The total number of phishing attacks doubled in 2020, with phishing for cloud credentials, specifically SaaS and webmail app credentials, accounting for nearly a third of the targets of phishing campaigns. Over the same period, we saw cybercriminals hosting 13% of their baits in cloud apps. This blog post summarizes the top phishing trends from 2020 and looks forward at what to expect for the rest of 2021.
This blog post accompanies the release of the February 2021 Cloud and Threat Report, which analyzes 2020’s most interesting trends in enterprise cloud and web security. In addition to highlighting personal app usage, the Cloud Threat Report also highlights four other trends:
- Cloud app use continues to rise, with a 20% increase led by collaboration and consumer apps
- Malicious Office documents increased dramatically, now representing 27% of all malware downloads.
- Personal app usage in the enterprise continues to increase, with 83% of users accessing personal apps from managed devices.
- Cloud-delivered malware continues to increase, now representing 61% of all malware.
Cloud phishing targets
The total number of phishing attacks doubled over the course of the year in 2020, according to the 4th Quarter 2020 Phishing Activity Trends Report from the Anti-Phishing Working Group (APWG). In October 2020, APWG reported a new record for the highest number of new phishing attacks seen in one month.
At the same time, the percentage of the total phishing attacks targeting cloud app credentials, specifically SaaS and webmail credentials, fell to 22.2%. As shown in the figure below, this is the lowest percentage since 2018. This relative decrease compared to other phishing targets was driven by an increase in phishing campaigns targeting financial institutions, payment providers, online retailers, and eCommerce platforms.
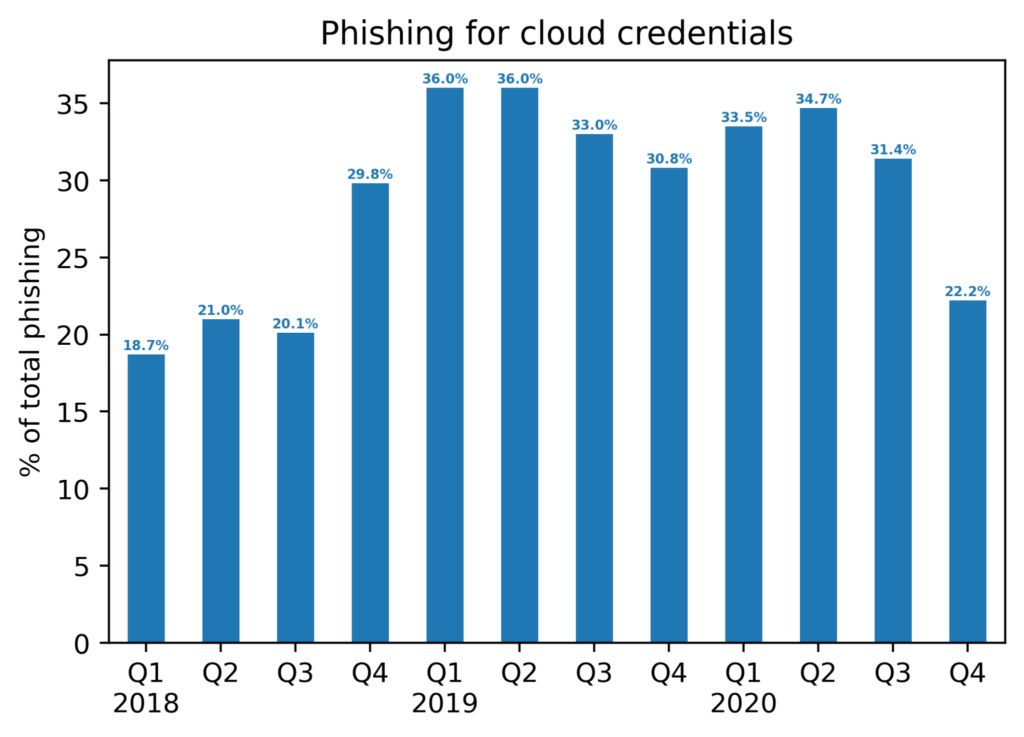
Despite the marked decrease in SaaS and webmail credentials as a percentage of the total phishing attack targets, it remains in the second place position behind financial institutions (22.5%) and ahead of payment providers (15.2%). We expect SaaS and webmail will continue to remain among the top two phishing targets along with financial institutions for the foreseeable future and will continue to account for around one-quarter of all phishing attacks. The primary drivers behind this prediction are:
- There are a lot of potential targets. SaaS and webmail apps are popular among both consumers and enterprises.
- There is a lot of valuable data hosted in SaaS and webmail apps. This data can be leveraged for extortion, sold on the black market, or leveraged for broader attacks.
- SaaS and webmail platforms themselves can be abused for other purposes, such as hosting illicit content or launching broader cyber attacks. Phished accounts can be used directly by the phishers or sold on the black market.
Phishing from cloud apps
In 2020, we saw 13% of all phishing baits hosted directly in SaaS applications on the web. There are two popular types of SaaS applications abused to host phishing baits: app hosting providers and online forms.
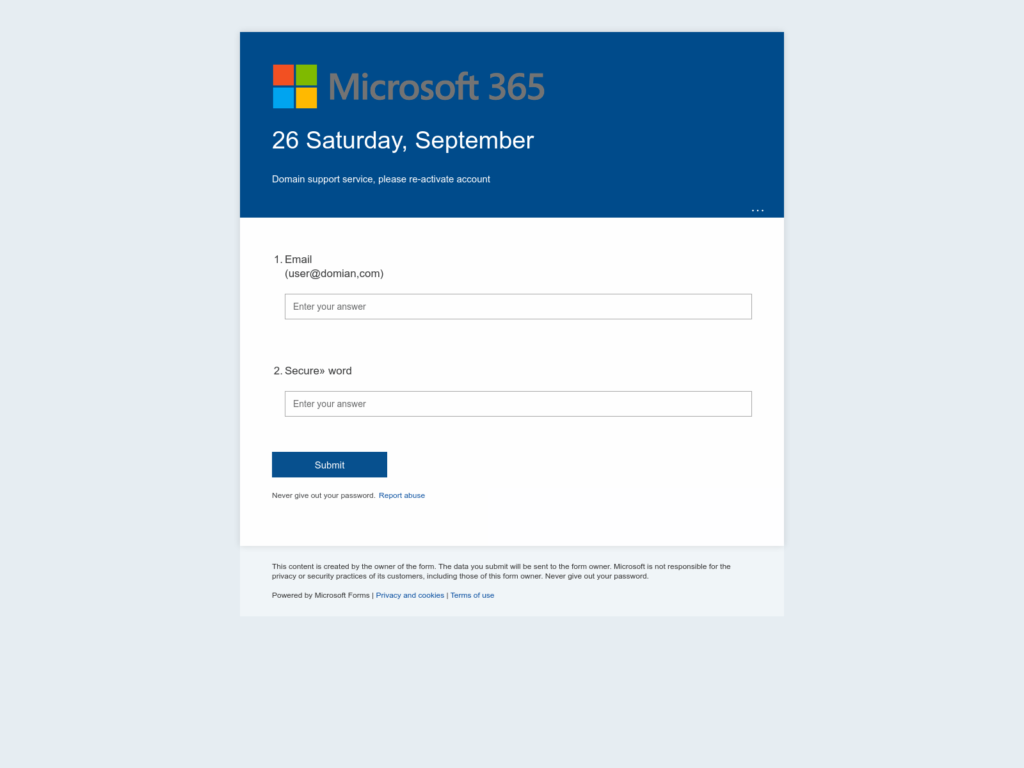
In this first example, the attacker created a low-effort Office 365 login form using Microsoft Forms. Aside from the logo and color scheme, there is little here in common with the actual login page. However, there are some advantages to this type of phishing attack — the attacker abuses a Microsoft service to phish for Microsoft credentials. The victim will see a login page to Office 365 hosted on an office.com subdomain (forms.office.com) with a certificate issued by DigiCert to Microsoft. In other words, the onus is on the victim to notice the unusual aesthetic or the warning at the bottom of the page that warns not to share your password.
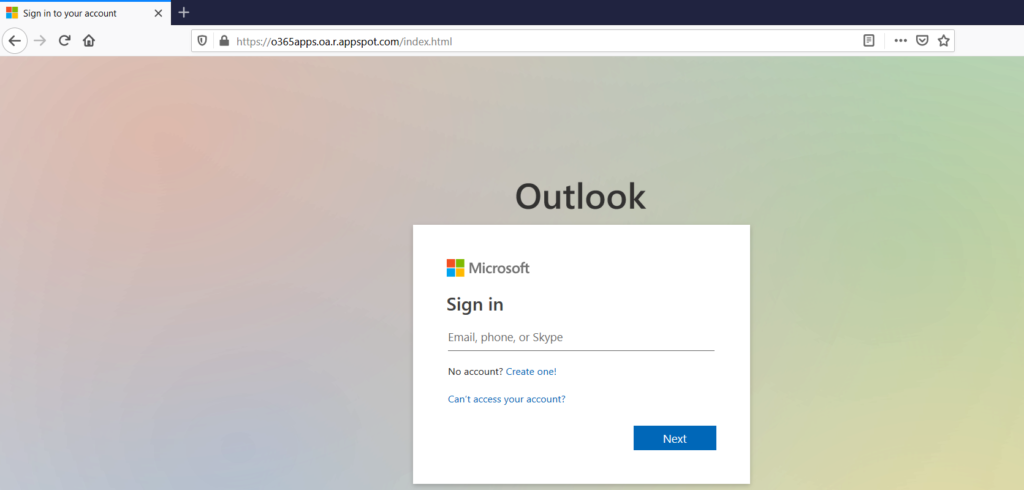
In this second example, the actual login page is a nearly perfect copy of the actual Microsoft login page. This phishing campaign was created in Google App Engine. Here, the onus is on the victim to notice that the page is a user-generated page hosted in a Google service. This type of hosting of phishing pages is common on phishing-as-a-service platforms where templates for creating phishing pages can be shared easily.
Predictions
In 2021, we expect SaaS and webmail credentials to remain in the top two targets of phishing attacks. At the same time, we expect the percentage of phishing baits hosted in cloud apps to increase as more attackers begin to abuse cloud services for phishing. Finally, we expect to see an increase in attackers abusing OAuth workflows in their phishing attacks to circumvent MFA and fly under the radar.
The analysis presented in this blog post is based on anonymized usage data collected by the Netskope Security Cloud platform relating to a subset of Netskope customers with prior authorization.

















