Summary
Netskope Threat Labs is tracking multiple phishing campaigns that abuse Cloudflare Workers. The campaigns are likely the work of different attackers since they use two very different techniques. One campaign (similar to the previously disclosed Azorult campaign) uses HTML smuggling, a detection evasion technique often used for downloading malware, to hide the phishing content from network inspection. The other uses a method called transparent phishing, where the attacker uses Cloudflare Workers to act as a reverse proxy server for a legitimate login page, intercepting traffic between the victim and the login page to capture credentials, cookies, and tokens.
Netskope Threat Labs has been tracking an increasing number of Netskope users targeted by malicious content hosted in Cloudflare Workers throughout 2023 and into 2024. The number of targeted users appears to have leveled off so far in 2024, although the number of domains continues to increase. At the same time, the distinct number of applications hosting the malicious content continues to increase, indicating that attackers are constantly creating new apps to evade detections and takedowns.
Over the past 30 days, phishing campaigns hosted on Cloudflare Workers have primarily targeted victims in Asia, North America, and Southern Europe, across multiple segments led by technology, financial services, and banking. The majority of the phishing pages Netskope Threat Labs has uncovered target Microsoft login credentials, with Gmail, Yahoo Mail, and cPanel Webmail among the other targets.
Abusing free cloud services to host malicious content, including malware and phishing pages, is a common practice among adversaries. Our most recent Threat Stats post highlights that no cloud apps are immune to such abuse and that abusive content hosted on the most popular apps tends to be most successful in reaching its victims.
Let’s take a closer look at these campaigns:
Cloudflare Workers serving phishing sites
Cloudflare Workers is a serverless computing platform for application deployment, including serving HTML pages to visitors. Cloudflare Workers is available to free tier users and therefore abused by attackers who continuously abuse free cloud services. With a free tier account, attackers can create multiple Cloudflare Worker applications that can serve up to 100,000 access a day from their victims, using a free publicly accessible domain and a valid TLS certificate. Netskope Threat Labs has previously written about the abuse of other free services, including Cloudflare R2.
Netskope Threat Labs first observed an increase in traffic to phishing pages hosted in Cloudflare Workers in Q2 2023 and spiking in Q4 2023. So far in 2024, the number of users targeted with malicious content hosted in Cloudflare Workers appears to have leveled off, but we are still seeing thousands of Netskope users attempting to access malicious content hosted in Cloudflare Workers each quarter.

At the same time, the number of distinct malicious applications that Netskope users are attempting to visit is growing. Each application has a distinct domain of the format https://{application-name}.workers.dev. The following graph shows the number of distinct domains to be steadily increasing throughout 2023 and into 2024 and has not yet leveled off.

Phishing pages smuggled through Cloudflare Workers
Several phishing campaigns hosted in Cloudflare Workers use HTML smuggling to deliver phishing pages to their victims. As described in our previous blog post, HTML smuggling is a defense evasion technique that attempts to bypass network controls by assembling the malicious payloads on the client side. In that post, the attacker saved the malicious payloads to the disk for the victim to execute. In this case, the malicious payloads are the phishing pages themselves, so the attacker simply reconstructs them and displays them in the browser. In both cases, the objective is to try to evade network-based defenses.
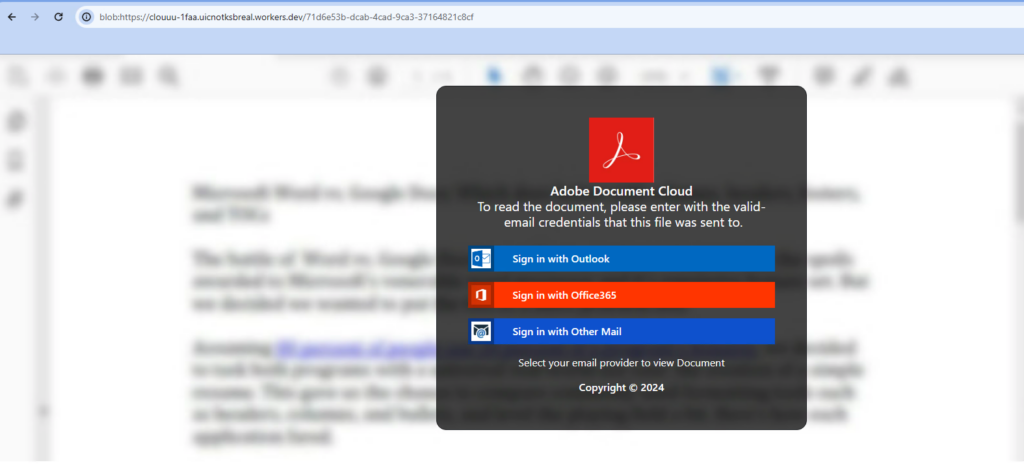
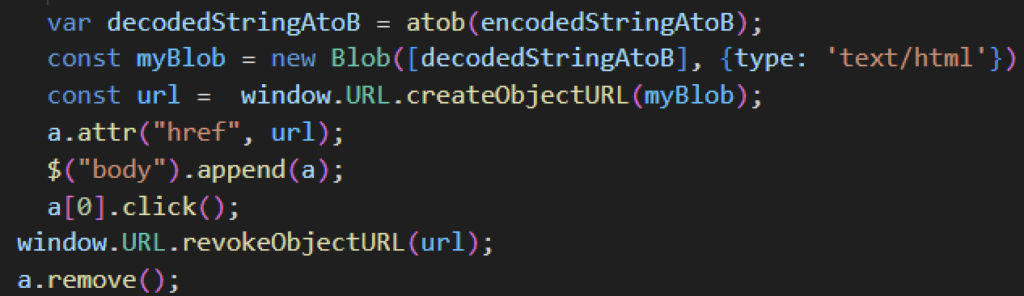
The attackers have embedded the actual phishing page as a blob inside a benign web page. The phishing page is initially encoded in base64 and then encoded multiple additional times to obfuscate the code and avoid static detection. To make the blob object accessible in the endpoint, they use the createObjectURL() method to create a blob URL. Then, they simulate a click on the blob URL using the click() method.
Transparent phishing hosted in Cloudflare Workers
Conventional phishing involves attackers crafting their own phishing pages that replicate legitimate login pages to trick their victims into providing their login credentials. However, the traditional approach now has some pitfalls. First, the attacker has to constantly keep their phishing page up-to-date to mimic the look and functionality of the legitimate website. Second, and more importantly, they need to overcome whatever multi-factor authentication is in place.
These traditional phishing flaws are addressed by transparent phishing. Transparent phishing, or adversary-in-the-middle phishing, is a relatively new form of phishing where the attacker creates a server that acts as an intermediary between the authenticating service and the victim. When victims enter their login credentials and multi-factor authentication code, the transparent phishing servers will collect and forward them to the target application, successfully logging the victim into the app while collecting credentials, cookies, and tokens along the way. And, unlike traditional phishing which copies the login page, the transparent phishing page will show the exact content of the legitimate login page.

Netskope Threat Labs replicated some of the transparent phishing pages hosted in Cloudflare to better understand how they work and how to defend against them. The entire phishing page is created using a modified version of an open-source Cloudflare MITM toolkit. The attacker sets up a Cloudflare application using the “Hello World” Worker template that listens for fetch events using the addEventListener() method. Once the victim accesses the attacker’s login page, the attacker collects its web request metadata, including the HTTP request method, region, IP address, and headers, and uses it to send the request on behalf of the victim to the legitimate page.
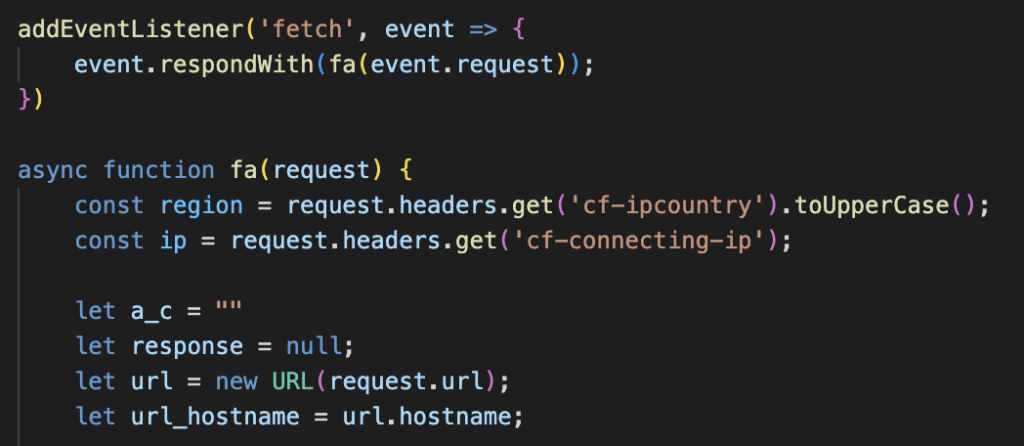
The attacker’s application will also collect the legitimate site’s response to the victim’s request and display it to the victim. Prior to showing the response, the domain of the legitimate site will be replaced with the application’s domain.

The application will then collect the victim’s login credentials, which will subsequently be sent to the attacker either using Cloudflare webhook notification or through HTTP. Once the victim enters their credentials, they will be logged in to the legitimate website, and the attacker will collect the tokens and cookies in the response. Furthermore, the attacker will also have visibility into any additional activity the victim performs after login.

Conclusions
Cloudflare Workers is a platform that enables its users to execute serverless functions, including serving web pages to its visitors. Over the past year, Netskope Threat Labs has tracked an increase in traffic to phishing pages hosted on the service, including campaigns that use HTML smuggling to evade detection and other campaigns that use transparent, man-in-the-middle phishing pages to bypass MFA. Netskope Threat Labs will continue to monitor malicious traffic towards Cloudflare Worker applications and report phishing and other malicious content to Cloudflare to be taken down.
Recommendations
The scams and phishing pages described in the post are easily recognizable by the domain pattern *.workers.dev. Users can avoid becoming victims of the attacks described in this post by checking the URL. Users should always access important pages, such as their banking portal or webmail, by typing the URL directly into the web browser instead of using search engines or clicking any other links.
Netskope Threat Labs recommends that organizations review their security policies to ensure that they are adequately protected against these and similar phishing pages and scams:
- Inspect all HTTP and HTTPS traffic, including all web and cloud traffic, to prevent users from visiting malicious websites. Netskope customers can configure their Netskope NG-SWG with a URL filtering policy to block known phishing and scam sites, and a threat protection policy to inspect all web content to identify unknown phishing and scam sites using a combination of signatures, threat intelligence, and machine learning.
- Use Remote Browser Isolation (RBI) technology to provide additional protection when there is a need to visit websites that fall in categories that can present higher risk, like Newly Observed and Newly Registered Domains.
IOCs
All the IOCs related to this campaign can be found in our GitHub repository.




 Back
Back
















 Read the blog
Read the blog