Summary
In the summer of 2020, there was a big, short-lived spike in malicious Office documents. The Emotet crew had been quiet in the spring and began leveraging their botnet to send extremely convincing phishing emails to their victims, often with a link to download an invoice or other document from a popular cloud service. Those documents contained malicious code that installed backdoors, ransomware, bankers, and other malware on unsuspecting victims’ computers. This blog post looks back at malicious Office document trends in 2020, with a preview of what is to come in 2021.
This blog post accompanies the release of the February 2021 Cloud and Threat Report, which analyzes 2020’s most interesting trends in enterprise cloud and web security. In addition to highlighting the increase in cloud app usage, the Cloud Threat Report also highlights four other noteworthy trends from 2020:
- Cloud app use continues to rise, with a 20% increase led by collaboration and consumer apps
- Cloud-delivered malware continues to increase, now representing 61% of all malware.
- Cloud phishing continues to increase, with 13% of phishing campaigns hosted in the cloud and 33% targeting cloud app credentials.
- Personal app usage in the enterprise continues to increase, with 83% of users accessing personal apps from managed devices.
The calm
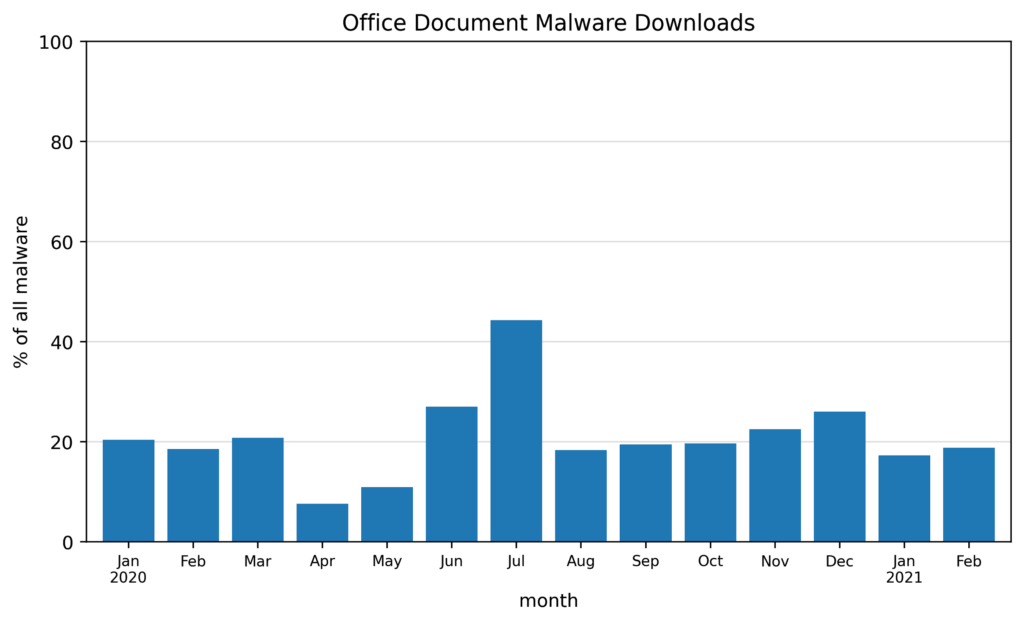
The February 2021 Cloud and Threat Report examines trends in malicious Office documents at a quarterly granularity. In this blog post, we take a more granular look at a broader dataset. The chart below shows the percentage of malware downloads detected by the Netskope Security Cloud Platform that were Office documents. For the first three months of the year, Office documents represented nearly 20% of all malware downloads. This changed in April and May, in the early days of the COVID-19 pandemic, when the Emotet crew and other threat actors were relatively quiet. During that time, only 10% of malware downloads were Office documents.
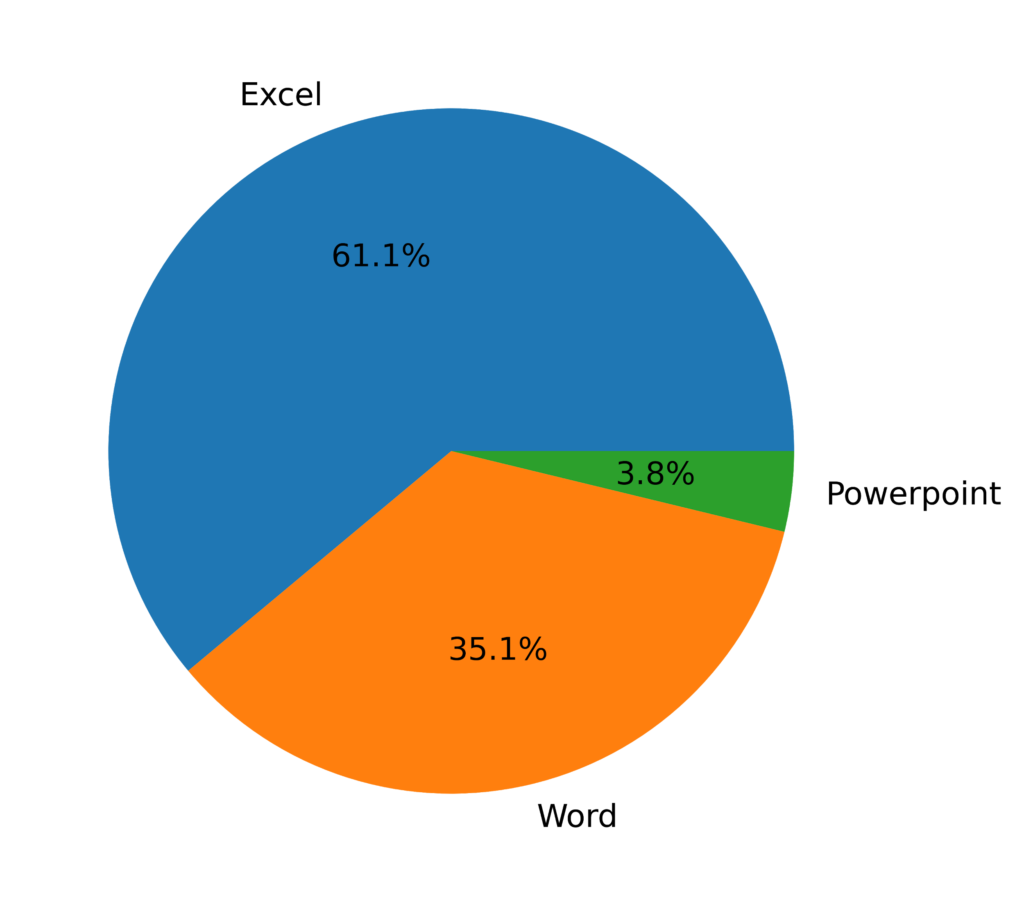
Throughout the year, the Office document format most favored by cybercriminals was the Excel spreadsheet, representing 61.1% of all the malicious office documents in 2020. Excel is most popular because it provides rich scripting capabilities that threat actors abuse for malicious purposes. Word documents were the second most popular, followed by a small selection of Powerpoint documents.
The storm
Everything changed over the summer. The Emotet crew began leveraging their extensive botnet to send phishing emails to their victims, often with a link to download an invoice or similar document from a popular cloud service. The documents contained malicious code that installed backdoors, ransomware, bankers, and other malware on unsuspecting victims’ computers. The malicious code typically took the form of an XSL script or VBA script that would construct and execute a second script. That second script would download the next stage payload. This was an evasion technique designed to bypass detection by traditional signature-based malware detectors at the time.
At its peak in July, malicious Office documents represented 44% of all malware downloads. Following the summertime spike, Office docs returned to the same levels as the beginning of the year before increasing into December. The December spike was driven primarily by Dridex, the second most popular crimeware family, which also favors Office documents as a delivery mechanism.
The aftermath
In January 2021, a multinational effort that included Europol, the FBI, and the UK National Crime Agency, as well as agencies from Canada, France, Germany, Lithuania, the Netherlands, and Ukraine, teamed up to take down the Emotet botnet. January saw a dropoff from the December spike, but through February, malicious Office documents still represent nearly 20% of all malware downloads. What is going on? While the Emotet botnet has been taken down, the techniques used to craft evasive malicious Office documents remain available to other groups, like Dridex, that continue to use them for malware delivery.
Conclusions
There were a couple of spikes in malicious Office documents in 2020, a summertime spike driven by Emotet and an end-of-year spike from Dridex. Despite the Emotet takedown, malicious Office documents are still a popular tool used by cybercriminals to deliver malware to their victims. Malicious Office documents currently account for 20% of all malware downloads, which we expect to continue through 2021.




 Voltar
Voltar
















 Leia o Blog
Leia o Blog