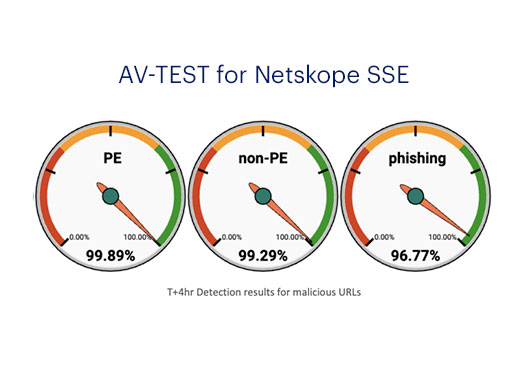
Netskope One Threat Protection uses a multi-layered approach including inline machine learning (ML)-based defenses to detect unknown phishing attacks, unknown malicious portable executable (PE) files, HTML smuggling attacks, AV and web-based IPS signature detection, multiple threat intelligence feeds, shared threat indicators of compromise (IOCs) between customer defenses using Cloud Threat Exchange, de-obfuscation and unpacking, pre-execution heuristics and ML analysis of Office files, cloud sandboxing with MITRE analysis, patient zero protection to sandbox and ML analyze files allowing only benign downloads, plus patient zero retrospective alerts on new detections and detecting compromised credentials found on the dark web. These layers allow the platform to stop threats at every stage of a cyberattack.




 Back
Back

















)
)