Netskope Threat Research Labs has recently observed a spam campaign using multi-vector attack methodology. The malicious files are zipped and sent in an email as an attachment. The ZIP file contains a PDF and VBS file. Upon execution, the VBS file downloads a malicious binary to the victim’s machine which further communicates with a C&C server. Netskope Threat Protection detects the VBS file and the malicious payload as Backdoor.Vbs.VAD and Backdoor.Ransm.BOK. The analysis of the malicious binary revealed that it fails to replicate on the Windows XP operating system, which is still used by a number of sandbox vendors. The comparison between the execution of the malicious binary in Windows 7 and the execution of the patched malicious binary in Windows XP provides good insight into the API call fluctuation that is highly unlikely in benign files.
In a number of enterprises, email attachments are often automatically synced to cloud storage services using file collaboration settings in popular SaaS applications like Microsoft Office 365 and Google G Suite. This auto-syncing feature can also be achieved through third party applications as well. Since the filenames appear less suspicious, they are more likely to be viewed as coming from within the organization (and therefore trusted) and shared with others in the same user group. This blog will detail the evasion techniques used by the malicious payload when the malicious files within the attachment are executed by users.
Evasion Techniques
During our analysis, we observed the following two evasion techniques used by the packer and the behavior of the unpacked file.
Execution failure on Windows XP using NUMA
Non Uniform Memory Access ( NUMA ) is a method to configure memory management in multi-processing systems. This is done by linking to a whole set of functions declared in Kernel32.dll. This is used to increase processor speed without increasing the load on the processor bus. The support of this feature is available in Windows Vista and above operating systems. The sample we analyzed used VirtualAllocExNuma API and was packed with the PECompact packer. The sample might have been packed with a modified version of PECompact packer, as we have not seen this type of behavior from the PECompact packer before. We have taken the the API execution trace and execution graph of the sample to investigate how it works as shown in Figure 1 and Figure 2.
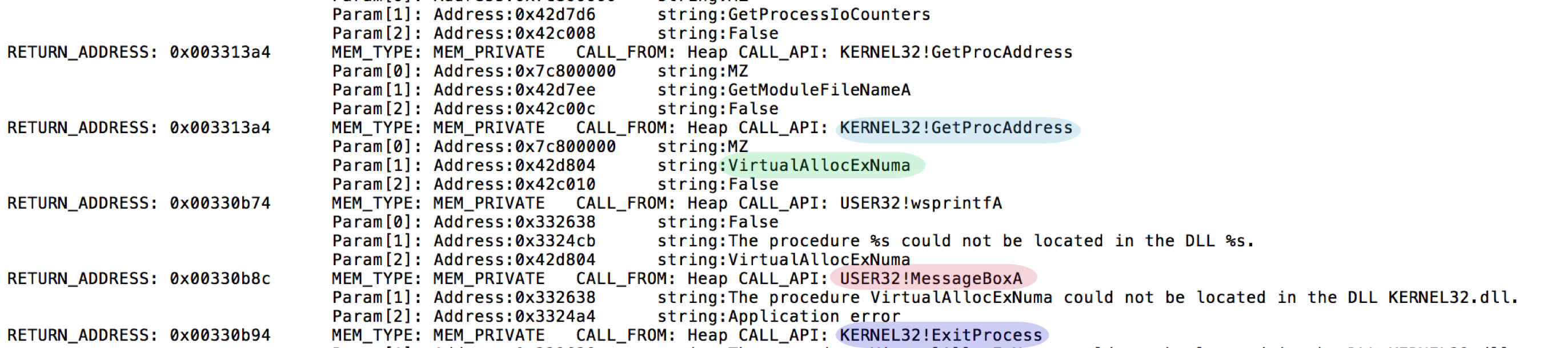
Figure 1: API Execution Trace in Windows XP
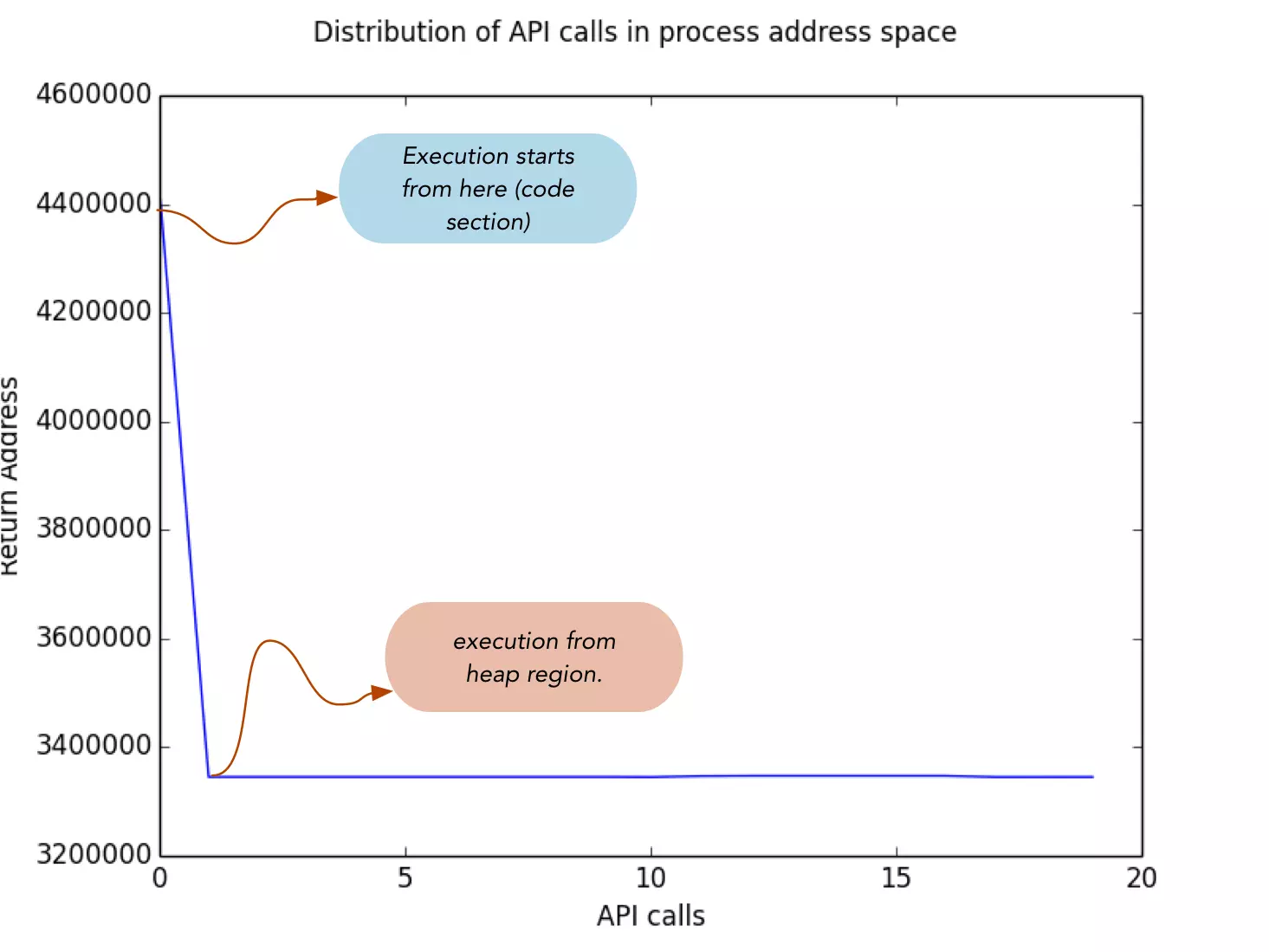
Figure 2: Execution Graph in Windows XP
From Figure 1, we see that the executable calls GetProcAddress to resolve the address of the VirtualAllocExNuma API. Since VirtualAllocExNuma is not available in Windows XP, GetProcAddress fails to retrieve the address of the function, which results in calling ExitProcess to stop further execution. These API calls are coming from the heap region as shown in Figure 2. In order to proceed with the execution, we patched the heap region to make a valid call to GetProcAddress.
The execution graph of the unpacked binary is shown in Figure 3.
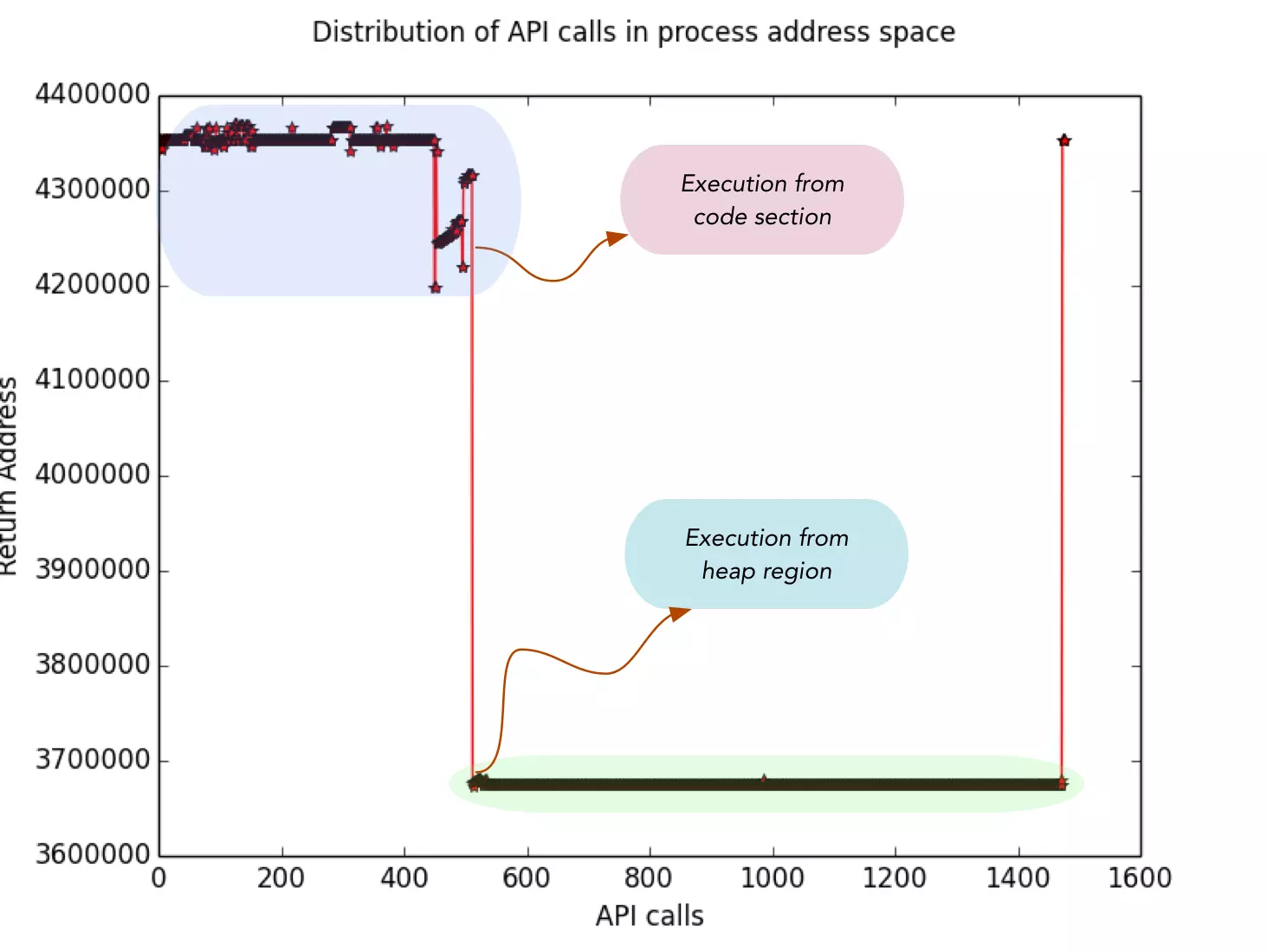
Figure 3: Execution Graph of unpacked binary
In Figure 3, we see the unpacked binary again unpacking the segment of code in the heap region to download the malware. This type of API call fluctuation in the address space is highly unlikely in benign files.
UAC bypass in Windows 7
User Account Control (UAC) gives us the ability to run in standard user rights instead of full administrator rights. This feature is supported in all Windows operating systems since Vista. The sample we analyzed bypassed UAC using the Windows event viewer utility. This is a known technique detailed here. The API execution trace of the UAC bypass is shown in Figure 4.
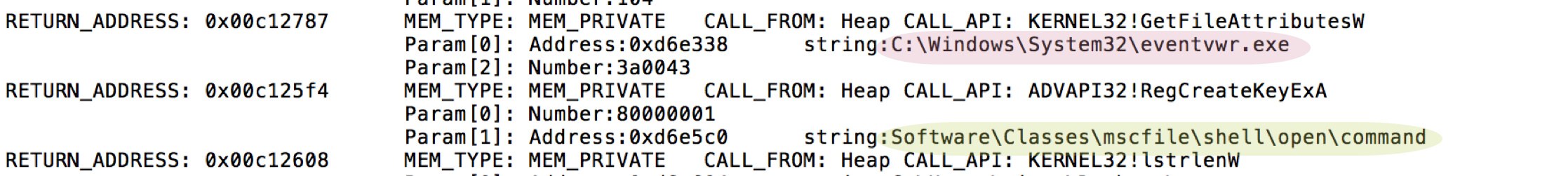
Figure 4: UAC bypass execution trace in Windows 7
The execution graph of the binary in Windows 7 is shown in Figure 5.
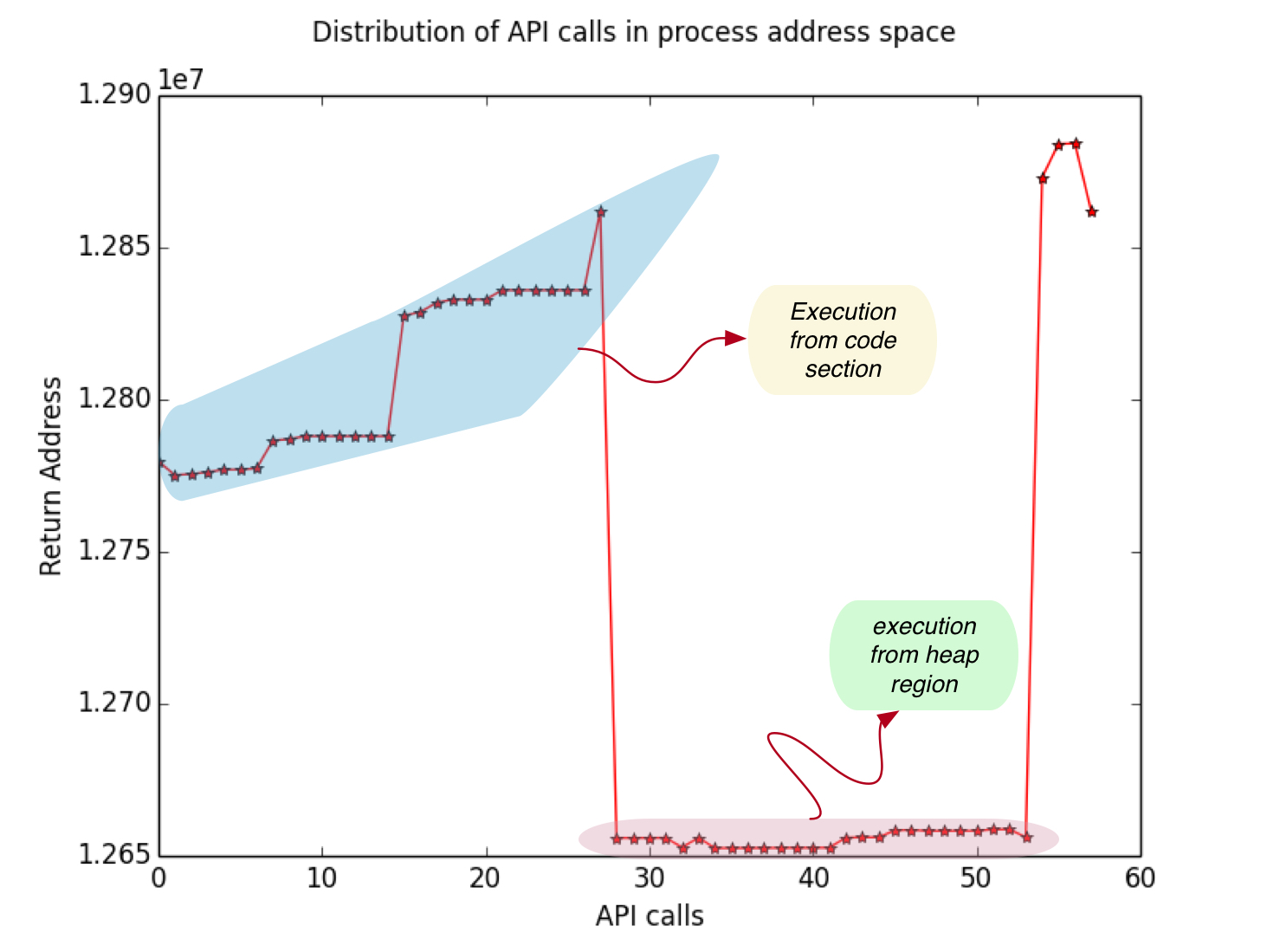
Figure 5: Execution graph in Windows 7
On comparing the execution graph in Windows XP and Windows 7 as shown in Figure 2 and Figure 5, we see a deviation in execution on both platforms, which confirms that the binary will behave differently in different environments.
Godzilla Botnet Loader
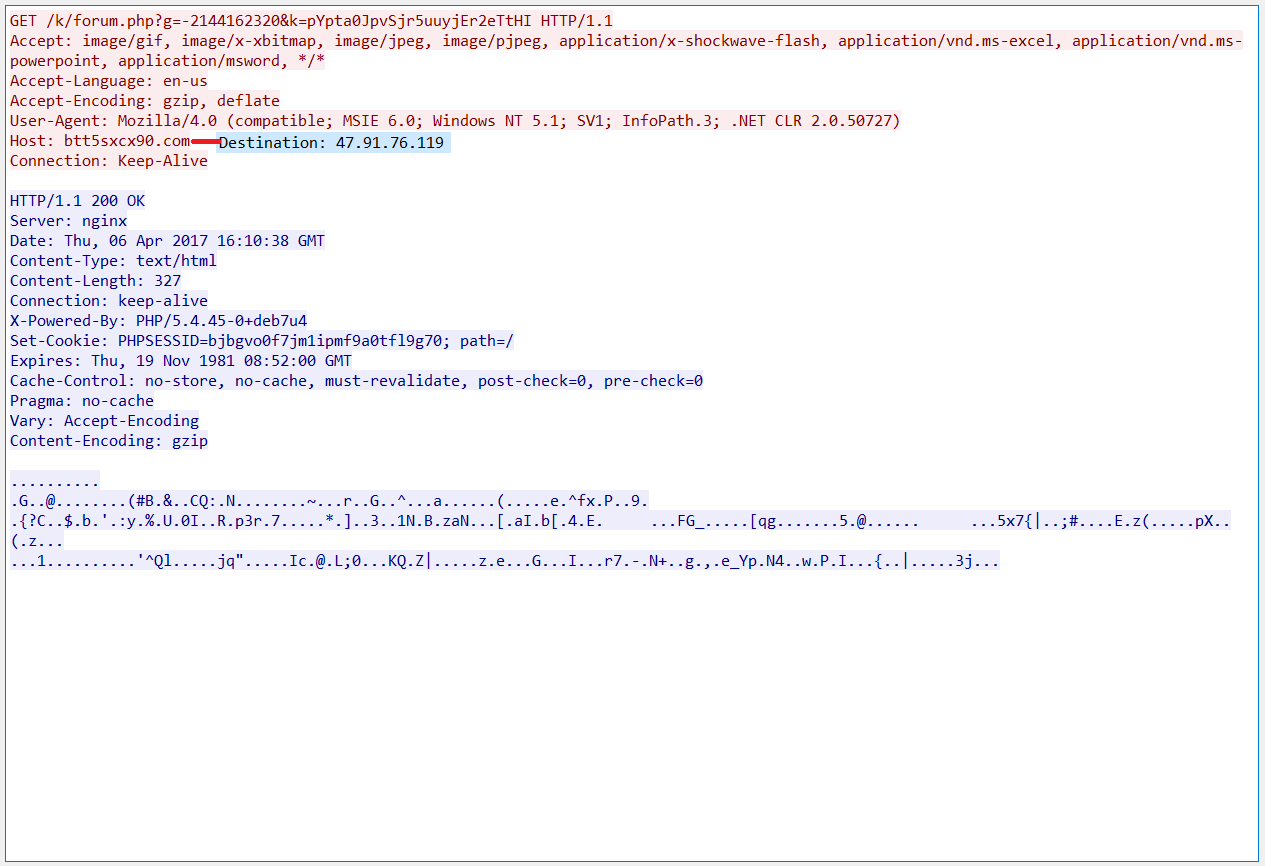
Figure 6: Pcap showing the C&C connection to btt5sxcx90[.]com
When C&C was accessed, it presented a C&C admin login panel as shown in Figure 7.
Figure 7: C&C panel of btt5sxcx90[.]com
We searched for similar C&C admin login panels using the same theme, from the image taken from the path “k/media/img/logo.png” and we found the C&C panel theme related a known botnet named Godzilla.
The passive DNS records revealed that the IP 47.91.76[.]119 was associated with multiple domain names according to VirusTotal as shown in Figure 8. A majority of these domains were associated with the distribution of various malware.
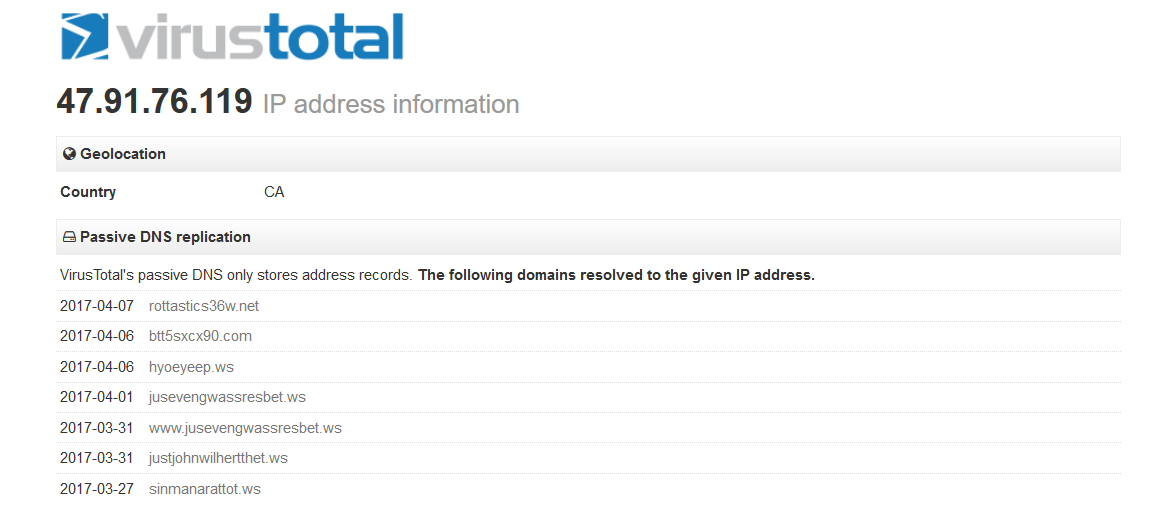
Figure 8: Passive DNS of C&C 47.91.76[.]119 in VirusTotal
At the time of this writing, the C&Cs were not serving any payload. A research article published by Arbor observed Godzilla Botnet installing a banking trojan named Trickbot.
Conclusion
As we observed in this variant of the Godzilla Botnet, the use of VirtualAllocExNuma raises concerns for security products using sandbox environments and AV emulators that depend on Windows XP for the replication of the binary. We believe that this behavior was unintentional, as later in the day attackers updated the executable file with a new MFC builder that worked on Windows XP. It is also becoming more evident that bypassing UAC is increasingly popular for new variants of malware in general. It should be noted that sending malicious files via email attachment is not new, but the flexibility offered by a number of such email providers to auto-sync the files to enterprise cloud storage and collaboration services amplify the impact of risk to an organization due to the cloud malware fan-out effect.
General Recommendations
Netskope recommends the following to combat cloud-based malware threats:
- Detect and remediate all threats in sanctioned and unsanctioned cloud services using a threat-aware cloud access security broker like Netskope
- Actively track usage of unsanctioned cloud services and enforce DLP policies to control files and data en route to or from your corporate environment
- Regularly back up and turn on versioning for critical content in cloud services
- Enable the “View known file extensions” option on Windows machines
- Warn users to avoid executing any file unless they are very sure that they are benign
- Warn users against opening untrusted attachments, regardless of their extensions or file names
- Keep systems and antivirus updated with the latest releases and patches




 Back
Back 














 Read the blog
Read the blog