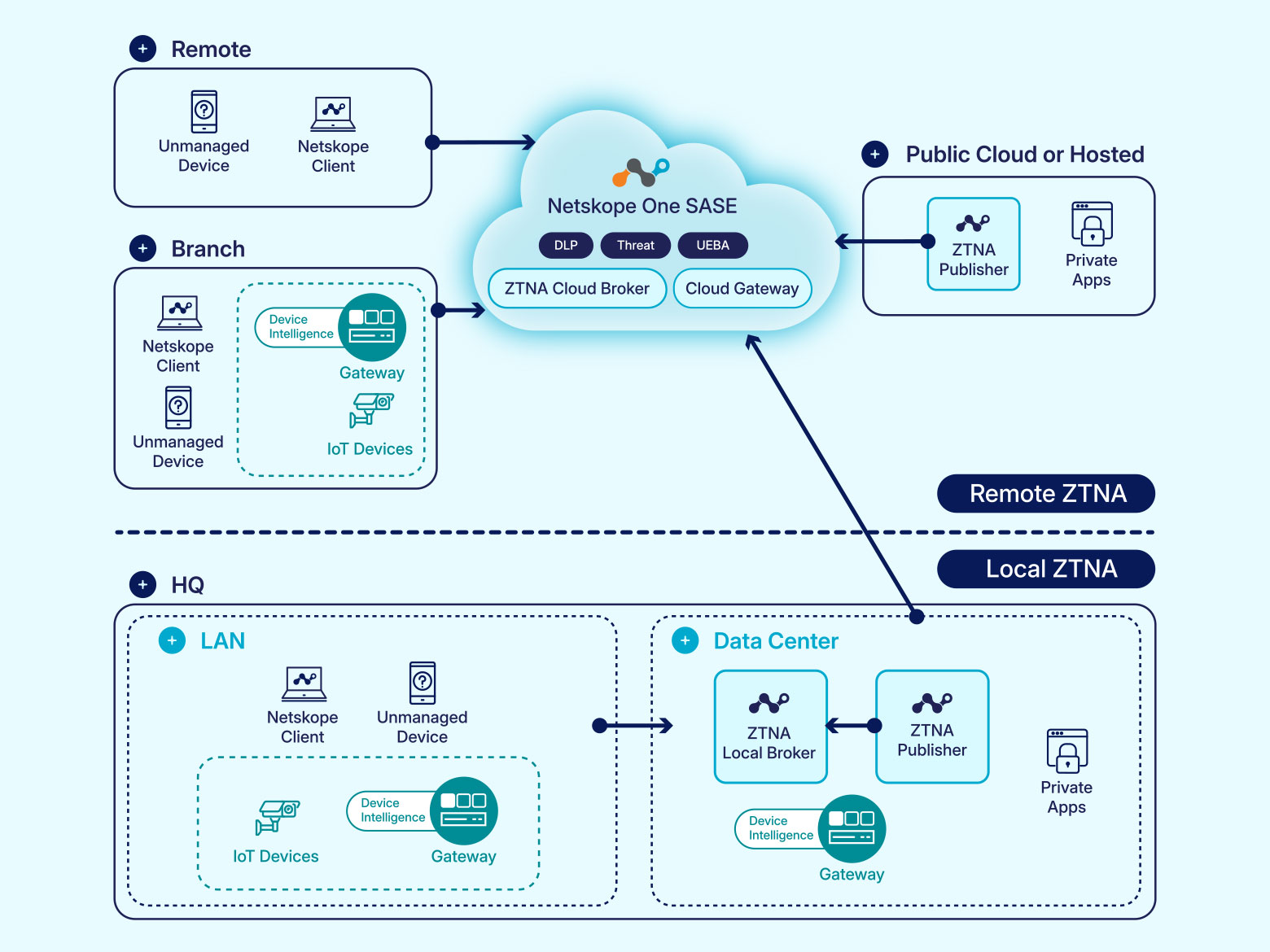
Universal ZTNA (UZTNA) extends traditional zero trust network access by securing not only users but also IT, OT, and IoT devices. It delivers identity-centric, zero-trust access across on-prem, cloud, and hybrid environments, with unified policies, continuous monitoring, and real-time enforcement to ensure consistent security and user experience everywhere. Unlike traditional ZTNA, which is often limited to user-to-app access, UZTNA unifies controls across people, devices, and environments, remote, campus, and beyond.
For enterprises, this means stronger security, simplified operations, and seamless high-performance access to any application, from any device, managed or unmanaged. With its ability to consolidate and replace legacy VPN, NAC, and VDI tools, universal ZTNA is the modern standard for organizations looking to support hybrid work, secure unmanaged devices, and prepare for the future of AI-driven, risk-aware access.
Traditional ZTNA | Universal ZTNA |
Designed mainly for remote user access | Extends secure access to remote, branch, campus, and non-user devices (IoT/OT) |
User experience varies by location (remote vs. on premises) | Delivers a consistent user experience everywhere |
Coverage of endpoint-initiated apps | Coverage of endpoint- and server-initiated apps |
Agent-based access (managed devices) | Agent-based or agentless access (unmanaged/BYOD) |
Multiple, disparate policy engines and enforcement points | Single, unified policy engine for all users and devices |
Access permissions rarely adapt after login | Real-time, risk-based adjustments based on user and device behavior |
Cloud-based trust broker | Cloud- and local-based broker |
Requires multiple management consoles | Managed through a single administration console |




 Back
Back