We couldn’t be more pleased to announce a major Netskope milestone: our formal launch in the Europe, Middle East, and Africa region.
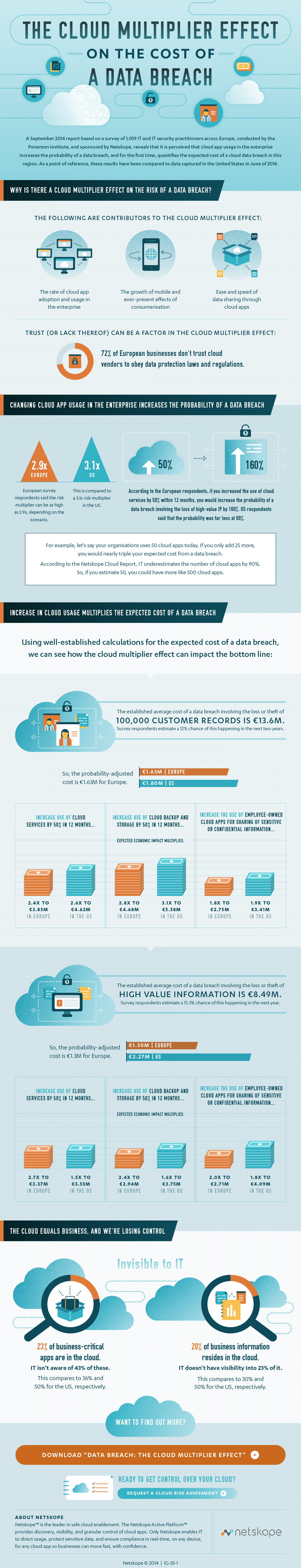
Beyond appointment and product announcements, we are supporting this launch with an unprecedented and critical body of research entitled Data Breach: The Cloud Multiplier Effect. Collaborating with the Ponemon Institute, a long-time expert in data security, privacy, and data breach research, our goal was to bring to light the differences that cloud computing brings to the table for enterprises, and how those differences can impact cloud data security given the ever-growing landscape of data breaches.
The report pulls from a survey of 1,059 IT and security practitioners across Austria, Belgium, Denmark, France, Germany, Greece, Ireland, Italy, Netherlands, Poland, Russian Federation, Slovakia, Spain, Sweden, Switzerland and the United Kingdom (there is also a separate report for Germany by itself, based on a survey of 514 such practitioners within Germany), and measures not only the multiplier effect that cloud services have on the probability and economic impact of a data breach, but also takes stock of perceptions of cloud vendor enterprise-readiness.The report reveals several telling findings about the state of cloud security in EMEA, including:
- The presence of cloud services can increase the probability and economic impact of a data breach involving the loss or theft of customer information by as much as three times.
- A breach involving the loss or theft of 100,000 customer records would cost an organisation €13.6M, based on previously established cost metrics. Probability-adjusted, the expected economic impact comes to €1.63M. When asked about the increased use of cloud services, respondents projected a new probability that brought that estimate to nearly €5M.
- 85 percent of respondents don’t believe their cloud provider would notify them immediately if they had a data breach involving the loss or theft of their intellectual property or business confidential information.
- 77 percent of respondents fear their cloud service provider would not notify them immediately if they had a data breach involving the loss or theft of customer data.
- 57 percent of respondents believe their cloud service providers don’t use enabling security technologies to protect and secure sensitive and confidential information.
- 72 percent believe their cloud service providers aren’t in full compliance with privacy and data protection regulations and laws.
More findings are available in the report infographic included at the end of this post.
This may sound like doom and gloom, but there’s actually never been a better time to safely adopt cloud services in your organisation. Based on our and our customers’ experience, here are three ideas for safely enabling cloud services while mitigating the risk and magnitude of data breaches and other security threats.
First, discover what cloud apps are in your environment and find out how enterprise-ready they are. This is a big step toward understanding and mitigating risk of a data breach because you know what you’re dealing with and can triage the most important apps first. These important apps may include: 1. Systems of record or business-critical apps, including your salesforce automation, renewal and billing, and salary and performance tracking systems, to name a few; or 2. Apps that contain sensitive data, such as a big data app that you use to crunch medical clinical trial results, a business intelligence app that has your company’s non-public financial information, or a software development app that contains your source code, roadmap, and quality assurance bug queue. Did you know that, in addition to being apps that contain sensitive data, each of these is an example of an app that enables sharing?
Second, beyond discovering apps and understanding their risk, it’s critical to know how those apps are being used and what data are being uploaded to and reside in them. Answering questions such as “Is anyone uploading personally-identifiable health information to the cloud?,” “Is anybody downloading personally-identifiable information to a mobile device?,” and “Who’s sharing sensitive content outside of my organisation?” will give you a significant leg up on the problem. Once you can answer these types of questions, you can address the risk, whether by having a conversation with users or line-of-business owners, granularly blocking activities like sharing outside of the company, or encrypting certain data when they are uploaded to the cloud.
Finally, get support. We have tremendous resources in organisations like the Cloud Industry Forum and Cloud Security Alliance. Also, reach out to your vendors such as Netskope and our partners. We have a treasure trove of best practices and advice from customers who have experienced similar challenges.
Data breaches are serious business, and if you believe the respondents in this study, the cloud can have a tremendous multiplying effect on them. However, between understanding your cloud app environment and reaching out for a little help from your friends, you can mitigate the cloud risk multiplier for your organisation and take advantage of all of the productivity benefits that the cloud provides.