On a recent visit to a company highlighted as a shining star of disruptive innovation, the CISO expressed concern about being blindsided by third-party apps connecting to their Google Suite. He was concerned about a proliferation of third-party apps that can, at a click of a button, gain complete control of a user’s data whether that data is personal or corporate information.
The permissions for these third-party apps are granted behind the scenes via OAuth access tokens and the Gdrive Admin may be unaware of a new third-party app that is allowed to not only view but also manage corporate data. Google does provide the capability to allow list certain apps and revoke the tokens, however we have noticed that this capability has some limitations. This is where Netskope provides added value to the G Suite offering.
For G Suite, Netskope lists the third-party apps that are installed in the customer domain using an OAuth 2.0 token. Netskope identifies these apps and describes them using a Netskope Cloud Confidence Index (CCI) score, Google scopes (permissions) required to run those apps, and severity type (High or low severity).
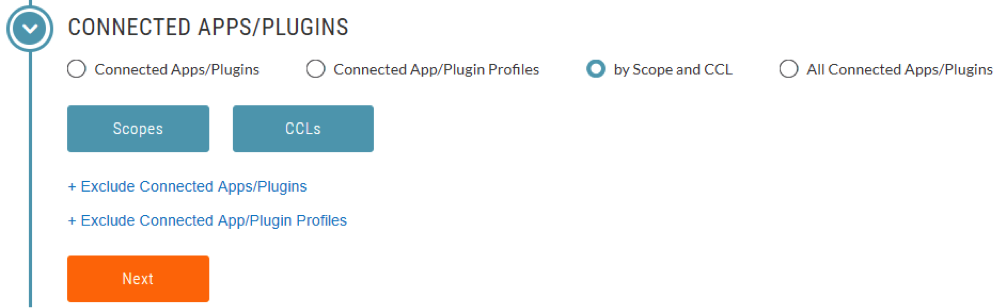
Users can create policies to revoke apps based on specific criteria. Policies may be based on an app ID, scopes used, CCI score, and more. Here are some fine-grained use cases.
- Revoke app access for either all users or selected users who have installed the app. (i.e allow only certain users to install apps and exclude others from the policy).
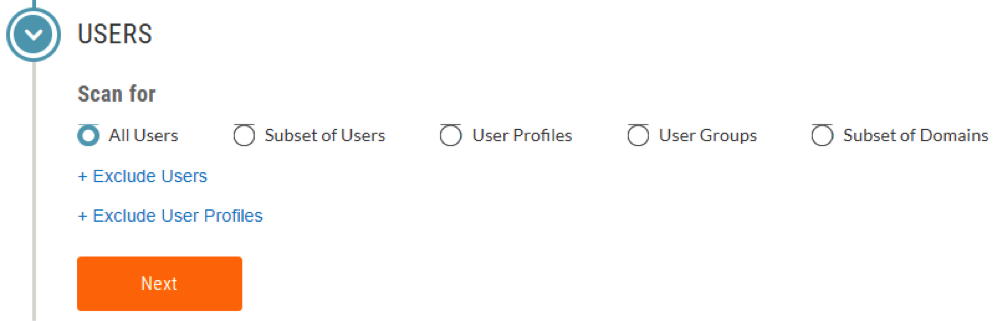
- Allow certain apps for certain users but revoke for everyone else
- Leverage multiple criteria for revocation policies. For example, revoke based on:
- A selected profile comprising a custom list of Google apps and plugins or upload a .csv file comprising the same.
- 200 different Google scopes (set of resources and operations that an access token permits like view, manage, share, etc.). You have the option to select a single scope or multiple scopes. You can also select All, High Impact, or Low Impact to further filter the scopes shown.
- With this option, you can select apps/plugins based on their Cloud Confidence Index Level (CCL).
- With this option, all connected apps/plugins are selected.

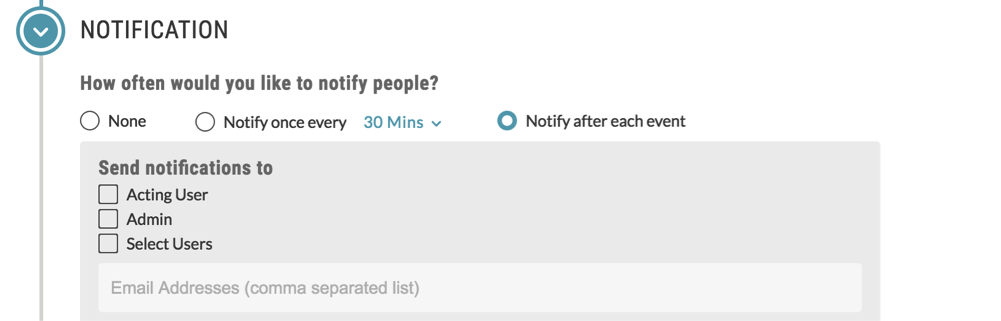
Of course, we wouldn’t want you to be inundated with support cases about not being able to access revoked third-party apps. So Netskope gives you the capability to email users that their app is being revoked.
So keep calm and allow your employees to install these plugins knowing fully well that you have the ability to monitor and control third-party apps and block high-risk apps with unnecessary and irrelevant permissions needed for installation. This should also reduce the risk of being a victim of the next Google phishing attack.