Microsoft Word, Excel, PowerPoint, and other Office document formats are popular among attackers, who abuse them to infect their victims with ransomware, infostealers, backdoors, and other malware.
- The attacker sends a link to download an Office document to the victim via email, social media, SMS, cloud storage apps, or messaging apps.
- The attacker uses social engineering to convince the victim to download the file, open it using Microsoft Office, and enable content.
- If the victim enables content, the malicious code in the Office document infects their computer.
In this article, we look at the anatomy of a recent Office document attack from the victim’s perspective, highlight the most common types of Office document attacks seen today, and suggest strategies to reduce your risk of becoming the latest victim.
Anatomy of an Office document attack
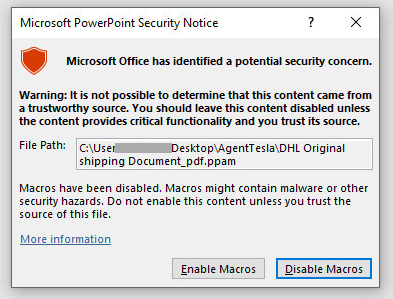
In early 2022, Netskope saw a series of Office document attacks using malicious PowerPoint files to deliver the remote access Trojans AveMaria/Warzone and AgentTesla. The victims received an email with a generic message asking them to review an order. Fake invoices, order forms, inventory lists, shipping notifications, and sales quotes are commonly used by attackers to bait victims into downloading malicious Office documents. When the victim downloads and opens the attachment using Microsoft PowerPoint, they are presented with a dialog box that asks them whether they want to enable macros.
This is a pivotal moment for the victim. If they click “Disable Macros,” nothing will happen. They will see a blank page. Perhaps this nothingness will inspire them to try again and click “Enable Macros” instead? If they click “Enable Macros,” the malicious code embedded in the document will run automatically and their computer will be infected with a remote access Trojan within seconds, which means the attacker will now be able to access the victim’s computer.
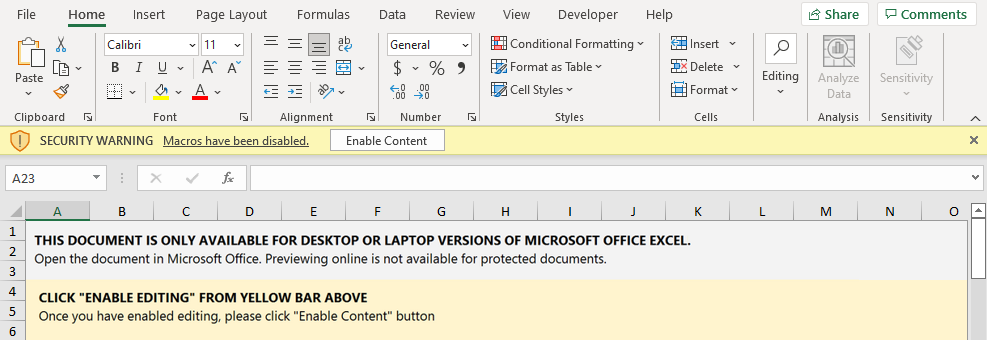
Another similar attack uses Excel instead of PowerPoint, but with an identical flow. Below is another example from January of an Emotet Office document attack. The attacker uses the body of the document itself to do some social engineering, telling the user they must open the document on their computer and must click “Enable Content.” If they don’t, they won’t be able to open the document. Both of these are required steps for the attacker to infect the victim’s computer, which is why the attacker is so insistent.
In response to the prevalence of attackers using this tactic to spread malware, Microsoft decided to block VBA macros by default for files downloaded from the internet.
Malicious file types
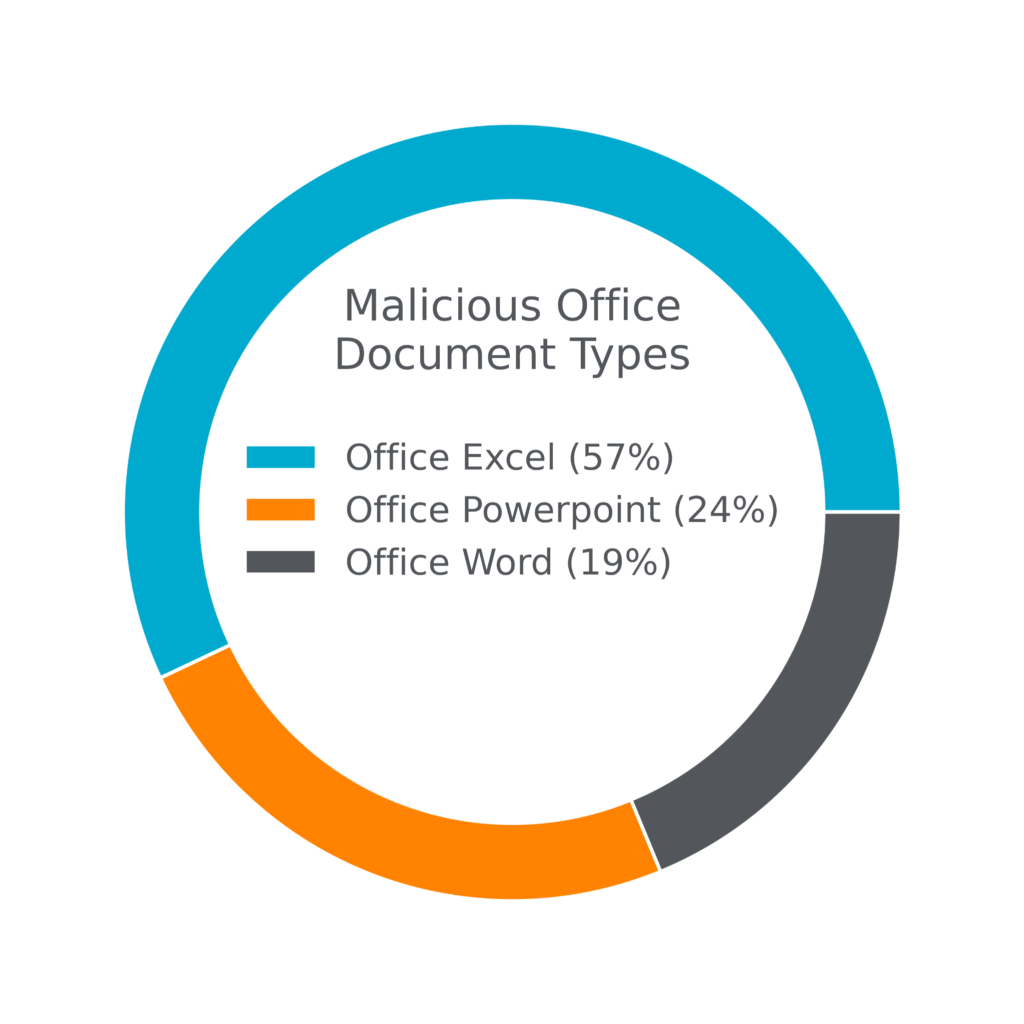
In the preceding examples, we highlighted an Office document attack that used a malicious PowerPoint file to infect victims with remote access Trojans. Overall, nearly one-quarter of all malicious Office documents observed so far in 2022 were PowerPoint files. Excel files are comparatively more popular among attackers, representing more than half of all malicious Office documents observed. The preceding examples provide some hint as to why: The Excel file format allows attackers to display some content for social engineering purposes, to convince the victim to “Enable Content.” Also, Excel supports additional features often abused by attackers, such as Excel 4.0 Macros.
Features of malicious Office documents
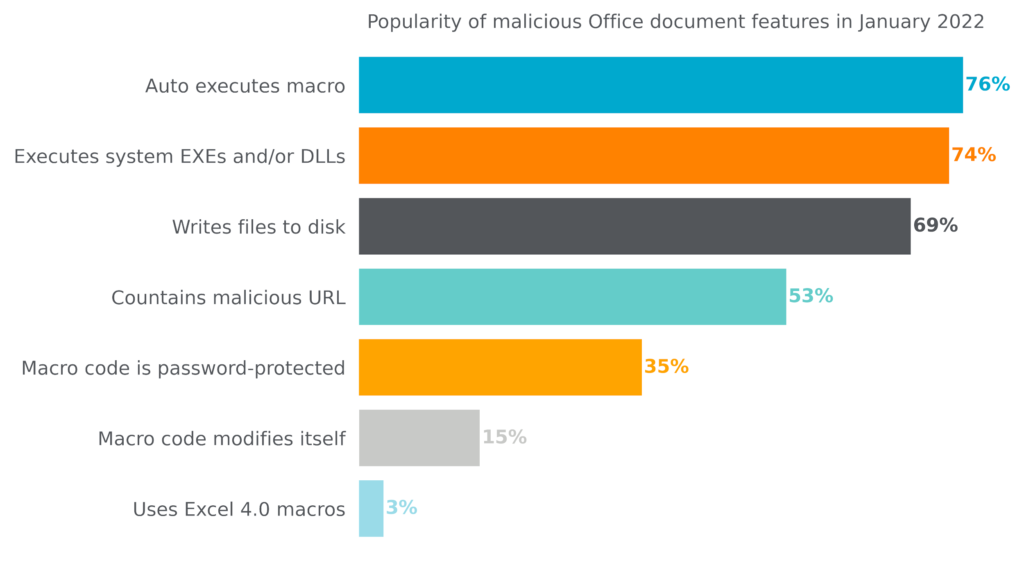
Most Office document attacks today aim to either infect a victim’s computer with malware or trick the victim into visiting a malicious website. Despite being written by different attackers, the majority of malicious Office documents seen today share a common set of features.
- Auto executes macro: Macros are small programs meant to automate repetitive tasks in Microsoft Office and are commonly abused by attackers to infect victims’ computers. Automatic execution of macros means that the macro runs as soon as the user clicks “Enable Content” or “Enable Macros.”
- Executes system EXEs and/or DLLs: To install the malware, malicious macros will often use built-in Windows system features. This technique is referred to as living-off-the-land.
- Writes files to disk: Attackers write malware files to the disk so they can persist even if you reboot your computer.
- Contains malicious URLs: Some attackers embed malicious URLs directly into the files, either to entice the victim to click on them or to download malware automatically.
- Macro code is password-protected: Some attackers password protect the malicious macro to hide from security tools or researchers that might try to analyze the code and discover its function.
- Macro code modifies itself: Some attackers write self-modifying macros to hide their true purpose from security tools or researchers that might try to analyze the code.
- Uses Excel 4.0 macros: Excel 4.0 macros are an old Office feature that gained popularity among attackers and are now disabled by default. They are used in only a small percentage of Office document attacks.
The following chart breaks down the popularity of these features among the thousands of malicious Office documents discovered and analyzed by Netskope in January 2022.
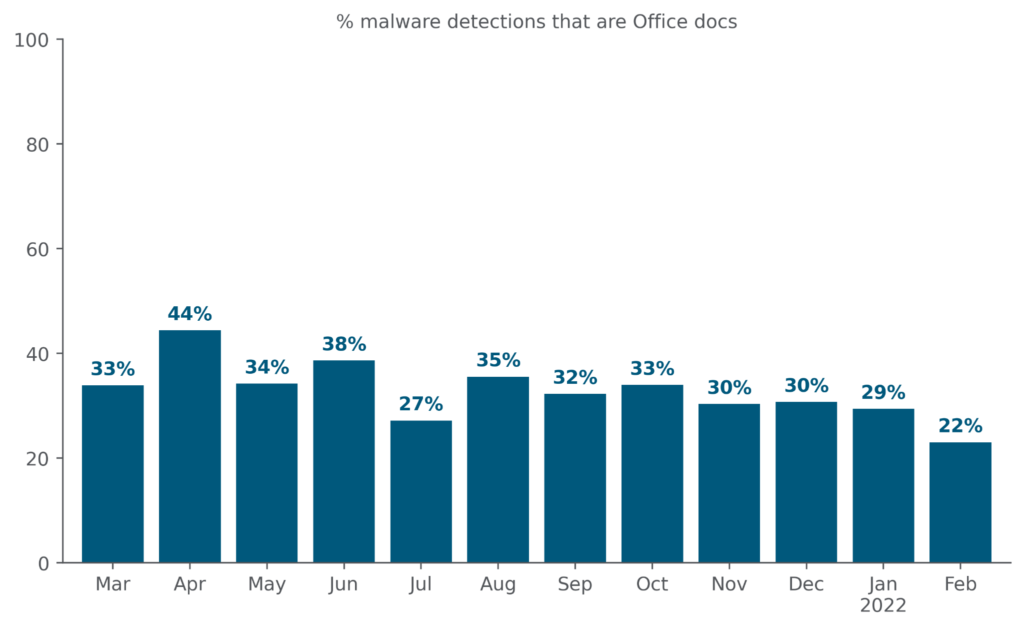
A continuing wave of malicious Office documents
In the spring of 2020, Emotet launched a large-scale and highly effective spam campaign to deliver malware via weaponized Office documents. Prior to the Emotet campaign, Office documents represented only 20% of all malware downloads. During the campaign, they surged to nearly 50% of all malware downloads. Since then, other attackers have attempted to recreate Emotet’s success, resulting in a higher-than-before flow of malicious Office documents targeting unsuspecting users. After Microsoft announced that they would start blocking VBA macros for files downloaded from the internet by default, we saw a decrease in downloads of malicious Office documents in February to pre-Emotet levels. We hope to continue to see this fall in the coming months.
Malicious Office documents lurking in cloud storage apps
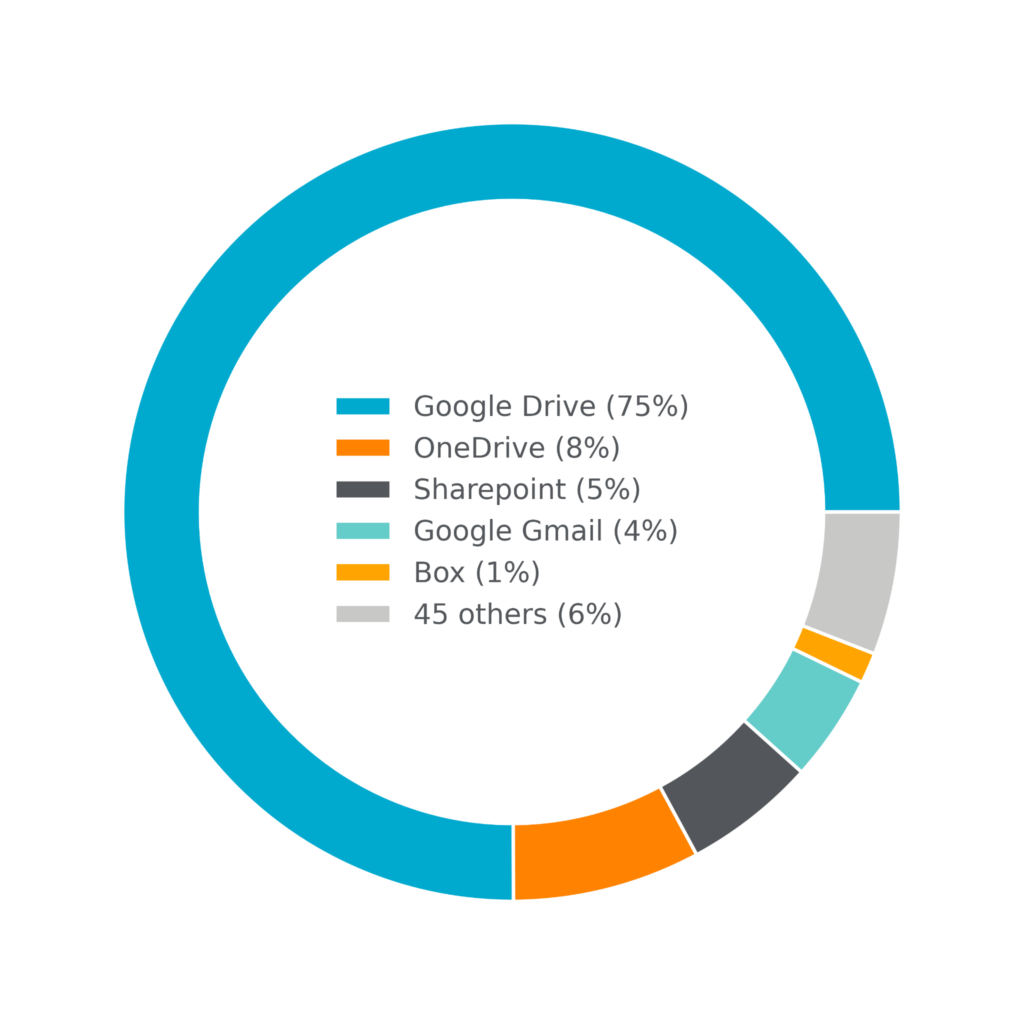
One bit of social engineering attackers use to try to lure victims into downloading malicious Office documents is to abuse popular cloud storage apps to share them. For example, as someone who regularly uses Microsoft OneDrive and Microsoft Office, I’m much more likely to download and open a document shared with me over OneDrive than I am a document hosted at some strange URL I’ve never seen before. Emotet famously abused Box to spread malicious Office documents in their 2020 malspam campaign, and other attackers have been emulating their tactics ever since. Today, 95% of malicious Office documents are delivered via cloud apps, with only 5% being delivered via traditional websites. In February 2022 alone, Netskope blocked downloads of malicious Office documents from 50 different apps, led by Google Drive and OneDrive.
At the same time, attackers also abuse cloud apps for additional stages of the attack. In the PowerPoint-based attack described at the beginning of this post, the malicious macro triggers additional malware downloads for files hosted using MediaFire, Blogger, and GitHub.
Defensive measures
The best way to avoid becoming a victim of an Office document attack is to never download, open, and enable macros for Office documents that are shared with you. So what do you do when someone shares a document with you? The safest way to open it is to use a web-based viewer like Google Drive or Microsoft Office 365. In the second example I shared, the attacker explicitly tells the victim not to do this, because it nullifies the attack. And if you do download a file, never enable macros. If you are a system administrator, you can also use the Group Policy Editor to restrict all users in your organization from enabling macros.

















