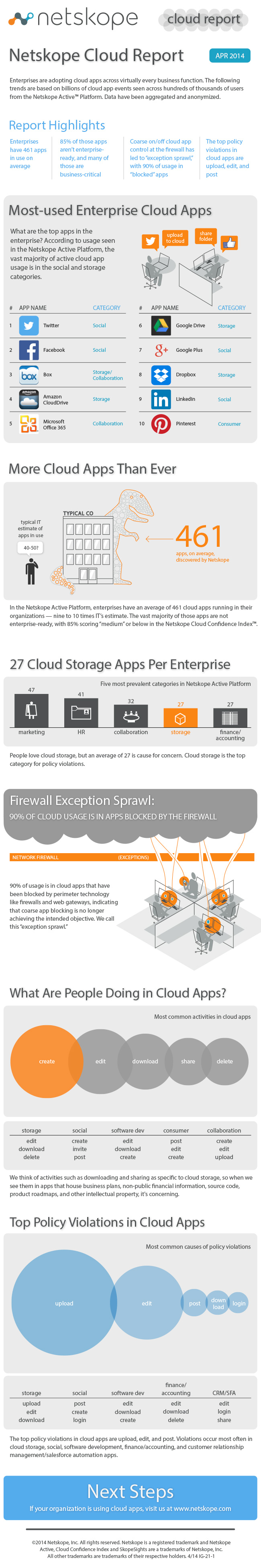
We released the Netskope Cloud Report today. Rather than take you through all of the findings (check it out here to see top used apps, user activities, and policy violations), I want to focus on one thing. It’s something we’re calling “exception sprawl” and it’s the single most shocking stat: 90 percent of cloud app usage is in blocked apps.
But how can that be? Surely not all of our customers’ firewalls are broken! Here’s how it happens: IT sets a policy and the network team blocks a service like Dropbox or Twitter at the perimeter.
Then some poor guy in marketing whose job it is to tweet about new product releases goes to IT and asks for an exception. It’s granted. Then the ENTIRE marketing team asks for the exception. Granted. The CEO, who has just gotten her groove on in the social media realm, also asks for an exception…for herself AND the entire executive staff. Granted, of course. PR needs an exception too, as does the CTO and his staff, and all the PMs and program managers. Customer support wants in on the action because they need to monitor social media for complaints and problems. And if they’re ahead of the game, they’ve got an “Acme Cares” Twitter handle so they can send out proactive messages. And so it goes…until you have the vast majority of usage in the exceptions, and the exceptions truly become the rule. The point is: Blocking at the perimeter no longer makes sense given how our business practices have changed.
Here’s another stat (I know, I lied: I said I would only talk about one stat from the report. Please indulge me for just one more!) For all of this blocking at the perimeter, one conspicuously missing policy at the top of our policy violations list in the Netskope Active Platform is – you guessed it – blocking. The way blocking is instantiated in Netskope is login = block. We count how many times that policy is violated. Surprisingly, login is only the fifth most common policy violation, behind upload, edit, post, and download. We didn’t report on this in the report, but looking back at the data, login violations represent only about 4 percent of the number of upload violations, so there’s really a big drop-off between granular, activity-based blocking and straight-up blocking.
This tells me that when people are presented with an alternative to heavy-handed policies, they go for it. If they know that perimeter blocking breaks so many business processes that they have to “except” 90 percent of usage, the granular approach is a no-brainer.
Here’s the infographic. You can download the full report here.