Summary
The COVID-19 pandemic caused a dramatic shift to remote work that placed many who previously worked in the office at home working alongside their families. We saw an increase in personal usage of company laptops, including personal web browsing, gaming, media consumption, and online shopping. In this blog post, we will take a look at the personal usage of managed devices from a different angle: data security. In 2020, 83% of users accessed personal app instances from managed devices each month. What kind of data did they upload? Was any of it sensitive?
This blog post accompanies the release of the February 2021 Cloud and Threat Report, which analyzes 2020’s most interesting trends in enterprise cloud and web security. In addition to highlighting personal app usage, the Cloud Threat Report also highlights four other trends:
- Cloud app use continues to rise, with a 20% increase led by collaboration and consumer apps
- Malicious Office documents increased dramatically, now representing 27% of all malware downloads.
- Cloud-delivered malware continues to increase, now representing 61% of all malware.
- Cloud phishing continues to increase, with 13% of phishing campaigns hosted in the cloud and 33% targeting cloud app credentials.
Personal app instances
83% of users on the Netskope Security Cloud platform access personal app instances from managed devices each month. Personal app instances pose a data security threat when users upload sensitive data to them: the organization loses control over access to the data, making it more prone to exposure or misuse. In this blog post, we quantify the risk that personal app instances introduce.
First, what is a personal app instance? Let’s consider Google Drive as an example. A user can upload a file to Google Drive using their @gmail.com account or their @acme.com account. Their @gmail.com account is a personal instance, created and controlled by them, and not managed or monitored by their employer. Their @acme.com account is a managed instance, belonging to and managed by their employer, with controls in place to prevent and detect leaks and misuse. Like Google Drive, users frequently have both business and personal instances of many other apps: Microsoft OneDrive, Zoom, Box, DropBox, GitHub, Slack, etc.
This blog focuses on a specific data security problem: Users uploading data to personal apps instances. On average, a user uploads 20 files to personal app instances per month. This means that an organization with 1,000 employees sees on average 240,000 uploads to personal app instances each year. This blog post provides more details about that data movement.
Uploads
We begin by breaking down which personal apps users upload the most data to. By the number of files uploaded, the pie chart below shows that Google Gmail is by far the most popular personal app for uploads, followed by Google Drive. Among the other top apps are social media apps and other webmail and cloud storage apps. There is also a slice of the pie that represents the other 107 personal apps to which users are uploading files.
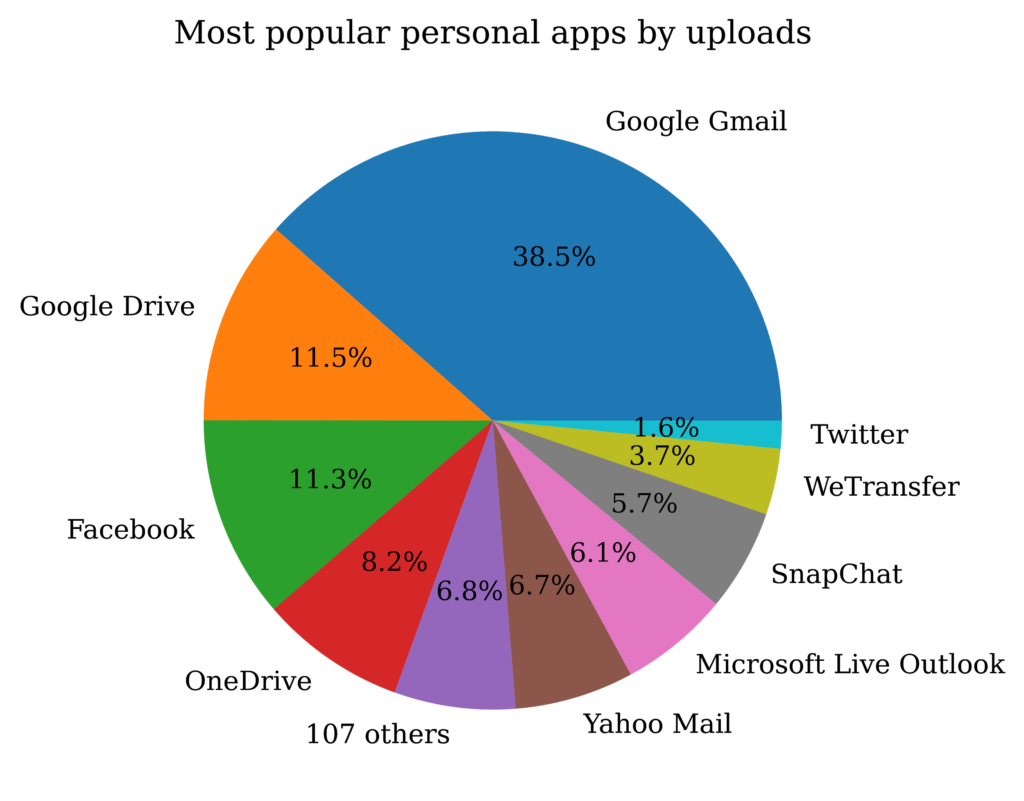
While the types of files uploaded to social media apps are predominately images and videos, the types of files uploaded to the other apps, especially the cloud storage and webmail apps, vary. Overall, the top five types of files uploaded to personal cloud apps were:
- PDFs
- Office Documents
- Source code
- Images
- Archive files
Insider threats
Does any of the data uploaded to personal apps pose a data security risk? To answer this question, we consider two different viewpoints. First, we focus specifically on organizations that implemented data protection policies to prevent their users from uploading sensitive data to personal app instances. For example, an organization might put a policy in place that prevents users from uploading company intellectual property to personal app instances. The top categories of sensitive data that our data protection policies prevented users from uploading to personal app instances were:
- Source code
- Personally identifiable information
- Healthcare records
- Intellectual property
- Encrypted or encoded data
- Financial data
- Secrets, like passwords and API keys
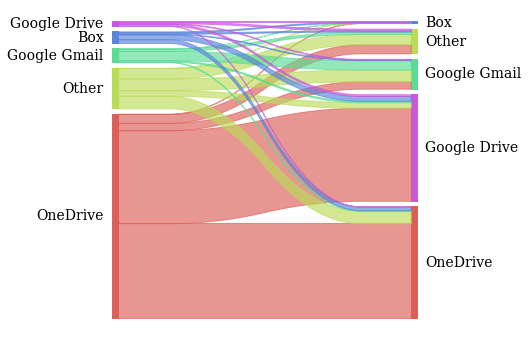
The second viewpoint is data provenance, or where the data the users are uploading to personal apps originates from. Specifically, we consider files that are unique to an organization that were first downloaded from a managed app and then uploaded to a personal app—in other words, files that are likely to contain sensitive information. The Sankey diagram below shows the managed apps on the left and the personal apps on the right. The size of the lines connecting the apps indicates the number of files that were downloaded from the managed instance and uploaded to a personal instance. Managed instances of OneDrive are by far the most popular source of files that are later uploaded to a personal app instance. This is because OneDrive is also the most popular app used by enterprises using the Netskope Security Cloud platform. Similarly, Google Drive and OneDrive are the most popular personal cloud storage apps on the Netskope Security Cloud platform and are therefore also the top personal app instances to which this data is uploaded.
Conclusions
Personal apps instances are widely used in the enterprise. Sensitive data, including intellectual property and source code, are often uploaded to personal app instances. Data is often downloaded from managed apps and then uploaded to personal instances, often of the same app. Netskope’s instance-awareness combined with data protection policies can help prevent users from uploading sensitive data to personal app instances.
The analysis presented in this blog post is based on anonymized usage data collected by the Netskope Security Cloud platform relating to a subset of Netskope customers with prior authorization.

















