Introduction
The ransomware landscape has dramatically grown since inception. Ransomware typically propagates via email, exploit kits, removable drives or external network shares. Ransomware authors regularly deploy several tactics to make the infection scale larger and also use hard-to-recover encrypted files to ensure that user pays the ransom.
Virlock is one such special case of ransomware that encrypts files and also infects them, thereby making it a polymorphic file infector ransomware. As a result, any user who subsequently opens the infected file also becomes infected, causing all the files to become to encrypted and infected.
Virlock ransomware potentially exhibits a new propagation vector with a combination of ransomware and file infection characteristics that could be detrimental for an enterprise customer. This blog will talk about Virlock and the new propagation vector demonstrating a case where ransomware in an enterprise enables cloud storage apps to deliver malware on the fly, a real-world example of the malware fan-out effect. This infection amplification requires adequate security scanning on all resources that also include cloud shares.
How Virlock Works
The latest variant of Virlock ransomware typically arrives via external shares or USB sticks. In some cases Virlock was also observed bundled with other malware. Once the malicious file is executed, Virlock drops three randomly named executables with different hashes in randomly named folders. These files are polymorphic and therefore carry different hashes each time. Two of these executables infect other files on the victim’s machine. They also create run entries in HKEY_CURRENT_USER and HKEY_LOCAL_MACHINE so that they are launched each time the operating system boots up. The third executable file registers itself as a service.
Malicious File
MD5 – 28E8B1E88CC8AA33C5AE49299C24A460
Dropped Files
OoQYwkQI.exe – DF0B3DD3E412EF5373372EA207577C00
pWgooMEg.exe – DE2297B150DA6785A301F690C909F96D
UqMsIwoY.exe – F0286F192D8E0A58F19FC887AAA8B2C0
Virlock disables the Task Manager and Registry editor, preventing the user from manually identifying and removing the running process and entries created by Virlock. Virlock also changes the registry settings to not show the hidden files, hide known file extensions, and to disable User Access Control (UAC).
Registry Changes
Do not Show Hidden Files
Registry Key: [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced]
Value Name: Hidden
Value Data: 2
Hide Known File Extensions
Registry Key: [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced]
Value Name: HideFileExt
Value Data: 1
Disable UAC
Registry Key: [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System]
Value Name: EnableLUA
Value Data: 0
The Virlock variant we analyzed targets files with the following extensions and encrypts them:
File Extension List
.exe, .doc, .xls, .zip, .rar, .pdf, .ppt, .mdb, .mp3, .mpg, .png, .gif, .bmp, .p12, .cer, .psd, .crt, .pem, .pfx, .p12, .p7b, .wma, .jpg, .jpeg
For the files that are not “.exe”, Virlock appends “.exe” to the original file name. As an example, hello-world.pdf would become hello-world.pdf.exe. Since the file extensions are hidden, the user will not notice this important change to the file name. Virlock excludes the files that contain \Program, \Temp and \Windows in their file path.
After completing all the malicious actions, Virlock displays a screen asking for a ransom as shown below in Figure 1:
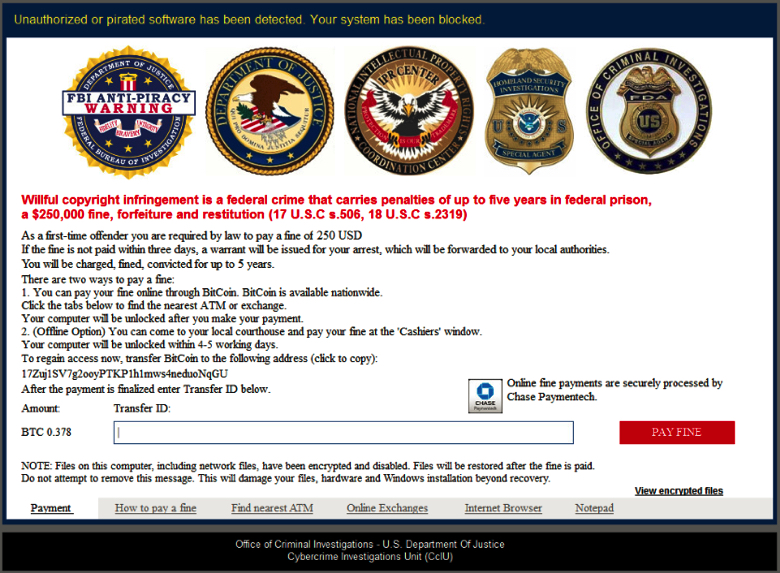
Figure 1: Screen displayed after the execution of Virlock
What is special about the new variant of Virlock?
Virlock stands out as a unique family of ransomware that not only encrypts files but converts them into a polymorphic file infector. An infected Virlock file contains polymorphic code, malware code and embedded clean code. Figure 2 shows a representation of an infected Virlock file.
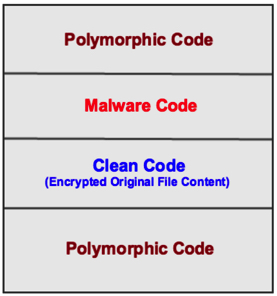
Figure 2: Representative structure of a Virlock-infected file
An excerpt of a file infected from our analysis is shown in Figure 3. We observed that the malware code was mostly similar with little variations in most of the Virlock variants.
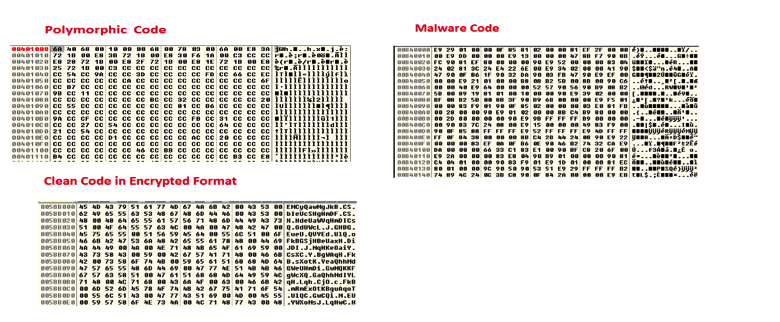
Figure 3 – Polymorphic, Malware, and Clean code in a Virlock-infected file
When the Virlock-infected file is shared with another user, and the new user executes that file, the entire process repeats and all the files belonging to the new user are encrypted. Each of these encrypted files is again a file infector and can infect other benign users.
Malware Fan-out with Virlock
- The Virlock file infector can become a dangerous weapon in the cloud context especially due to inadvertent spreading of infected files through cloud sync and share via cloud storage and collaboration apps. A single user infected with Virlock ransomware can infect the rest of the enterprise by way of existing shared/collaborated files
Demonstration
The following is a demonstration of the Malware Fan-out with Virlock. For demonstration purposes we are using the cloud storage app Box with two user machines “User A” and “User B”. The fan-out can occur with any cloud app and is not restricted to Box as mentioned in this blog.
(Please note: in the following figures, we show the file extensions for demonstration purposes but in reality, Virlock hides the file extensions).
Let’s say User A and User B are collaborating on a shared a folder with the name “Important” as shown in Figure 4.
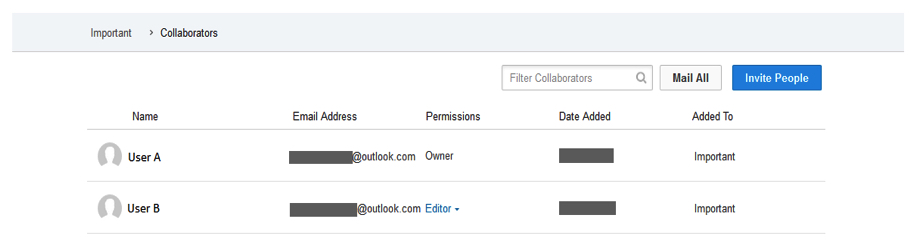
Figure 4: User A and User B collaborating on a folder called “Important”
This “Important” folder has few files that both User A and User B have synced on their respective machines as shown in Figure 5.
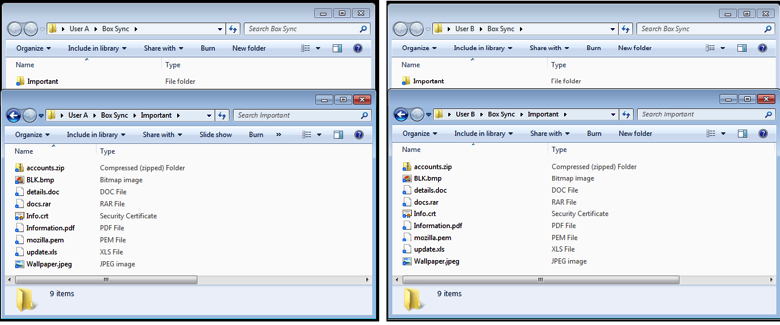
Figure 5: User A and User B with the collaborated folder named “Important” on their respective machines
User A gets infected with Virlock ransomware. User A’s files are all encrypted and turn in to Virlock infector files. As part of encrypting all the files on User A’s machine, the files within the Box Sync “Important” folder are also encrypted and turn into Virlock infector files as shown in Figure 6.
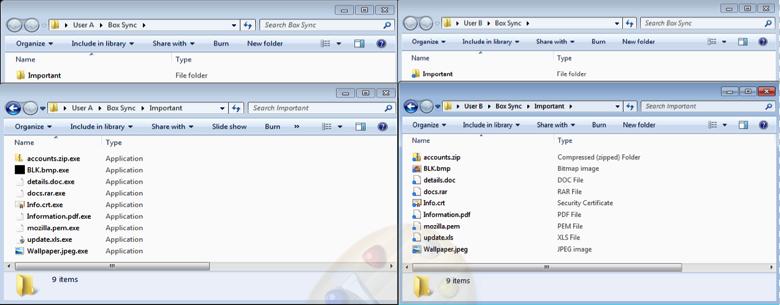
Figure 6 – Sync folder “Important” of User A after Virlock Infection. Also shown is the clean “Important” folder in User B machine.
The Box sync client on User A’s machine will sync the files to the cloud as shown in Figure 7.
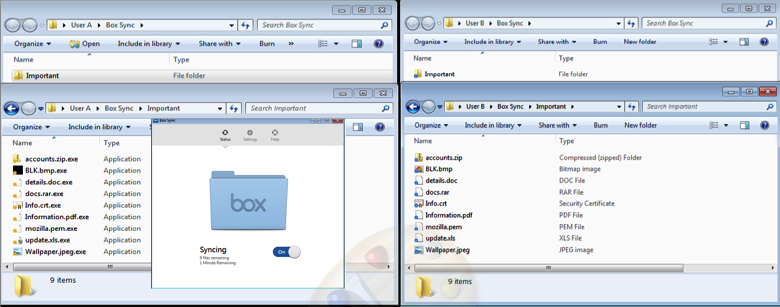
Figure 7: Virlock infected files of User A synced to Box
As the “Important” folder is also shared with User B, the files within “Important” folder are synced to User B’s machine Box sync folder as shown in Figure 8.
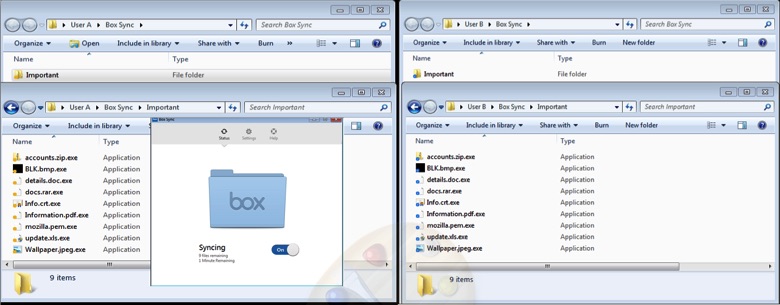
Figure 8: User A and User B Sync folder “Important” after Virlock infection
When User B clicks on any of the files in the “Important” folder, the Virlock file infector is executed and the rest of the files on User B’s machine are encrypted and also turn into Virlock file infectors.
The above scenario is not just limited to User A and User B and will extend to all the users of an enterprise who are collaborating with each other. Consider Figure 9 showing a User-File collaboration graph of a typical enterprise with Users (in black dots) and the Files (in blue dots). All the users within the red boundary might get infected with Virlock ransomware due to fan-out effect within minutes.
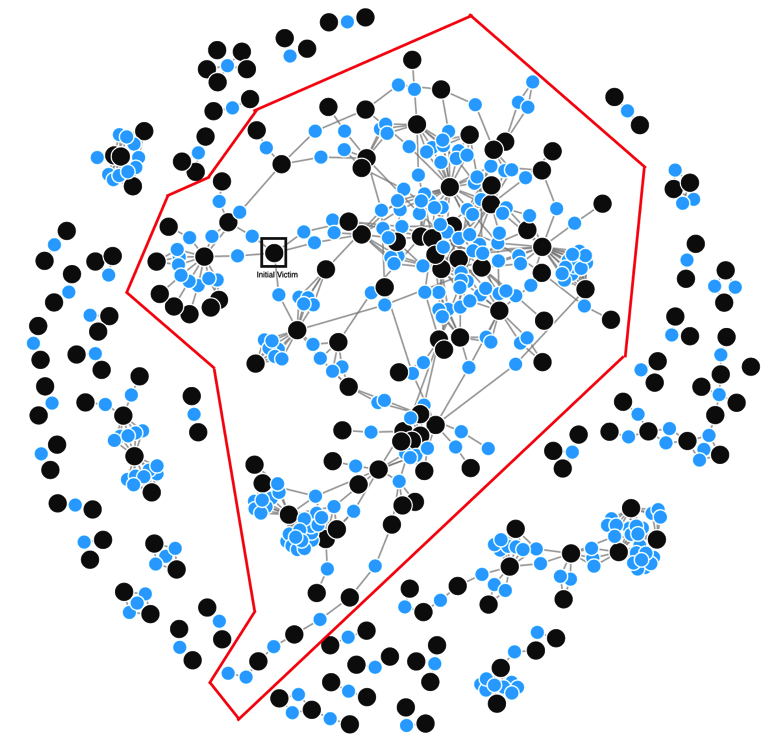
Figure 9: User-File collaboration graph in a typical enterprise and impact of Virlock Ransomware Fan-out
Detection, Protection & Best Practices
The Netskope Malware and Threat Protection solution provides full coverage for all variants of Virlock with the detection name “PE.PE.Gn.5”. The Virlock file infectors can be blocked from syncing to the cloud both from the original victim to the cloud and also for the cases where file infectors might be syncing from the cloud to a new user’s machine. Effectively stopping the fan-out as shown in Figure 10.
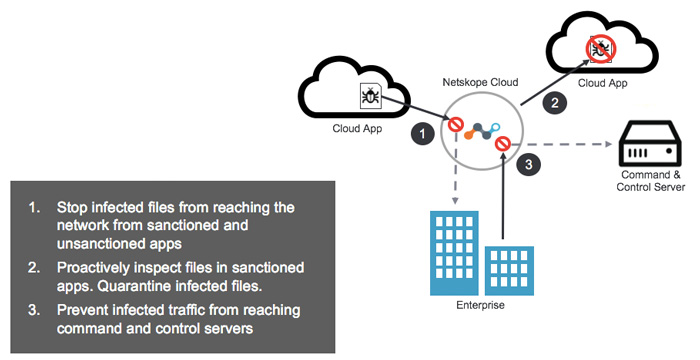
Figure 10: Netskope Malware and Threat Protection solution preventing Virlock file infector Fan-Out.
Netskope recommends the following best practices to enterprises in order to protect from ransomware threats:
- Administrators should regularly back up critical data in a cloud account.
- Administrators should apply the Netskope Malware and Threat Protection solution to Netskope Active Threat Protection so that threats such as Virlock ransomware can be blocked.
- On managed devices, Administrators should enable the option to view known file extension in windows
- Administrators should advise their uses to avoid executing any files with dual extensions unless they are very sure that the files are benign.
- Enterprise users should avoid opening untrusted email attachments regardless of their extension or filename.
- Enterprise users should always keep their systems and antivirus updated with the latest releases and patches.




 Zurück
Zurück 
















 Den Blog lesen
Den Blog lesen