Netskope Threat Labs publishes a monthly summary blog post of the top threats we are tracking on the Netskope platform. The purpose of this post is to provide strategic, actionable intelligence on active threats against enterprise users worldwide.
Summary
- Attackers continue to attempt to fly under the radar by using cloud apps to deliver malware, with 62% of all malware downloads in April originating from 150 cloud apps.
- While malicious PE (EXE/DLL) files, archives (ZIP, 7Z, GZ), and plain text files (PS, LNK) continue to dominate malware downloads, DMG files are on the rise as attackers target Mac OSX users.
- Trojans continue to represent the majority of malware downloads, used to deliver payloads such as the infostealers RecordBreaker and AgentTesla, and the Stop and Royal ransomware.
Cloud Malware Delivery
Attackers attempt to fly under the radar by delivering malicious content via popular cloud apps. Abusing cloud apps for malware delivery enables attackers to evade security controls that rely primarily on domain block lists and URL filtering, or that do not inspect cloud traffic. In April 2023, 62% of all HTTP/HTTPS malware downloads originated from popular cloud apps, matching the all-time high we saw in February.
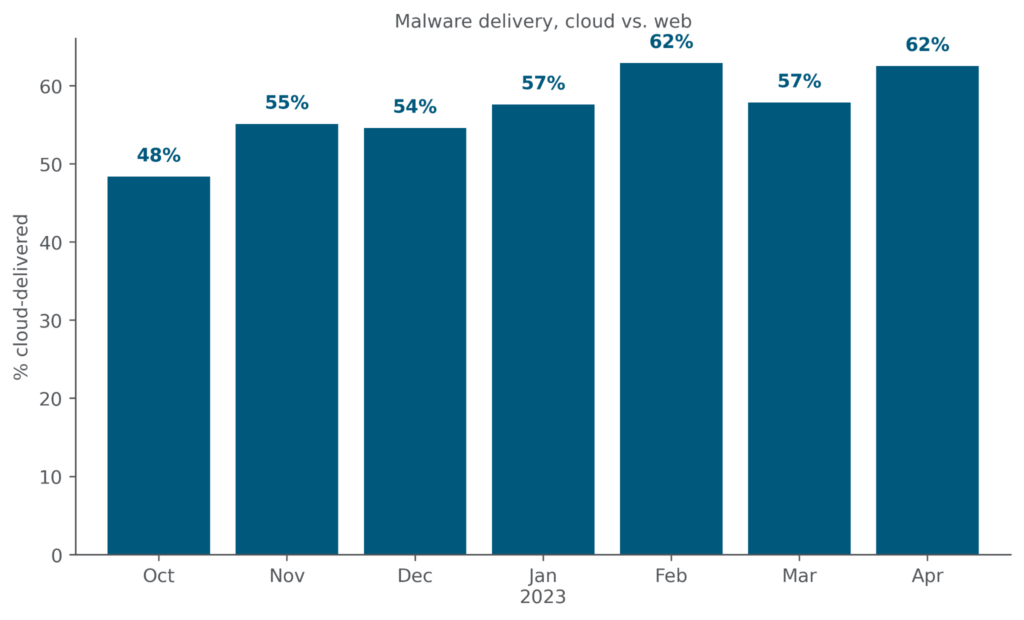
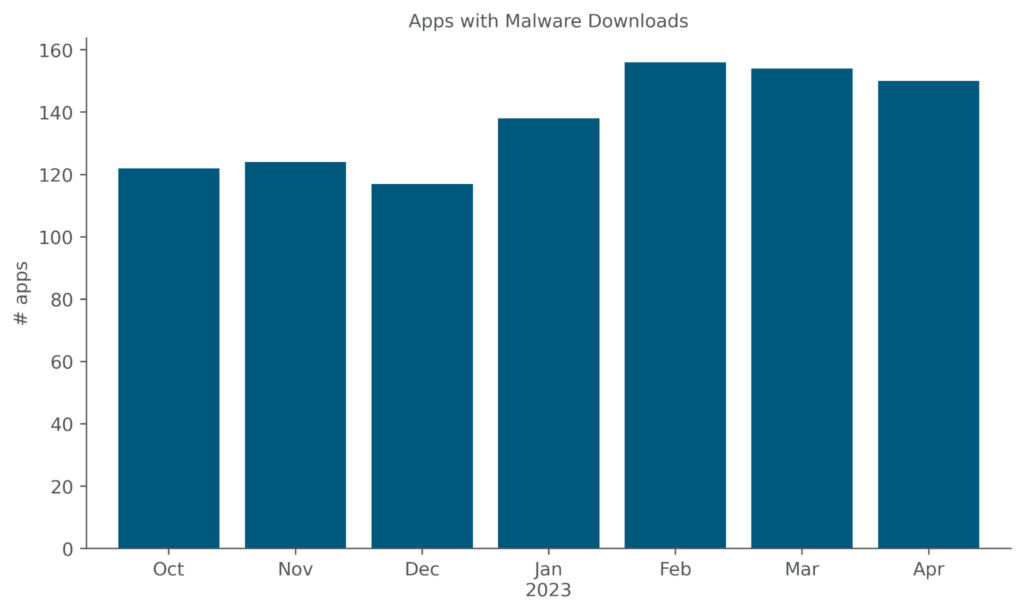
At the same time, the number of distinct cloud apps from which users attempted to download malware decreased slightly from its February high, from 156 to 150.
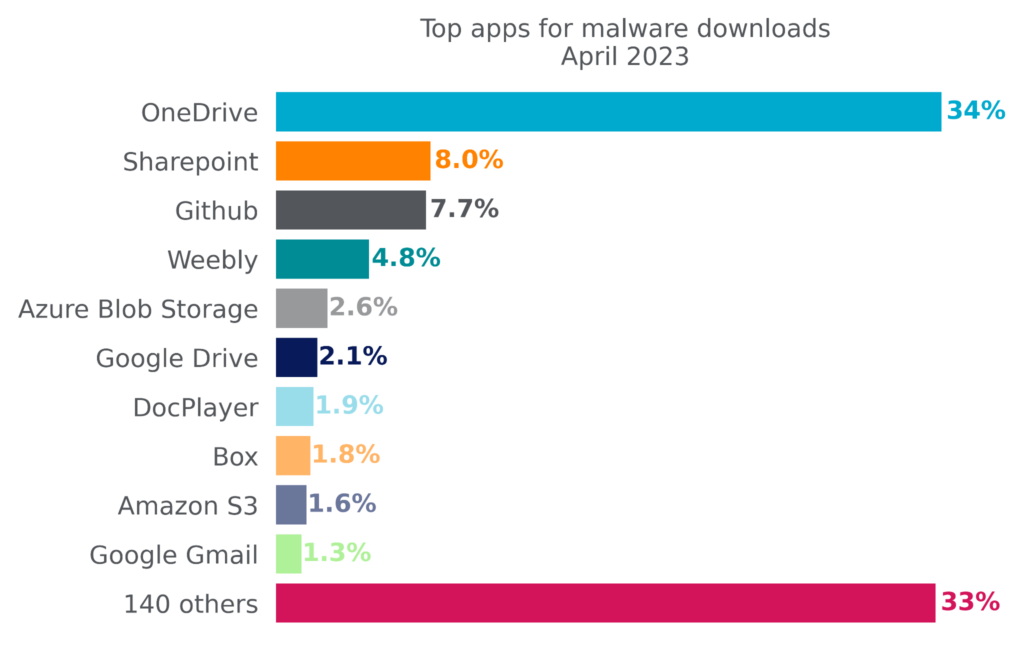
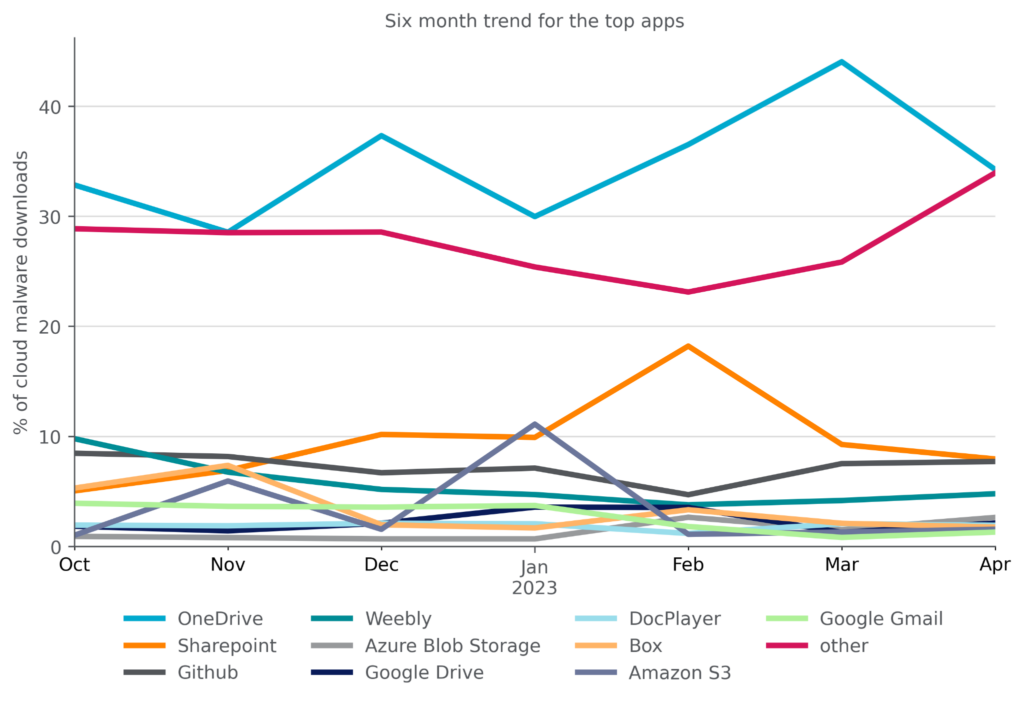
Attackers achieve the most success reaching enterprise users when they abuse cloud apps that are already popular in the enterprise. Microsoft OneDrive, the most popular enterprise cloud app, has held the top spot for the most cloud malware downloads for more than six months. In April, it fell 10 points from the six-month high it hit in March. The other top apps for malware downloads include collaboration apps (Sharepoint), free software hosting sites (GitHub), free web hosting services (Weebly), and cloud storage apps (Azure Blob Storage, Google Drive, Box, Amazon S3). DocPlayer, a free document sharing app, re-entered the top ten in April after a brief hiatus. Meanwhile, webmail apps remained in the top ten, with Google Gmail edging out Outlook.com. The top ten list is a reflection of attacker tactics, user behavior, and company policy.
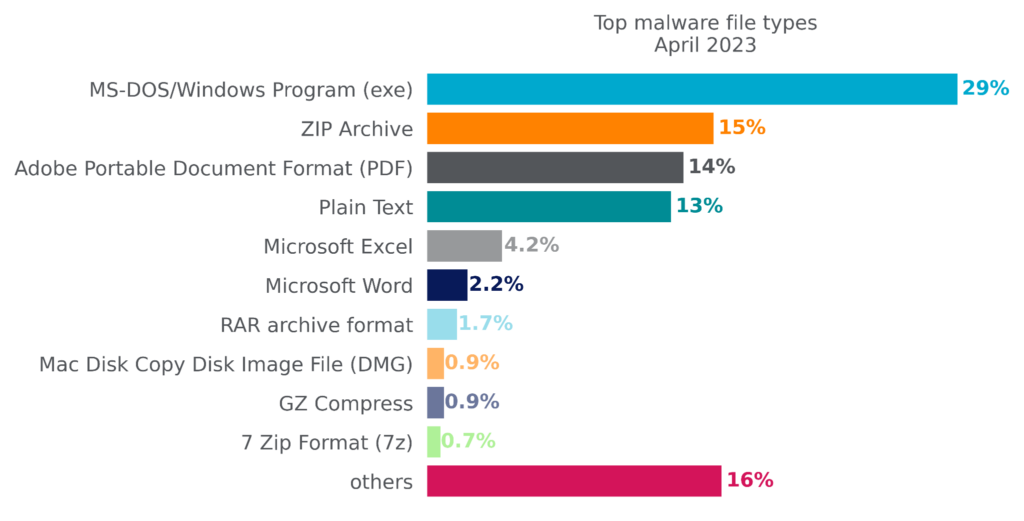
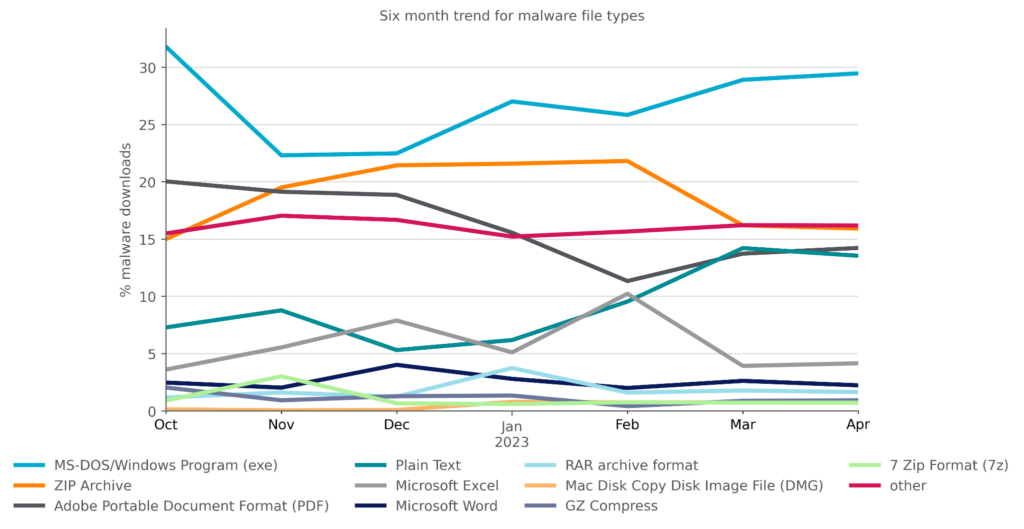
Top Malware File Types
By file type, Microsoft Windows Portable Executable files (EXE/DLL) accounted for the plurality of malware downloads in April, as they have for at least the past six months. Zip Archives, which had been steadily growing in popularity, saw a second consecutive decrease in April, but still remained in the second spot. Other archive formats RAR, GZip and 7 Zip stayed relatively constant, as did PDF files and text files, like PowerShell scripts and LNK files. Mac DMG files appeared in the top list for a second consecutive month as attacker activity targeting Mac OSX users remains constant.
Top Malware Families
Attackers are constantly creating new malware families and new variants of existing families, either as an attempt to bypass security solutions or to update their malware’s capabilities. In April 2023, 63% of all malware downloads detected by Netskope were either new families or new variants that had not been observed in the preceding six months. The other 37% were samples that had been previously observed during the preceding six months and are still circulating in the wild.
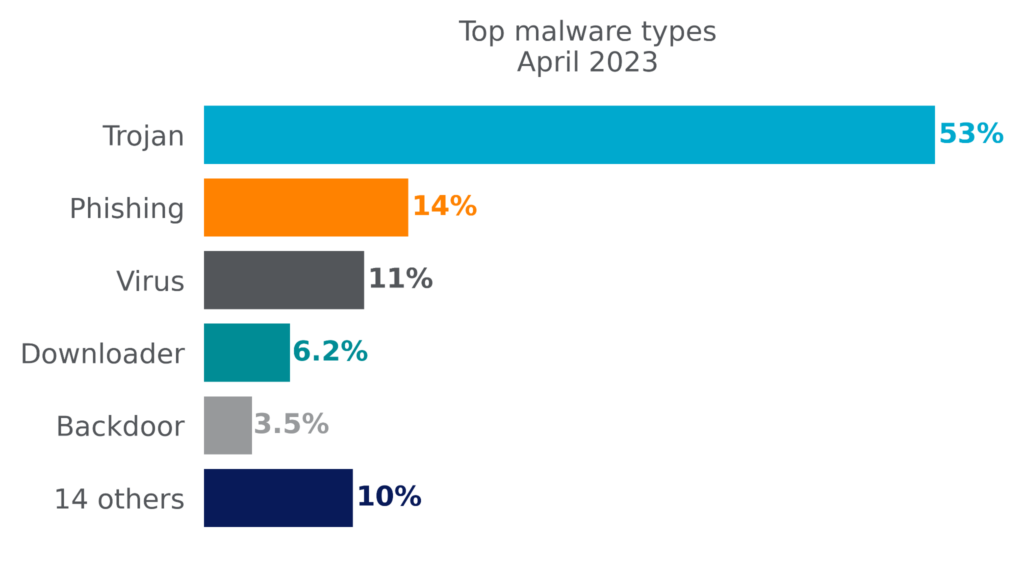
By volume, Netskope blocks more Trojans than any other malware type. Trojans are commonly used by attackers to gain an initial foothold and to deliver other types of malware, such as infostealers, Remote Access Trojans (RATs), backdoors, and ransomware. Other top malware types include phishing lures (typically PDF files designed to lure victims into phishing scams), viruses (which can propagate themselves), downloaders (which download additional malicious payloads), and backdoors (which provide clandestine remote access to infected hosts).
The following list contains the top malware and ransomware families blocked by Netskope in April 2023:
- Backdoor.Zusy (a.k.a. TinyBanker) is a banking Trojan based on the source code of Zeus, aiming to steal personal information via code injection into websites. Details
- Downloader.BanLoad is a Java-based downloader widely used to deliver a variety of malware payloads, especially banking trojans. Details
- Downloader.SLoad (a.k.a Starslord) is a download that is often used to deliver Ramnit. Details
- Infostealer.AgentTesla is a .NET-based Remote Access Trojan with many capabilities, such as stealing browsers’ passwords, capturing keystrokes, clipboard, etc. Details
- Infostealer.Dridex has been around since at least 2015 and has had its botnet infrastructure taken down multiple times, but continues to re-emerge with new features and new infrastructure. Details
- Phishing.PhishingX is a malicious PDF file used as part of a phishing campaign to redirect victims to a phishing page.
- Trojan.Masson (a.k.a. Dripion) has been around since at least 2016 and first found targeting victims in Taiwan. Details
- Trojan.Razy is a Trojan typically distributed via malicious ads disguised as legitimate software, often used to steal cryptocurrency data. Details
- Trojan.Valyria (a.k.a. POWERSTATS) is a family of malicious Microsoft Office Documents that contain embedded malicious VBScripts usually to deliver other malicious payloads. Details
- Ransomware.CrossLock emerged in April 2023 targeting organizations in Brazil. Details
Recommendations
Attackers have always sought to evade detection and avoid suspicion in delivering malware. Two strategies that attackers have been using increasingly in the past six months are to deliver malware by abusing cloud apps and to package malware in archive files. Netskope Threat Labs recommends that you review your security posture to ensure that you are adequately protected against both of these trends:
- Inspect all HTTP and HTTPS downloads, including all web and cloud traffic, to prevent malware from infiltrating your network. Netskope customers can configure their Netskope NG-SWG with a Threat Protection policy that applies to downloads from all categories and applies to all file types.
- Ensure that your security controls recursively inspect the content of popular archive files such as ZIP files for malicious content. Netskope Advanced Threat Protection recursively inspects the content of archives, including ISO, TAR, RAR, 7Z, and ZIP.
- Ensure that high-risk file types like executables and archives are thoroughly inspected using a combination of static and dynamic analysis before being downloaded. Netskope Advanced Threat Protection customers can use a Patient Zero Prevention Policy to hold downloads until they have been fully inspected.
- Configure policies to block downloads from apps that are not used in your organization to reduce your risk surface to only those apps and instances that are necessary for the business.
- Block downloads of all risky file types from newly registered domains and newly observed domains.
In addition to the recommendations above, Remote Browser Isolation (RBI) technology can provide additional protection when there is a need to visit websites that fall in categories that present higher risk, like Newly Observed and Newly Registered Domains.
About This Report
Netskope provides threat and data protection to millions of users worldwide. Information presented in this report is based on anonymized usage data collected by the Netskope Security Cloud platform relating to a subset of Netskope customers with prior authorization. This report contains information about detections raised by Netskope’s Next Generation Secure Web Gateway (SWG), not considering the significance of the impact of each individual threat. Stats in this report are based on the period starting October 1, 2022 through April 30, 2023. Stats are reflection of attacker tactics, user behavior, and organization policy.

















