The Cloud Threats Memo is a weekly series from Paolo Passeri, digging into a recent cloud threat and highlighting how Netskope can best help mitigate it.
The Anti-Phishing Working Group has recently released its Q4 Phishing Trends Report 2020, which analyzes the top phishing attacks and other identity theft techniques, as reported by the members of the group.
The latest edition brings an important change: according to the APWG data, in Q4 2020 “SaaS/Webmail” was no longer the most targeted sector, sliding to number two with 22.2% (from 31.4% in Q3 2020), and it was overtaken by “Financial Institutions” with 22.5% (from 19.2% in Q3 2020).
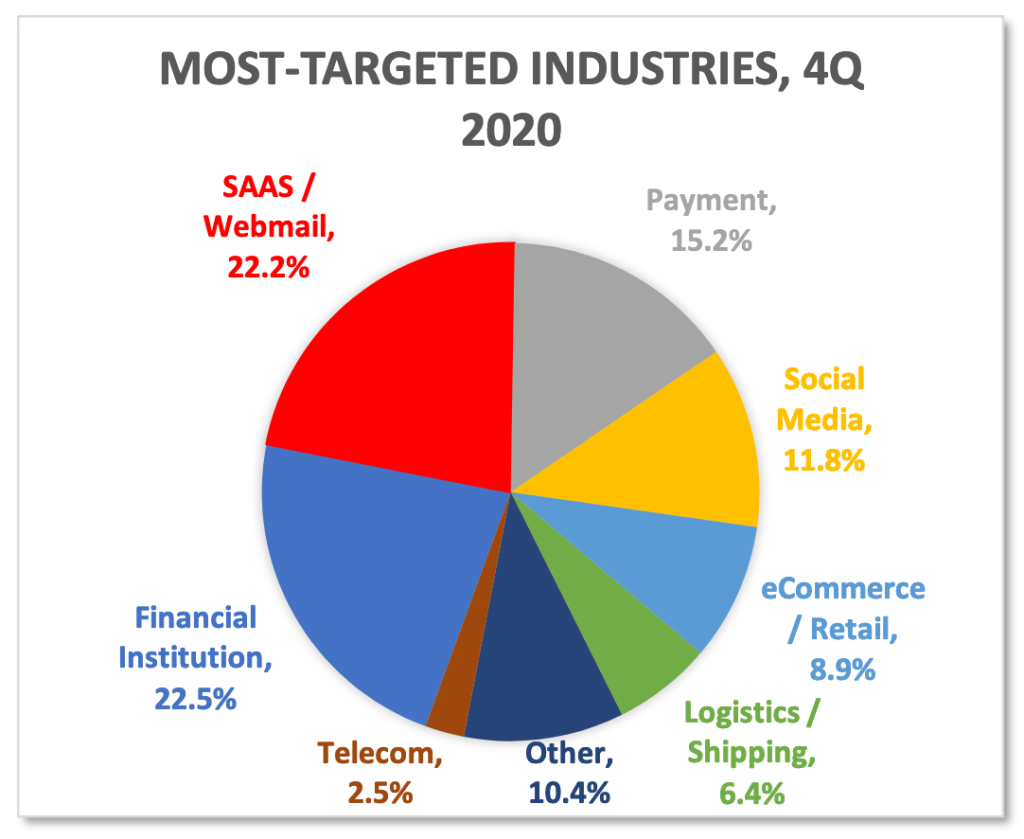
Despite this apparent decrease, SaaS/Webmail services are still top-of-mind for threat actors. A similar recent report released by Check Point saw, unsurprisingly, Microsoft leading the pack of the most impersonated brands in Q4 2020 with a whopping 43%. And Microsoft it’s not the only cloud service in the top ten, given that Linkedin (another brand of the Microsoft galaxy), and Google also appear in the top ten at number three (6%) and seven (2%), respectively. Interestingly, this report places Technology at the top of the sectors.
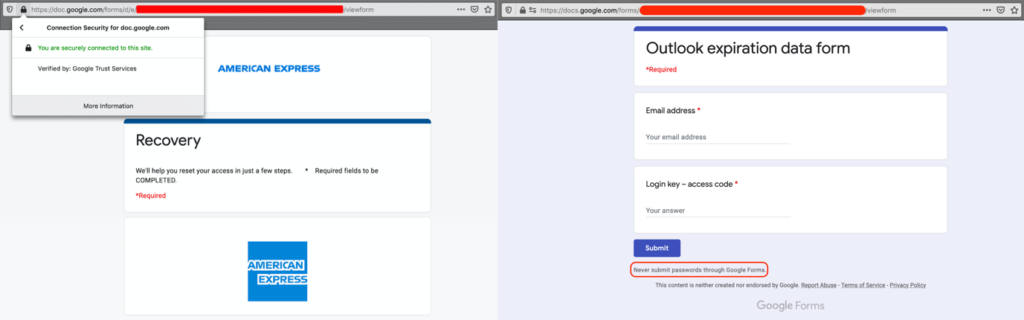
Besides being among the most impersonated brands, SaaS/IaaS applications also offer an ideal infrastructure to deliver phishing pages. As we know, they provide simplified hosting for the attackers, present the user with a legitimate domain, a legitimate certificate, and are implicitly trusted, without considering that they are too often whitelisted by legacy technologies that can’t perform TLS decryption at-scale, or simply lack the context of the connection (meaning they can’t recognize if the traffic is going to a corporate instance or a rogue instance of a cloud application).
It’s interesting to note that in the Top 50 exploited ISPs for phishing in 2021, according to phishstats.info, Google ranks at number three, Amazon at number six, and Microsoft at number eleven. The following picture shows an example of the creativity threat actors apply with two different pages hosted on Google Forms mimicking American Express (left), an organization in the financial sector, and Outlook (right) a webmail service. Unfortunately, the simple layout and the express disclaimer to never submit passwords are not enough to prevent similar campaigns from being successful.
How Netskope mitigates the risk of phishing
Netskope provides web content filtering for more than 120+ categories including “Security Risk – Phishing/Fraud.” This allows for complete protection from phishing for any device/any location. If the phishing pages are served from a legitimate cloud service, Netskope can uniquely identify the context of the connection, thanks to the Cloud XDTM engine, recognizing if the user is landing on a legitimate instance of a cloud service or a rogue instance serving a phishing page.
Regardless of the impersonated brand, the impersonated sector, or where the phishing page is served from, Netskope customers can rely on complete protection against phishing.

















