In working with many of our customers to implement the Netskope cloud access security broker (CASB), we find that the moments after the customer discovers how many cloud apps are in use in their organization for the first time can be a little overwhelming. The customer usually discovers about 10x the expected number of apps, and the question then becomes “Where do I start?” That transition to policy development to mitigate risk, while simple to implement in Netskope, can be tricky in general because there are a lot of considerations, including corporate culture, corporate stance on cloud usage, existing policies and controls, business case for the use of apps, and risk prioritization.
To address this issue, we are pleased to introduce a new tool that we have created in partnership with a few of our customers. The Netskope Discovery Playbook is a triage checklist-of-sorts for those of you who are using a CASB app enterprise-readiness rating system, such as the Netskope Cloud Confidence Index (CCI), to make decisions about which apps to accept, which to throttle usage of, which to block activities in, which to limit to certain groups of users, and which (yes, there are some) to block entirely. You can use the Playbook on its own, or in conjunction with our vendor assurance checklist, a crowd-sourced document from our customers and solutions architects that provides guidance on what capabilities to look for in the most enterprise-ready cloud apps.
The Playbook has three main sections:
- A framework for prioritizing actions
- A checklist for which enterprise-readiness parameters matter most for cloud apps, and suggested compensating or mitigating controls
- A checklist for commonly-found risks in a Netskope Cloud Risk Assessment, and suggested compensating or mitigating controls
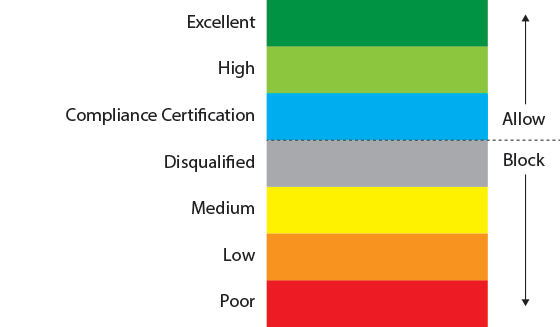
The Playbook first shows you a framework for determining which of the apps or app categories you will focus on and how to choose the parameters that matter most to you. Here’s a simplified view of that framework, assuming Discovery-only deployment mode.
Next, the Playbook breaks down each of the enterprise-readiness parameters (such as certifications, user and admin auditability, cloud encryption and key management, single sign-on and multi-factor authentication support, privacy features, data ownership terms, etc.) in the CCI into a clear definition, shows where you will find it in the CCI, and offers a list of suggested compensating or mitigating controls. We also indicate the level of importance that we place on each parameter, type of control (available in Netskope, available in other technologies, or legal or contractual), and a framework for prioritizing the controls. We purposely wrote those suggested controls for both Discovery-only (out-of-band) deployment mode as well as Active (in-line) deployment mode, to give you a sense for what you would need in either case and help you make the decision about whether and when to transition from Discovery to Active.
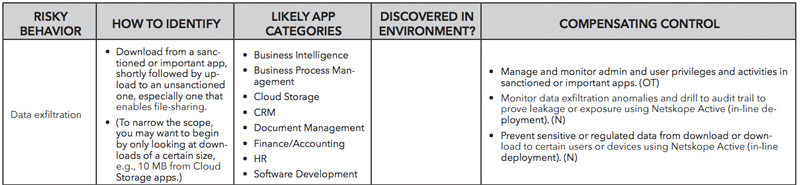
Finally, beyond providing a checklist for each of the parameters in the CCI, the Netskope Discovery Playbook provides a short checklist for the commonly-found risks in a Netskope Cloud Risk Assessment, e.g., cloud data exfiltration, usage anomalies, and indicators of malware, indicates in which cloud app categories you’d likely have the risk, and similar to the first checklist, articulates a set of suggested compensating controls. Here is a sample from that checklist:
Now when you discover more apps than you thought, instead of feeling overwhelmed, you’ll have a framework and prioritization scheme at the ready. Get your Netskope Discovery Playbook here.




 Back
Back 






















 Read the blog
Read the blog