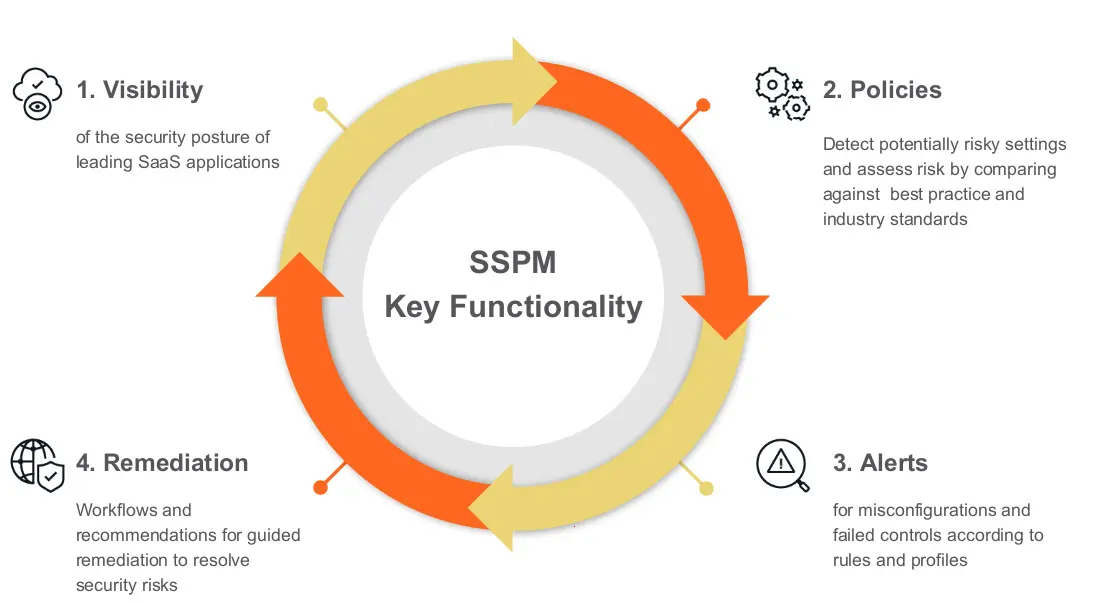
With that definition in mind, SaaS Security Posture Management (SSPM) provides automated continuous monitoring of cloud-based Software-As-A-Service (SaaS) applications like Slack, Salesforce, and Microsoft 365 to minimize risky configurations, prevent configuration drift, and help security and IT teams to ensure compliance.

As enterprises accelerate moving workloads and sensitive data into SaaS apps, the risk of accidental exposure, overly permissive entitlements that cause data leakage, non-compliance, and threats like malware remain significant challenges. SSPM gives organizations the visibility, control, and compliance management capabilities to protect their critical workloads and combat these challenges. With SSPM, you gain insight into the risks associated with your SaaS stack and the tools needed to rapidly detect misconfigurations, enforce compliance, and protect against insider threats and malware.
SaaS applications hold untold amounts of corporate, personal, and other types of sensitive data, and oftentimes vendors lack the expertise or resources to develop all the requisite security policies with their users. Developing and enforcing these different security policies consistently across applications and users is an extremely difficult task. SSPM simplifies this process by continuously monitoring the configuration of SaaS applications against pre-built policy profiles that map to industry standards such as CIS or NIST. Misconfigurations are quickly alerted and users can even automatically remediate issues before they are exploited.
SSPM is tightly coupled with CASBs (Cloud Access Security Brokers) to provide both in-line and API protection for SaaS applications.
Datasheet: Netskope SaaS Security Posture Management
Learn More: Netskope for Managed Cloud Applications




 Back
Back