Google Forms is one of the preferred tools used by cybercriminals to quickly set up and deliver phishing pages. We have seen examples of Google Forms pages mimicking Microsoft Office 365 logins (one of the preferred imitated applications), financial institutions like American Express, and in general any applications. Despite the naïve layout, the tool is flexible enough to build an (un)realistic login page with few clicks. Additionally, the Google infrastructure simplifies the operational tasks of the infrastructure (no need to register a domain for example) and as a plus, it also offers Gmail, a precious tool to deliver the phishing page directly to the victim’s mailbox, bypassing the security controls of traditional email security gateways.
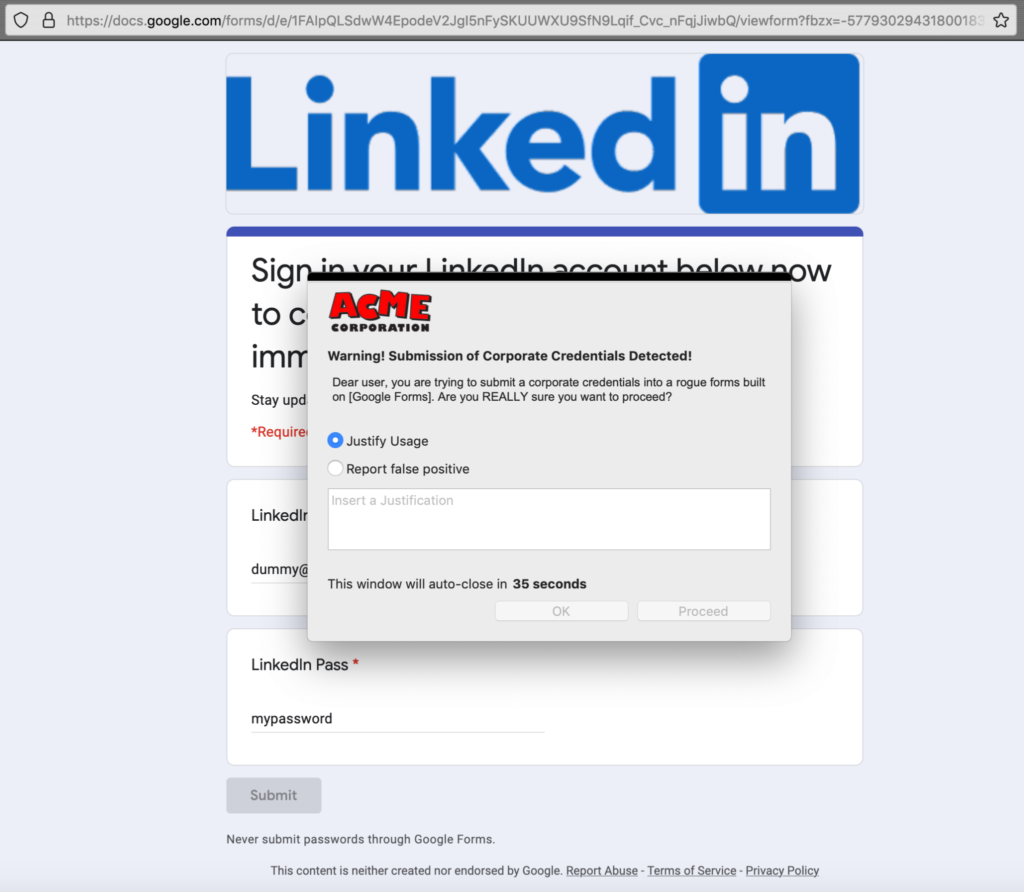
With such a powerful set of capabilities exploitable by threat actors, it comes as no surprise that new phishing pages imitating more and more applications are built on Google Forms. In the latest campaign, discovered by Armorblox, the platform has been abused to launch a campaign harvesting LinkedIn credentials. To make the campaign even more evasive, the link to the phishing page has been sent via a compromised email account. It took me literally two minutes to build a page like the one used in this attack (and much less to create a simple universal policy to block it as shown below). And, once again, don’t hope that naïve layout and the explicit disclaimer keep the user from falling into the trap: similar harvesting campaigns occur and succeed on an hourly basis.
How Netskope mitigates the risk of cloud phishing
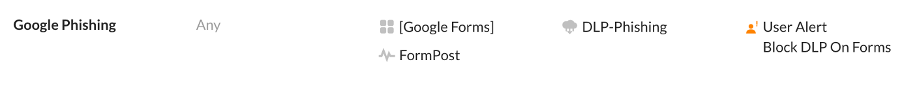
The Netskope Next Generation Secure Web Gateway provides granular visibility for Google Forms, Microsoft Forms, and hundreds of additional cloud applications (besides web traffic), allowing you to enforce DLP and threat protection. This visibility is a real differentiator in the current scenario where, according to our Cloud and Threat Report: July 2021 Edition, 67% of malware is delivered from the cloud, and 66.4% of this cloud-native malware is distributed from storage apps. In this specific case, it is possible to create a simple DLP policy that prevents the submission of specific information inside the rogue form. The following policy warns the users if they are submitting a corporate domain (dummy.com) into an unrecognized Google Forms page (and the outcome is shown above, this coaching action is critical to alert the users if they are performing any potential harmful actions in a cloud app or web page without necessarily blocking the traffic and hence limiting the occurrence of false positives). The domain “dummy.com” is the custom identifier used in the “DLP-Phishing” custom rule. Of course, it is possible to use a more sophisticated DLP profile combining one or more custom identifiers with any of the 3,000 predefined ones, and also to enforce a more restrictive block action. Don’t forget that cloud phishing is also one of the core differentiators of our ProveIt campaign.
Additionally, the UEBA component in the CASB module can mitigate the risk of compromised cloud accounts exploited to launch phishing campaigns or perform any other malicious activities.
Stay safe!




 Back
Back
















 ブログを読む
ブログを読む