let’s take a look at a real-world example – a large financial services organization followed the four steps to triaging cloud security.




 Retour
Retour 















 Lire le blog
Lire le blog