Summary
Netskope Threat Labs is tracking a 17x increase in traffic to malicious web pages hosted on DigitalOcean in the last six months. This increase is attributed to new campaigns of a known tech support scam that mimics Windows Defender and tries to deceive users into believing that their computer is infected. The end goal of this scam is to lure victims into calling a fake “help line”, where attackers may attempt to remotely access the victim’s computer to either install malware or request payment for a service to fix the bogus infection.
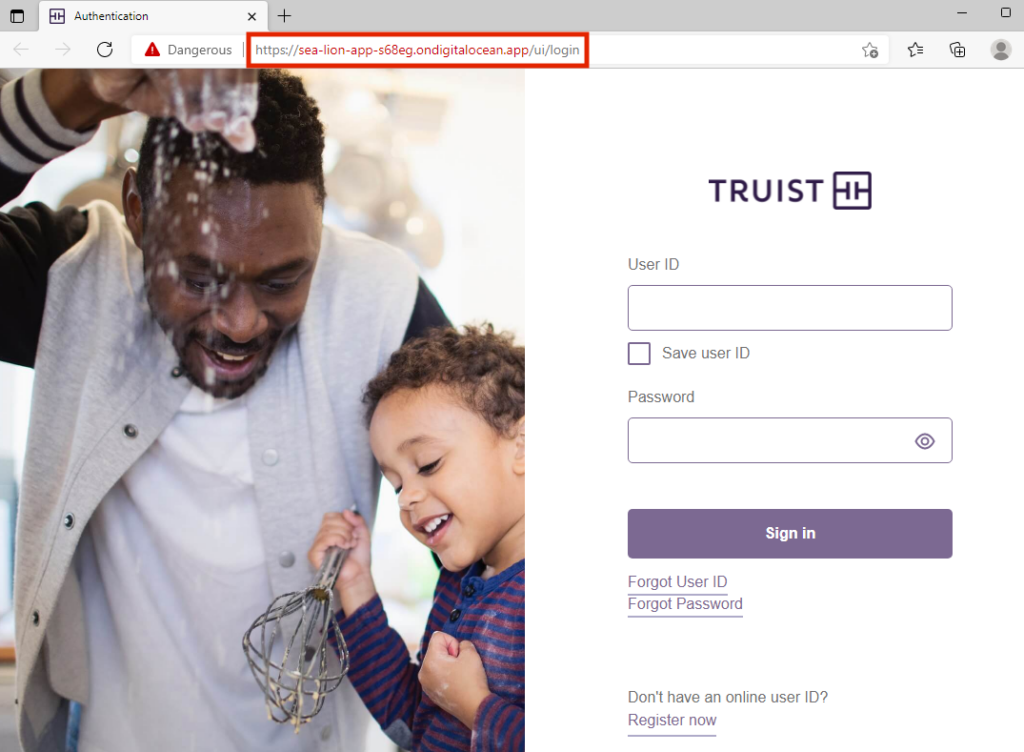
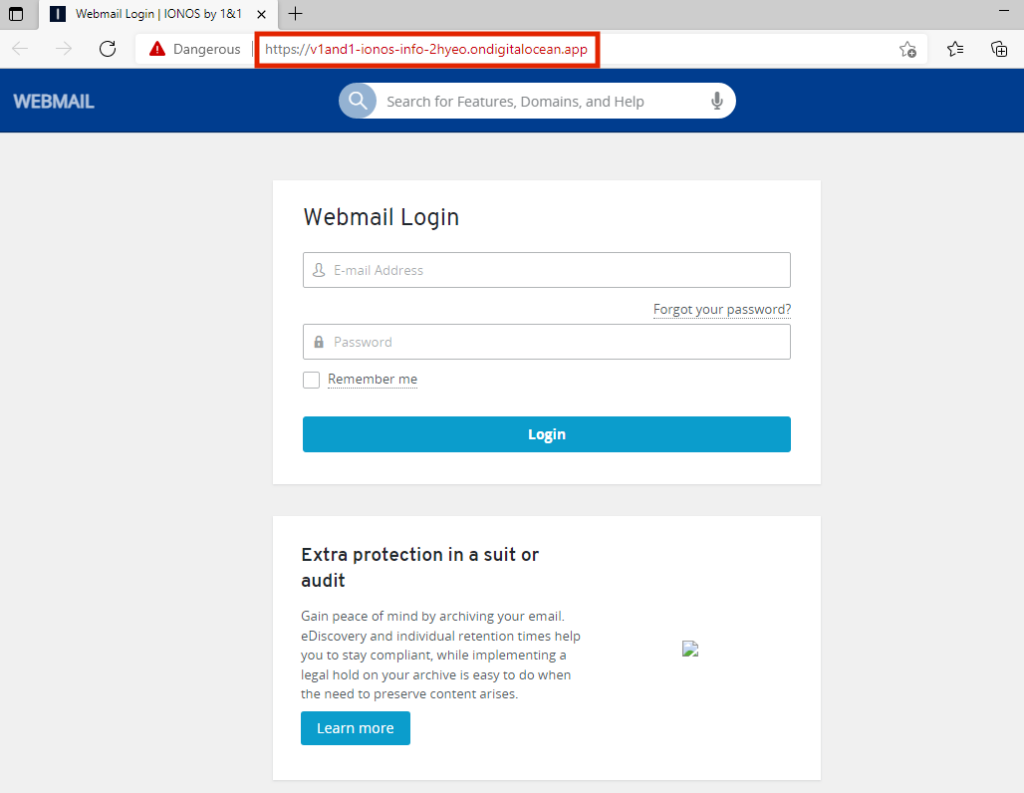
In addition to the tech support scam, there has also been an increase in phishing pages hosted on DigitalOcean, targeting customers of the financial institutions America First Credit Union, Huntington, and Truist, and one phishing page targeting IONOS Webmail users.
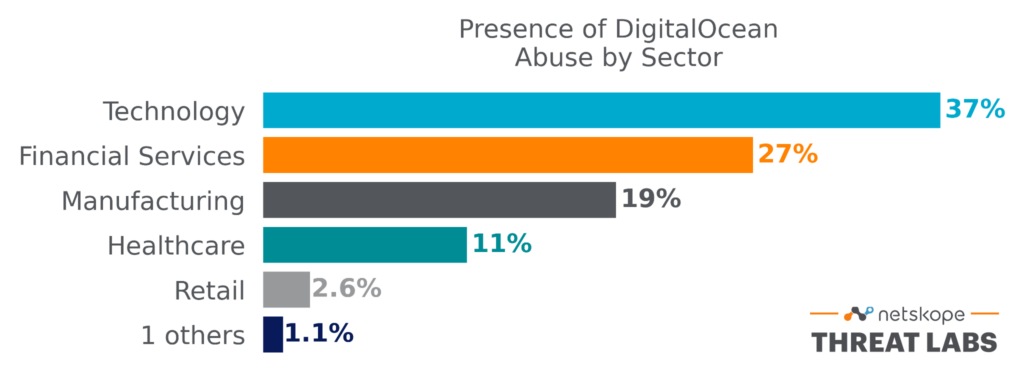
The attacks have been targeting victims mainly in North America and Europe across different segments, led by the technology, financial services, and manufacturing sectors.
Attackers are creating free-tier DigitalOcean apps to host the scam and phishing pages. Abusing free cloud services, especially services that provide free web hosting or free object hosting, is a common technique used by attackers to host malicious content. This blog post provides a summary of what these scams and phishing pages look like, along with recommendations and threat intel you can use to protect yourself and your organization.
Tech Support Scam
How it Works
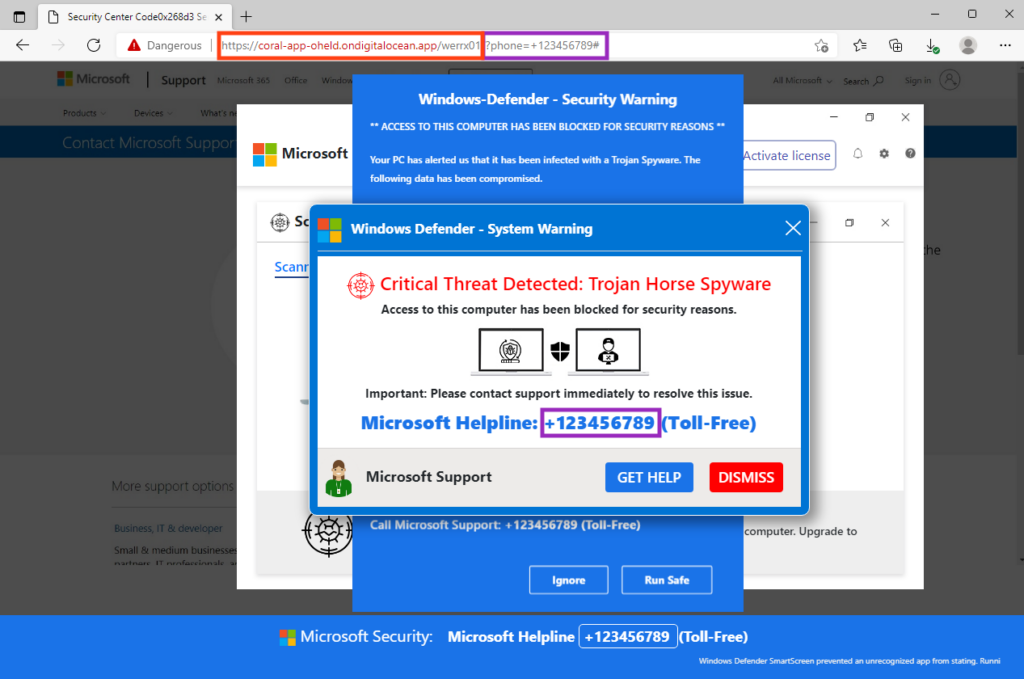
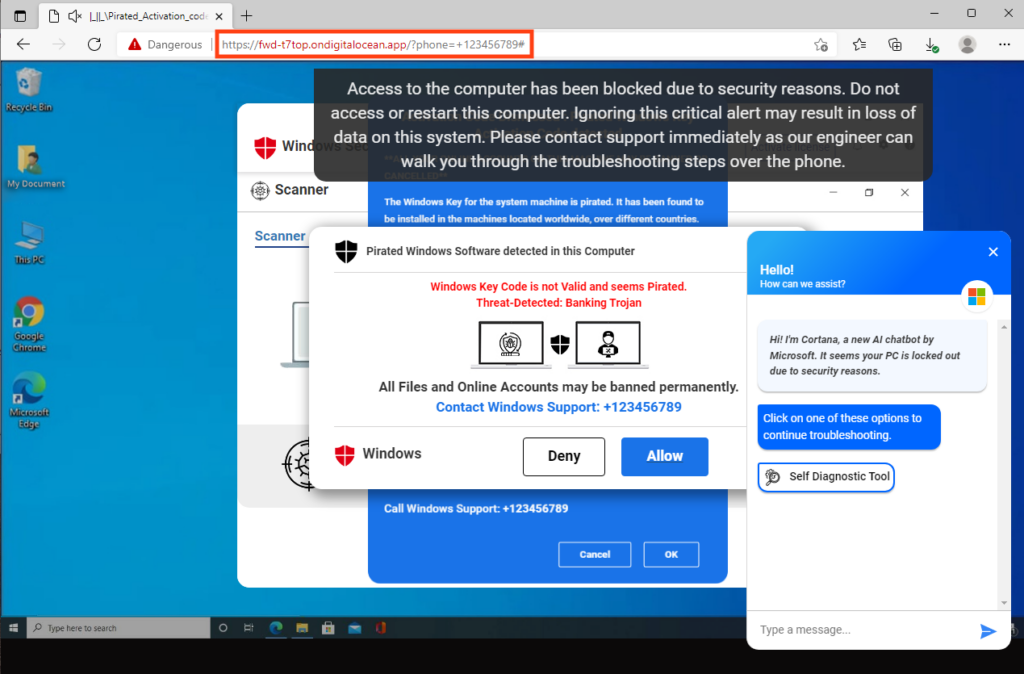
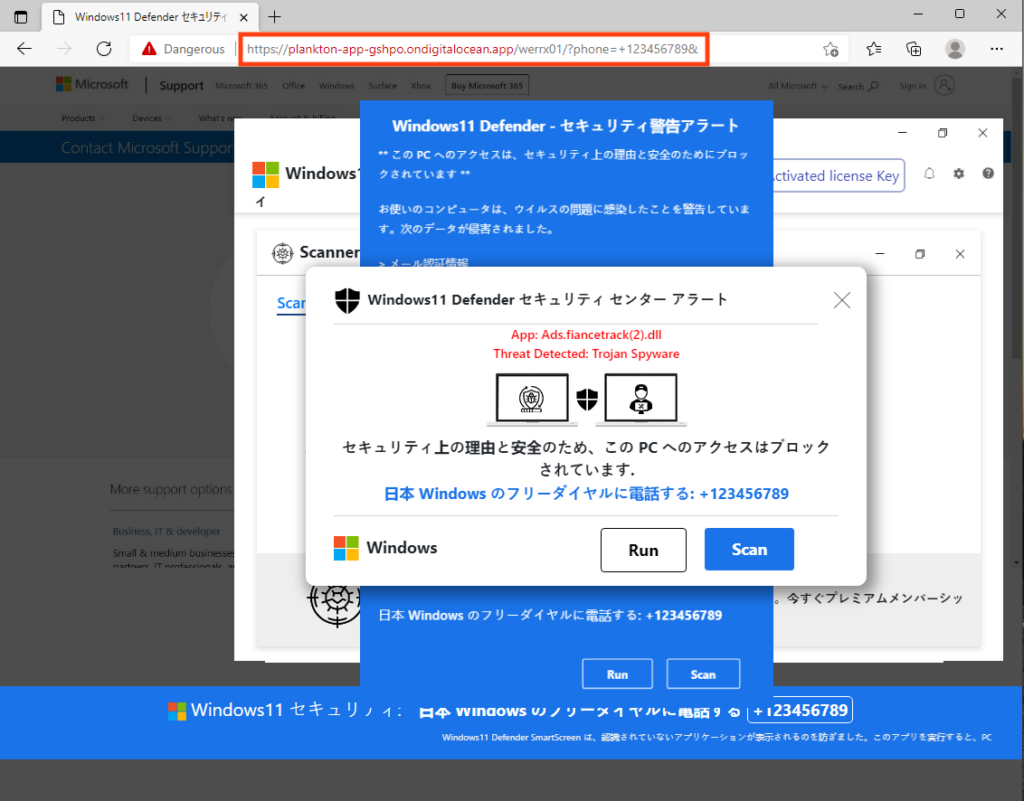
This scam works by mimicking Windows Defender alerts, luring victims into believing that their computer is infected with malware. The goal of this attack is to convince the victim to call the scammer’s phone number. Attackers may attempt to remotely access the victim’s computer to either install malware or request payment for a service to fix the bogus infection. Attackers typically use malvertising to redirect victims to these scam pages.
Once the victim interacts with the webpage, the web browser’s window is maximized and an audio starts playing with the following message:
“Important security message.
Your computer has been locked up.
Your IP address was used without your knowledge or consent to visit websites that contain identity theft virus.
To unlock the computer, please call support immediately.
Please, do not attempt to shutdown or restart your computer. Doing that may lead to data loss and identity theft.
The computer lock is aimed to stop illegal activity.
Please, call our support immediately.”
These are all attempts to scare victims and force them to call the attacker’s phone number. The campaigns Netskope Threat Labs has identified all use different “themes”, but rely on the same technique. For example, below is an example that shows a fake Windows desktop in the background and a fake webchat, which eventually displays a message saying that there’s an error and asks the victim to contact the phone number instead of the chat.
We also found pages in different languages such as Japanese, showing that this is a multilingual campaign.
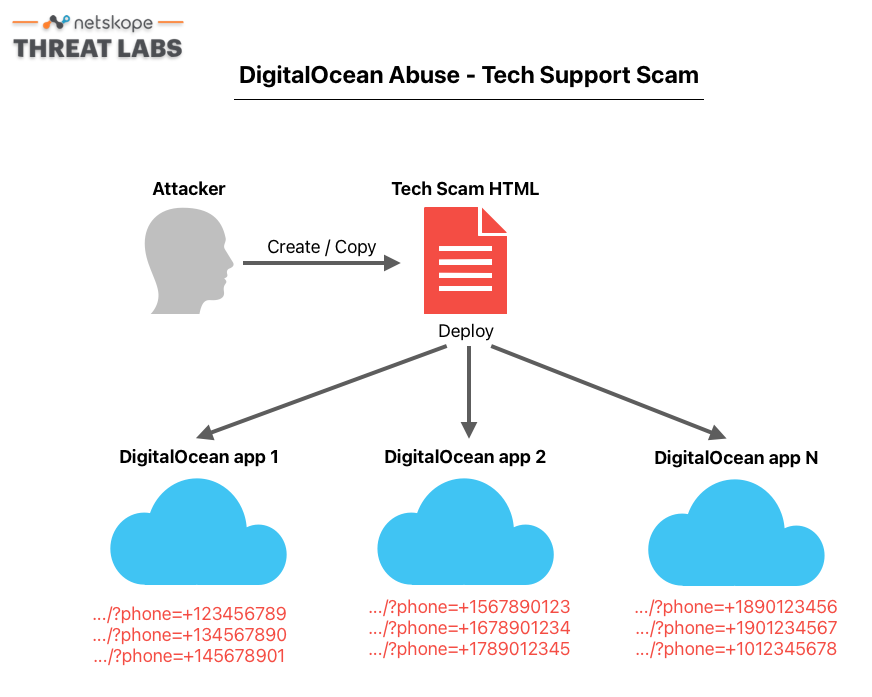
How is it spread across DigitalOcean?
DigitalOcean allows users to host up to three static websites for free. Since the phone number displayed on the tech scam page is dynamic and can be changed via the “phone” parameter in the URL, attackers can use different phone numbers in the same DigitalOcean instance, without changing anything in the HTML or the scripts. This also means that attackers can create multiple DigitalOcean instances and replicate the same HTML and script files, as these do not require any changes.
In the example below, we used fake numbers to illustrate how this works.
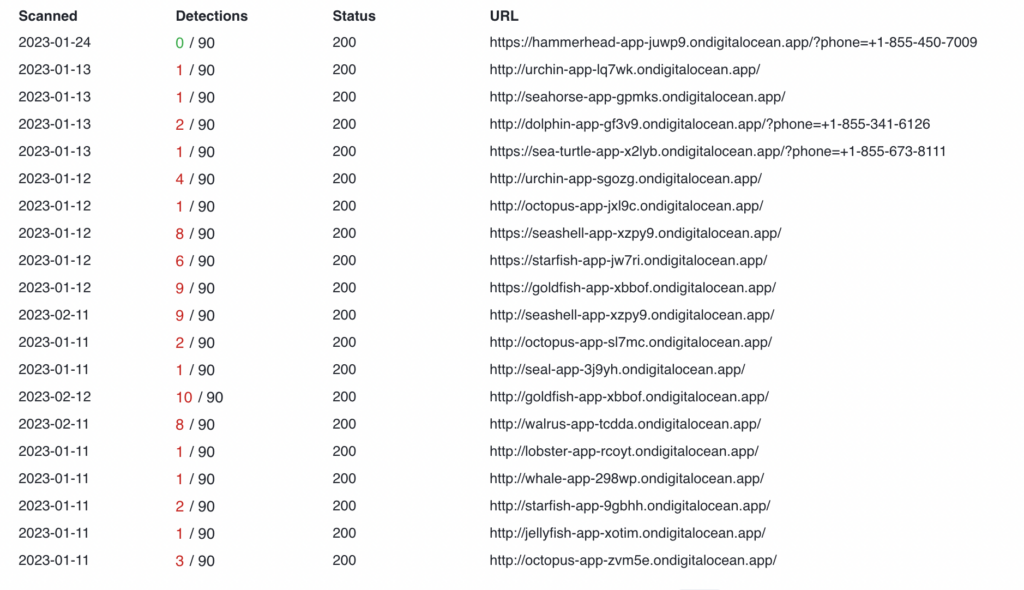
This can also be confirmed by checking VirusTotal. For example, one of the pages we analyzed is related to 87 different domains from DigitalOcean.
Although Netskope Threat Labs has been tracking attackers abusing DigitalOcean in these campaigns, there are also recent reports of similar scams where attackers are abusing Microsoft Azure to host the pages.
Phishing Pages
Netskope Threat Labs is also tracking an increase in phishing activity hosted on DigitalOcean, focused primarily on stealing sensitive financial data, like credit card and debit card numbers.
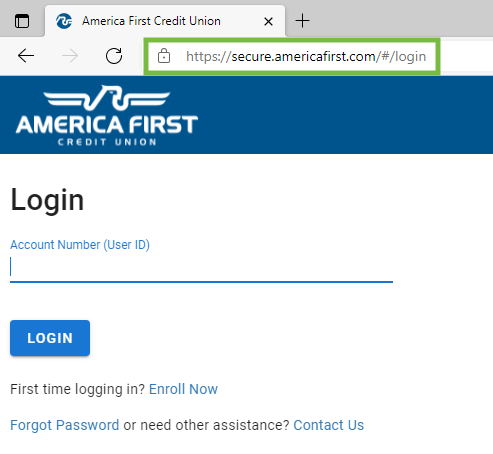
America First Credit Union
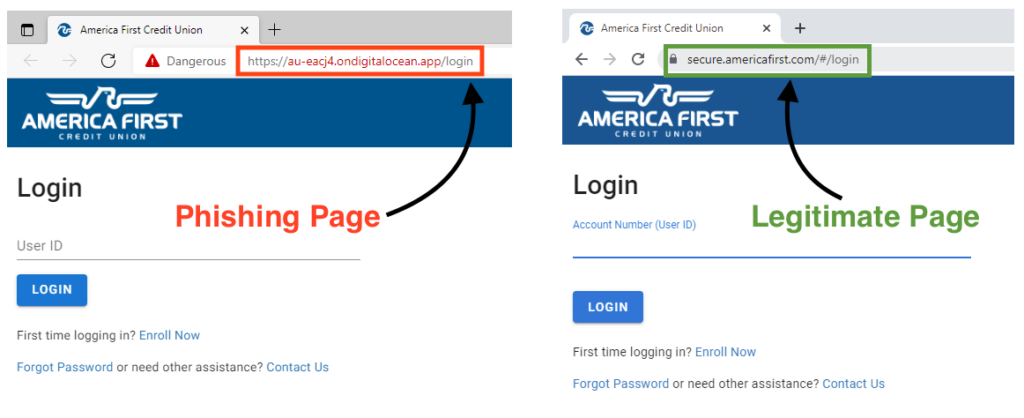
One of the targets is America First Credit Union, where attackers created a very similar phishing page compared to the original website. Although the page looks very similar, one can easily distinguish between the original website by checking the URL.
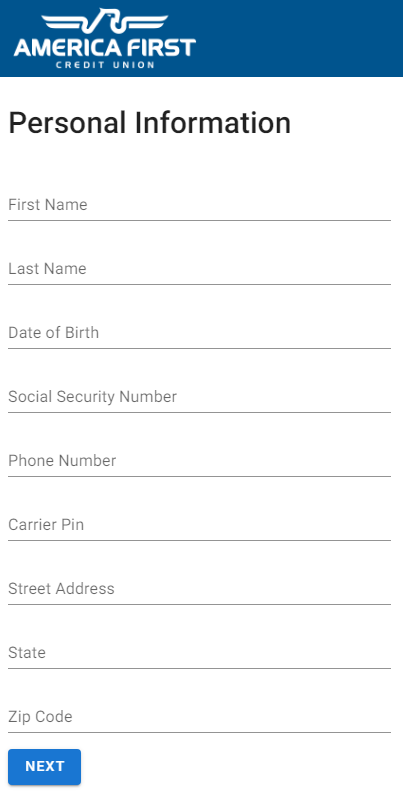
Once the victim adds the login information, the attackers attempt to steal more personal information like the victim’s full name, date of birth, social security number, carrier pin, and the address.
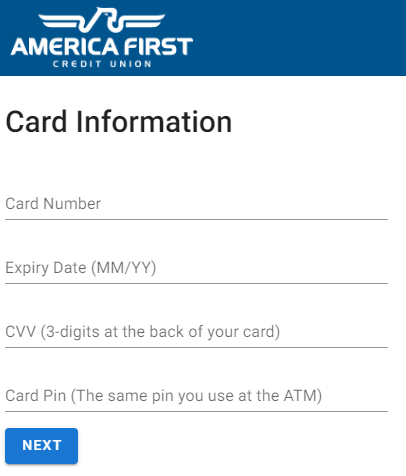
After entering all the data above, the page then asks for the victim’s debit card number, expiration date, CVV, and the card pin.
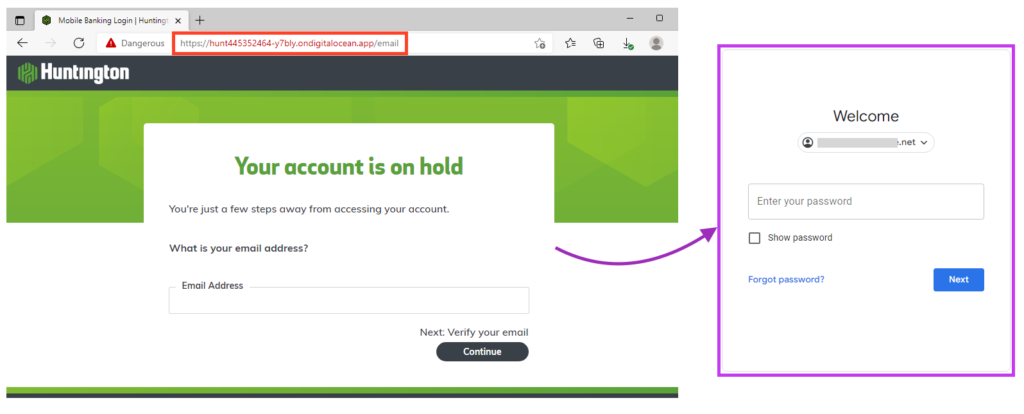
Then, the phishing page attempts to steal the victim’s email address and password. This is done by simulating a third-party login after inserting the email address in the phishing page. Attackers try to take over the victim’s email in order to gain control over the account’s MFA, if enabled. The access to the victim’s email also allows attackers to attempt to reset passwords and gain access to other accounts that are linked to the same email address.
As an extra attempt to deceive the victim, the phishing page tries to simulate the login page according to the email address provided by the user. For example, if a Gmail account is detected, the phishing page simulates Google’s login page.
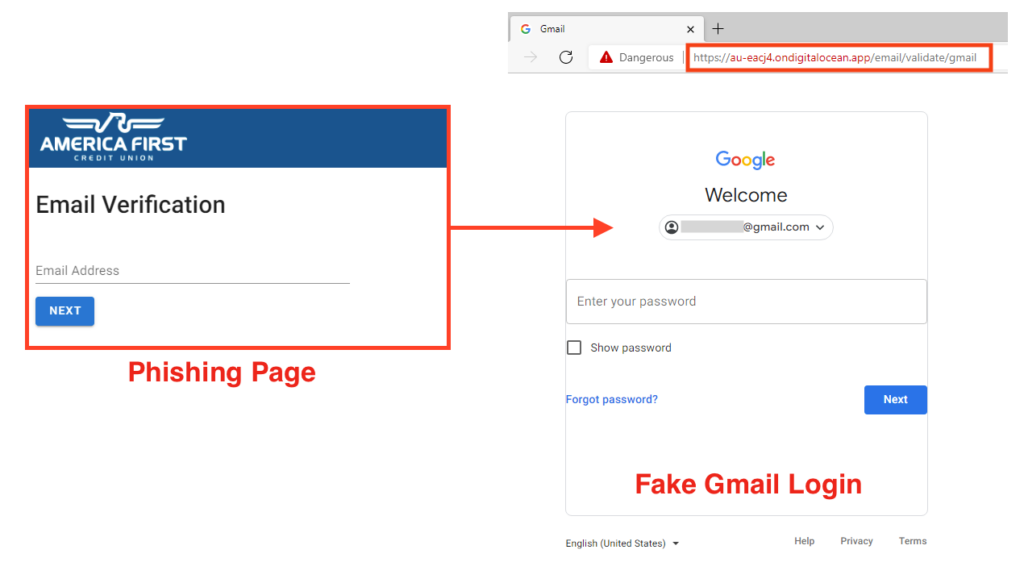
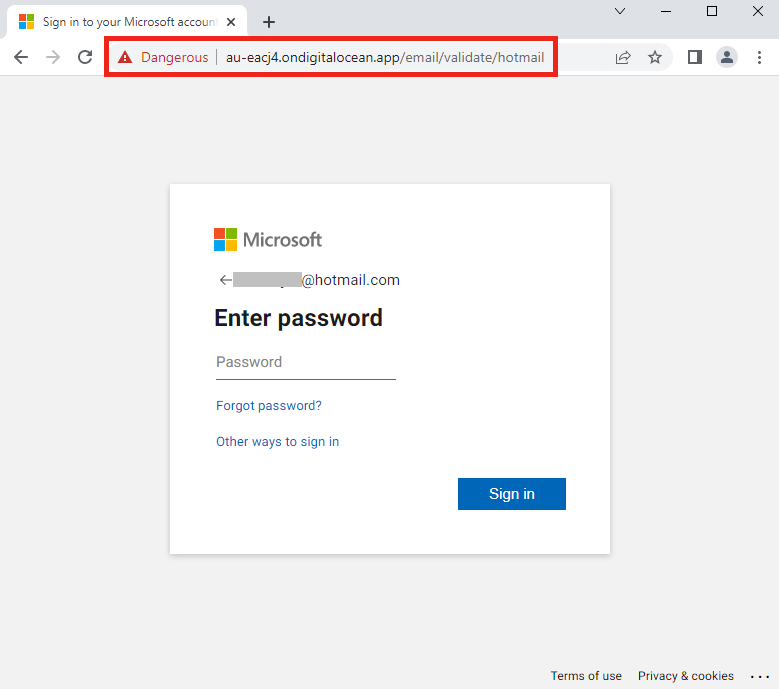
The same thing happens if a Microsoft email is detected.
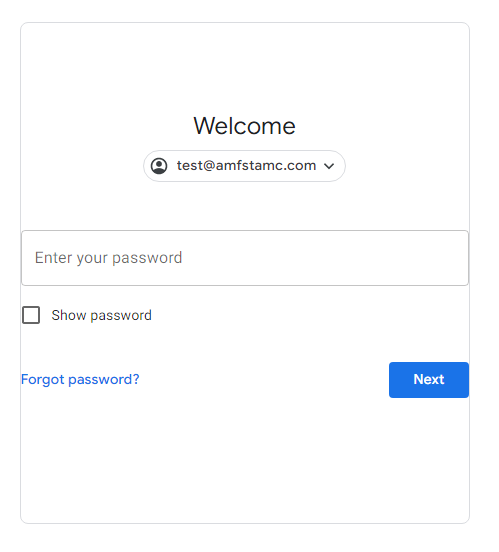
If the email provided by the victim is not from a known service, the phishing page uses the same layout as the one used for Gmail, but without Google’s logo.
And lastly, the victim is redirected to the legitimate website.
Huntington National Bank
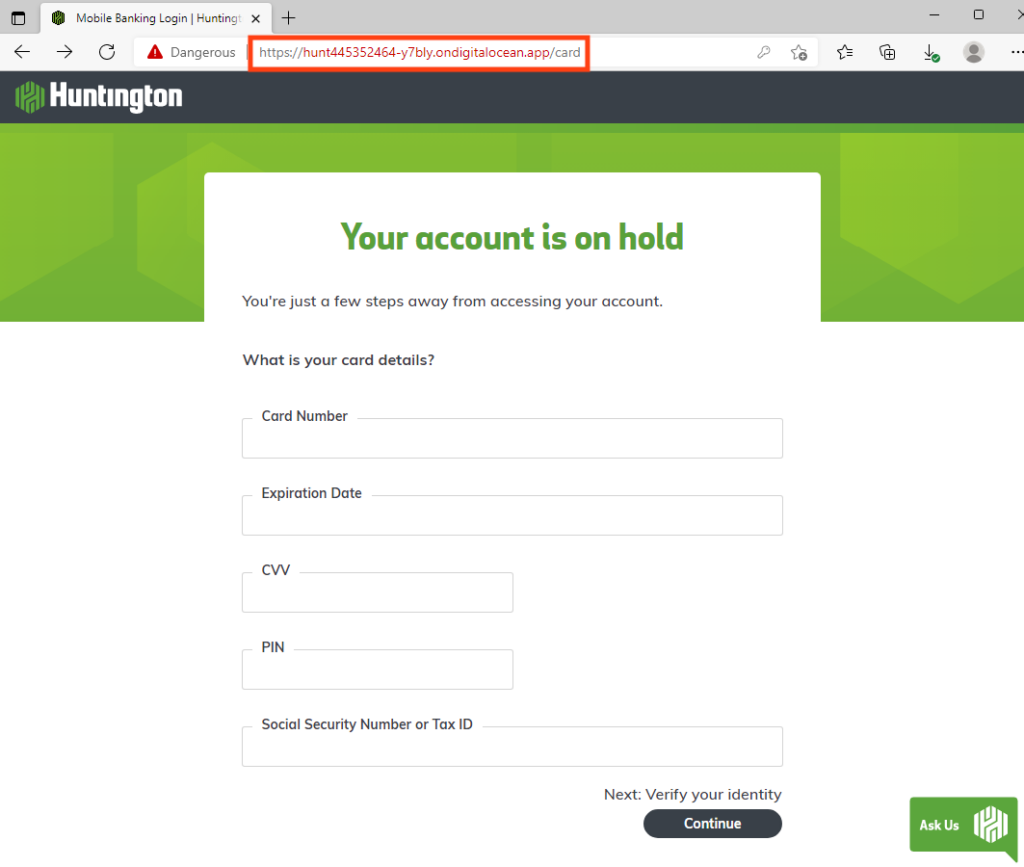
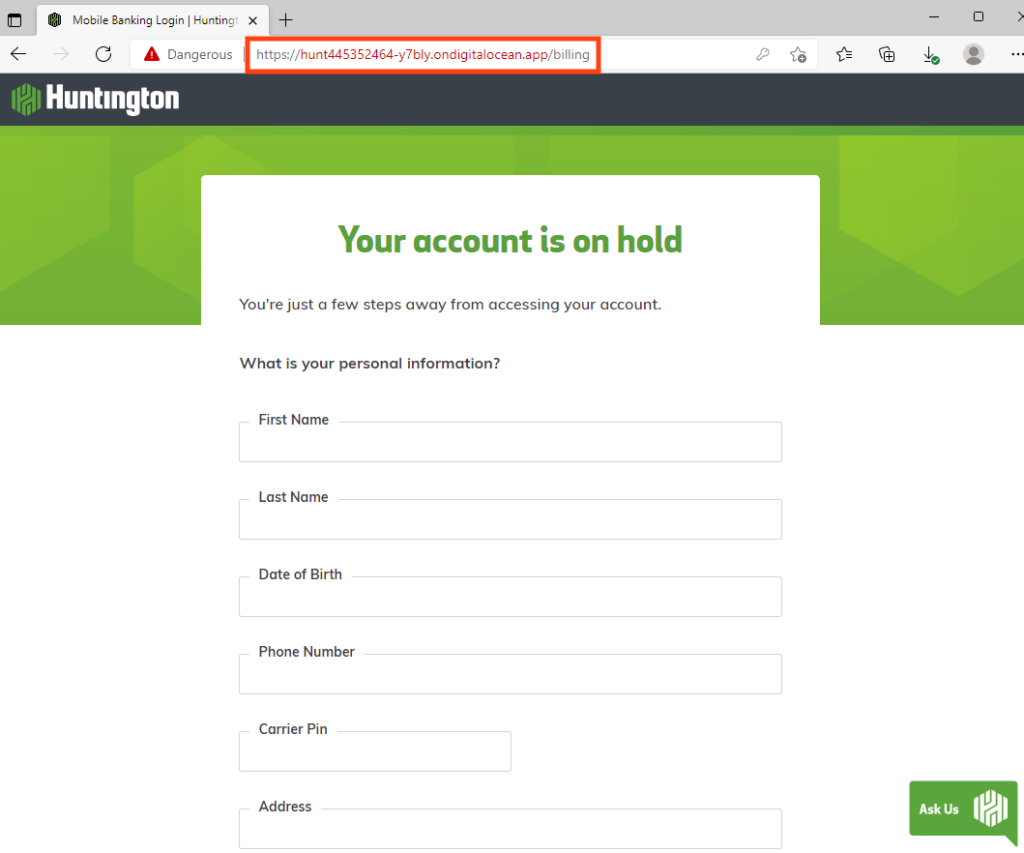
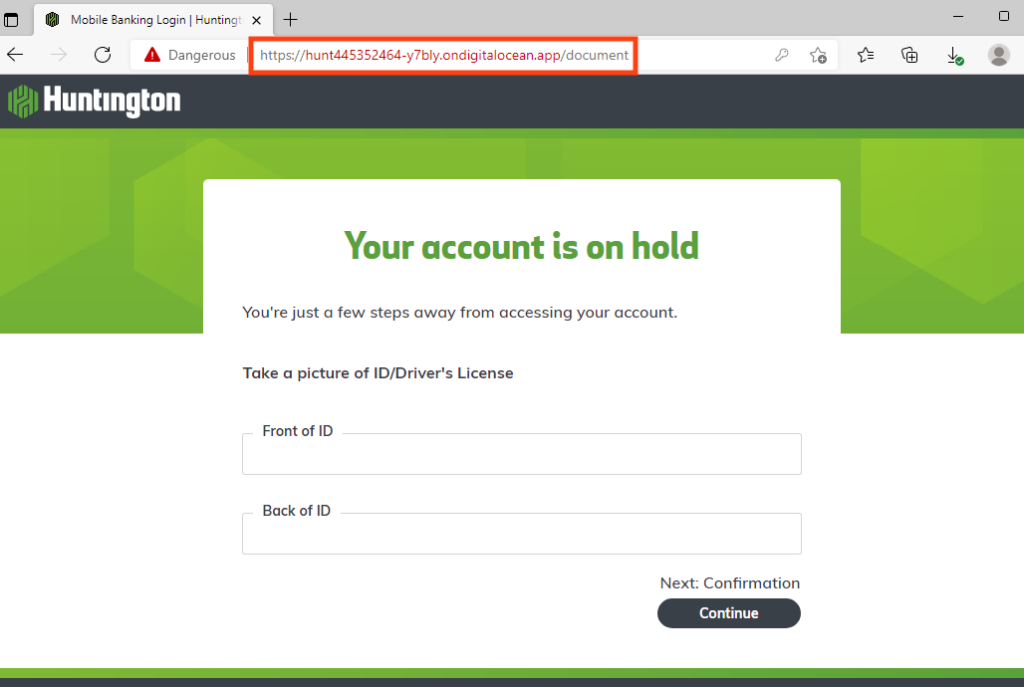
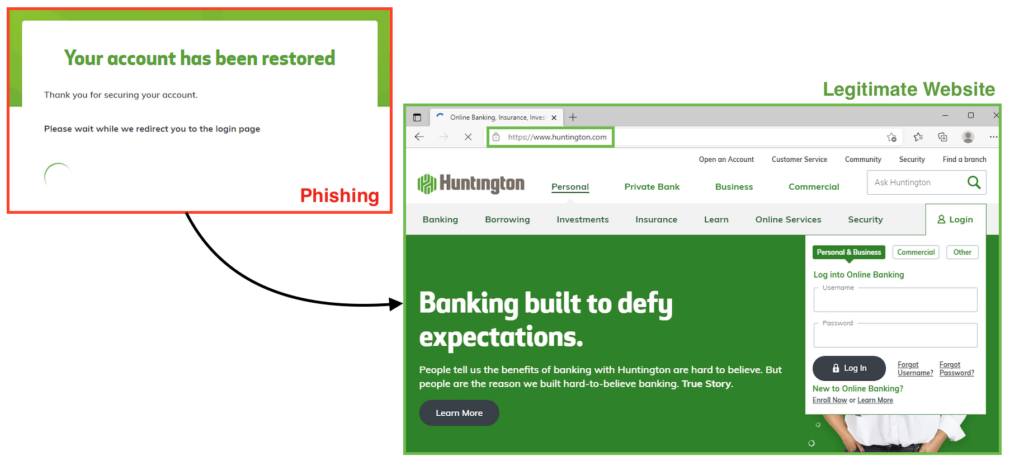
The second target is Huntington National Bank, where the attack flow is similar to the America First’s phishing page.
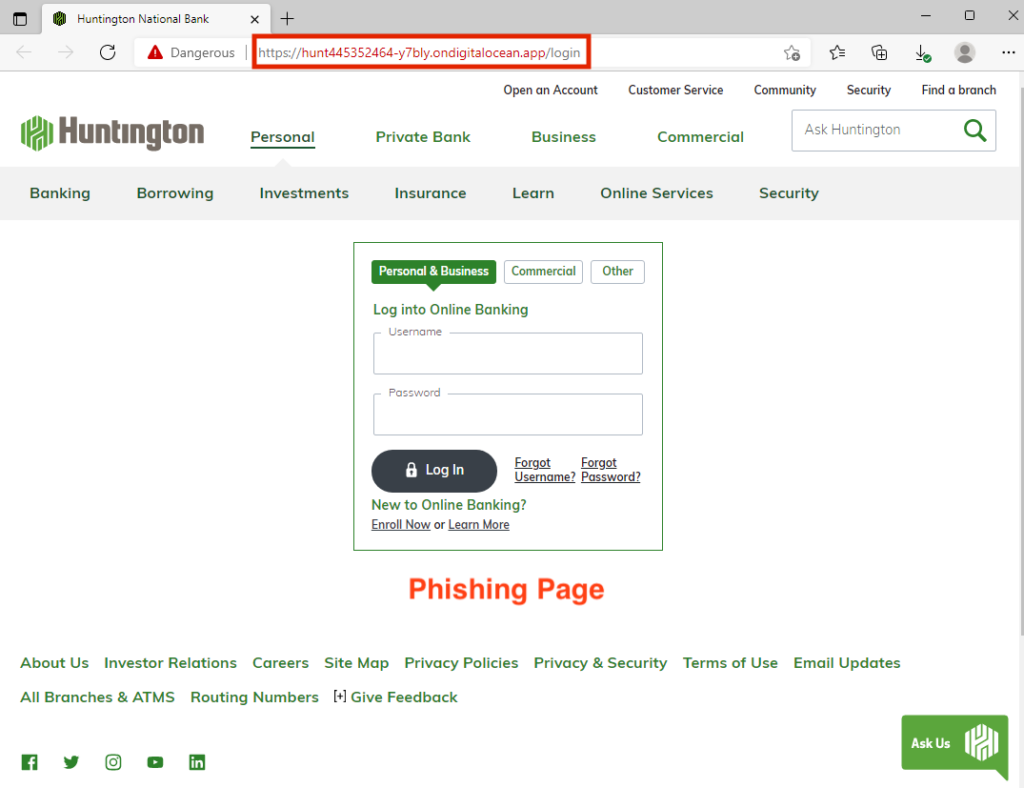
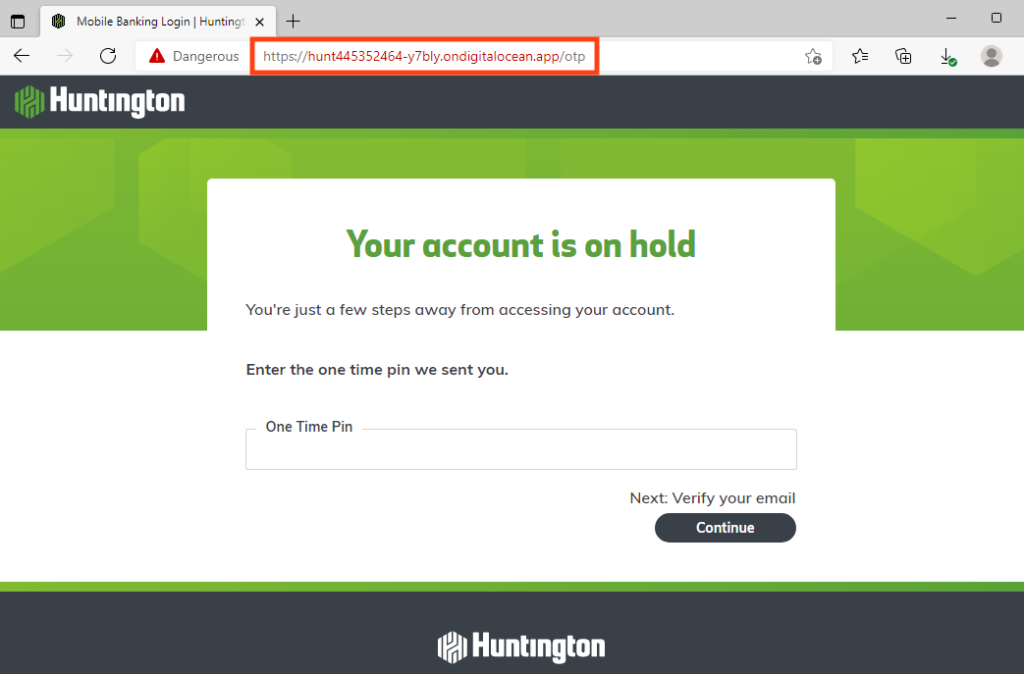
After stealing the username and password, the phishing page asks for the one time pin sent to the victim, as an attempt to bypass the multi-factor authentication.
Then, the phishing tries to steal the victim’s email address and password, using the same technique as the America First phishing.
The phishing campaign then attempts to steal information, such as credit card number, expiration date, CVV, pin, and social security number or tax ID.
Then, all personal information is requested, including full name, date of birth, phone number, carrier pin, and address.
The Huntington phishing page goes even further and requests a picture (front and back) of the victim’s ID or driver license to continue.
And finally, the phishing page redirects the user to the legitimate Huntington website after stealing all the information described above.
Truist
Truist Financial was also targeted, and the phishing page works exactly as the America First phishing page. It attempts to steal the Truist login and password, the victim’s personal information, credit card data, and also the victim’s email and password.
IONOS Webmail
IONOS webmail is the only phishing page in the set Netskope Threat Labs is tracking on DigitalOcean that is targeting email compromise exclusively without also targeting credentials for any financial institutions.
Conclusions
Tech support scams and phishing are a persistent problem, with attackers constantly looking for new ways to target their victims. This latest set of tech support scams and phishing pages are noteworthy because of the focused abuse of DigitalOcean and the success in reaching their victims, resulting in a 17-fold increase in blocking malicious content hosted on DigitalOcean in the Netskope platform. Netskope Threat Labs has been reporting the URLs to the targeted institutions and to DigitalOcean as they are discovered. Although DigitalOcean is promptly taking down the sites, attackers have been responding by continuing to create new ones. Netskope Threat Labs will continue to track and respond to this set of campaigns as they continue and evolve.
Recommendations
The scams and phishing pages described in the post are easily recognisable by the URL, as the attacker has made little effort to disguise the URL. Users can easily avoid becoming victims of the types of attacks described in this post by simply checking the URL and making sure it is the legitimate website. Users should access important pages like their banking portal or webmail by typing the URL directly in the web browser instead of using search engines or any other links, as the results could be manipulated by SEO techniques or malicious ads. We strongly recommend immediately closing web pages that say your computer is infected and also never calling the number on the screen.
Therefore, Netskope Threat Labs recommends that organizations review their security policies to ensure that they are adequately protected against these and similar phishing pages and scams::
- Inspect all HTTP and HTTPs traffic, including all web and cloud traffic, to prevent users from visiting malicious websites. Netskope customers can configure their Netskope NG-SWG with a URL filtering policy to block known phishing and scam sites, and a threat protection policy to inspect all web content to identify unknown phishing and scam sites using a combination of signatures, threat intelligence, and machine learning.
- Use Remote Browser Isolation (RBI) technology to provide additional protection when there is a need to visit websites that fall in categories that can present higher risk, like Newly Observed and Newly Registered Domains.
Protection
Netskope Threat Labs is actively monitoring this campaign and has ensured coverage for all known threat indicators and payloads.
- Netskope Threat Protection
- Document-HTML.Trojan.TechScam
- Document-HTML.Trojan.Cryxos
- Netskope Advanced Threat Protection provides proactive coverage against this threat.
- Gen.Malware.Detect.By.StHeur indicates a sample that was detected using static analysis
- Gen.Malware.Detect.By.Sandbox indicates a sample that was detected by our cloud sandbox
IOCs
Below are the IOCs related to the web pages analyzed in this blog post.
Domains
au-eacj4.ondigitalocean[.]app
clownfish-app-2-acvrg.ondigitalocean[.]app
clownfish-app-3gui7.ondigitalocean[.]app
coral-app-66eu3.ondigitalocean[.]app
coral-app-lql2j.ondigitalocean[.]app
coral-app-oheld.ondigitalocean[.]app
coral-app-yn7we.ondigitalocean[.]app
dolphin-app-cin9g.ondigitalocean[.]app
dolphin-app-gf3v9.ondigitalocean[.]app
dolphin-app-i9rjs.ondigitalocean[.]app
fwd-t7top.ondigitalocean[.]app
goldfish-app-8fmrx.ondigitalocean[.]app
goldfish-app-ede6s.ondigitalocean[.]app
goldfish-app-gmvba.ondigitalocean[.]app
goldfish-app-narvj.ondigitalocean[.]app
goldfish-app-xbbof.ondigitalocean[.]app
hammerhead-app-3icpw.ondigitalocean[.]app
hammerhead-app-6ajmd.ondigitalocean[.]app
hammerhead-app-6xlbp.ondigitalocean[.]app
hammerhead-app-juwp9.ondigitalocean[.]app
hammerhead-app-yqhlx.ondigitalocean[.]app
hunt445352464-y7bly.ondigitalocean[.]app
jellyfish-app-xotim.ondigitalocean[.]app
king-prawn-app-4fyti.ondigitalocean[.]app
king-prawn-app-8hzfo.ondigitalocean[.]app
king-prawn-app-bk8g5.ondigitalocean[.]app
king-prawn-app-s6uog.ondigitalocean[.]app
lionfish-app-9rfsh.ondigitalocean[.]app
lionfish-app-j9fnn.ondigitalocean[.]app
lionfish-app-sek9a.ondigitalocean[.]app
lionfish-app-uasdm.ondigitalocean[.]app
lobster-app-frzqt.ondigitalocean[.]app
lobster-app-or6ca.ondigitalocean[.]app
lobster-app-rcoyt.ondigitalocean[.]app
lobster-app-xkaxb.ondigitalocean[.]app
monkfish-app-29akh.ondigitalocean[.]app
monkfish-app-4e22q.ondigitalocean[.]app
monkfish-app-fkiac.ondigitalocean[.]app
monkfish-app-qjdhk.ondigitalocean[.]app
octopus-app-jxl9c.ondigitalocean[.]app
octopus-app-sl7mc.ondigitalocean[.]app
octopus-app-zvm5e.ondigitalocean[.]app
orca-app-2-3tyvd.ondigitalocean[.]app
orca-app-bxy2l.ondigitalocean[.]app
orca-app-ic4os.ondigitalocean[.]app
orca-app-njlq2.ondigitalocean[.]app
orca-app-nkxdn.ondigitalocean[.]app
oyster-app-2333f.ondigitalocean[.]app
oyster-app-865s6.ondigitalocean[.]app
oyster-app-8kk5m.ondigitalocean[.]app
oyster-app-ca5fh.ondigitalocean[.]app
oyster-app-fubtw.ondigitalocean[.]app
plankton-app-gshpo.ondigitalocean[.]app
sea-lion-app-2-pgi8v.ondigitalocean[.]app
sea-lion-app-9rbus.ondigitalocean[.]app
sea-lion-app-hvqyk.ondigitalocean[.]app
sea-lion-app-nwjq8.ondigitalocean[.]app
sea-lion-app-r4jk3.ondigitalocean[.]app
sea-lion-app-s68eg.ondigitalocean[.]app
sea-turtle-app-ohd6t.ondigitalocean[.]app
sea-turtle-app-w39rq.ondigitalocean[.]app
sea-turtle-app-wswat.ondigitalocean[.]app
sea-turtle-app-x2lyb.ondigitalocean[.]app
sea-turtle-app-z52sr.ondigitalocean[.]app
seahorse-app-7kqqk.ondigitalocean[.]app
seahorse-app-eutff.ondigitalocean[.]app
seahorse-app-gpmks.ondigitalocean[.]app
seahorse-app-yjvts.ondigitalocean[.]app
seal-app-3j9yh.ondigitalocean[.]app
seal-app-69ujp.ondigitalocean[.]app
seal-app-x97ny.ondigitalocean[.]app
seashell-app-fpxh9.ondigitalocean[.]app
seashell-app-ja7sl.ondigitalocean[.]app
seashell-app-xzpy9.ondigitalocean[.]app
shark-app-2ty5w.ondigitalocean[.]app
shark-app-qgt9i.ondigitalocean[.]app
squid-app-apvo6.ondigitalocean[.]app
squid-app-yd9gw.ondigitalocean[.]app
starfish-app-3otoz.ondigitalocean[.]app
starfish-app-9gbhh.ondigitalocean[.]app
starfish-app-cwjye.ondigitalocean[.]app
starfish-app-f94j3.ondigitalocean[.]app
starfish-app-gwo9e.ondigitalocean[.]app
starfish-app-jw7ri.ondigitalocean[.]app
starfish-app-l97z5.ondigitalocean[.]app
stingray-app-96edb.ondigitalocean[.]app
stingray-app-do3v9.ondigitalocean[.]app
stingray-app-se98o.ondigitalocean[.]app
urchin-app-5qitv.ondigitalocean[.]app
urchin-app-lq7wk.ondigitalocean[.]app
urchin-app-sgozg.ondigitalocean[.]app
v1and1-ionos-info-2hyeo.ondigitalocean[.]app
walrus-app-npj6k.ondigitalocean[.]app
walrus-app-tcdda.ondigitalocean[.]app
whale-app-298wp.ondigitalocean[.]app
whale-app-56tpr.ondigitalocean[.]app
whale-app-mqejr.ondigitalocean[.]app
whale-app-usrbm.ondigitalocean[.]app
Phone Numbers Observed in the Tech Scam Pages
+1-844-676-9966
+1-855-341-6126
+1-855-341-7111
+1-855-450-7009
+1-855-598-1009
+1-855-673-8111
+1-855-676-9050


















