After a Summer break, our Cloud Threats Memo is back!
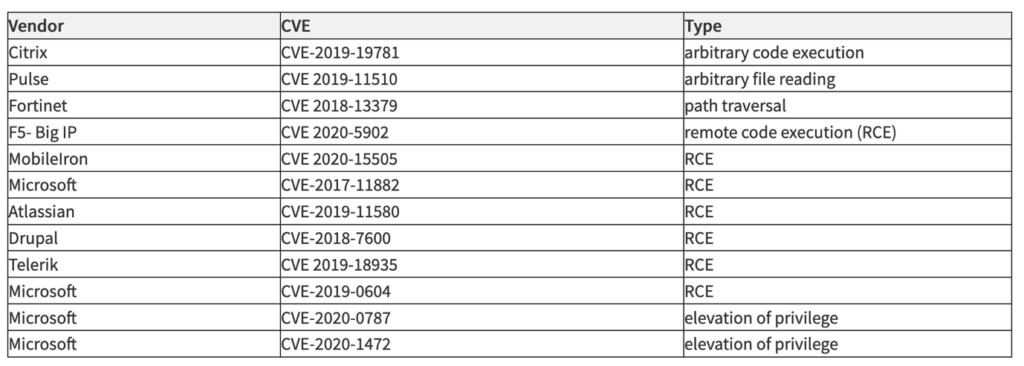
The U.S. Cybersecurity and Infrastructure Security Agency (CISA), the Australian Cyber Security Centre (ACSC), the United Kingdom’s National Cyber Security Centre (NCSC), and the U.S. Federal Bureau of Investigation (FBI) have recently published a joint advisory providing details on the top 30 vulnerabilities routinely exploited by malicious cyber actors in 2020 and those widely exploited in 2021 so far. The findings are not particularly surprising for us, in a previous memo we already illustrated the risks of the shift to remote working deriving from the unprecedented wave of severe vulnerabilities that have hit traditional remote access technologies, and this advisory just confirms the same figures: the top three routinely exploited vulnerabilities according to the CISA, the ACSC, the NCSC, and the FBI concern traditional remote access technologies. Along with three VPN technologies, the list contains a number of internet-facing technologies (application servers and load balancers) that have been regularly exploited by criminals.
Unsurprisingly this trend is continuing in 2021.
Providing access to a corporate network, these vulnerabilities can be equally exploited by ransomware gangs and APT actors. Additionally, some of them date back more than three years, so the systematic exploitation of these vulnerabilities has allowed the so-called initial access brokers to accumulate a trove of compromised credentials that they then outsource to cybercriminals or state-sponsored actors.
Providing a Zero Trust alternative to remote access technologies and exposed services.
Netskope Private Access allows you to publish resources in a simple and secure manner providing a Zero Trust alternative to legacy remote access technologies and preventing the direct exposure of services like SMB, RDP, SSH, or even on-prem Exchange and Sharepoint. It is possible to publish and segment virtually any application located in a local data center, as well as in a private or public cloud, without opening any inbound service that can be probed by threat actors. There is also no need for any on-prem hardware device to install, patch, and maintain, which avoids scalability issues and performance bottlenecks. Finally, a check on the security posture of the endpoint is enforced before accessing the target application. A smarter and more secure way to provide remote connectivity in the “new normal.”
Stay Safe!




 Voltar
Voltar
















 Leia o Blog
Leia o Blog