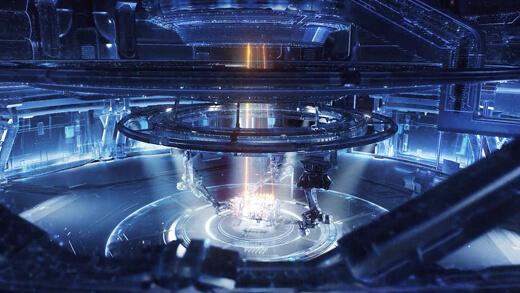
The Zero Trust Engine is the “brain” of the Netskope One platform. Unlike legacy “bolt-on” security that creates latency and policy gaps, this engine is a single-pass architecture. It decrypts, decodes, and inspects all traffic in one unified flow—applying granular controls across web, cloud, and private apps simultaneously without multiple redundant inspection “hops.”
+2

























)