Netskope Threat Research Labs detected an Adware family named, ‘CapitalInstall’ delivered from Microsoft Azure blob storage whose IP range was allow listed by the multiple customers. The malware was identified via telemetry that recently alerted us on a high number of detections. These detections were related to multiple customers in the health and retail sector that recently deployed Netskope Advanced Threat Protection. Before this deployment, the binaries were shared in multiple apps internally across several enterprise users, external users, public, and anyone with a cloud share link. These binaries, which claimed to provide keys and licenses related to popular software, were downloaded in the victims’ machines and synced to cloud storage apps. These files were in turn shared across several users who needed the keys and licenses of that software. Using our clustering mechanism, we also identified similar strains of CapitalInstall across several other customer instances which we detected in the past. This particular variant of CapitalInstall installers were delivered from the same Microsoft Azure blob storage URL and packaged with a bundled adware named ‘Linkury’.
This post describes our discovery and analysis of CapitalInstall and concludes with some recommendations to help protect and remediate such threats.
Netskope Detection
Netskope Advanced Threat Protection detects CapitalInstall samples we identified as SilentInstall.Gen.
Disclosure
The Azure blob storage URL delivering CapitalInstall was reported to Microsoft on 19 November 2018.
Discovery
As mentioned earlier, since the detections were considerably high in number, our Outbreak Detection System triggered malware alerts as shown in Figure 1.
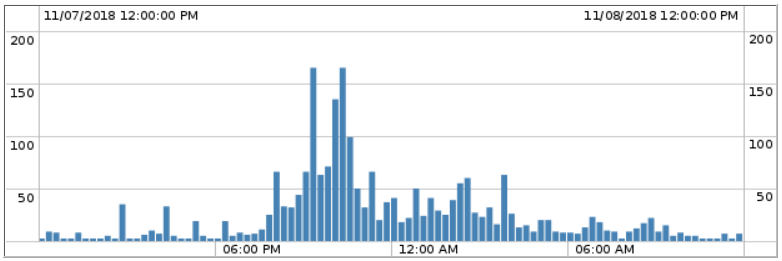
Figure 1: Malware alerts from telemetry
Figure 1 illustrates a surge in the malware alerts from telemetry across several customer instances. The spikes above 100 were caused by the customers that recently deployed Netskope Threat Protection.
After analysis, we confirmed that the detections were related to several known malware, including potentially harmful and unwanted applications. A specific strain,’CapitalInstall’ packaged with an Adware family named ‘Linkury’ with a considerably high number of detections caught our attention. Several samples related to this malware family resident in cloud storage apps were shared across internal and external users and any user with the cloud share link.
Since the detections were high in number and shared across several users, we performed a deeper investigation leading us to the discovery of the Microsoft Azure blob storage link IP range allow listed by the customers that was delivering CapitalInstall binaries.
Delivery
After analyzing all the CapitalInstall binaries related to Linkury, we identified the delivery mechanism to be drive-by-download links from a website that claim to provide keys and licenses related to popular softwares. The drive-by-download links were attributed to several TLDs, which all proceed to fetch the Linkury binary from the same Azure blob storage link, intie[.]blob.core.windows.net.
CapitalInstall – Linkury
CapitalInstall is associated to a family of potentially unwanted applications (PUPs) that the victim might have inadvertently installed in the machine. The application’s network traffic can be easily identified by the User-Agent, ‘InstallCapital’ that is most commonly used by the installers. An example of the packet capture is shown in Figure 2.
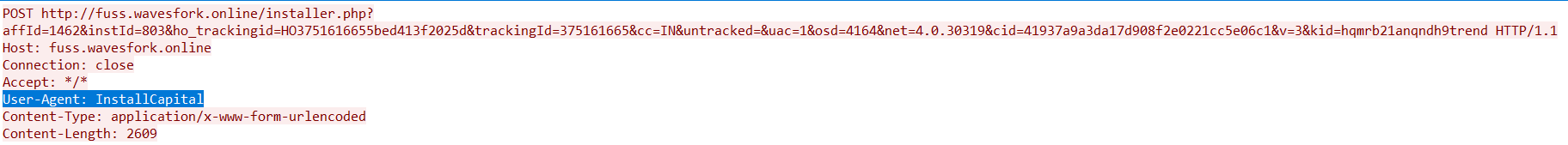
Figure 2: User-Agent: InstallCapital
The potentially unwanted applications are packaged with bundlewares like Linkury. These applications plague the machine with annoying advertisements and download additional unwanted applications.
Malware Analysis
For the analysis, we have taken a software sample that has been downloaded several times by our customer. The sample is an ISO image file named Adobe+CC+2019+Crack.iso delivered from the Azure blob storage link, https://intie[.]blob.core.windows.net/54148/a350ab7c93a511322f4fd0/Adobe+CC+2019+Crack.iso
The iso file, Adobe+CC+2019+Crack.iso contained an executable named Adobe+CC+2019+Crack.exe as shown in Figure 3.
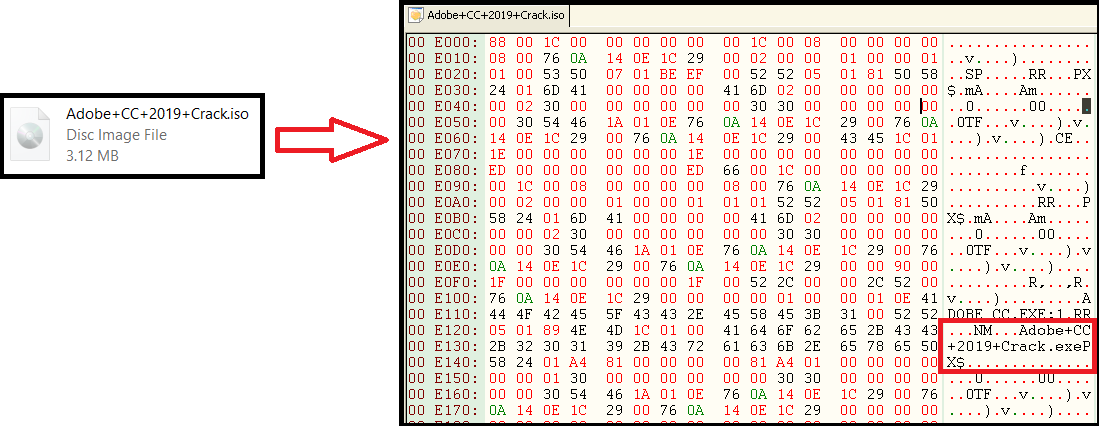
Figure 3: Adobe+CC+2019+Crack.iso embedded with CapitalInstall
The usage of iso image for embedding the CapitalInstall binary was something uncommon for traditional Adware related families.
The embedded binary, Adobe+CC+2019+Crack.exe was compiled with Microsoft Visual C++ 6.0 with an entry point function pointing to WinMain() in Olly debugger is as shown in Figure 4.
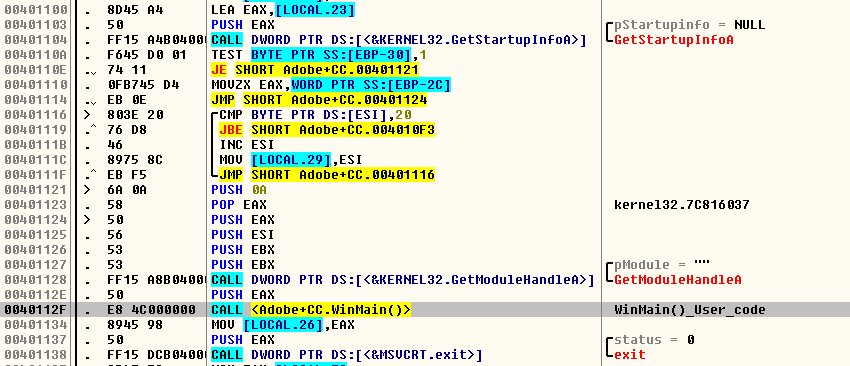
Figure 4: WinMain() of Adobe+CC+2019+Crack.exe in Olly debugger
After stepping in WinMain(), we found the presence of runtime packer code. As the name suggests, runtime packers is a packer that uses executable compression to unpack the executable during execution. Malware authors tend to use this compression in an attempt to thwart traditional Antivirus engines that scan for identifying the malicious code in the executable.
On execution, the installer displays a message to the victim as shown in Figure 5.
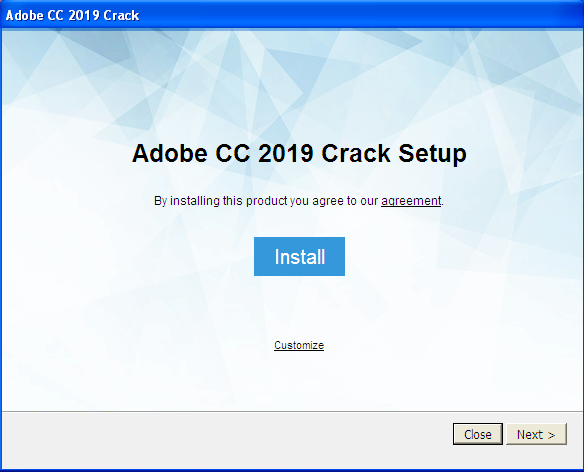
Figure 5: Message displayed on execution
After clicking Next, the victim is then presented with the message from Linkury as shown in Figure 6.
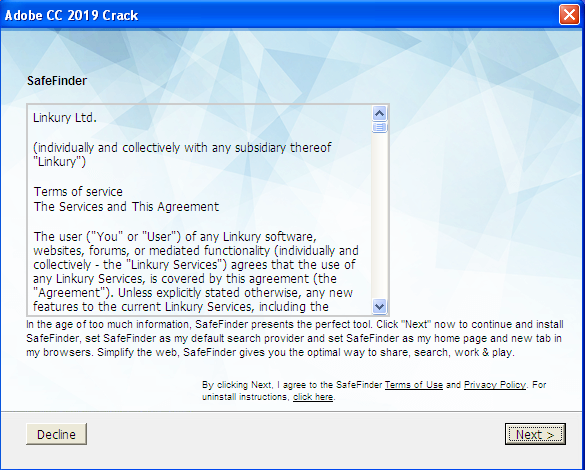
Figure 6: Linkury install message
After clicking on Next, the victim is presented with a message that the installation of the Adobe CC 2019 crack is in progress and then directed to a webpage, http://ic-dc[.]bundlessafevault[.]com/pr/3e07b12e-e7d1-11e6-836f-02e33f60d095/typ_1.html, thanking the download/install of the binary.
Though the crack/key is not installed in the machine, the victim is instead displayed with a web page from swiftviz[.]net to install an unwanted browser search add-on named searchfort (http://www.searchfort[.]online/nlp/lp.html?source=912&clickid=w542O31BFM27RJ8IHON3L46E) as shown in Figure 7.
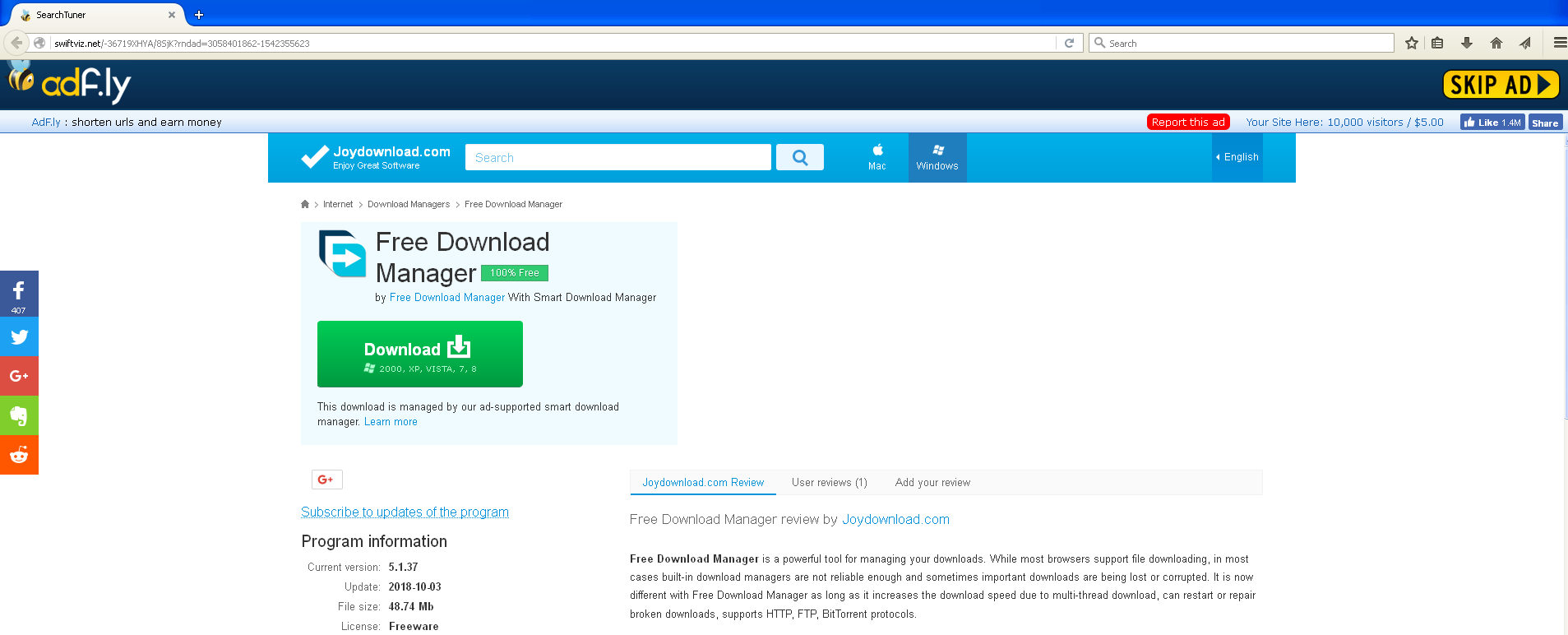
Figure 7: Victim displayed with a page to install searchfort browser add-on
Swiftviz[.]net is a service that lets one earn money for each visitor that visits the shortened links with adf.ly. There are several enticing messages displayed from swiftviz[.]net as shown in Figure 8, 9 and 10.

Figure 8: Message prompting to install CryptoTab

Figure 9: Message prompting to install Olymptrade
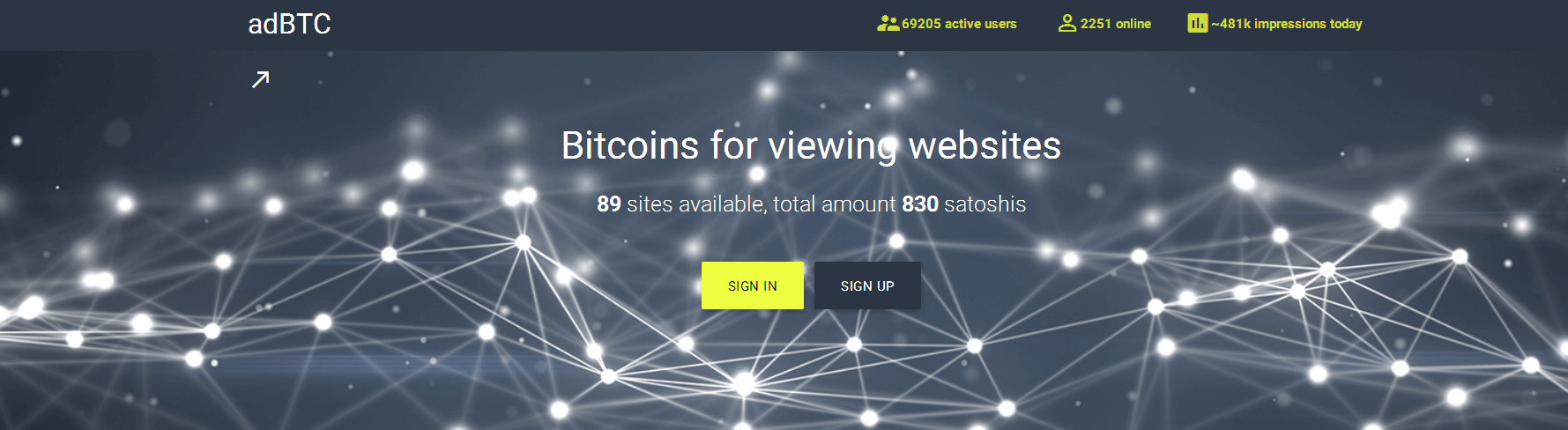
Figure 10: Message prompting to use adBTC
Several of these enticing messages invite the download and install of several unwanted software the victim’s machine.
All the metrics of the web pages displayed to the victim are sent to the website fuss.wavesfork[.]online with the User-Agent: InstallCapital as shown in Figure 11.
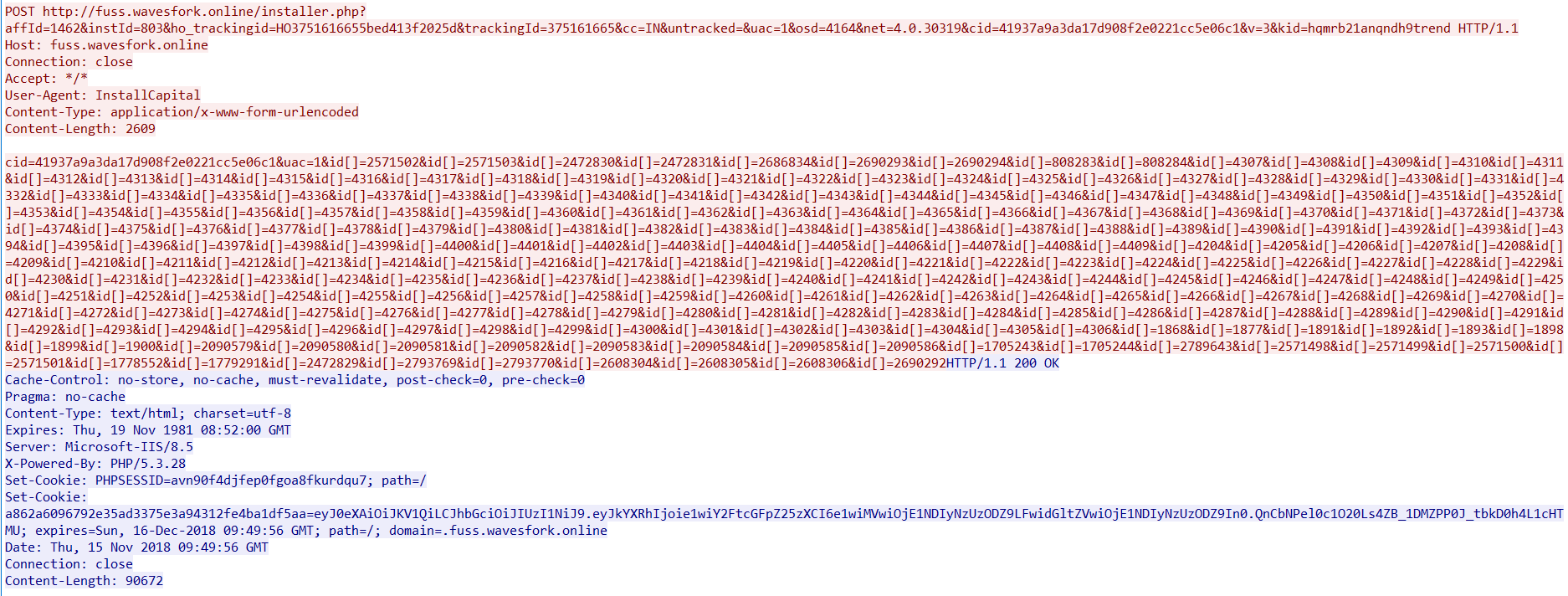
Figure 11: Metrics sent to the website fuss.wavesfork[.]online
Drive-by-download links, Similar strains, and Azure blob storage URL
As we continued to research the similar files using our clustering mechanism, we also identified similar strains of CapitalInstall in several customer instances which we detected in the past. Most of the files were initially delivered from URL’s with TLD’s club, fun, online, us, space, icu, pw, xyz, press, site, host, website, services, accountant, red. Nonetheless, all these were used as placeholders to download the binaries from the Azure blob storage URL, intie[.]blob.core.windows.net. An example of the HTTP traffic delivering the CapitalInstall from Azure blob storage as follows
HTTP headers:
GET /56181/JhdkWGnod56ahkspldunbRYdvpGaWemdFGaqG9Rm3dXRcXu/%5BPiratePCNet%5D%2BDrive%2BSnapShot%2B_%2B_%2BOnlyzip.exe HTTP/1.0
Host: intie[.]blob.core.windows.net:443
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)
Referer: http://playground.hospitalcar[.]fun/JhdkWGnod56ahkspldunbRYdvpGaWemdFGaqG9Rm3dXRcXu/
Accept-Encoding: gzip
Using Virustotal Passive DNS records for the domain intie[.]blob.core.windows.net and our clustering mechanism, we identified close to 2000 unique hashes downloaded from the domain, starting from April 2018.
Conclusion
The advent of new technologies like containers, serverless applications, and SaaS storage are now the new standards of the industry with companies building their entire infrastructure on IaaS providers like Amazon AWS, Google Cloud, and Microsoft Azure. With a major shift of services towards cloud, the dynamics of threats have changed and they have started adapting to this new playground.
The research on CapitalInstall is a classic example of malware being hosted over IaaS for delivering the payload using placeholder websites. We also observed the Azure blob IP was allow listed and the downloaded binaries were shared across several across internal and external users. Generally, allow listing is done to reduce the performance issues introduced by scanners that treat the entire cloud app space equivalently. Organizations that do not have a multi-layered cloud-aware solution for threat detection are particularly vulnerable to attackers hosting malicious files in IaaS object stores.
Enterprises should educate users on the best practices and to refrain from installs, downloads and accessing any website promoting cracks, keys, and licenses of popular software. Enterprise Administrators and Users must also be educated on the implications of allow listing IP’s and sharing files across users.
Netskope Advanced Threat Protection with its unique cloud vantage point combined with multi-layered threat detection and remediation capabilities offers customers a cloud scale platform that understands, protects and responds such attacks




 戻る
戻る
















 ブログを読む
ブログを読む