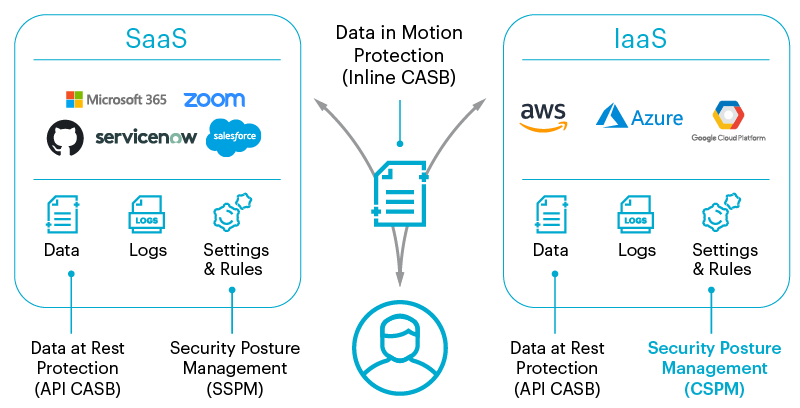
セキュリティポスチャは前述の通りですが、Cloud Security Posture Management (CSPM) は、組織とクラウド間の設定ミスを特定し修正することを目的とした一連のセキュリティツールとプラクティスを意味しています。具体的には、Amazon Web Services (AWS)、Microsoft Azure、Google Cloud、などのクラウドサービスプロバイダー (CSP) のInfrastructure-as-a-Service (IaaS) クラウド環境などのサービスを対象とします。
これは、SaaS アプリケーションの構成を扱う SaaS Security Posture Management (SSPM) とは違います。CSPMとSSPMはカバーするインフラストラクチャやプラットフォームサービスが異なるのです。

CSPMが必要な理由とは?
多くの企業がオンプレミスのデータストレージやウェブホスティングからクラウドベースのインフラストラクチャに移行する中、クラウドサービスの利用は増加傾向にあります。設定ミスに伴うセキュリティリスクは数多くあります。実際、クラウド設定ミスの48%が機密データの漏洩に繋がっています。データ、ユーザー、デバイス、システムのすべてが、意図的または意図しない侵害のリスクにさらされているのです。
クラウドインフラストラクチャを正しく設定したとしても、時間の経過とともに(意図的または意図せずに)元の設定から外れていく可能性があります。これは「設定ミスドリフト」と呼ばれるもので、データをある場所から別の場所に移動させるなど、特定の業務上の必要性から、ユーザーが例外的に権限などの設定をし直すことで発生します。問題は、このような変更によって、意図せずとも他の資産が露出してしまうことです。最終的に、これらの変更が積み重なって、クラウドの安全性が損なわれ、本来ならアクセスできないはずの人たちが資産やシステムにアクセスできるようになってしまいます。
ブログ: CSPMとSSPMによる設定エラーへの対応




 戻る
戻る