Summary
On July 12, 2022, Microsoft researchers disclosed a large-scale phishing campaign that has targeted more than 10,000 organizations since September 2021. The campaign used adversary-in-the-middle (AiTM) phishing sites to proxy the authentication process and hijack the victims’ Office 365 session cookies.
With these stolen session cookies, the attackers were able to authenticate to Office 365 as the victims and perform a whole slew of malicious activities from the user’s mailboxes, such as business email compromise (BEC).
Attackers have been using real-time active directory authentication since late 2020 and last year, researchers identified a new fingerprinting technique, called PHOCA, that makes it possible to identify AiTM phishing kits. There are also phishing attacks that make use of malicious OAuth apps. This particular attack is different and effective because it bypasses corporations’ MFA protections, since capturing a user’s session cookie enables an attacker to skip the authentication workflow (including MFA) altogether.
Threat
The attackers used the Evilginx2 phishing kit to carry out the AiTM attacks. The initial lures were emails that contained “important” voice messages, which in reality ended up downloading malicious html attachments. When a victim clicked on these attachments, they were redirected to the Office 365 credential-stealing landing pages.
Contrary to the traditional phishing setup, AiTM phishing does not require a custom built phishing site, but rather the requests are proxied to and from the actual website. The phishing site creates a proxy to the organization’s Azure Active Directory login portal (login.microsoftonline.com). Essentially, the attackers open up two lines of communication: one from the victim to the attacker-controlled phishing site and one from the attacker-controlled site to the real Office 365 login portal. Hence the URL used by the phishing campaign would be different from the original website, which is not the case in other phishing attacks like device code phishing attacks.
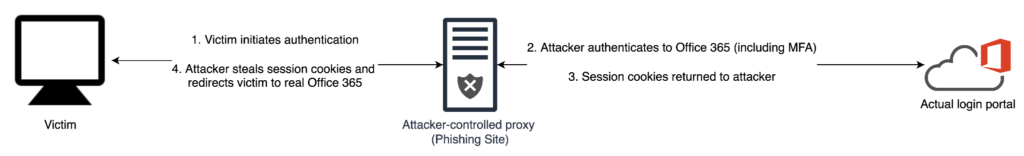
Once the victim logs into the phishing portal, the attacker steals the session cookies and is able to authenticate to Office 365 via Outlook Web Access (OWA) on a Chrome browser. The endgame for the attackers appeared to be using existing email threads to perform payment fraud by hijacking ongoing finance-related email threads in the compromised account’s mailbox.
Protection
The above-mentioned attack circumvents MFA. However, MFA still remains a powerful and very effective security control to fight off credential attacks. Hence, organizations should still use MFA to protect their users. Defending this specific attack, however, can really be broken down into protecting against two threats:
- A phishing attack (Step 1 in Fig above)
- Train employees on how to identify and report phishing attacks
- Inform employees to never post sensitive information on social media
- Sandbox and scan incoming emails for malicious phishing content
- Use a combination of threat intelligence, signatures, heuristics, and machine learning to identify and block phishing pages in real time
- Use a SWG to prevent credential submission to unknown places. If you are using SSO, that SSO portal is likely the only place your users should be entering their credentials.
- Followed by a compromised credential attack (Step 2 & 3 in Fig above)
- Identify anomalous attempts to use stolen credentials from new locations
- Evaluate sign-in requests using additional signals like group membership, IP information, ISP, user agent, use of anonymisation services, and compliant devices status
- If possible, allow connections only from specified IP address ranges
Netskope provides proactive coverage against this and other phishing threats via threat protection, advanced threat protection, and UEBA.
- Netskope Threat Protection
- Netskope uses threat intelligence, signatures, heuristics, and machine learning to identify and block phishing pages in real time
- Known phishing pages will generate “malsite” alerts, while phishing pages detected through content inspection will generate “malware” alerts.
- Netskope Advanced UEBA detects compromised accounts by identifying unusual behaviors associated with account compromise, including:
- Activity from a risky country
- Access from IP ranges that are unusual for the user or organization
- Unusual data access patterns, including spikes in files downloaded

















