There are many things that characterize good security hygiene. One obvious aspect is clearly defined trust boundaries and secure connectivity requirements. Allowing an unmanaged and untrusted device to be directly plugged into a trusted network would significantly violate one of the core tenets of the Zero Trust principle.
The truth is, enabling secure connectivity on mobile devices cannot be done in an ad-hoc manner, it must follow a best practice approach in order to be successful. While many internet security and remote access solutions offer a self-service workflow (e.g., go to the App/Play Store, download the client, authenticate, and connect), this can lead to potential risks. Sensitive data could end up on an untrusted and unmanaged device, which could get lost, stolen, or be used for unauthorized access and data exfiltration. This poses a real risk for both internal and SAAS applications, and it raises doubts about the effectiveness of the data protection perimeter.
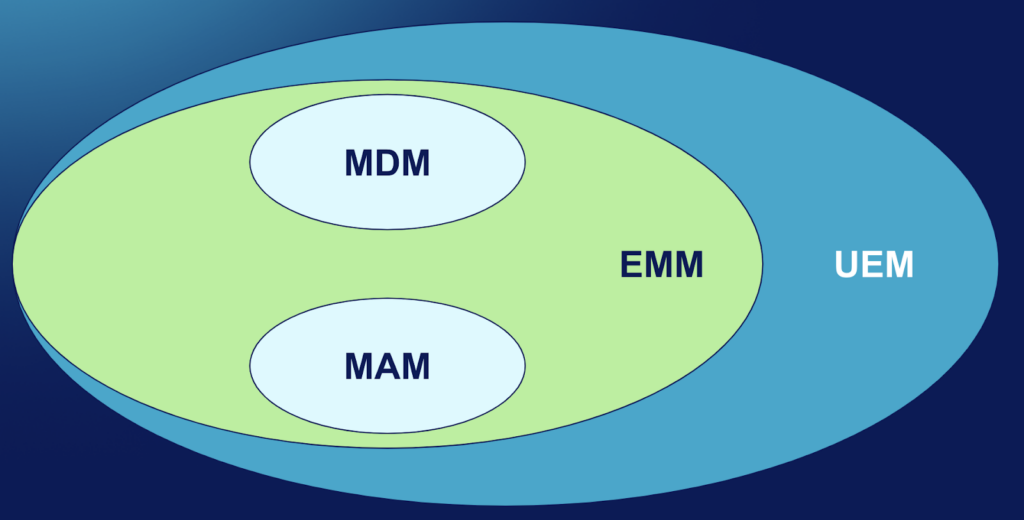
To address these challenges, the recommended best practice approach is to use a centralized management system for mobile management. There are many different specialized solutions on the market. The most commonly used platform types include:
- MDM (Mobile Device Management): Historically focused on corporate-owned mobile assets.
- EMM (Enterprise Mobility Management): Addresses all enterprise mobile use cases, including company-owned and personal devices.
- UEM (Unified Enterprise Management): Comprehensive platforms that manage both desktop and mobile devices.
- MAM (Mobile Application Management): Targets app management on both managed and unmanaged devices.
Among these, MDM has been in the market for the longest time and can serve as the primary term, although some may use EMM and UEM for more specific contexts.
The market is divided between major UEM players like Microsoft Intune, Vmware Workspace One, Ivanti Neurons, and many smaller niche players that focus on specific use cases or verticals. MAM solutions are often associated with mobile app manufacturers. For instance, Microsoft Intune serves as a MAM for Office 365 mobile apps and 100+ third-party apps integrated with the Intune SDK. Salesforce also has its own MAM capabilities within Salesforce App.
Another vital part of the ecosystem is the management tools provided by device manufacturers to control device and app inventory for corporate-owned devices and automate enrollment processes. Examples include Apple’s Business Manager (ABM) and School Manager (ASM), as well as Google’s integration with various device manufacturers, such as Samsung Knox. As the company is making mobile device purchases, its serial number gets tracked by the tools mentioned above, and the device gets enrolled into MDM at the time of initial activation. Personal devices can also be enrolled to MDM – this would require manual user action and an explicit consent.
Depending on the ownership type, MDMs get vastly different controls over the enrolled device. Overall, device enrollment and its security and privacy consequences are worth a greater review with breakdown per platform – that would be a separate post.
Let’s jump forward and imagine the device is already enrolled in MDM, what it would really mean in terms of security controls? What does a Data Protection perimeter look like?
Netskope platform would provide secure connectivity to Web, SAAS and private Apps enforcing embedded threat and data protection controls described here. All external communications between managed apps and the external world would be handled by Netskope.
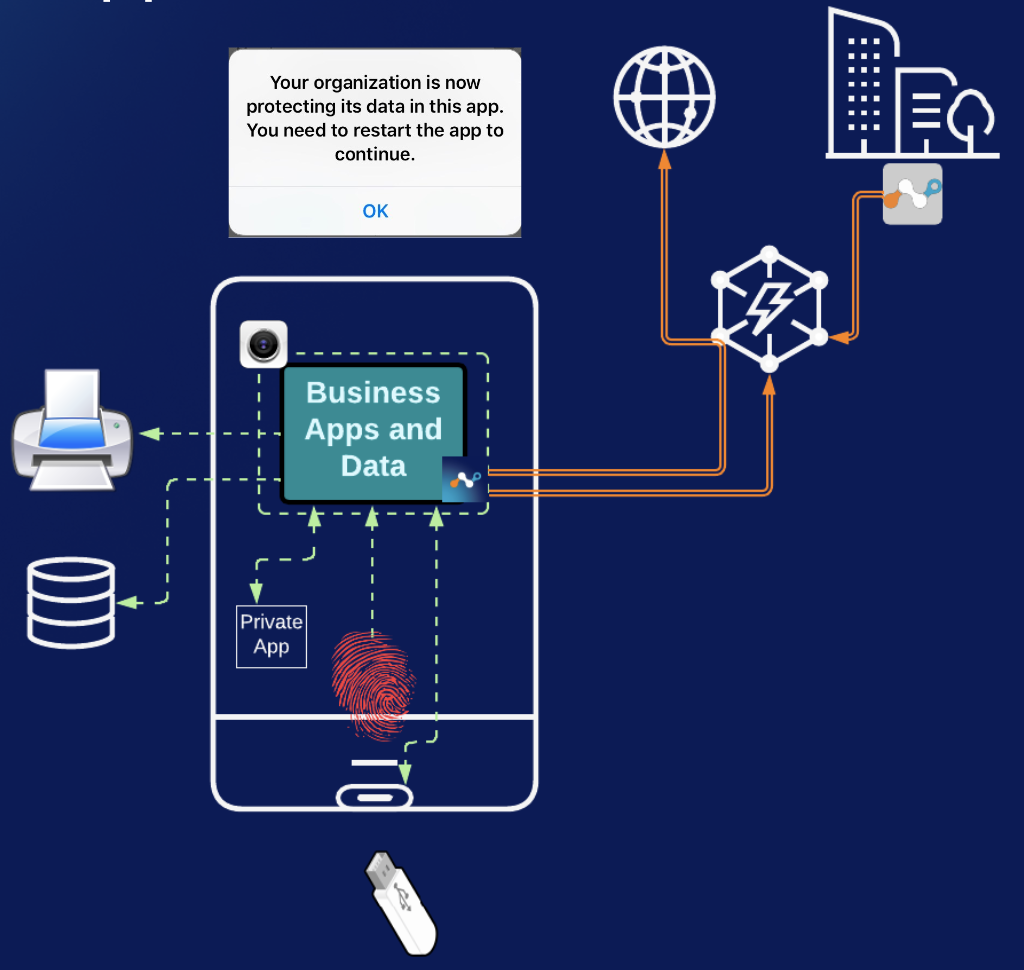
MDM and MAM platforms take care of enforcing device and data restriction controls on the device itself. This ensures that data remains within a defined trusted boundary, which could be the entire device or a managed part of it. Such controls include restricting abilities like sharing, opening in unmanaged apps, leveraging the clipboard, printing and many others.
This writeup only scratches the surface of how the overall Netskope for Mobile solution looks. Stay tuned for more content here and let me know if you have comments & questions!




 Voltar
Voltar


























 Leia o Blog
Leia o Blog