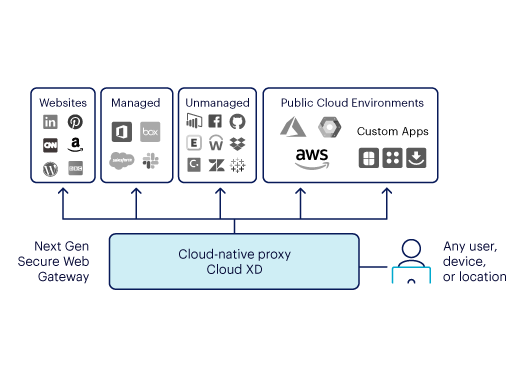
A traditional web filter only looks at URLs and web objects in HTTP/S transactions. Netskope One Next Gen SWG decodes the actual content and context of SaaS cloud traffic. This allows the gateway to see beyond web categories and web objects into SaaS application traffic for risky behaviors, coaching users in real time, detecting data exfiltration to personal cloud storage with instance awareness, and allowing users to provide justifications for unusual requests so business continuity is enabled.




 Back
Back

















)

)