Summary
Emotet is one of the world’s prolific modular botnets that has several evasive and technical variations up its sleeve. After a brief intermission, Emotet has recently re-emerged using massive malspam campaigns.
Threat
Emotet first emerged as a banking Trojan in 2014 and later evolved into a Malware-as-a-Service model operating from three server clusters known as Epoch 1, Epoch 2, and Epoch 3. These clusters use unique RSA keys to communicate with their C2 servers and have been used to deliver high profile malware including Ryuk, TrickBot, Ursnif, LokiBot, and AZORult. These payloads are typically delivered from websites with vulnerable plugins that are exploited by the threat actors. This approach of using compromised webpages is used to evade security solutions that rely on URL filtering alone to block malware downloads.
Scope
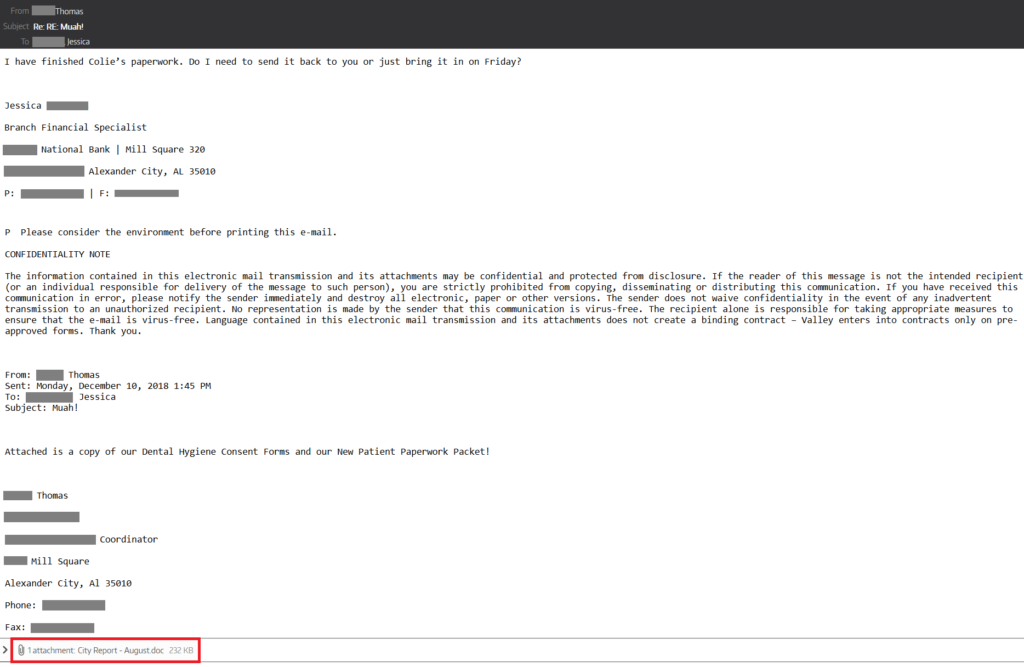
Emotet is majorly distributed via malspam phishing emails posing as transactions, payments, or invoices related to the targets. The emails contain links or attachments of Office documents embedded with malicious macro code to download the next stage payload. The emails are often socially engineered to appear as though they come from someone the victim has emailed previously.
Protection
Netskope Threat Labs is actively monitoring the malware campaigns using Emotet and has ensured coverage for all known threat indicators and payloads.
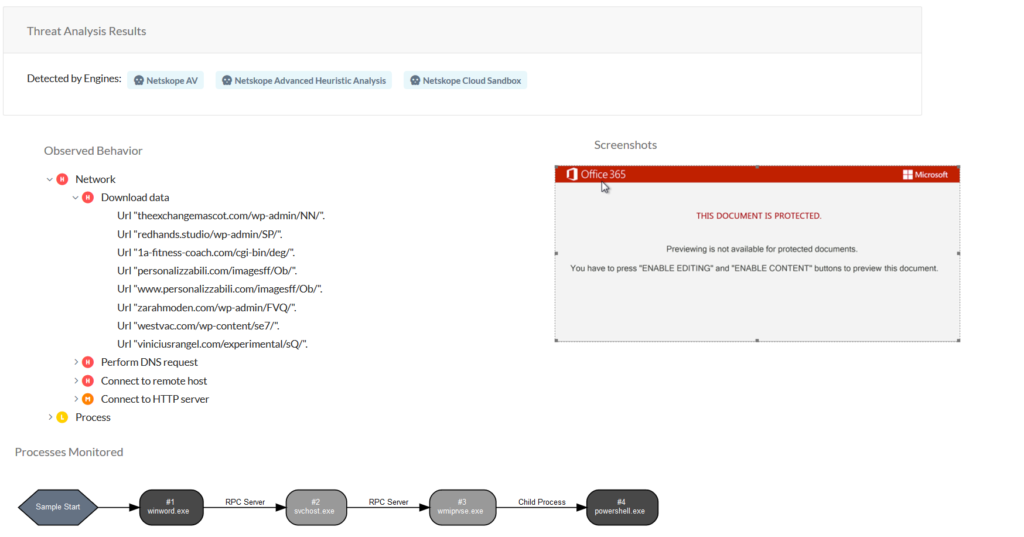
Netskope’s Advanced Threat Protection includes static analysis and dynamic engines that can detect previously unseen Emotet malware samples in the wild. Figure 2 shows the sandbox results for an Emotet sample in the Netskope UI. This example is a malicious Office document that downloads the next stage payload from compromised websites and executes the malicious payload via powershell.
- Netskope Threat Protection
- W97m.Downloader.IXT
- W97m.Downloader.IYH
- W97m.Downloader.IYJ
- W97m.Downloader.IYK
- Trojan.EmotetO.Gen.1
- VBA.Heur.Mail.Emotet.1.6073CA60.Gen
- VBA.Heur.Mail.Emotet.1.D943B401.Gen
- VB:Trojan.VBA.Agent.BHE
- VB.Heur2.EmoDldr.5.B611173F.Gen
- VB.Heur2.EmoDldr.14.ADD10D99.Gen
- VB.Heur.EmoDldr.28.A98FECAB.Gen
- And many more…
- Netskope Advanced Threat Protection provides proactive coverage against this threat using both our ML and heuristic-based static analysis engines and our cloud sandbox.
- Gen.Malware.Detect.By.Sandbox indicates a sample that was detected by Netskope’s cloud sandbox
- Gen.Malware.Detect.By.StHeur indicates a sample that was detected by one of Netskope’s static analysis engines

















