Summary
Netskope Threat Labs is tracking phishing campaigns targeting customers of seven different financial institutions across North, Central, and Latin America, aiming to steal their credentials to make fraudulent transactions. Attackers are abusing the Royal Web Hosting company, which provides a free web hosting plan, to host the malicious pages. Furthermore, the majority of these pages are abusing Telegram channels to not only receive stolen data, but also to bypass two-factor authentication (2FA) in some cases.
We have also found more than 130 pages targeting Microsoft users, all of them in Spanish. In this blog post, we will show how this attack works and how to stay protected against this kind of phishing.
How it works
The diagram below illustrates how this attack works. A Telegram channel is used to receive the stolen username and password of banking or Microsoft 365 accounts. The channel is also used to bypass 2FA when enabled.
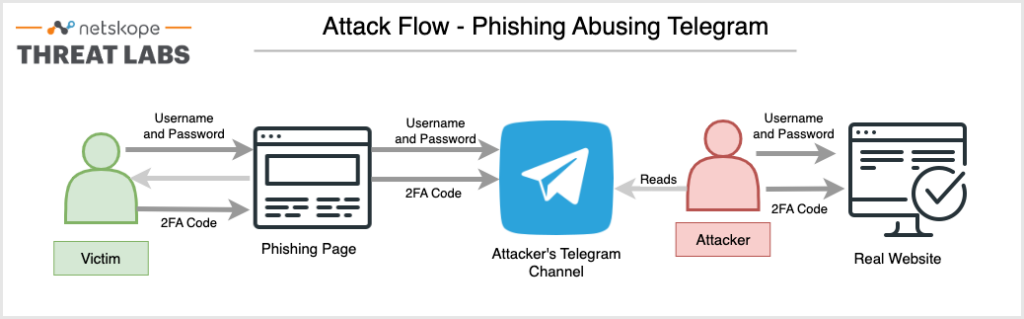
This is how it works:
- The phishing’s main page mimics the real website, which could be a financial institution or a Microsoft 365 login page;
- When the victim adds the credentials, they are automatically sent to the attacker’s Telegram channel;
- The attacker can then use this information to log into the real website. When 2FA is enabled, the real website would automatically send or ask for the code from the user’s mobile device;
- The phishing page then asks the user for a 2FA code, which is also sent to the attacker’s Telegram channel when added by the victim;
- With the stolen information, the attacker is able to successfully authenticate to the real website, allowing them to perform malicious transactions or access the victim’s personal email and data.
Example
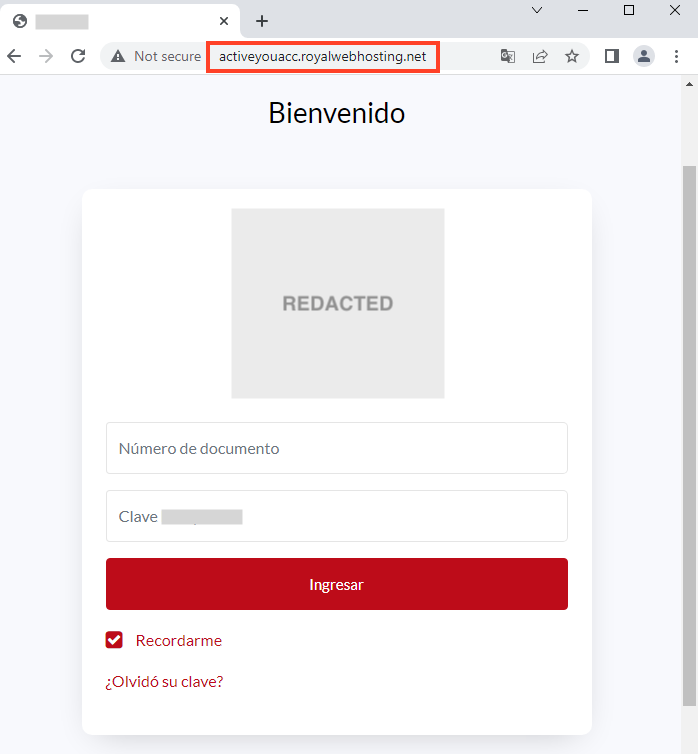
The main page shows a fake login page of a financial institution, asking for the victim’s document number and password.
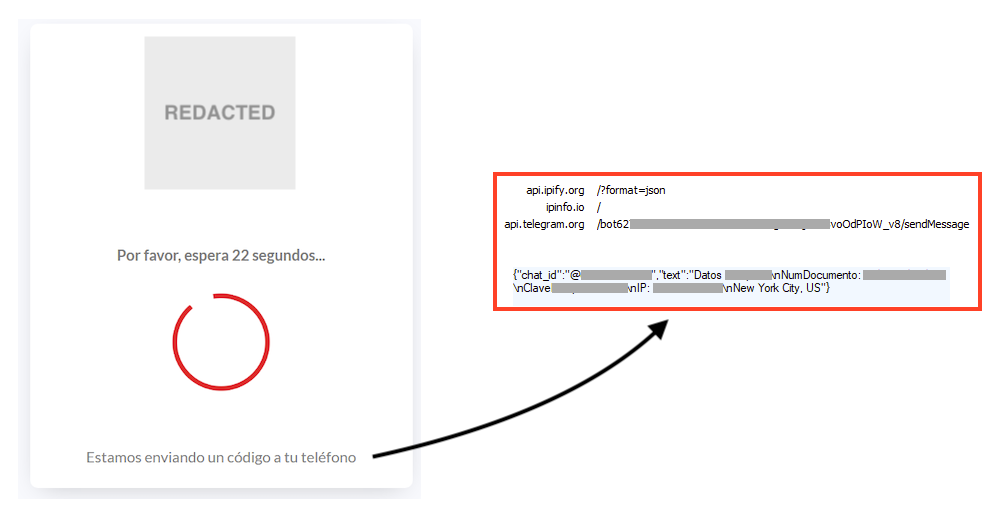
Once the victim enters the document number and the password in the phishing page, all the data is sent to a Telegram channel along with the victim’s IP address obtained through ipfy’s API. Meanwhile, the phishing page shows a countdown of 30 seconds, likely to provide attackers time to use the stolen information in the real website.
After the countdown, the phishing page asks the victim for a code that was sent to the mobile device, as an attempt to bypass the two-factor authentication. If the victim enters this code in the page, the data is sent back to the same Telegram channel, where the attacker could use the code to authenticate in the real website.
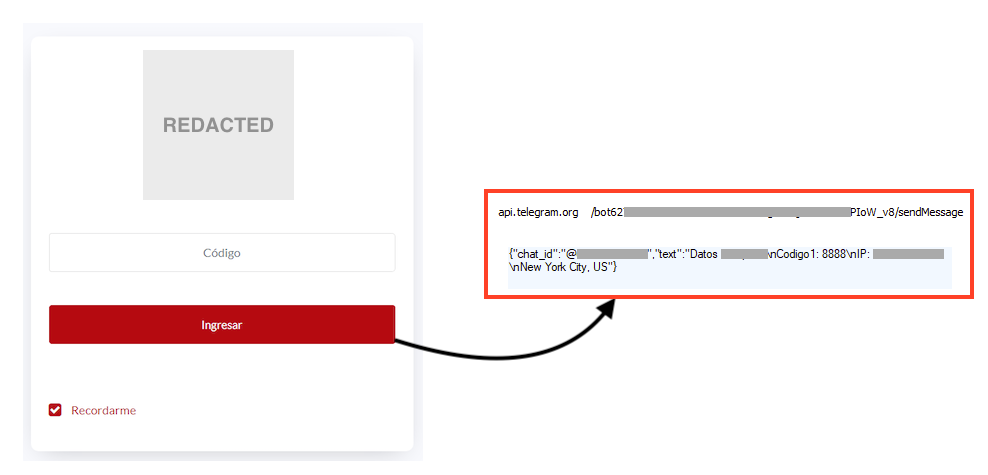
The phishing repeats the same step of asking the victim for the code that was sent to the device, likely to provide resilience and additional time to the attacker. Then, the victim is redirected to the bank’s real website.
Other Targets
The same flow we demonstrated for the phishing page above applies to a total of seven financial targets we found, where the attacker tries to exfiltrate the account number and password to a Telegram channel, and then uses the same channel to receive 2FA codes.
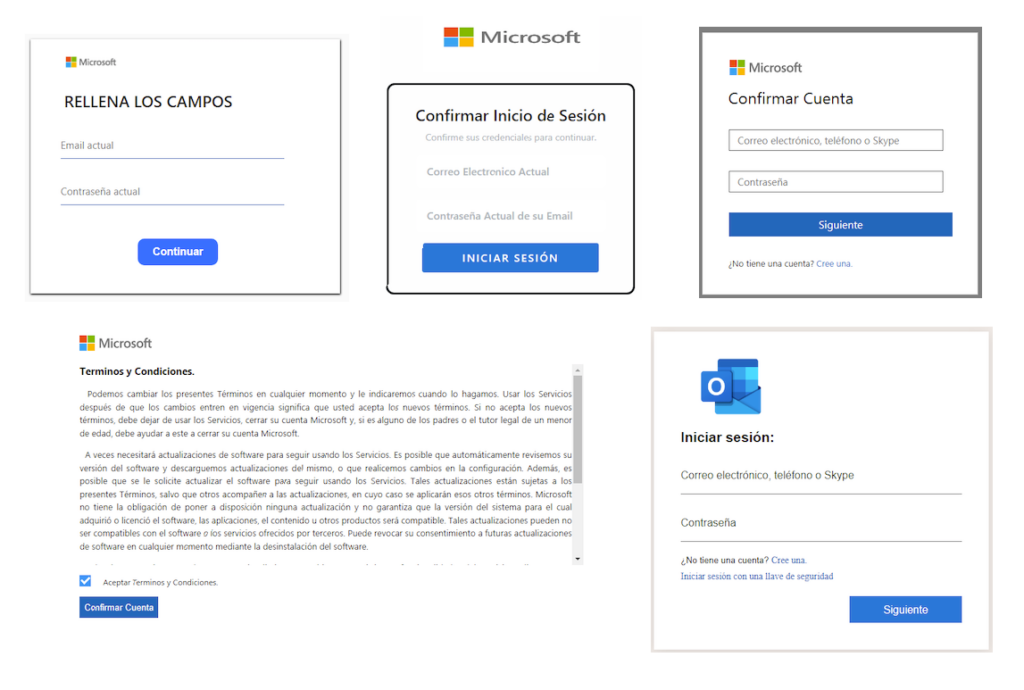
We have also found hundreds of phishing pages targeting Microsoft users, some of them also abusing Telegram to exfiltrate data, but the majority of them simply sending the stolen data to a PHP page. We found 11 different templates that are being used by attackers.
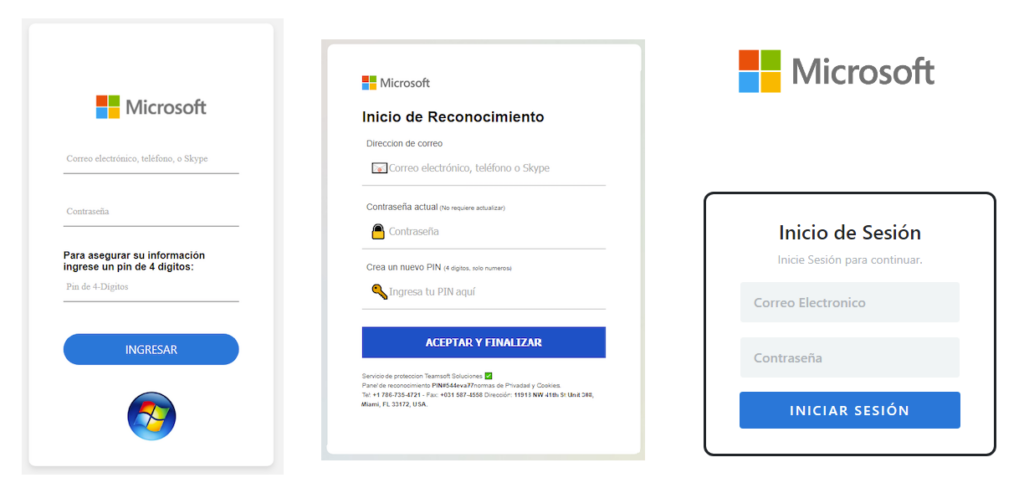
Despite the differences across these pages, the end goal is the same, which is to steal Microsoft 365 accounts.
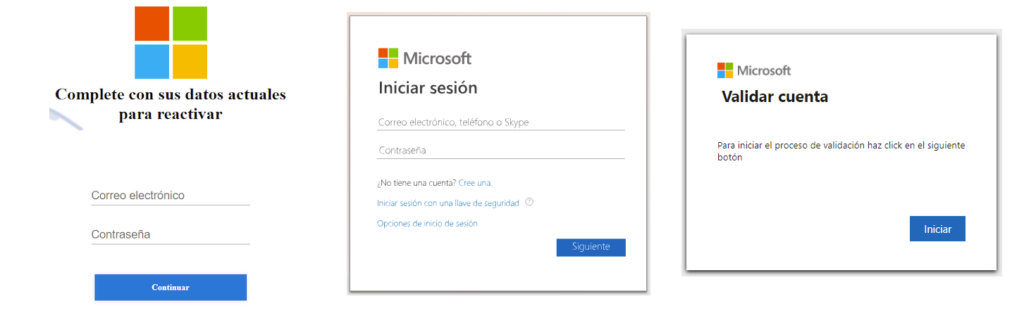
Some of these pages are even showing a fake EULA before asking the account email and password, as an attempt to add more credibility to the page.
Telegram Channels
We found 21 different Telegram channels used by attackers to receive the stolen data. Two of these channels are wide open, so it is possible for anyone to access and see the user credentials the attacker receives once the victim adds the information to the phishing page. These channels were created in March and April of 2023, respectively, each having just a few subscribers.
Conclusions
By abusing Telegram to receive stolen data from phishing pages, attackers can not only be alerted in real time, but also abuse the cloud app to bypass two factor authentication, by requesting the code from the victim while accessing the real website with the stolen data. Also, attackers are heavily abusing Royal Web Hosting likely due to the free hosting plans that offer the necessary tools to carry out the attacks, such as PHP, MySQL, etc. Netskope Threat Labs reported all the domains we found to Royal Web Hosting, and they promptly took the necessary actions to remove the malicious content and suspend the accounts associated with the domains.
Recommendations
Phishing pages in the campaign described in this post are easily recognizable by the URL, as the attacker has made little effort to disguise the URL using typosquatting or other techniques. We strongly recommend users access email and banking websites by always typing the website address into the browser address bar, and confirming if it is the real page before entering any data.
Netskope Threat Labs also recommends that organizations review their security policies to ensure that they are adequately protected against these and similar phishing pages and scams:
- Inspect all HTTP and HTTPs traffic, including all web and cloud traffic, to prevent users from visiting malicious websites. Netskope customers can configure their Netskope NG-SWG with a URL filtering policy to block known phishing and scam sites, and a threat protection policy to inspect all web content to identify unknown phishing and scam sites using a combination of signatures, threat intelligence, and machine learning. Netskope’s AI-powered phishing detector was the first to identify the phishing campaigns highlighted in this post.
- Use Remote Browser Isolation (RBI) technology to provide additional protection when there is a need to visit websites that fall in categories that can present higher risk, like Newly Observed and Newly Registered Domains.
IOCs
All the domains related to these campaigns can be found in our GitHub repository.

















